A small but consequential race-condition fix landed in the Linux kernel in late October 2025: uio_hv_generic has been changed to stop touching the interrupt mask and instead let userspace control it, closing a hang‑causing race that could leave guest UIO consumers permanently waiting for interrupts.
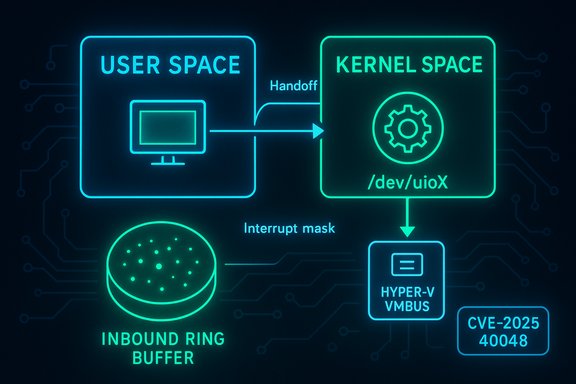
The vulnerability tracked as CVE-2025-40048 concerns the Linux kernel's uio_hv_generic driver — the UIO (Userspace I/O) front-end for the Hyper‑V VMBus. The issue is not a memory-corruption or arbitrary code‑execution bug; it is a logical race between kernel driver code and userspace code over the interrupt mask bit for inbound ring buffers. When the driver attempts to set the interrupt mask by default, it can race with user‑mode operations on the ring buffer. If the mask bit is flipped by the driver at the wrong time, a userspace process waiting on pread can miss an interrupt and hang indefinitely. The upstream patch removes instances where the driver modifies the mask and preserves only the user‑controlled set_event path, shifting mask responsibility entirely to userspace. Why this matters: UIO is intentionally designed to move device handling into user space for flexibility and safety. When the kernel driver unilaterally manipulates the interrupt mask it violates that contract and creates a window where the host (Hyper‑V) can deliver messages that are not signaled to the guest user process, producing a deadlock-like hang. The fix is surgical — remove driver-side mask modifications and rely on the documented userspace interface — but it eliminates a subtle, real-world hang scenario.
A technical note: the definitive upstream discussion and patch appear on the linux‑hyperv mailing list and in the stable kernel patch rollups; distribution-specific advisories and package versions should be consulted to find the exact kernel package that contains the fix for your environment. If your estate includes vendor‑forked kernels or embedded appliances, open a vendor support ticket and request a backport of the upstream commit; those platforms are the most likely to remain vulnerable after upstream integration. Conclusion: CVE-2025-40048 is not dramatic in its root cause, but it is practically important — a small protocol/ownership mistake that produced an avoidable hang. The upstream patch restores the UIO contract, and administrators should treat this as a high‑priority operational patch where UIO is in use.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The vulnerability tracked as CVE-2025-40048 concerns the Linux kernel's uio_hv_generic driver — the UIO (Userspace I/O) front-end for the Hyper‑V VMBus. The issue is not a memory-corruption or arbitrary code‑execution bug; it is a logical race between kernel driver code and userspace code over the interrupt mask bit for inbound ring buffers. When the driver attempts to set the interrupt mask by default, it can race with user‑mode operations on the ring buffer. If the mask bit is flipped by the driver at the wrong time, a userspace process waiting on pread can miss an interrupt and hang indefinitely. The upstream patch removes instances where the driver modifies the mask and preserves only the user‑controlled set_event path, shifting mask responsibility entirely to userspace. Why this matters: UIO is intentionally designed to move device handling into user space for flexibility and safety. When the kernel driver unilaterally manipulates the interrupt mask it violates that contract and creates a window where the host (Hyper‑V) can deliver messages that are not signaled to the guest user process, producing a deadlock-like hang. The fix is surgical — remove driver-side mask modifications and rely on the documented userspace interface — but it eliminates a subtle, real-world hang scenario. Technical anatomy: what the bug is and how it manifests
The components involved
- uio_hv_generic: the kernel driver that exposes Hyper‑V VMBus channels to userspace via /dev/uioX.
- Inbound ring buffer: the structure where host messages are queued for the guest.
- Interrupt mask bit: a flag that controls whether the host should generate interrupts for inbound-to-empty→not-empty transitions.
- Userspace daemon (e.g., hv_fcopy_uio_daemon): the process that reads the ring buffer, clears entries, and re‑arms the interrupt mask via the standard userspace API.
