Microsoft released KB5087583 on April 30, 2026, as a Setup Dynamic Update for Windows 11 versions 24H2 and 25H2, improving setup components while again warning that Secure Boot certificates on most Windows devices begin expiring in June 2026. The update itself is not dramatic; the timing is. Microsoft is using even routine servicing notes to push administrators toward a deadline that is now measured in weeks, not quarters. The message is blunt beneath the bland KB prose: the Windows boot chain is entering its first ecosystem-scale trust rollover, and waiting for Patch Tuesday muscle memory to solve it is a gamble.
KB5087583 is, on paper, the kind of servicing artifact that usually slips past everyone except deployment engineers. It updates Windows setup binaries and files used during feature updates for Windows 11 24H2 and 25H2. It is available through Windows Update, the Microsoft Update Catalog, and WSUS, requires no restart, and replaces a prior setup dynamic update.
That sounds administrative, almost boring. But Microsoft placed a prominent Secure Boot warning at the top of the support article, and that placement matters. The company is no longer treating the 2026 certificate rollover as a niche UEFI footnote. It is attaching the warning to the plumbing of Windows setup itself.
Setup Dynamic Updates exist to make Windows upgrades less brittle. They refresh the components Setup uses before and during an upgrade, helping the installer cope with newer compatibility data, drivers, and servicing changes. When that sort of update carries a Secure Boot warning, Microsoft is effectively telling IT departments that upgrade readiness and boot-chain readiness are now part of the same operational conversation.
The important distinction is that KB5087583 is not, by itself, the universal fix for Secure Boot certificate expiration. It is a setup servicing update with a warning attached. The fix lives in a broader certificate rollout involving Windows updates, firmware readiness, OEM cooperation, registry targeting for managed environments, event monitoring, and in some cases manual action.
That is precisely why the warning deserves attention. If this were just another cumulative update note, administrators could file it under monthly patch hygiene. Instead, Microsoft is trying to surface a quiet infrastructure deadline in every channel it can.
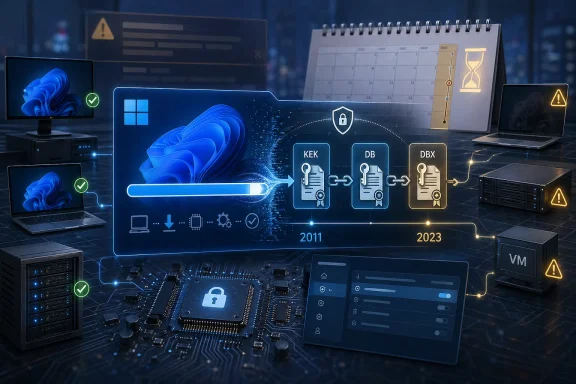
The problem is not that Secure Boot suddenly stops being a good idea in June 2026. The problem is that certificates have lifetimes. Microsoft’s 2011-era Secure Boot certificates begin expiring in June 2026, with the Windows Production PCA 2011 certificate following in October 2026. That schedule turns an abstract certificate lifecycle into a fleet management problem.
Microsoft’s new 2023 certificates are meant to replace the old anchors. The Microsoft Corporation KEK CA 2011 gives way to the Microsoft Corporation KEK 2K CA 2023. The Windows boot loader moves from trust rooted in the Microsoft Windows Production PCA 2011 to the Windows UEFI CA 2023. The older third-party UEFI CA is being split into more granular trust for third-party boot loaders and option ROMs.
That split is more than housekeeping. It lets systems trust third-party boot loaders without necessarily extending the same broad trust to option ROMs, or vice versa. In other words, Microsoft is not merely renewing an expiring card; it is tightening the shape of trust in the firmware era.
For home users, that distinction may feel academic. For administrators, security teams, Linux dual-boot users, virtualization operators, and anyone managing fleets of older hardware, it is not. The firmware trust store is not a web browser certificate store. You do not want to discover during an outage window that the machine’s boot policy and Microsoft’s new signing chain never shook hands.
That sounds reassuring, and it is — up to a point. The trouble is that “the computer still turns on” is a low bar for security compliance. The deeper consequence is that devices without updated certificates may no longer receive new protections for early boot components, including Secure Boot database updates, revocation updates, boot manager protections, and mitigations for newly discovered boot-level vulnerabilities.
