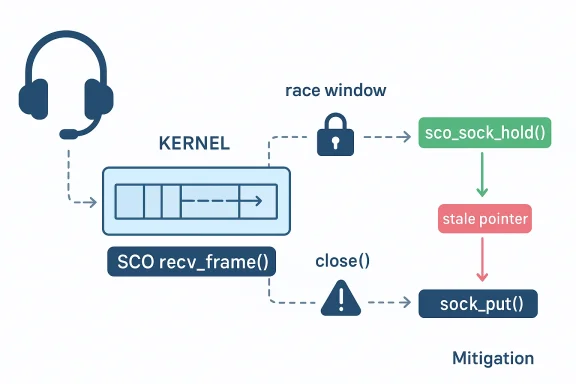
Linux’s Bluetooth stack has a fresh use-after-free flaw, tracked as CVE-2026-31408, and the issue sits in one of the trickier parts of kernel networking: the SCO path that handles synchronous audio traffic. The bug arises in sco_recv_frame(), where the code reads
CVE-2026-31408 is another reminder that Linux kernel security often comes down to reference counting discipline rather than dramatic algorithmic failure. In this case, the Bluetooth SCO implementation briefly exposes a socket pointer after a lock is dropped, which is enough time for another thread to free the underlying object. The resulting race is the classic kernel pattern: a valid pointer becomes stale just after a synchronization boundary, and the next dereference lands on reclaimed memory.
The vulnerable path is not a random corner of the stack. SCO, or Synchronous Connection-Oriented transport, is part of the Bluetooth audio and telephony pipeline, and kernel code in this area has historically required careful coordination between connection lifetime, socket lifetime, and delayed work. The CVE record notes that related functions in the same file already use
The public record shows the CVE was received from kernel.org and published by NVD on April 6, 2026, with the description stating that the issue has been resolved upstream and in stable trees. NVD had not yet assigned a CVSS score at the time of the record’s publication, so the practical security discussion has to focus on impact and exposure rather than a numerical severity label. In kernel security, that is often the right order of operations anyway.
What makes this class of bug interesting is that it is often both easy and hard at the same time: easy to describe in a sentence, hard to eliminate everywhere consistently. Linux kernel maintainers explicitly note that CVEs are commonly assigned after fixes land in stable trees, and that the process is intentionally conservative because many bugfixes could potentially be security relevant. That policy explains why Bluetooth fixes such as this one keep appearing in CVE channels, especially where object lifetime intersects with concurrent teardown.
The bug is especially notable because the file already contains examples of the correct pattern. The CVE description explicitly says
A use-after-free in a networking subsystem is not just a crash risk. Depending on allocator behavior, reuse timing, and surrounding data structures, stale memory reads can become corrupt state transitions or, in more dangerous scenarios, a stepping stone toward code execution. The CVE text does not claim exploitation, and there is no public NVD severity yet, but the class of bug is serious enough that administrators should treat it as security-relevant until patched.
The role of
Kernel socket references are a lifetime contract.
The fact that the patch touches exit paths as well as the acquisition point tells us this was fixed with ordinary kernel hygiene, not a broader architectural rewrite. That is a strength, because it limits the blast radius. It is also a warning, because bugs of this type can exist in more than one code path if the same lifetime assumptions were repeated elsewhere.
The Bluetooth subsystem in Linux has seen repeated memory-safety fixes over the years, including several in neighboring code paths. That history does not imply systemic failure, but it does show that Bluetooth is a complex, stateful subsystem where lifecycle bugs are not unusual. When one area like SCO accumulates multiple fixes over time, it becomes a cue for maintainers and downstream vendors to scrutinize adjacent code for similar patterns.
This also helps explain why the same file’s other functions matter. If
That kind of fix is preferable to broader synchronization changes because it addresses the actual bug with minimal collateral damage. Extending the lock scope would likely serialize more code than necessary and might create new contention or deadlock risks. By contrast, reference counting is local, explicit, and already part of the subsystem’s established patterns.
The CVE record’s added references point to multiple kernel.org stable commits, reinforcing that this is not merely a theoretical cleanup but a bug that has been fixed through the normal Linux security workflow. Kernel documentation notes that CVEs are typically tied to fixes already applied in stable trees, which means distributions are expected to pick up the repair through their usual update channels.