The race in plain language
- The host writes a message into the inbound ring buffer. If the mask is clear and the buffer transitions from empty to non‑empty, the host must generate an interrupt to wake the guest readers.
- The kernel driver, as shipped in some trees, could set the inbound interrupt mask to 1 (masked) by default in certain code paths.
- If the host places a message while the kernel has masked interrupts, it will not signal the guest — the message sits in the ring.
- Later, userspace sets the interrupt mask to 0 (unmasked) and calls pread expecting either an interrupt or to discover an existing message. But because the kernel's relative ordering allowed the driver to mask at the wrong time, userspace can block waiting for an interrupt that will not arrive — the host will not retrigger an interrupt for the existing pending message because the ring never transitioned from empty to non‑empty in the userspace-visible chronology.
- The result: the userspace process can hang waiting forever.
Root cause summary
At heart, this is a contract mismatch between kernel and userspace: the interrupt mask semantics for UIO VMBus channels are intentionally a userspace responsibility. Kernel code that assumed a safe default and modified the mask created a race window. The correct behavior is simple — do not change the mask on behalf of userspace — and that is what the upstream patch enforces.What was changed (the upstream patch)
- The patch removes instances where the kernel driver sets the interrupt mask by default.
- The only driver-side write to the mask that remains is the explicit set_event handler used to implement the documented userspace control path.
- The net effect: userspace writes to /dev/uioX (or otherwise uses the UIO interface) become the single source of truth for the mask bit; the kernel no longer flips the mask asynchronously and thus avoids the race window that could cause hangs.
Scope and affected systems
- Affected component: Linux kernel uio_hv_generic driver (Hyper‑V UIO front-end).
- Typical environments at risk:
- Guest VMs running on Hyper‑V that use UIO-based userspace drivers (for example, guests using hv_fcopy_uio_daemon or other UIO consumers).
- Systems that integrate custom userspace UIO daemons which rely on the mask semantics.
- Not directly affected: hosts that do not use uio_hv_generic in guests, or user processes that do not rely on the UIO mask behavior.
Impact: availability, not code execution
This CVE’s primary impact class is availability. The observable symptom is a guest-side hang: userspace processes that wait for interrupts on a UIO channel can block indefinitely. There is no public evidence that this bug enables remote code execution or privilege escalation in the host or guest by itself. Treat it as a deterministic-but-local DoS against the guest userspace process, which in multi‑tenant or service contexts can be a significant operational problem. Risk profile highlights:- Impact: Userspace hang/blocked I/O operations; application- or service-level unresponsiveness.
- Exploitability: Low complexity — reproducible with carefully timed operations (reliable in lab conditions when the race is triggered), but requires ability to execute the relevant userspace actions in the guest.
- Confidentiality/Integrity: Not implicated by current reports — this is not a memory-corruption primitive.
- Cloud and multi‑tenant concern: If a VMBus channel is exposed to untrusted guests, a misbehaving guest could craft sequences that trigger hang conditions in its own userspace. While this does not escalate directly to other VMs, the operational fallout (support, resource consumption, monitoring noise) can be material.
Cross‑checking and verification
Multiple independent sources corroborate the kernel change and the nature of the bug:- The upstream patch and mailing-list discussion are publicly available in the linux‑hyperv archives; the patch description matches the observed behavioral fix (remove driver mask toggles).
- Open vulnerability indices (OSV, Debian tracker, cvefeed) list CVE-2025-40048 with descriptions that match the patch summary and note the remediation as removing driver-side mask modifications.
- Stable kernel update postings (stable patch lists and spinics entries) include the same change in their rollups, indicating the patch was merged into the stable trees for downstream packaging.
Remediation and mitigation guidance (practical playbook)
- Inventory first
- Identify guests and images that use UIO-based userspace drivers.
- Check kernel versions and whether your distribution’s kernel packages include the stable patch that removes driver-side mask writes.
- Patch kernel packages
- Apply the distribution kernel update or vendor-provided backport that includes the stable commit. This is the definitive fix.
- Reboot hosts/guests as required by your patch process.
- Test before wide rollout
- In a staging environment reproduce the scenario with hv_fcopy_uio_daemon (or your UIO consumer) by delaying mask changes and verifying there is no hang post-patch.
- Confirm that /dev/uioX semantics remain unchanged for legitimate userspace—functionality should be preserved because the patch is conservative.
