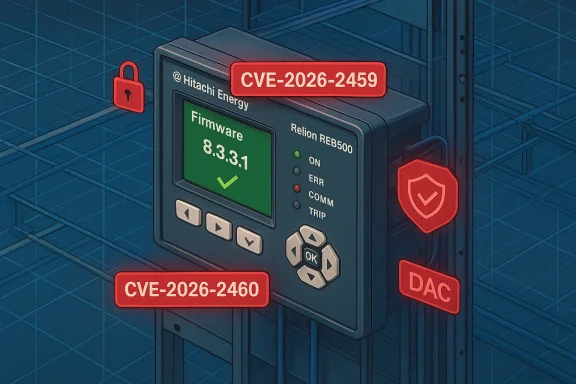
Hitachi Energy's Relion REB500, a cornerstone device for distributed busbar protection in modern substations, has been the subject of coordinated vulnerability disclosures that should be treated as urgent by utilities and integrators. Two privilege-related vulnerabilities — tracked as CVE-2026-2459 and CVE-2026-2460 — allow authenticated users with elevated or even low-level credentials to read and modify directory contents they should not be able to access. Hitachi Energy and public vulnerability databases identify the affected firmware as versions earlier than 8.3.3.1, and the vendor’s recommended remediation is to upgrade to REB500 version 8.3.3.1 as soon as practicable. s://nvd.nist.gov/vuln/detail/CVE-2026-2459)
The Relion REB500 is an IEC 61850‑enabled intelligent electronic device (IED) used for protection, control, measurement and supervision of busbar systems. Operators use the REB500 to create distributed protection solutions across multiple bays; its communications and file services are therefore frequently accessible to station‑level networks and maintenance systems. These attributes — while enabling operational efficiency — also increase the potential blast radius if access controls are bypassed. The REB500’s product page, which describes features such as centralized account management, HMI access and support for IEC standards, provides context for why a directory‑access vulnerability on this device is consequential to utilities and grid operators.
The security disclosures were published and coordinated with authorities and vendor channels in late February 2026. Public records (including vendor advisories and NVD entries) summarize the weaknesses as access‑control failures: an Installer role with overly broad permissions (CVE‑2026‑2459) and a DAC‑protocol path that permits low‑privilege accounts to reach and alter protected directories (CVE‑2026‑2460). The common classification is CWE‑267 — Privilege Defined With Unsafe Actions, an indicator that the device’s role or protocol handlers grant operations beyond the principle of least privilege.
Why it’s serious:
Why it’s serious:
Practical mitigation options while patching:
These vulnerabilities reinforce the practical reality of OT security: design choices and access‑control models in field devices matter as much as — if not more than — traditional network hardening. For grid operators and integrators, the safest course is immediate mitigation followed by methodical patch rollout and strengthened credential and protocol controls to reduce the chance that authenticated access will translate into operational compromise.
Source: CISA Hitachi Energy Relion REB500 Product | CISA
 Background
Background
The Relion REB500 is an IEC 61850‑enabled intelligent electronic device (IED) used for protection, control, measurement and supervision of busbar systems. Operators use the REB500 to create distributed protection solutions across multiple bays; its communications and file services are therefore frequently accessible to station‑level networks and maintenance systems. These attributes — while enabling operational efficiency — also increase the potential blast radius if access controls are bypassed. The REB500’s product page, which describes features such as centralized account management, HMI access and support for IEC standards, provides context for why a directory‑access vulnerability on this device is consequential to utilities and grid operators.The security disclosures were published and coordinated with authorities and vendor channels in late February 2026. Public records (including vendor advisories and NVD entries) summarize the weaknesses as access‑control failures: an Installer role with overly broad permissions (CVE‑2026‑2459) and a DAC‑protocol path that permits low‑privilege accounts to reach and alter protected directories (CVE‑2026‑2460). The common classification is CWE‑267 — Privilege Defined With Unsafe Actions, an indicator that the device’s role or protocol handlers grant operations beyond the principle of least privilege.
What the advisories say — quick, verifiable facts
- Affected product: Hitachi Energy Relion REB500 firmware versions prior to 8.3.3.1.
- CVE identifiers:
- CVE‑2026‑2459 — Installer role can access and alter directories outside its intended scope.
- CVE‑2026‑2460 — Low‑privilege users can leverage the DAC protocol to access/modify directory contents.
- Vendor remediation: update to REB500 version 8.3.3.1 (vendor advisory and downstream aggregators list 8.3.3.1 as the fixed release).
- Severity: public CVSS and CNA scores vary; vendor/NVD reporting places the issues in the medium–high range depending on metric set and attack requirements (CVSS v3/v4 variants have been published). Operators should assume significant loss of confidentiality and integrity is possible if exploited.
Technical analysis — how both CVEs work and why they matter
CVE‑2026‑2459: Installer role overreach
The first issue stems from a role‑based access control (RBAC) misconfiguration or enforcement bug: an authenticated user assigned the Installer role can access and alter directories beyond what the role is meant to permit. In practice, an Installer account is routinely used during commissioning, maintenance and firmware updates — activities that are often performed from station or engineering networks. If that role is too permissive, a compromised or rogue Installer credential becomes a powerful tool for an attacker to tamper with configuration files, logs or software packages stored in on‑device directories.Why it’s serious:
- Installer accounts are often trusted and may be excluded from strict daily monitoring during maintenance windows.
- Unauthorized modification of directory contents can change protection settings, introduce malicious binaries, or corrupt profile/state data, potentially undermining protection functions.
- Because this is an authenticated privilege misuse, detection via standard network intrusion signatures may be delayed until operational anomalies appear.
CVE‑2026‑2460: DAC protocol privilege bypass
The second issue takes advantage of how the device processes DAC (data acquisition/control) protocol requests. A low‑privilege user can craft requests that the DAC handler accepts and uses to read or write directory entries without the proper authorization check. Unlike pure web‑UI bugs, this vector targets the protocol stack used by OT management systems and remote IED communications — a layer that sometimes bypasses hardened management interfaces.Why it’s serious:
- DAC is a legitimate operational protocol; restricting or filtering it can be operationally frictionful, so it’s often allowed across station networks.
- A low‑privilege account is easier to obtain through social engineering, credential reuse, or lateral movement than an administrative account.
- Protocol‑level exploitation can be automated and scripted, enabling rapid, large‑scale misuse across many devices if credentials exist.
Attack scenarios and operational impact
Think beyond a single compromised device. Reasonable exploitation paths include:- A compromised Installer laptop or stolen Installer credentials used during a routine firmware update — the attacker uses Installer permissions to write malicious configuration files that disable alarms or change trip thresholds.
- A contractor account with low privileges inadvertently exposed to the station LAN is used to probe DAC endpoints; the attacker escalates impact by modifying device files that get processed by protection functions.
- An attacker performs small directory modifications that silently alter logging or replay record files, hampering forensic collection and masking later intrusion steps.
- Silent tampering with protection settings that can disable or desensitize relays, increasing risk of equipment damage or outages.
- Corruption of device state or firmware images, causing unpredictable behavior or loss of protection.
- Loss or alteration of logs and telemetry, making incident detection and recovery far harder.
Vendor response, patching and mitigations
Hitachi Energy’s published remediation is straightforward: upgrade REB500 to firmware 8.3.3.1 where the permission checks and DAC handling have been corrected. Public vulnerability records and vendor‑referenced advisories repeatedly point operators to that fixed version.Practical mitigation options while patching:
- Disable the Installer role when not actively performing firmware updates or commissioning. Enable it only for the minimum window required,ndows closely. This is a vendor‑suggested mitigation in the advisory and is an effective stopgap when patches cannot be applied immediately.
- Limit DAC protocol exposure: firewall or ACL DAC ports so that only authorized engineering/management hosts can reach REB500 devices. Where possible, avoid exposing DAC to broader station networks.
- Enforce strict credential hygiene for Installer and maintenance accounts: unique credentials, rotation, and multifactor authentication (MFA) where supported by identity gateways or jump hosts.
- Implement file integrity monitoring on REB500‑accessible directories and alert on unexpected writes or permission changes.
- Apply network segmentation (separating business, engineering, and OT traffic) and restrict remote access via hardened jump hosts and modern VPNs with endpoint posture checking. CISA and vendor guidance stress minimizing network exposure for control system devices.
Detection and response playbook for operators
Operators should treat these advisories as actionable and uncident response plans accordingly.- Inventory: Identify every REB500 device on your network and list firmware versions. Prioritize devices in critical substations or those with remote management exposure. Use configuration management databases and asset discovery tools to cross‑check.
- Patch plan: Schedule firmware updates to 8.3.3.1 following normal change control — but accelerate where devices are reachable from non‑trusted networks. Test in a lab or an isolated staging environment before wide deployment.
- Monitoring: Enable and centralize device‑level logging, and set alerts for suspicious Installer activity or unexpected file writes. Monitor DAC protocol traffic patterns; anomalous sequences or write operations from low‑privilege accounts should trigger immediate investigation.
- Hardening: Remove or restrict default or unnecessary accounts, disable installation/maintenance roles when idle, and restrict file transfer services (FTP/SFTP) to known hosts. Implement role separation and least privilege for all maintenance functions.
- Incident response: If unauthorized changes are detected, follow standard OT IR steps: isolate the affected device, preserve volatile logs, capture memory/firmware images if safe to do so, and coordinate with vendor support and national CSIRTs. Consider rolling back to a known good configuration if integrity cannot be confirmed.
Critical evaluation — strengths and risks in the vendor and public response
Strengths:- Coordinated disclosure: The vendor provided a fixed firmware line (8.3.3.1) and published advisories that were republished by national authorities, which is the right operational model for ICS vendors. Public records (NVD and security vendors) reflect this coordination.
- Actionable mitigations: The vendor recommended simple mitigations — disabling Installer role when unused — that are practical for on‑site engineers and can be implemented quickly to reduce risk before patching.
- Deployment friction: Upgrading firmware in substation equipment often requires planning, testing and outage windows. Operators may be unable to immediately apply the vendor update across distributed fleets, leaving time for adversaries to exploit weaknesses if compensations are not enforced. This operational reality increases urgency for mitigations and network controls.
- Credential exposure and insider risk: Because the vulnerabilities require authenticated access (Installer role or low‑privilege account), the real threat vector includes credential theft and misuse. Many OT environments do not yet mandate MFA or strong centralized identity for device maintenance, which raises ris
- Detection limitations: Protocol‑level abuse via DAC may not be visible to traditional IT IDS systems. Many utilities lack full IEC/OT protocol visibility, requiring investment in specialized monitoring to detect misuse effectively.
Practical rollout checklist for utilities and integrators
- Inventory all REB500 devices and confirm current firmware version. Prioritize by criticality and network exposure.
- Schedule a staged firmware upgrade to REB500 8.3.3.1: test in lab environments, validate protection settings and backup device configurations before deployment.
- Implement immediate mitigations:
- Disable Installer role between maintenance windows.
- Restrict DAC ports via firewall rules and ACLs to management networks only.
- Harden credentials: rotate and remove shared Installer/maintenance passwords, require unique operator accounts and, where possible, use jump hosts with MFA.
- Monitor and alert: enable file integrity checks on critical directories and watch for unexpected writes; add DAC protocol monitoring to NOC/SOC dashboards.
- Update incident response playbooks to include REB500 compromise scenarios and contact vendor support channels immediately if integrity concerns arise.
Detection examples and tactical indicators to implement now
- Unexpected file timestamps or sizes in configuration directories.
- Installer‑role logins at odd hours or from unexpected source IPs.
- DAC protocol write operations initiated by low‑privilege accounts.
- Repeated DAC requests that attempt directory traversal or unusual filmplement alerts that combine these indicators with threat intelligence — even low‑probability DAC anomalies should generate operator review for high‑value IEDs.
Broader lessons for OT security
- Role hardening matters. Roles intended for maintenance or commissioning should be time‑limited and separated from routine operator access.
- Protocol exposure is a common blind spot. Operational protocols (IEC, DAC, serial tunnels) often bypass hardened perimeters; they must be explicitly controlled and logged.
- Change management and asset visibility are defensive multipliers. If you cannot quickly inventory which REB500 firmware versions are in the field, you cannot reliably prioritize remediation.
- Vendor coordination is effective but requires operational readiness. A vendor patch must be consumable by field teams — including clear upgrade instructions, rollback plans and test guidance — to be truly useful.
Final assessment and urgent recommendations
These CVEs — CVE‑2026‑2459 and CVE‑2026‑2460 — exploit the same root cause family: insufficient enforcement of role‑ and protocol‑level authorization on devices that sit at the protective core of power substations. The vendor has provided a fix (REB500 8.3.3.1), and operators should treat the advisory as high priority:- Immediately plan and execute upgrades to REB500 8.3.3.1 after lab validation.
- Where a full upgrade cannot be done immediately, disable the Installer role between maintenance windows, restrict DAC access at the network perimeter, and enforce credential hardening.
- Enhance detection for DAC protocol anomalies and file integrity events on REB500 devices.
These vulnerabilities reinforce the practical reality of OT security: design choices and access‑control models in field devices matter as much as — if not more than — traditional network hardening. For grid operators and integrators, the safest course is immediate mitigation followed by methodical patch rollout and strengthened credential and protocol controls to reduce the chance that authenticated access will translate into operational compromise.
Source: CISA Hitachi Energy Relion REB500 Product | CISA