The pattern is familiar: a connection object is established, work is scheduled, a socket is closed, and another thread touches state that should no longer be assumed valid. Earlier Linux Bluetooth CVEs show similar themes, including dangling pointers, delayed work races, and stale references after connection teardown. CVE-2026-31408 fits that lineage almost perfectly, which is why it should be read as part of a broader maintenance story rather than a one-off defect.
In practical terms, this kind of history should encourage defenders to monitor Bluetooth-related advisories closely, especially for systems that expose audio accessories, headsets, telephony integrations, or kiosk-style wireless peripherals. The issue is kernel-local, but the operational surface is broad because Bluetooth is built into so many endpoint workflows. That is what gives these bugs enduring relevance.
A kernel use-after-free is especially relevant in enterprise environments because it can convert a routine peripheral interaction into an instability or privilege risk. Even if exploitation is difficult, the operational downside of a crash in a production laptop or field device can be immediate. Security teams should treat the update as part of their normal kernel hygiene, especially where Bluetooth is needed and cannot simply be disabled.
That also means patch triage should be version-aware. Some systems will receive the fix quickly through enterprise Linux updates, while others may wait on vendor certification or on backports to older maintained branches. The safest posture is to map the advisory to your exact kernel lineage rather than assuming a generic “Linux” label applies equally everywhere.
This is one of those situations where “I only use Bluetooth occasionally” is not a reliable defense. A vulnerability in the kernel’s Bluetooth stack can matter precisely because the stack is part of the operating system, not an optional app. If your device is running a distribution kernel that has not yet absorbed the fix, you should assume the issue remains relevant until updates are applied.
There is also a broader lesson here: kernel vulnerabilities are often invisible until they are not. Consumers generally do not see the lock-and-reference-count machinery underneath their headphones, but they depend on it every time they connect one. That is why kernel security updates deserve the same urgency as browser or firmware updates, even when the headline sounds esoteric. The bug may be deep; the impact is not.
In the near term, administrators should care less about the abstract CVE number and more about whether their kernels have absorbed the fix. In the long term, this issue is another argument for careful code review around object lifetime in Bluetooth and for fast, disciplined backporting when a race is found. The underlying lesson is simple, but it is one kernel developers have to relearn constantly: if a pointer can outlive its lock, it must be held.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
conn->sk while holding sco_conn_lock(), then drops the lock without first taking a socket reference. That opens a race where a concurrent close() can free the socket before sk->sk_state is checked, turning a routine state access into a memory-safety hazard. The fix is conceptually simple but operationally important: use sco_sock_hold() before releasing the lock and pair it with sock_put() on every exit path.
 Overview
Overview
CVE-2026-31408 is another reminder that Linux kernel security often comes down to reference counting discipline rather than dramatic algorithmic failure. In this case, the Bluetooth SCO implementation briefly exposes a socket pointer after a lock is dropped, which is enough time for another thread to free the underlying object. The resulting race is the classic kernel pattern: a valid pointer becomes stale just after a synchronization boundary, and the next dereference lands on reclaimed memory.The vulnerable path is not a random corner of the stack. SCO, or Synchronous Connection-Oriented transport, is part of the Bluetooth audio and telephony pipeline, and kernel code in this area has historically required careful coordination between connection lifetime, socket lifetime, and delayed work. The CVE record notes that related functions in the same file already use
sco_sock_hold() correctly, which means the bug is less about missing architecture and more about an inconsistent implementation in one function. That is exactly the kind of issue that tends to survive code review until a race makes it obvious.The public record shows the CVE was received from kernel.org and published by NVD on April 6, 2026, with the description stating that the issue has been resolved upstream and in stable trees. NVD had not yet assigned a CVSS score at the time of the record’s publication, so the practical security discussion has to focus on impact and exposure rather than a numerical severity label. In kernel security, that is often the right order of operations anyway.
What makes this class of bug interesting is that it is often both easy and hard at the same time: easy to describe in a sentence, hard to eliminate everywhere consistently. Linux kernel maintainers explicitly note that CVEs are commonly assigned after fixes land in stable trees, and that the process is intentionally conservative because many bugfixes could potentially be security relevant. That policy explains why Bluetooth fixes such as this one keep appearing in CVE channels, especially where object lifetime intersects with concurrent teardown.
