A subtle race in the Linux kernel’s Unix-domain socket garbage collector can let the kernel free socket buffers (skbs) while another path still holds a pointer to them, producing a classic use‑after‑free (UAF) that can crash or destabilize systems and — in theory — open the door to more serious memory‑corruption outcomes; this flaw is tracked as CVE‑2023‑6531 and was publicly recorded on January 21, 2024.
Unix domain sockets (AF_UNIX) are a foundational IPC mechanism on Unix and Linux systems. They support passing file descriptors between processes via SCM_RIGHTS messages; that mechanism is implemented using socket buffers (struct sk_buff or skb) that carry an array of file-pointer structures until the recipient consumes the message. The kernel must manage those inflight file references carefully — when sockets are closed without consuming their SCM_RIGHTS payloads, the kernel’s unix garbage collector (unix_gc) walks the graph of sockets and file objects and reclaims anything that’s unreachable from user space. That reclamation is necessary but delicate: the GC touches skbs that may also be observed by ordinary socket read code, and any mismatch between the GC’s locking and the reader’s locking can produce races.
CVE‑2023‑6531 arises in exactly that intersection: the GC’s deletion of an skb can race with the AF_UNIX receive path — specifically unix_stream_read_generic() — which can temporarily hold a pointer into a receive queue. If the GC removes and frees the skb while the reader still intends to touch it, the kernel dereferences freed memory — a use‑after‑free — with the broad consequence set that memory‑safety violations in the kernel imply: kernel panics (denial of service), kernel memory corruption, and, in some scenarios, potential privilege escalation or arbitrary code execution. Multiple distributors and vulnerability databases assigned a CVSS score of 7.0 (High) to this issue and flagged it as a local, high‑impact race bug.
Key implementation facts that make this subtle:
Kernel mailing‑list discussion and patch threads for the unix_gc problems are available in the upstream archives and were referenced by vendor advisories; those threads document design choices and the reasoning behind the chosen fixes. In practice the fixes are narrowly targeted: they do not remove SCM_RIGHTS or the garbage collection idea, but they adjust lock sequences and the GC’s scanning logic to avoid freeing skbs that can still be referenced by readers.
Important cautions:
For deeper technical reading and to verify the exact fix and the backport status for your distribution, consult your vendor’s security advisory and the upstream kernel patch materials referenced by the advisories; public writeups from kernel developers and distribution security teams also provide a useful explanation of the locking mismatch and the rationale for the chosen remediation.
CVE‑2023‑6531 demonstrates how compact, well‑intentioned kernel subsystems (UNIX‑domain socket GC and fast async I/O integrations) can interact in unexpected ways and produce critical operational consequences; the remedy is straightforward in theory (apply the fix), but practical mitigation requires disciplined patch management, sensible temporary controls, and careful monitoring while upgrades are rolled out.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Unix domain sockets (AF_UNIX) are a foundational IPC mechanism on Unix and Linux systems. They support passing file descriptors between processes via SCM_RIGHTS messages; that mechanism is implemented using socket buffers (struct sk_buff or skb) that carry an array of file-pointer structures until the recipient consumes the message. The kernel must manage those inflight file references carefully — when sockets are closed without consuming their SCM_RIGHTS payloads, the kernel’s unix garbage collector (unix_gc) walks the graph of sockets and file objects and reclaims anything that’s unreachable from user space. That reclamation is necessary but delicate: the GC touches skbs that may also be observed by ordinary socket read code, and any mismatch between the GC’s locking and the reader’s locking can produce races.CVE‑2023‑6531 arises in exactly that intersection: the GC’s deletion of an skb can race with the AF_UNIX receive path — specifically unix_stream_read_generic() — which can temporarily hold a pointer into a receive queue. If the GC removes and frees the skb while the reader still intends to touch it, the kernel dereferences freed memory — a use‑after‑free — with the broad consequence set that memory‑safety violations in the kernel imply: kernel panics (denial of service), kernel memory corruption, and, in some scenarios, potential privilege escalation or arbitrary code execution. Multiple distributors and vulnerability databases assigned a CVSS score of 7.0 (High) to this issue and flagged it as a local, high‑impact race bug.
