A subtle memory-management timing bug in the Linux kernel has been documented as CVE-2023-52576: an instance where IMA’s kexec cleanup code frees memblock-managed memory after the memblock allocator has already been torn down, producing a use‑after‑free that can lead to kernel instability and denial‑of‑service. The upstream remedy is simple in code — switch the free to memblock_free_late() — but the implications for operators, embedded developers, and cloud platform maintainers are broader: kernel bugs that only show up in late‑boot or teardown paths are easy to overlook, can crash otherwise healthy systems under certain debug configurations, and require disciplined patching and validation to close safely.
The affected code paths live at the intersection of three kernel subsystems:
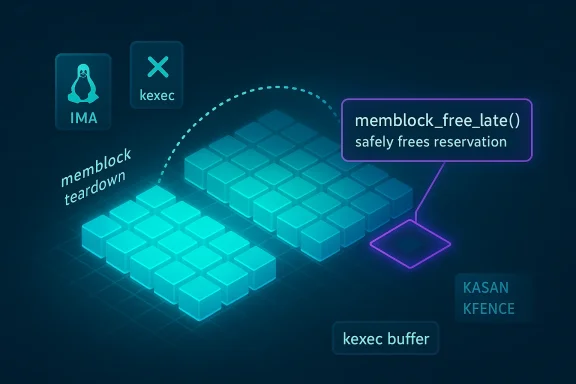
The reported defect is a timing/ordering error in ima_free_kexec_buffer(): the function was freeing memblock-managed memory in a context that can run after memblock has been torn down, which leaves memblock_isolate_range() operating on already‑freed structures — a classic use‑after‑free. With debugging hooks such as KASAN or KFENCE enabled, that use‑after‑free triggers an explicit BUG() in the idle task, causing a kernel panic. Even outside KASAN/KFENCE builds, the incorrect ordering can result in unpredictable behavior or panics under certain conditions.
At the code level the upstream fix is to switch calls to memblock_free_late(), which is intended specifically for freeing memblock reservations at a later point in the boot/shutdown lifecycle and avoids touching torn‑down memblock internals.
For organizations building kernels from upstream or maintaining a longterm-support custom tree, the change can be cherry‑picked or backported safely to the affected branches, followed by a rebuild and validation.
Operational lessons:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The affected code paths live at the intersection of three kernel subsystems:- the x86 memory-management layer (mm),
- kexec (the kernel feature that loads and boots another kernel from a running kernel), and
- IMA (Integrity Measurement Architecture), which interacts with device tree and memblock during kernel setup and kexec image preparation.
The reported defect is a timing/ordering error in ima_free_kexec_buffer(): the function was freeing memblock-managed memory in a context that can run after memblock has been torn down, which leaves memblock_isolate_range() operating on already‑freed structures — a classic use‑after‑free. With debugging hooks such as KASAN or KFENCE enabled, that use‑after‑free triggers an explicit BUG() in the idle task, causing a kernel panic. Even outside KASAN/KFENCE builds, the incorrect ordering can result in unpredictable behavior or panics under certain conditions.
At the code level the upstream fix is to switch calls to memblock_free_late(), which is intended specifically for freeing memblock reservations at a later point in the boot/shutdown lifecycle and avoids touching torn‑down memblock internals.
Why this matters: availability, not escalation
This is primarily an availability problem, not an elevation or data‑integrity issue. The bug results in:- a use‑after‑free in memblock_isolate_range(), and
- under sanitizers (KASAN/KFENCE) a reproducible BUG/panic from the idle task.
- Local actors (unprivileged or low‑privileged) with the ability to trigger the vulnerable code path can cause a kernel panic or sustained denial‑of‑service.
- In testing/CI environments where sanitizers are enabled, the issue is very obvious and deterministic. In production kernels without sanitizers, exploitation requires hitting the specific timing/ordering conditions; it is less deterministic but still capable of producing system crashes or instability.
- There is no credible evidence that this defect allows privilege escalation or secrets disclosure; the impact is crash/DoS-focused.
Technical deep dive: what goes wrong and why memblock_free_late fixes it
memblock lifecycle and early boot
- Memblock manages the early physical memory map before the page allocator exists.
- Many components reserve or modify memblock ranges during init; later, memblock is torn down (migrated) when the kernel hands memory control to the regular allocator.
- Functions that touch memblock must respect that lifecycle; touching memblock internals after teardown risks operating on freed or migrated structures.
The faulty path
- IMA maintains a kexec buffer/structure used during kexec preparation and cleanup.