What CVE-2026-31408 Actually Breaks
At the center of the vulnerability is a race between frame reception and socket teardown.sco_recv_frame() consults conn->sk under sco_conn_lock(), but once the lock is released, the code no longer has a guarantee that the socket remains alive. If another thread closes the socket in that gap, the subsequent access to sk->sk_state can dereference freed memory. That is a textbook use-after-free, and in kernel space even a “small” race like this can have outsized consequences.The bug is especially notable because the file already contains examples of the correct pattern. The CVE description explicitly says
sco_sock_timeout() and sco_conn_del() use sco_sock_hold() under the lock, which pins the object until later cleanup. That contrast matters: it suggests the fix was not inventing a new lifetime model, but applying the existing one consistently to a missed code path.Why the race matters
In kernel code, a lock protects the contents of a critical section, but it does not automatically extend object lifetime past that section. If a function caches a pointer and then drops the lock, it must usually take an explicit reference before doing anything else. Otherwise, teardown code can win the race and free the object. The moment the pointer’s lifetime and the lock’s scope diverge, you get the kind of bug thatsock_hold() and sock_put() are designed to prevent.A use-after-free in a networking subsystem is not just a crash risk. Depending on allocator behavior, reuse timing, and surrounding data structures, stale memory reads can become corrupt state transitions or, in more dangerous scenarios, a stepping stone toward code execution. The CVE text does not claim exploitation, and there is no public NVD severity yet, but the class of bug is serious enough that administrators should treat it as security-relevant until patched.
- The vulnerable window opens after
sco_conn_lock()is dropped. - A concurrent
close()can free the socket during that gap. - The next state check reads memory that may already be reclaimed.
- The correct pattern is to take a reference first, then unlock.
sock_put()must be paired with every successful hold.
The role of sock_hold() and sock_put()
Kernel socket references are a lifetime contract. sco_sock_hold() increments the reference count so the socket cannot disappear while a caller still depends on it, and sock_put() releases that claim when the caller is done. The CVE record says the patch adds sock_put() on all exit paths, which is an important detail because partial cleanup is often where reference leaks or latent lifetime bugs are born.The fact that the patch touches exit paths as well as the acquisition point tells us this was fixed with ordinary kernel hygiene, not a broader architectural rewrite. That is a strength, because it limits the blast radius. It is also a warning, because bugs of this type can exist in more than one code path if the same lifetime assumptions were repeated elsewhere.
Why Bluetooth SCO Is a Special Case
Bluetooth SCO is not just another packet path; it is tied to real-time audio and voice use cases, which tend to be timing-sensitive and concurrency-heavy. Kernel code handling synchronous audio often has to manage active connections, disconnect events, and delayed work while preserving stable behavior for user space. That creates exactly the kind of environment where object lifetime mistakes can hide in plain sight.The Bluetooth subsystem in Linux has seen repeated memory-safety fixes over the years, including several in neighboring code paths. That history does not imply systemic failure, but it does show that Bluetooth is a complex, stateful subsystem where lifecycle bugs are not unusual. When one area like SCO accumulates multiple fixes over time, it becomes a cue for maintainers and downstream vendors to scrutinize adjacent code for similar patterns.
How SCO differs from simple socket code
SCO traffic is tied to connection semantics that can change quickly and asynchronously. A socket may be live from the perspective of one worker while already in teardown from the perspective of another thread. That makes a short-lived pointer cache far more dangerous than it would be in a single-threaded or purely synchronous path. That is the heart of the bug.This also helps explain why the same file’s other functions matter. If
sco_sock_timeout() and sco_conn_del() already needed explicit holds, then the design assumption is clear: socket access in this subsystem must be guarded by both locking and reference counting. A function that skips one half of that bargain is effectively an outlier, and outliers are where races become security issues.- SCO is timing-sensitive and connection-oriented.
- Teardown can happen concurrently with frame processing.
- Locks alone do not preserve object lifetime after unlock.
- Reference counting is the intended defense.
- The bug is consistent with a broader kernel class of lifetime errors.