That is the slow-burn risk Microsoft is trying to prevent. Bootkits are dangerous precisely because they operate before the operating system has a chance to defend itself. Once the boot chain is no longer receiving new trust and revocation updates, the system drifts into a degraded security posture even if the desktop looks perfectly healthy.
This is where the messaging gets awkward for Microsoft. Consumers hear “certificate expiration” and worry about a mass boot failure. Enterprises hear “no longer receiving boot-level security protections” and worry about audit exceptions, cyber insurance attestations, and incident response scenarios in which the endpoint agent never had a chance.
Both fears are understandable. But the second one is the more realistic management problem. The June 2026 deadline is not a cinematic cliff where every unpatched PC falls off at once. It is the start of a period in which outdated boot trust becomes an increasingly embarrassing and dangerous exception.
This is sensible engineering. Secure Boot certificate updates touch firmware variables and boot policy, two areas where a bad assumption can produce a very bad day. A staged rollout informed by device health signals is safer than blasting the same change indiscriminately across every machine ever sold since the Windows 8 era.
It is also a governance headache. Some organizations deliberately minimize diagnostic data, route updates through tightly controlled systems, or treat Microsoft-managed rollout behavior as something to be fenced off rather than embraced. For those shops, the “automatic” path becomes less automatic.
Microsoft’s answer is an opt-in mechanism for managed environments, including a registry value under the Secure Boot control path. The company recommends targeting devices so Windows’ scheduled task can process the certificate update bits in order, applying the relevant 2023 certificates and eventually updating the boot manager to one signed by the newer Windows UEFI CA 2023.
That is a reasonable deployment model, but it is not a consumer-grade switch. It demands inventory, targeting, monitoring, and rollback planning. It also makes clear that Secure Boot is no longer a firmware checkbox administrators can safely ignore after imaging day.
This is where fleet reality becomes messy. Enterprises rarely run one perfectly standardized hardware generation. They run whatever survived procurement cycles, acquisitions, lab exceptions, executive devices, warehouse machines, and remote-office improvisation. Some machines are new enough to be ready. Some need firmware updates. Some are in closets. Some are powered off for months. Some are “temporary” and have been temporary since 2019.
The machines most likely to surprise administrators are not necessarily the ones on desks. They are loaner pools, kiosk systems, classroom devices, cold spares, offline industrial PCs, test rigs, and virtual machines with Secure Boot enabled but neglected template maintenance. Certificate updates favor devices that are alive, reachable, and allowed to process servicing tasks. Many operational exceptions are none of those things.
There is also the dual-boot and third-party boot loader angle. Secure Boot’s Microsoft UEFI CA has long been important beyond Windows because it underpins trust for many third-party boot components. The 2023 certificate split is cleaner, but it also means environments that depend on non-Windows boot paths should verify behavior rather than assume nothing changes.
This is the part of the story that resists simplification. Microsoft can publish guidance, OEMs can issue firmware, and Windows can run scheduled tasks. But the last mile belongs to the organization that knows which devices actually exist.
That distinction should stop anyone tempted to treat this as a background desktop hygiene project. Server maintenance is slower, more scheduled, more political, and more failure-sensitive. A certificate update that might be routine on a laptop becomes a change ticket when the system hosts domain services, line-of-business applications, virtualization workloads, or regulated data.
The recommended path begins with current cumulative updates, then moves to initiating Secure Boot certificate updates on in-scope servers. That sounds simple until it collides with real maintenance windows, cluster sequencing, backup validation, vendor support matrices, and the ritual question of who owns firmware risk.
Virtualization adds another layer. Secure Boot is common in modern VM configurations, and template images can carry old assumptions forward. If administrators update physical hosts but ignore guest settings, golden images, and dormant VMs, they may end up with a split estate where the compliance dashboard looks better than the actual boot-trust landscape.
Server teams are generally good at fearing change. In this case, Microsoft is asking them to fear delay at least as much.
Windows 10 machines will still exist in large numbers through 2026. Some will be in ESU programs. Some will be unmanaged home PCs. Some will be embedded in business processes no one budgeted to replace. Some will be perfectly capable machines blocked from Windows 11 by CPU, TPM, or organizational policy constraints.