- ima_free_kexec_buffer() is invoked in a path that, on some kernels or in some sequences, runs after memblock teardown.
- When that happens, the function calls into memblock routines that expect memblock to be live. Because memblock is already torn down, those routines can dereference freed structures — the classic use-after-free.
Why KASAN/KFENCE make this noisier
- KASAN (Kernel Address Sanitizer) and KFENCE are runtime sanitizers that detect invalid memory accesses, including use-after-free.
- When the use‑after‑free occurs under these sanitizers, it is quickly detected and turned into a BUG() — typically from the idle task — which produces an obvious panic and stack trace.
- This makes debugging trivial in sanitized builds but also highlights the defect’s severity: even if it only shows under special builds, the logic is simply incorrect and unsafe.
The proper remedial action: memblock_free_late()
- memblock_free_late() was designed for precisely this category of callers: free or adjust memblock reservations in a way that’s safe when invoked later in the kernel’s lifecycle.
- Replacing the direct free calls with memblock_free_late() avoids touching torn-down memblock internals and thus removes the use-after-free window.
- The change is small, surgical, and low-risk from a correctness perspective; it changes the timing semantics of the free operation to match caller expectations.
Who’s affected and how to assess exposure
Affected systems include kernels that:- contain the vulnerable commit (i.e., the pre‑fix kernel trees and distribution kernels that did not yet include the memblock_free_late change),
- run on x86 (the CVE description references x86/mm),
- have kexec and/or IMA involved in workflows (even if only for some build/boot paths),
- and systems where local users or processes can exercise the kexec/IMA cleanup path.
- Check the running kernel version:
- Run uname -a or cat /proc/version to capture the exact kernel release.
- Compare the version against your vendor’s security advisories or the kernel stable release notes that mention the fix.
- Search distribution changelogs for the presence of the commit message “mm, ima, kexec: use memblock_free_late from ima_free_kexec_buffer” or similar lines.
- Identify systems that permit local, untrusted users to execute workflows that touch kexec or IMA functionality — these are higher risk.
Detection and forensics: what to look for in logs
When this bug triggers a crash, logs and traces have tell‑tale signs:- KASAN or KFENCE messages in dmesg/syslog showing a use-after-free report referencing memblock_isolate_range or memblock internals.
- A BUG or panic trace coming from the idle task; on sanitized kernels, the panic commonly occurs in the idle context with a KASAN report preceding it.
- Generic kernel panic stack traces that include IMA or kexec functions and memblock helpers.
- If you have kernel crash dump collection (kdump, crash utility), collect the vmcore for offline analysis; the backtrace should show ima_free_kexec_buffer calling into memblock routines.
- dmesg | sed -n '1,200p' — look for KASAN/KFENCE or BUG messages.
- journalctl -k --since "1 hour ago" — to gather kernel logs around the crash time.
- If you reproduce the condition on a test host, enable KASAN/KFENCE in a controlled build to obtain a clean, annotated stack trace.
Mitigation and remediation: immediate and medium-term steps
Short‑term, if you cannot patch immediately:- Reduce attacker surface: restrict untrusted local users (remove shell access, limit build/test accounts) on systems where local access is possible.
- Restrict execution of kexec where feasible: many systems do not use kexec in production; disable it if you can. This typically requires changing kernel config or ensuring that the kexec tools and modules are not available and rebooting.
- Limit IMA usage if your operational model permits: IMA is valuable for integrity measurement, but if not needed, consider disabling it until patches can be applied. Note: disabling IMA may require kernel config changes and reboots and can have policy/attestation implications.
- Patch the kernel:
- Apply vendor-supplied kernel updates. Most distributions rolled the fix into their stable kernels; install the updated kernel package and schedule a controlled reboot.
- For vendors or operators who build custom kernels:
- Backport or apply the upstream commit that replaces the free with memblock_free_late() in ima_free_kexec_buffer and rebuild.
- Test in a staging environment (preferably with KASAN/KFENCE enabled for validation) before rolling to production.
- Validate after patching:
- Re-run crash reproducer tests if you had a test case.
- Monitor kernels for absence of KASAN/KFENCE warnings and for reduced incidence of related panics.
Patch management and testing recommendations
- Treat this as an operational kernel update, not a trivial maintenance patch:
- Kernel updates can impact drivers, third-party modules, and platform-specific integrations.
- Use staged rollouts: test → canary → production.
- Use sanitizer-enabled testing in CI:
- If you maintain a kernel test fleet or CI loop, enable KASAN/KFENCE on a test kernel build to detect regression and ensure the free ordering is correct.