The Fix and Why It Is the Right One
The published description is refreshingly direct: take a socket reference withsco_sock_hold() before dropping sco_conn_lock(), and add sock_put() on all exit paths. This is the canonical kernel answer to a reference lifetime race. It preserves the object long enough for the post-lock state access, then releases it predictably once the function is finished.That kind of fix is preferable to broader synchronization changes because it addresses the actual bug with minimal collateral damage. Extending the lock scope would likely serialize more code than necessary and might create new contention or deadlock risks. By contrast, reference counting is local, explicit, and already part of the subsystem’s established patterns.
Why the patch is low-risk but high-value
A good kernel security fix often looks boring. That is a compliment. The best patches are the ones that make the object lifetime unambiguous without changing how the subsystem behaves under normal conditions. In this case, the code becomes safer while remaining faithful to the existing design, which is exactly what downstream maintainers want in a stable-tree backport.The CVE record’s added references point to multiple kernel.org stable commits, reinforcing that this is not merely a theoretical cleanup but a bug that has been fixed through the normal Linux security workflow. Kernel documentation notes that CVEs are typically tied to fixes already applied in stable trees, which means distributions are expected to pick up the repair through their usual update channels.
- The patch follows standard socket lifetime rules.
- It avoids widening the locking scope.
- It aligns
sco_recv_frame()with sibling functions. - It is suitable for stable backporting.
- It reduces the chance of future refcount regressions in the same path.
Sequential logic of the repaired path
- Acquire
sco_conn_lock(). - Grab a reference with
sco_sock_hold(). - Release the lock.
- Safely inspect
sk->sk_state. - Call
sock_put()on every return path.
Historical Context: Another Entry in a Long Bluetooth Pattern
CVE-2026-31408 does not arrive in isolation. Linux Bluetooth has repeatedly produced memory-safety advisories over the past several years, including use-after-free and dangling-pointer bugs in related subsystems such as SCO, RFCOMM, HCI, and VHCI. That matters because it shows the blast radius is not one function, but a family of concurrency-sensitive paths where connection teardown and asynchronous work interact.The pattern is familiar: a connection object is established, work is scheduled, a socket is closed, and another thread touches state that should no longer be assumed valid. Earlier Linux Bluetooth CVEs show similar themes, including dangling pointers, delayed work races, and stale references after connection teardown. CVE-2026-31408 fits that lineage almost perfectly, which is why it should be read as part of a broader maintenance story rather than a one-off defect.
What this says about subsystem maturity
This is not evidence that Bluetooth in Linux is uniquely broken. It is evidence that complex kernel subsystems mature by iterating through edge cases, and edge cases in concurrency are notoriously hard to see until real-world stress or fuzzing exposes them. The Linux security process is built around exactly that reality, with fixes flowing into stable trees once the danger is understood.In practical terms, this kind of history should encourage defenders to monitor Bluetooth-related advisories closely, especially for systems that expose audio accessories, headsets, telephony integrations, or kiosk-style wireless peripherals. The issue is kernel-local, but the operational surface is broad because Bluetooth is built into so many endpoint workflows. That is what gives these bugs enduring relevance.
Enterprise Impact: Why Administrators Should Care
For enterprises, the first question is not whether an attacker has a glamorous exploit chain. It is whether a vulnerable kernel path is reachable on endpoints that routinely use Bluetooth peripherals. Laptops, conference-room systems, retail terminals, and mobile workstations often keep Bluetooth enabled for legitimate business reasons, which means the exposure window can be wider than teams assume.A kernel use-after-free is especially relevant in enterprise environments because it can convert a routine peripheral interaction into an instability or privilege risk. Even if exploitation is difficult, the operational downside of a crash in a production laptop or field device can be immediate. Security teams should treat the update as part of their normal kernel hygiene, especially where Bluetooth is needed and cannot simply be disabled.
Fleet management considerations
Enterprises rarely run mainline kernel trees. Instead, they depend on distribution kernels and vendor backports, which makes the practical question “Has my vendor shipped the fix?” more important than “Has upstream merged it?” Linux kernel documentation notes that downstream distributions often need to carry fixes into supported versions, and that CVEs are assigned after fixes exist in stable trees. In other words, patch availability in your vendor channel is the gating factor.That also means patch triage should be version-aware. Some systems will receive the fix quickly through enterprise Linux updates, while others may wait on vendor certification or on backports to older maintained branches. The safest posture is to map the advisory to your exact kernel lineage rather than assuming a generic “Linux” label applies equally everywhere.