For those systems, the practical message is not “panic.” It is “do not assume old Windows plus old firmware plus old servicing policy will somehow produce modern boot trust.” If a device remains in production, it needs a path to the 2023 certificates or a documented exception that security teams can live with.
This is one of the underappreciated costs of long platform transitions. Hardware, firmware, OS servicing, and compliance clocks do not tick at the same speed. A device can be operationally useful and strategically obsolete at the same time. Secure Boot certificate expiration exposes that contradiction in a place organizations cannot easily paper over.
The irony is sharp. Secure Boot was once one of the requirements that made Windows 11 feel exclusionary to some users. Now the Secure Boot ecosystem itself is forcing a maintenance reckoning across machines old and new.
That ordering is a form of editorial judgment. Microsoft knows most administrators do not read every support article line by line. It also knows that update titles travel through dashboards, RSS feeds, forums, and change logs. By stapling the Secure Boot warning to routine KBs, Microsoft increases the odds that someone in the deployment chain sees the deadline before it becomes an incident.
This is not new behavior. Microsoft has used KB notes for years to carry known issues, compatibility holds, upgrade blockers, servicing stack reminders, and end-of-support warnings. But this case is more consequential because the affected layer is beneath the operating system.
There is a risk, however, that the repetition numbs the audience. When every update note starts carrying a standard warning block, administrators learn to skim past it. The challenge for Microsoft is to repeat the message often enough to drive action without making it feel like boilerplate.
The April 30 timing helps. With June close enough to affect change calendars, the Secure Boot note no longer reads like distant planning advice. It reads like the sort of thing that should already be in a ticket queue.
Microsoft’s own guidance starts with verifying whether Secure Boot is enabled. On a single machine, that can be done through Windows Security, System Information, or PowerShell. Across a fleet, it requires management tooling, compliance scripts, reporting, and enough discipline to chase down the devices that do not answer.
This is a familiar pattern in enterprise IT. The security control is simple in concept and messy in deployment because exceptions multiply. Machines with Secure Boot disabled cannot have active Secure Boot variables updated in the same way. Toggling Secure Boot can reset settings in undesirable ways. Firmware updates may be prerequisites. Dormant systems may miss the rollout entirely.
The uncomfortable truth is that Secure Boot certificate readiness is not one status. It is a chain of statuses. If any link is unknown, the machine belongs in the exception bucket until proven otherwise.
That exception bucket is where work hides. It contains the old laptop assigned to a contractor, the lab machine dual-booting Linux, the VM template nobody owns, the branch-office PC behind a restrictive firewall, and the server that cannot be rebooted until the vendor blesses the next maintenance window.
For IT pros, that slogan is too thin. The certificate rollover is about trust continuity. Windows needs to keep trusting newly signed boot components. Firmware needs to accept the updated databases. The revocation pipeline needs to remain viable. Third-party boot paths need to keep working where they are part of the environment. Compliance teams need evidence, not vibes.
That is why Microsoft’s guidance talks about the KEK, DB, DBX, Platform Key, scheduled tasks, registry targeting, diagnostic data, OEM firmware, and server playbooks. Those details are not bureaucratic garnish. They are the moving parts of the boot-trust system.
The BlackLotus-era lesson hangs over this entire process. Boot-level attacks are rare compared with phishing and commodity malware, but their strategic value is high because they can undermine the operating system before its defenses fully load. Secure Boot does not solve every firmware or boot-chain problem, but an unmaintained Secure Boot trust store solves even less.
The argument for acting early is not that June 2026 will produce universal catastrophe. It is that waiting until after a trust deadline to discover whether your boot chain can still be serviced is operational negligence dressed up as patience.
The work should begin with visibility, not panic. Administrators need to identify which devices have Secure Boot enabled, which are receiving Microsoft-managed updates, which are blocked from diagnostic-data-dependent rollout logic, which need OEM firmware, and which servers require manual handling. That information should then feed deployment rings, not a last-minute all-hands scramble.
For consumers and enthusiasts, the advice is simpler but still meaningful. Keep Windows updated. Install firmware updates from the device manufacturer when they are offered through trusted channels. Check Secure Boot status before June if the machine is old, dual-booted, heavily customized, or has spent long periods offline.