- Sanitizers make these defects deterministic and quickly reveal any lingering use-after-free errors.
- Validate modules and out-of-tree drivers:
- Rebuild DKMS or third-party kernel modules against the new kernel; test module loads and expected behavior.
- Monitor for modpost warnings or section mismatch messages when building modules that reference .init or late teardown sections (the memblock_free_late change surfaced similar warnings in some distributions’ build logs).
- Consider automated log monitoring:
- Add detectors for KASAN/KFENCE output patterns, memblock_isolate_range, or BUGs from the idle task to your centralized logging and alerting system.
Risk assessment for different environments
- Development and CI: high risk of immediate detection because sanitizers are commonly used in these environments. Expect rapid panics in unpatched test builds.
- Production servers not using sanitizers: moderate risk — exploitability is less trivial but still possible; if local untrusted users are present, risk increases.
- Cloud providers and multi-tenant hosts: elevated concern — local-tenant actions in multi-user environments can potentially trigger local kernel paths. Providers should prioritize kernel updates and coordinate with tenant maintenance windows.
- Embedded devices and appliances with infrequent updates: high operational risk if the vendor firmware/kernel is not patched, especially for devices that offer limited remote management and cannot be easily updated.
Practical remediation checklist (step-by-step)
- Inventory
- 1.1. Run uname -r and capture kernel versions for all hosts.
- 1.2. Query your OS vendor security bulletin database for CVE-2023-52576 coverage.
- Prioritize
- 2.1. Prioritize systems that:
- Allow untrusted local access,
- Run kexec/IMA paths,
- Participate in critical service roles where reboots are disruptive.
- Patch
- 3.1. Apply vendor kernel updates that include the memblock_free_late fix.
- 3.2. For self-built kernels, apply the upstream patch and rebuild.
- Verify
- 4.1. Boot patched kernels on test hosts with KASAN/KFENCE enabled where possible.
- 4.2. Monitor dmesg and kernel logs for related warnings.
- Roll out
- 5.1. Stage updates: test → canary → group → full fleet.
- 5.2. Coordinate reboots to preserve service availability.
- Post‑deployment monitoring
- 6.1. Alert on panics, KASAN/KFENCE messages, and memblock-related BUGs.
- 6.2. Confirm incident-free operation for a reasonable observation window.
Vendor responses and patches
The fix is small and was picked up in multiple stable kernel trees and distribution kernels. Vendors and distribution maintainers have released updated kernel packages incorporating the memblock_free_late change. If you run a vendor kernel (Ubuntu, Debian, SUSE, Red Hat derivatives, or commercial kernels), consult the vendor advisory and apply the published kernel package; those advisories typically reference the fix and the affected kernel branches.For organizations building kernels from upstream or maintaining a longterm-support custom tree, the change can be cherry‑picked or backported safely to the affected branches, followed by a rebuild and validation.
Why surgical kernel fixes like this matter in the long run
This CVE is a textbook example of where small lifecycle semantics — “when should we free this memblock reservation?” — matter enormously. The fix is tiny but essential: the right function with the right timing semantics. Left unfixed, the code may lie dormant for years and only surface under a specific sequence of late teardown operations or under sanitized builds, making detection and root cause analysis difficult.Operational lessons:
- Early-boot allocators and teardown helpers carry strong invariants; any code that touches those must be explicit about ordering.
- Sanitizers (KASAN/KFENCE) are powerful not just for development but for validating correctness before wide rollout.
- Kernel changes with seemingly low functional impact can still cause availability loss; treat kernel security patches as first-class operations.
Final assessment and recommendations
- Severity and impact: CVE-2023-52576 is a medium (availability-focused) vulnerability: it causes use-after-free in memblock paths and can produce kernel panics under sanitizer configurations or particular runtime sequences.
- Likelihood of exploitation: the defect requires local conditions and careful timing; it's not an easy remote exploit. However, an attacker with local access can provoke crashes. Multi‑tenant hosts and systems that permit less‑trusted users are at greater risk.
- What to do now:
- Identify kernels in your fleet and verify whether vendor updates are available that include the memblock_free_late fix.
- If a vendor patch is available, schedule and apply it with controlled reboots; validate on staging/canary hosts first.
- For systems where immediate patching is impossible, reduce local attack surface, disable or restrict kexec/IMA where feasible, and monitor kernel logs for memblock/KASAN/KFENCE symptoms.
- Use sanitizer-enabled testing in your CI to catch similar lifecycle errors early in development.
Source: MSRC Security Update Guide - Microsoft Security Response Center