What exactly goes wrong — a technical deep dive
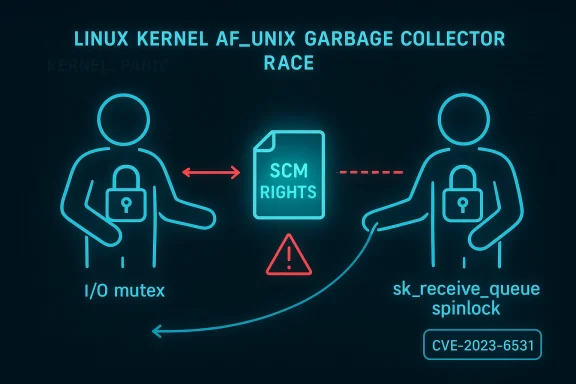
To understand the vulnerability we need to look at two interacting code paths and their locking assumptions:- unix_stream_read_generic(): invoked when a process reads from an AF_UNIX stream socket. That code takes a per‑socket mutex (typically expressed as u->iolock) to protect some high‑level socket state while it walks the socket’s sk_receive_queue and holds a pointer to the skb currently being processed.
- unix_gc / scan_inflight(): the unix garbage collector scans sockets that have been flagged as inflight (sockets that are holding SCM_RIGHTS file objects that might have become unreachable). scan_inflight() iterates the sk_receive_queue and may steal skbs or otherwise mutate the queue; the function uses the socket receive‑queue spinlock (sk->sk_receive_queue.lock) rather than the unix socket’s I/O mutex.
Key implementation facts that make this subtle:
- skbs carry the SCM_RIGHTS file‑pointer array that the GC inspects and uses to decrement inflight counts; those arrays tie file objects to the skb lifetime.
- The GC is invoked as part of socket teardown and cycle detection; GC activity therefore can run concurrently with normal I/O on other sockets in the cycle.
- The reader path’s mutex prevents other operations that take the same mutex, but it does not prevent code paths that take the receive‑queue spinlock directly — and the GC uses that spinlock for queue manipulation.
How the vulnerability was disclosed and patched
The issue was publicly recorded in January 2024 and assigned CVE‑2023‑6531; upstream kernel maintainers and distributions issued patches and advisories through the normal channels. The upstream kernel fixes — packaged into the 6.7 development cycle and picked up into stable backports by many distributors — aim to close the race by removing the dangerous interleavings (either tightening the locking or changing the GC path so it cannot free skbs while readers hold pointers to them). Vendors including Red Hat, Ubuntu, Oracle Linux and cloud distributions published advisories and backports for their supported kernels.Kernel mailing‑list discussion and patch threads for the unix_gc problems are available in the upstream archives and were referenced by vendor advisories; those threads document design choices and the reasoning behind the chosen fixes. In practice the fixes are narrowly targeted: they do not remove SCM_RIGHTS or the garbage collection idea, but they adjust lock sequences and the GC’s scanning logic to avoid freeing skbs that can still be referenced by readers.
Who and what is affected
- Affected components: the Linux kernel networking code for AF_UNIX and the unix garbage collector; affected upstream kernel versions are those prior to the fix merged around the 6.7 cycle. Vendor kernel packages were updated with distribution‑specific fixes and backports.
- Attack vector: local. Exploitation requires the ability to create, manipulate, and close AF_UNIX sockets and to deliver carefully crafted SCM_RIGHTS traffic and timing — i.e., a local user or process. The CVSS vector reflects this: AV:L (Local), PR:L (Low privileges required), AC:H (High complexity).
- Real‑world impact: the most immediate and reproducible impact is availability — kernel crashes or panics that cause denial of service. Security vendors and distro advisories also warn that memory‑corruption bugs in the kernel could be leveraged for privilege escalation in certain configurations, although demonstrating a reliable privilege‑escalation exploit often requires extra conditions and is nontrivial. Treat availability impact as the operational priority; treat possible elevation as an elevated but lower‑probability follow‑on risk.