For WindowsForum readers, the interesting part is that this is one of those rare moments when firmware, Windows servicing, and security policy all become visible at once. The update title says Setup Dynamic Update. The real story is the maintenance of trust beneath the installer.
Source: Microsoft Support KB5087583: Setup Dynamic Update for Windows 11, version 24H2 and 25H2: April 30, 2026 - Microsoft Support
 A Small Setup Update Carries a Much Larger Warning
A Small Setup Update Carries a Much Larger Warning
KB5087583 is, on paper, the kind of servicing artifact that usually slips past everyone except deployment engineers. It updates Windows setup binaries and files used during feature updates for Windows 11 24H2 and 25H2. It is available through Windows Update, the Microsoft Update Catalog, and WSUS, requires no restart, and replaces a prior setup dynamic update.That sounds administrative, almost boring. But Microsoft placed a prominent Secure Boot warning at the top of the support article, and that placement matters. The company is no longer treating the 2026 certificate rollover as a niche UEFI footnote. It is attaching the warning to the plumbing of Windows setup itself.
Setup Dynamic Updates exist to make Windows upgrades less brittle. They refresh the components Setup uses before and during an upgrade, helping the installer cope with newer compatibility data, drivers, and servicing changes. When that sort of update carries a Secure Boot warning, Microsoft is effectively telling IT departments that upgrade readiness and boot-chain readiness are now part of the same operational conversation.
The important distinction is that KB5087583 is not, by itself, the universal fix for Secure Boot certificate expiration. It is a setup servicing update with a warning attached. The fix lives in a broader certificate rollout involving Windows updates, firmware readiness, OEM cooperation, registry targeting for managed environments, event monitoring, and in some cases manual action.
That is precisely why the warning deserves attention. If this were just another cumulative update note, administrators could file it under monthly patch hygiene. Instead, Microsoft is trying to surface a quiet infrastructure deadline in every channel it can.
Secure Boot’s 2011 Trust Anchor Is Finally Aging Out
Secure Boot arrived in the Windows ecosystem with Windows 8-era hardware, and for more than a decade most Windows PCs have carried the same Microsoft-provided certificates in firmware. Those certificates form part of the trust chain that allows a system to decide what is permitted to run before Windows itself loads. In normal desktop use, they are invisible; in security architecture, they are foundational.The problem is not that Secure Boot suddenly stops being a good idea in June 2026. The problem is that certificates have lifetimes. Microsoft’s 2011-era Secure Boot certificates begin expiring in June 2026, with the Windows Production PCA 2011 certificate following in October 2026. That schedule turns an abstract certificate lifecycle into a fleet management problem.
Microsoft’s new 2023 certificates are meant to replace the old anchors. The Microsoft Corporation KEK CA 2011 gives way to the Microsoft Corporation KEK 2K CA 2023. The Windows boot loader moves from trust rooted in the Microsoft Windows Production PCA 2011 to the Windows UEFI CA 2023. The older third-party UEFI CA is being split into more granular trust for third-party boot loaders and option ROMs.
That split is more than housekeeping. It lets systems trust third-party boot loaders without necessarily extending the same broad trust to option ROMs, or vice versa. In other words, Microsoft is not merely renewing an expiring card; it is tightening the shape of trust in the firmware era.
For home users, that distinction may feel academic. For administrators, security teams, Linux dual-boot users, virtualization operators, and anyone managing fleets of older hardware, it is not. The firmware trust store is not a web browser certificate store. You do not want to discover during an outage window that the machine’s boot policy and Microsoft’s new signing chain never shook hands.
The Scary Part Is Not Instant Failure
The most important nuance in Microsoft’s guidance is also the easiest one to misread. Devices that fail to receive the new 2023 Secure Boot certificates are not expected to universally brick the moment June arrives. Microsoft says affected systems should continue to start and operate normally, and standard Windows updates should continue to install.That sounds reassuring, and it is — up to a point. The trouble is that “the computer still turns on” is a low bar for security compliance. The deeper consequence is that devices without updated certificates may no longer receive new protections for early boot components, including Secure Boot database updates, revocation updates, boot manager protections, and mitigations for newly discovered boot-level vulnerabilities.