- Temporary compensations (if you cannot patch immediately)
- Avoid relying on driver-side mask defaults in your userspace code: always check the ring contents before waiting on interrupts, and re‑arm the mask in a safe, idempotent way.
- For sensitive workloads, restrict deployment of UIO-based drivers where guests are untrusted.
- Increase monitoring for hung processes, prolonged pread waits on /dev/uio, and related guest-side symptoms.
- Post‑patch validation
- Run your UIO consumer test suite and validate no hangs occur when the host pushes messages concurrently.
- Monitor logs and health checks for anomalous I/O waits or degraded performance.
Developer guidance (for kernel and userspace authors)
- Respect the UIO contract: userspace controls the mask. Kernel drivers should not make presumptive changes to userspace-managed flags.
- Make userspace robust: when waiting on interrupts, always check for pending data in the ring before blocking on pread/poll. A read-then-wait pattern reduces the dependency on perfect ordering.
- Use atomic operations and well-documented synchronization primitives when toggling shared flags.
- Add unit and integration tests that simulate concurrent host writes and mask flips to catch regressions before release.
- For kernel maintainers: prefer small, surgical fixes that avoid hidden state changes. The upstream patch is intentionally conservative to minimize regressions.
Critical analysis: strengths of the fix and residual risks
Strengths (what went right)
- The fix is small, well-scoped, and aligns with the documented UIO design: userspace controls the mask. That reduces regression risk.
- Upstream and stable trees accepted the patch quickly and it has been circulated to distributions, so remediation is achievable via normal kernel updates.
- The technical change preserves functionality while eliminating the race window; it does not alter the API contract userspace relies on.
Residual risks and caveats
- Vendor lag: embedded vendors and appliance builders that maintain forked kernels may not backport the fix promptly. Those fleets are the highest long-term exposure.
- Operational detection: a hung user process can be misinterpreted as application-level failure rather than a kernel-driven race. Without proper instrumentation, incidents may be escalated incorrectly.
- Behavioral assumptions: some userspace code may have depended, implicitly, on the previous kernel behavior. Although the fix preserves explicit set_event semantics, any implicit reliance on driver masking must be audited.
- Severity perception: some commercial feeds labeled the CVE with higher severity; while technically the issue is availability-only, operational impact (service hangs) can justify high-priority remediation in production environments.
Detection and incident response guidance
- Hunting signals
- Guest-side processes blocked in pread on /dev/uioX for extended durations.
- Repeated attempts to read the ring that return empty while the expected producer activity occurs.
- Telemetry showing host wrote to the ring but no interrupt delivery logged on the guest side.
- For incident responders
- Correlate guest-side hangs with host-side VMBus traffic and timestamps.
- If you observe a live hang, capture userspace traces (strace, gdb attach if safe) and kernel logs on both guest and host.
- Quarantine affected VMs and reproduce the condition on a lab host patched with and without the fix to determine whether the problem is the uio_hv_generic race.
- Apply vendor kernel updates and retest. Keep forensic artifacts for post-mortem if you suspect malicious or misconfigured behavior caused the hang.
Bottom line and recommendations
CVE-2025-40048 is a classic example of a small design/ordering bug producing outsized operational pain: a userspace hang that can affect services relying on UIO VMBus channels. The upstream fix — remove driver-side mask toggles and let userspace manage the interrupt mask — is the right, low-risk remedy and is included in stable kernel updates. Operators should:- Inventory UIO usage across guest images.
- Apply the kernel updates or vendor backports that include the fix.
- Test UIO consumers for correct behavior after patching.
- For environments that cannot patch immediately, harden userspace by checking ring contents before waiting and restrict UIO exposure for untrusted guests.
A technical note: the definitive upstream discussion and patch appear on the linux‑hyperv mailing list and in the stable kernel patch rollups; distribution-specific advisories and package versions should be consulted to find the exact kernel package that contains the fix for your environment. If your estate includes vendor‑forked kernels or embedded appliances, open a vendor support ticket and request a backport of the upstream commit; those platforms are the most likely to remain vulnerable after upstream integration. Conclusion: CVE-2025-40048 is not dramatic in its root cause, but it is practically important — a small protocol/ownership mistake that produced an avoidable hang. The upstream patch restores the UIO contract, and administrators should treat this as a high‑priority operational patch where UIO is in use.
Source: MSRC Security Update Guide - Microsoft Security Response Center