Reproducer and exploitation notes (what researchers reported)
Public technical reports and security databases summarize the bug and show straightforward reproducer patterns: create AF_UNIX socket pairs, pass file descriptors across sockets repeatedly while closing peers so the GC marks sockets as inflight, then exercise io_uring or other code paths that hold references to file objects that the GC may reclaim. The exact sequences are timing‑sensitive; reproductions in the wild used syzbot/automated fuzzers and dedicated small programs to force the GC to operate concurrently with readers. Those reproduction artifacts were used by maintainers and distributors to validate fixes.Important cautions:
- The exploit scenarios and public reproducers show reliable kernel crashes; public materials do not show a widely reliable, universal privilege escalation exploit chain for CVE‑2023‑6531 (the realistic immediate threat is DoS/instability). However, kernel memory‑safety bugs can be pivot points, so defenders should not dismiss privilege‑escalation pathways without careful mitigation.
- The bug is local‑only: remote exploitation without a local foothold is not supported by the public evidence and vendor advisories.
Vendor responses and timelines
- Upstream fix: kernel maintainers merged targeted changes in the 6.7 development cycle to repair the race conditions and to harden GC/reader interactions. Many vendors pulled the upstream patch or implemented equivalent backports for supported stable kernels.
- Red Hat / Enterprise Linux: Red Hat published advisories and backported fixes into their kernel packages; advisories referenced the upstream changes and encouraged customers to update kernel packages to fixed versions.
- Ubuntu: The Ubuntu security team documented the issue and flagged it with a High severity score, recommending update and reboot as required by kernel package upgrades.
- Cloud and distribution vendors (Amazon Linux, Oracle Linux, Debian LTS, etc.) issued their own notices and updates to affected kernel packages; cloud images and managed kernels were similarly updated where applicable.
Practical mitigation and hardening steps (priorities)
- Patch and reboot upstream where possible — the only comprehensive fix is the updated kernel. Prioritize systems where untrusted or multi‑tenant code runs, and schedule reboots as required by your vendor’s advisory.
- If you cannot patch immediately, reduce the attack surface:
- Restrict local access to untrusted users and isolate processes that might be able to create AF_UNIX sockets and pass SCM_RIGHTS payloads.
- Enforce stronger user separation on multi‑tenant hosts; use container isolation, seccomp, and SELinux/AppArmor policies to limit the set of processes that can manipulate file descriptors across processes.
- Consider temporary io_uring controls:
- Some exploitation scenarios involve io_uring registration of file descriptors and other async I/O interactions that make certain GC races more likely. The kernel now supports a sysctl to limit or disable io_uring creation (kernel.io_uring_disabled) so distributions and admins can block unprivileged io_uring use without re‑compiling the kernel. Using that knob to restrict io_uring for unprivileged processes (value 1) or to disable it system‑wide (value 2) is a practical short‑term mitigation where io_uring is not required. Use this only as a stopgap until the kernel is patched.
- Monitor kernel logs and KASAN warnings:
- Watch for kernel oops, KASAN traces, or repeated AF_UNIX warnings that suggest the race is being triggered; these signs should accelerate patching plans.
- For cloud providers and shared hosts:
- Consider adding policy checks to disallow untrusted workloads from using socket FD passing or other IPC facilities that can create inflight cycles. Audit for SCM_RIGHTS usage if feasible.
- Apply least‑privilege and capability restrictions:
- Limit CAP_SYS_ADMIN and other broad capabilities; ensure W^X, SELinux, and kernel hardening features are enabled and tuned to reduce the likelihood of successful local privilege escalation even if a UAF occurs.
Risk analysis: strengths and remaining concerns
Strengths of the response- The flaw was responsibly disclosed, tracked under CVE‑2023‑6531 and documented across NVD and major distro advisories; upstream fixes were merged and backports produced by vendors, which means administrators have actionable remediation paths.
- The vulnerability is local and fairly complex to exploit (high attack complexity), which reduces its appeal to wide‑scale automated exploitation compared with simple remote bugs.
- The kernel community’s fix is surgical: maintainers adjusted synchronization and GC behavior without disabling SCM_RIGHTS or undoing needed functionality, minimizing long‑term functional regressions.
- Availability first: the practical exploit demonstrated in public writeups and automated fuzzers leads reliably to kernel crashes and host instability — a real availability risk for servers and multi‑tenant systems. Organizations should treat this as a high‑priority operational patch.
- Attack chaining: while no public, stable privilege‑escalation exploit specific to CVE‑2023‑6531 has become broadly weaponized, kernel UAFs are common building blocks for local privilege escalation. The presence of this bug increases the attack surface for determined local attackers who can combine it with other weaknesses.
- Coverage variance: not all distributions ship the same kernel versions or backports. Even when upstream patches exist, organizations may run vendor kernels with different timing and backport choices; auditing and testing are required to make sure your product/host receives the right mitigation. Vendor advisories (Red Hat, Ubuntu, Oracle Linux, Amazon Linux, etc.) document accepted fixed versions — follow those for your environment.
Operational checklist for system administrators
- Inventory: Determine which hosts run kernels affected by CVE‑2023‑6531 (kernels older than the vendor‑fixed versions; many upstream references point to fixes landing around the 6.7 cycle).
- Prioritize: Rank machines by exposure and tenancy — multi‑tenant hosts, developer build servers, and machines that allow untrusted local users get the highest priority.
- Patch: Apply vendor kernel updates (Red Hat RHSA/errata, Ubuntu security updates, Amazon/Oracle Linux advisories) and plan reboots as required by your maintenance windows.
- Short term mitigation (if you cannot patch immediately):
- Restrict local shell access and tighten sudoers groups.
- Consider setting kernel.io_uring_disabled=1 or 2 where io_uring is not needed. Test application compatibility before changing the sysctl in production.
- Monitor: Add kernel‑oops and KASAN alerts to monitoring dashboards; treat any unexplained kernel instability as high priority.
- Test: Validate vendor backports in staging to ensure the fix does not introduce regressions relevant to your workloads.
Broader lessons for kernel designers and operators
- Concurrency boundaries must be clearly owned by a single locking discipline. Mixing mutexes and spinlocks over overlapping data without well‑documented ordering invites subtle races that are difficult to reproduce and expensive to diagnose.
- Garbage collection that touches runtime‑observable structures (like skbs carrying file pointers) is a high‑risk design point that requires rigorous proof (or runtime checks) that GC actions cannot race with live readers.
- For operators: high‑performance kernel features (io_uring being the canonical example) increase attack surface; building admin‑controlled knobs (like kernel.io_uring_disabled) is a pragmatic way to let operators rapidly reduce risk without recompiling kernels. (blogs.oracle.com)
Final assessment and recommendation
CVE‑2023‑6531 is a high‑impact local kernel race that produces a reliable availability problem (kernel crashes) and, in principle, could be combined with other flaws to escalate privileges. The issue was responsibly patched upstream and by mainstream vendors; the primary, dependable remediation is install the vendor‑packaged kernel fixes and reboot. For environments where immediate patching is not possible, mitigate by restricting local access, reducing unprivileged io_uring usage via the kernel.io_uring_disabled sysctl, and increasing monitoring for kernel oops and KASAN traces. Administrators of shared‑service, multi‑tenant, or developer workstation fleets should treat this as an operational high priority and apply fixes as quickly as practical.For deeper technical reading and to verify the exact fix and the backport status for your distribution, consult your vendor’s security advisory and the upstream kernel patch materials referenced by the advisories; public writeups from kernel developers and distribution security teams also provide a useful explanation of the locking mismatch and the rationale for the chosen remediation.
CVE‑2023‑6531 demonstrates how compact, well‑intentioned kernel subsystems (UNIX‑domain socket GC and fast async I/O integrations) can interact in unexpected ways and produce critical operational consequences; the remedy is straightforward in theory (apply the fix), but practical mitigation requires disciplined patch management, sensible temporary controls, and careful monitoring while upgrades are rolled out.
Source: MSRC Security Update Guide - Microsoft Security Response Center