That is the slow-burn risk Microsoft is trying to prevent. Bootkits are dangerous precisely because they operate before the operating system has a chance to defend itself. Once the boot chain is no longer receiving new trust and revocation updates, the system drifts into a degraded security posture even if the desktop looks perfectly healthy.
This is where the messaging gets awkward for Microsoft. Consumers hear “certificate expiration” and worry about a mass boot failure. Enterprises hear “no longer receiving boot-level security protections” and worry about audit exceptions, cyber insurance attestations, and incident response scenarios in which the endpoint agent never had a chance.
Both fears are understandable. But the second one is the more realistic management problem. The June 2026 deadline is not a cinematic cliff where every unpatched PC falls off at once. It is the start of a period in which outdated boot trust becomes an increasingly embarrassing and dangerous exception.
Microsoft Is Making Telemetry Part of the Safety Mechanism
The least comfortable part of Microsoft’s enterprise guidance is its reliance on managed rollout intelligence. Microsoft’s preferred low-effort path is for devices to receive Windows updates from Microsoft and send diagnostic data back. That telemetry helps the company group devices by hardware and firmware profile, monitor results, pause deployment when needed, and resume when the risk looks acceptable.This is sensible engineering. Secure Boot certificate updates touch firmware variables and boot policy, two areas where a bad assumption can produce a very bad day. A staged rollout informed by device health signals is safer than blasting the same change indiscriminately across every machine ever sold since the Windows 8 era.
It is also a governance headache. Some organizations deliberately minimize diagnostic data, route updates through tightly controlled systems, or treat Microsoft-managed rollout behavior as something to be fenced off rather than embraced. For those shops, the “automatic” path becomes less automatic.
Microsoft’s answer is an opt-in mechanism for managed environments, including a registry value under the Secure Boot control path. The company recommends targeting devices so Windows’ scheduled task can process the certificate update bits in order, applying the relevant 2023 certificates and eventually updating the boot manager to one signed by the newer Windows UEFI CA 2023.
That is a reasonable deployment model, but it is not a consumer-grade switch. It demands inventory, targeting, monitoring, and rollback planning. It also makes clear that Secure Boot is no longer a firmware checkbox administrators can safely ignore after imaging day.
The Firmware Layer Gets a Vote
The Windows update stack can carry a great deal, but it cannot magically erase the role of OEM firmware. Microsoft’s guidance repeatedly points administrators back to firmware updates, because the Platform Key at the top of the Secure Boot hierarchy is typically controlled by the OEM or its delegate. If firmware behavior is wrong, stale, or incompatible, Windows can only do so much.This is where fleet reality becomes messy. Enterprises rarely run one perfectly standardized hardware generation. They run whatever survived procurement cycles, acquisitions, lab exceptions, executive devices, warehouse machines, and remote-office improvisation. Some machines are new enough to be ready. Some need firmware updates. Some are in closets. Some are powered off for months. Some are “temporary” and have been temporary since 2019.
The machines most likely to surprise administrators are not necessarily the ones on desks. They are loaner pools, kiosk systems, classroom devices, cold spares, offline industrial PCs, test rigs, and virtual machines with Secure Boot enabled but neglected template maintenance. Certificate updates favor devices that are alive, reachable, and allowed to process servicing tasks. Many operational exceptions are none of those things.
There is also the dual-boot and third-party boot loader angle. Secure Boot’s Microsoft UEFI CA has long been important beyond Windows because it underpins trust for many third-party boot components. The 2023 certificate split is cleaner, but it also means environments that depend on non-Windows boot paths should verify behavior rather than assume nothing changes.
This is the part of the story that resists simplification. Microsoft can publish guidance, OEMs can issue firmware, and Windows can run scheduled tasks. But the last mile belongs to the organization that knows which devices actually exist.
Servers Are Not Just Bigger PCs in This Rollout
Windows Server deserves its own anxiety category. Microsoft has said that server instances do not receive the 2023 Secure Boot certificates through the same Controlled Feature Rollout path as Windows PCs. Administrators managing servers with Secure Boot enabled must take action if those systems did not ship with the new certificates or have not otherwise been updated.That distinction should stop anyone tempted to treat this as a background desktop hygiene project. Server maintenance is slower, more scheduled, more political, and more failure-sensitive. A certificate update that might be routine on a laptop becomes a change ticket when the system hosts domain services, line-of-business applications, virtualization workloads, or regulated data.