- Validate whether Bluetooth is enabled on affected endpoints.
- Check the vendor kernel changelog for the SCO fix.
- Prioritize laptops and voice-capable endpoints first.
- Coordinate with endpoint management for staged rollout.
- Document whether any kiosk or field system uses SCO audio devices.
Consumer Impact: What Home Users Need to Know
For consumers, the practical risk is usually narrower but still real. If a laptop or desktop has Bluetooth enabled and uses headsets, earbuds, or telephony devices, it may touch the affected code path during ordinary use. The good news is that most consumers receive kernel fixes through distro updates without needing to understand the underlying bug. The bad news is that those updates are only protective once installed.This is one of those situations where “I only use Bluetooth occasionally” is not a reliable defense. A vulnerability in the kernel’s Bluetooth stack can matter precisely because the stack is part of the operating system, not an optional app. If your device is running a distribution kernel that has not yet absorbed the fix, you should assume the issue remains relevant until updates are applied.
Practical user guidance
Most users do not need to disable Bluetooth preemptively unless they are waiting on a vendor patch and have a specific exposure concern. However, checking for updates and rebooting after a kernel update remains the right move. If your distribution ships security bulletins separately, it is worth watching for language that references the SCO use-after-free or the affected commit lineage.There is also a broader lesson here: kernel vulnerabilities are often invisible until they are not. Consumers generally do not see the lock-and-reference-count machinery underneath their headphones, but they depend on it every time they connect one. That is why kernel security updates deserve the same urgency as browser or firmware updates, even when the headline sounds esoteric. The bug may be deep; the impact is not.
- Install vendor kernel updates promptly.
- Reboot after patching so the new kernel is active.
- Keep Bluetooth enabled only if you need it.
- Watch distro security advisories for Bluetooth fixes.
- Do not assume “low complexity” means “low importance.”
Strengths and Opportunities
The upside of a fix like this is that it is precise, consistent with existing code patterns, and easy for downstream vendors to backport. It also improves the maintainability of the SCO path by making the lifetime contract explicit instead of implicit. More broadly, it gives the kernel community another chance to audit related Bluetooth code for the same reference-counting mistake.- The patch is surgical and low-risk.
- It reinforces an existing kernel lifetime pattern.
- It likely backports cleanly to stable branches.
- It reduces the chance of adjacent races in the same file.
- It improves code readability for maintainers.
- It can be used as a review template for similar fixes elsewhere.
- It strengthens confidence in the Bluetooth subsystem’s defensive discipline.
Risks and Concerns
The main concern is not just the bug itself, but how easy it is to underestimate a kernel race that looks small on paper. If vendors delay backports, endpoints that depend on Bluetooth can remain exposed longer than expected. Another concern is that similar lifetime mistakes may exist in nearby code, especially where socket pointers are accessed after lock release.- The issue is a kernel memory-safety flaw, not a user-space bug.
- Exploitation impact can be difficult to model without a CVSS score.
- Distribution backports may lag behind upstream fixes.
- Bluetooth-heavy fleets may have many affected endpoints.
- Similar lifetime assumptions may exist in related SCO code.
- End users may not realize they are vulnerable until updates are installed.
- Crash-only outcomes can still create serious operational disruption.
What to Watch Next
The next phase is mostly about propagation, not discovery. Watch for downstream kernel advisories that reference the SCO use-after-free, and for distribution changelogs that map to the stable commits listed in the CVE record. It will also be worth watching whether any vendors bundle this fix with additional Bluetooth hardening, because subsystem fixes often arrive in clusters.Key items to monitor
- Vendor kernel advisories mentioning Bluetooth: SCO or sco_recv_frame().
- Backport notices in enterprise Linux security channels.
- Any follow-on fixes in adjacent Bluetooth connection-management code.
- Updated NVD enrichment once a CVSS score is assigned.
- Related Bluetooth CVEs that point to similar lifetime bugs.
sock_hold() can become a security event.In the near term, administrators should care less about the abstract CVE number and more about whether their kernels have absorbed the fix. In the long term, this issue is another argument for careful code review around object lifetime in Bluetooth and for fast, disciplined backporting when a race is found. The underlying lesson is simple, but it is one kernel developers have to relearn constantly: if a pointer can outlive its lock, it must be held.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
Last edited: