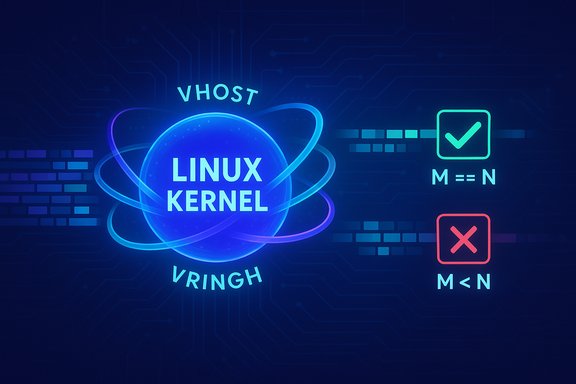
The Linux kernel received a surgical but important correctness fix for the vhost/vringh dataplane: a check that treated the return from copy_toiter (and related copy_iter helpers) as an error code was replaced with an equality test that verifies the exact number of bytes* were copied, closing a logic gap that could allow partial copies to be misinterpreted as full transfers and lead to host instability.
vhost is the kernel-side acceleration layer for virtio devices that moves I/O dataplane handling into the kernel for performance. vringh is the part of that code that manages ring buffers and performs data movement between guest memory and host userspace consumers. Because vhost/vringh operates in kernel context and handles guest I/O on behalf of virtual machines, correctness of tiny primitives — including the semantics of copy_to_iter and copy_from_iter — matters: a mistaken assumption about a helper’s return value can propagate into incorrect buffer contents, crashes, or other unpredictable behavior in hosts that run virtual machines.
The recently merged upstream changes address a recurring code pattern: the code requested N bytes to be copied and only tested whether the helper returned a negative value to indicate an error. However, copy_to_iter/copy_from_iter return the number of bytes actually copied (0 ≤ M ≤ N) rather than a negative errno. The correct contract is to compare the returned byte count to the requested length and treat mismatches as failures. Upstream maintainers changed the negative-value check to a strict equality check — i.e., require M == N — then route failures to the expected cleanup and error paths.
Prioritization guidance:
Appendix: quick commands and short reminders
Concluding statement: small code changes in privileged code paths matter. This fix — enforcing exact byte-copy semantics for copy_to_iter/copy_from_iter in vhost/vringh — is modest in size but high in practical value: it removes a class of silent partial-copy failures that can destabilize virtualization hosts, and it should be applied promptly in production virtualization infrastructure.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
vhost is the kernel-side acceleration layer for virtio devices that moves I/O dataplane handling into the kernel for performance. vringh is the part of that code that manages ring buffers and performs data movement between guest memory and host userspace consumers. Because vhost/vringh operates in kernel context and handles guest I/O on behalf of virtual machines, correctness of tiny primitives — including the semantics of copy_to_iter and copy_from_iter — matters: a mistaken assumption about a helper’s return value can propagate into incorrect buffer contents, crashes, or other unpredictable behavior in hosts that run virtual machines.The recently merged upstream changes address a recurring code pattern: the code requested N bytes to be copied and only tested whether the helper returned a negative value to indicate an error. However, copy_to_iter/copy_from_iter return the number of bytes actually copied (0 ≤ M ≤ N) rather than a negative errno. The correct contract is to compare the returned byte count to the requested length and treat mismatches as failures. Upstream maintainers changed the negative-value check to a strict equality check — i.e., require M == N — then route failures to the expected cleanup and error paths.
Technical anatomy: what went wrong and what changed
The bug pattern in plain language
- The code asked copy_to_iter/copy_from_iter to copy a fixed number of bytes (N).
- The helper returned M, the number of bytes actually copied, where 0 ≤ M ≤ N.
- Instead of verifying M == N, the original code only checked whether M was negative (M < 0) and treated non-negative values as success.
- Because these helpers never return negative error codes, a partial copy (M < N) silently passed the test and the caller assumed the rest of the bytes were present, leading to inconsistent data handling and, in some call paths, kernel oopses or other failures.
The fix (minimal and intentional)
- Replace the incorrect negative-value test with an equality test that verifies the number of bytes copied equals the number requested (ret == expected_len).
- On mismatch, execute the established error/cleanup path (deallocate, unwind state, return an error).
- The change is kept deliberately small to reduce regression risk and simplify downstream backports; it enforces the documented contract for the copy helpers without changing normal-case behavior.