The recommended path begins with current cumulative updates, then moves to initiating Secure Boot certificate updates on in-scope servers. That sounds simple until it collides with real maintenance windows, cluster sequencing, backup validation, vendor support matrices, and the ritual question of who owns firmware risk.
Virtualization adds another layer. Secure Boot is common in modern VM configurations, and template images can carry old assumptions forward. If administrators update physical hosts but ignore guest settings, golden images, and dormant VMs, they may end up with a split estate where the compliance dashboard looks better than the actual boot-trust landscape.
Server teams are generally good at fearing change. In this case, Microsoft is asking them to fear delay at least as much.
Windows 10’s Afterlife Makes the Deadline More Awkward
The certificate rollover arrives after Windows 10’s mainstream support story has already become complicated. Microsoft’s guidance focuses support on supported Windows client versions, with Extended Security Updates acting as the bridge for organizations that have not completed migration. That matters because Secure Boot certificate servicing is not just another app patch an administrator can download casually years later.Windows 10 machines will still exist in large numbers through 2026. Some will be in ESU programs. Some will be unmanaged home PCs. Some will be embedded in business processes no one budgeted to replace. Some will be perfectly capable machines blocked from Windows 11 by CPU, TPM, or organizational policy constraints.
For those systems, the practical message is not “panic.” It is “do not assume old Windows plus old firmware plus old servicing policy will somehow produce modern boot trust.” If a device remains in production, it needs a path to the 2023 certificates or a documented exception that security teams can live with.
This is one of the underappreciated costs of long platform transitions. Hardware, firmware, OS servicing, and compliance clocks do not tick at the same speed. A device can be operationally useful and strategically obsolete at the same time. Secure Boot certificate expiration exposes that contradiction in a place organizations cannot easily paper over.
The irony is sharp. Secure Boot was once one of the requirements that made Windows 11 feel exclusionary to some users. Now the Secure Boot ecosystem itself is forcing a maintenance reckoning across machines old and new.
KB5087583 Shows How Microsoft Uses the Update Stack as a Messaging System
The KB5087583 article is short, but its structure is revealing. Microsoft puts the Secure Boot warning before the actual summary of the update. Only after that does it explain that the package improves Windows setup files for 24H2 and 25H2, is automatically available through Windows Update, can be obtained from the Catalog, and syncs into WSUS as a Windows 11 update classification.That ordering is a form of editorial judgment. Microsoft knows most administrators do not read every support article line by line. It also knows that update titles travel through dashboards, RSS feeds, forums, and change logs. By stapling the Secure Boot warning to routine KBs, Microsoft increases the odds that someone in the deployment chain sees the deadline before it becomes an incident.
This is not new behavior. Microsoft has used KB notes for years to carry known issues, compatibility holds, upgrade blockers, servicing stack reminders, and end-of-support warnings. But this case is more consequential because the affected layer is beneath the operating system.
There is a risk, however, that the repetition numbs the audience. When every update note starts carrying a standard warning block, administrators learn to skim past it. The challenge for Microsoft is to repeat the message often enough to drive action without making it feel like boilerplate.
The April 30 timing helps. With June close enough to affect change calendars, the Secure Boot note no longer reads like distant planning advice. It reads like the sort of thing that should already be in a ticket queue.
The Real Inventory Is the One Beneath the Asset Database
Most organizations think they have an asset inventory. Secure Boot certificate rollover will test whether that inventory knows anything useful. Device name, owner, OS version, and serial number are not enough. Administrators need to know Secure Boot state, firmware level, certificate state, update channel, diagnostic data posture, OEM support status, and whether the device is actually checking in.Microsoft’s own guidance starts with verifying whether Secure Boot is enabled. On a single machine, that can be done through Windows Security, System Information, or PowerShell. Across a fleet, it requires management tooling, compliance scripts, reporting, and enough discipline to chase down the devices that do not answer.
This is a familiar pattern in enterprise IT. The security control is simple in concept and messy in deployment because exceptions multiply. Machines with Secure Boot disabled cannot have active Secure Boot variables updated in the same way. Toggling Secure Boot can reset settings in undesirable ways. Firmware updates may be prerequisites. Dormant systems may miss the rollout entirely.
The uncomfortable truth is that Secure Boot certificate readiness is not one status. It is a chain of statuses. If any link is unknown, the machine belongs in the exception bucket until proven otherwise.
That exception bucket is where work hides. It contains the old laptop assigned to a contractor, the lab machine dual-booting Linux, the VM template nobody owns, the branch-office PC behind a restrictive firewall, and the server that cannot be rebooted until the vendor blesses the next maintenance window.
The Certificate Rollover Is a Security Story, Not a Patch Story
It is tempting to reduce the whole thing to “install updates before June.” For many home users on supported Windows builds with Microsoft-managed updates, that may be close enough. Leave Windows Update alone, install OEM firmware when offered, and do not disable Secure Boot for sport.For IT pros, that slogan is too thin. The certificate rollover is about trust continuity. Windows needs to keep trusting newly signed boot components. Firmware needs to accept the updated databases. The revocation pipeline needs to remain viable. Third-party boot paths need to keep working where they are part of the environment. Compliance teams need evidence, not vibes.
That is why Microsoft’s guidance talks about the KEK, DB, DBX, Platform Key, scheduled tasks, registry targeting, diagnostic data, OEM firmware, and server playbooks. Those details are not bureaucratic garnish. They are the moving parts of the boot-trust system.
The BlackLotus-era lesson hangs over this entire process. Boot-level attacks are rare compared with phishing and commodity malware, but their strategic value is high because they can undermine the operating system before its defenses fully load. Secure Boot does not solve every firmware or boot-chain problem, but an unmaintained Secure Boot trust store solves even less.
The argument for acting early is not that June 2026 will produce universal catastrophe. It is that waiting until after a trust deadline to discover whether your boot chain can still be serviced is operational negligence dressed up as patience.
The April 30 Update Leaves Administrators With a Narrower Excuse Window
KB5087583’s practical content is modest. Its broader significance is that Microsoft has now made the Secure Boot deadline part of the routine Windows 11 24H2 and 25H2 servicing drumbeat. If a shop is already handling 24H2 or 25H2 feature-update mechanics, it has no real excuse for treating Secure Boot certificate readiness as a separate future project.The work should begin with visibility, not panic. Administrators need to identify which devices have Secure Boot enabled, which are receiving Microsoft-managed updates, which are blocked from diagnostic-data-dependent rollout logic, which need OEM firmware, and which servers require manual handling. That information should then feed deployment rings, not a last-minute all-hands scramble.
For consumers and enthusiasts, the advice is simpler but still meaningful. Keep Windows updated. Install firmware updates from the device manufacturer when they are offered through trusted channels. Check Secure Boot status before June if the machine is old, dual-booted, heavily customized, or has spent long periods offline.
For WindowsForum readers, the interesting part is that this is one of those rare moments when firmware, Windows servicing, and security policy all become visible at once. The update title says Setup Dynamic Update. The real story is the maintenance of trust beneath the installer.
The June Deadline Has Already Entered the Change Calendar
The useful reading of KB5087583 is not that it demands special emergency treatment on every Windows 11 device. It is that it confirms the Secure Boot certificate rollover has moved from long-range advisory to current operational risk. The concrete next steps are not glamorous, but they are the difference between a managed transition and a messy audit trail.- KB5087583 is a Windows 11 24H2 and 25H2 Setup Dynamic Update released on April 30, 2026, and it improves files used by Windows Setup during feature updates.
- The support article’s prominent Secure Boot warning reflects a broader Microsoft push to prepare devices before 2011-era Secure Boot certificates begin expiring in June 2026.
- Devices that miss the new certificates are not expected to universally stop booting immediately, but they may lose access to future boot-level security protections and revocation updates.
- Windows PCs on supported, Microsoft-managed update paths are the lowest-friction case, while restricted enterprise fleets and Windows Server environments require more deliberate action.
- Administrators should verify Secure Boot state, firmware readiness, certificate deployment status, update management policy, and dormant or offline devices before the June deadline arrives.
Source: Microsoft Support KB5087583: Setup Dynamic Update for Windows 11, version 24H2 and 25H2: April 30, 2026 - Microsoft Support