Why equality is the right check
APIs that return a byte count communicate both success and partial success via the returned integer. For code that depends on a full transfer, any partial transfer is semantically an error. Changing the check to require exact equality ensures the caller’s assumptions remain valid and that subsequent logic never operates on partially filled buffers. This is a widely accepted defensive coding practice in kernel development.Impact and exposure: where this matters most
Affected components and builds
Any Linux kernel build that included the vulnerable vhost/vringh implementation prior to the stable upstream commit(s) is potentially affected. That includes mainstream distribution kernels, cloud provider images, and vendor/embedded kernels that incorporated the upstream code without the fix. Because vhost/vringh is a standard kernel datapath for virtio acceleration, the exposure is primarily on hosts that enable and use vhost for guest I/O acceleration.Attack surface and vector
- The vector is local/guest rather than a simple unauthenticated remote network vector: a guest VM or a local process able to interact with the vhost datapath and exercise vringh operations could trigger the partial-copy path.
- Privileges required are relatively low in practice: an unprivileged guest that can submit virtio operations (or a local process on the host that uses the vhost interface) might be able to exercise the vulnerable code path.
Primary impact: availability (DoS) and host instability
The most realistic outcomes for unpatched hosts are Denial‑of‑Service (kernel oopses, crashes) and general host instability caused by incorrect buffer contents or inconsistent state. Public trackers and vendors characterize this fix as a correctness/robustness hardening rather than an immediate remote code execution (RCE) vulnerability; however, kernel crashes and resource corruption are high-value primitives for attackers who already have a foothold. Treat them seriously, especially in multi‑tenant or cloud environments.Where to prioritize remediation
- Highest priority: multi‑tenant hypervisor hosts, cloud compute nodes, and virtualization clusters where one host failure impacts many tenants.
- High priority: hosts that run untrusted guests (CI systems, public cloud instances, container-hosts that allow VM creation) or environments where guest I/O workloads frequently exercise vhost/vringh paths.
- Medium priority: single‑tenant desktops and tightly controlled servers, which should still be patched during normal maintenance windows.
Exploitability and real-world evidence (what is verified / unverified)
- At disclosure, there were no authoritative public reports that this bug was used in the wild to achieve remote code execution or privilege escalation. Public trackers classify it primarily as a correctness/availability issue. Absence of evidence is not proof of absence — kernel faults remain high-value to attackers — so treat the lack of a PoC as a caution, not as reason to deprioritize patching.
- The required preconditions (local or guest access and the ability to exercise specific vhost operations) make large-scale remote exploitation unlikely, but the potential for chaining with other local primitives means defenders should patch promptly.
Detection, triage and incident response
Hunting signals and telemetry
- Kernel logs (dmesg, journalctl) that show stack traces containing vhost, vringh, copy_to_iter, or copy_from_iter symbols.
- Kernel oops traces or panics that occur while guests are performing I/O-heavy workloads.
- Sudden or repeated failures correlated with particular guests or times when virtio devices were active.
- Confirm vhost modules are loaded:
- lsmod | grep vhost
- Confirm kernel release and build:
- uname -r
- Inspect kernel logs around a suspected incident:
- journalctl -k --since "YYYY-MM-DD HH:MM" | grep -iE "vhost|vring|oops|copy_from_iter|copy_to_iter"
Short incident playbook
- Isolate affected host(s) from production pools if multiple tenants are impacted.
- Correlate VM identifiers and workload traces to identify the guest(s) exercising vhost paths.
- Suspend or quarantine untrusted guests pending remediation.
- Apply vendor/distribution kernel update(s) that include the upstream stable commit and reboot into the patched kernel.
- Preserve logs and crash dumps for forensic analysis.
Remediation: patching and rollout guidance
Definitive remediation
Install a kernel package that contains the upstream stable commit(s) implementing the equality check and reboot into the patched kernel. This is the only reliable fix because the issue exists in kernel code paths. Distributions will typically backport the small, surgical upstream change into their stable packages; track your distro advisory for the exact package/version that contains the fix.Staged rollout recommendation
- Inventory: Identify hosts that run vhost/vringh (lsmod, kernel config, package inventory).
- Map: Cross-check kernel package changelogs or distribution advisories for references to the CVE identifier(s) and upstream commit IDs.
- Pilot: Apply the updated kernel to a small pilot group that exercises representative virtio workloads.
- Validate: Reproduce previously failing workloads in staging and monitor kernel logs for two weeks (7–14 days).
- Rollout: Expand to production in waves (pilot → expand → full rollout).
- Monitor: Keep kernel telemetry and SIEM rules active to detect residual traces or regressions.
Interim mitigations if patching is delayed
- Restrict which guests or local processes are allowed to use vhost/vringh functionality. If you operate a multi‑tenant environment, temporarily move untrusted guests to patched hosts where possible.
- Consider limiting the exposure by disabling vhost acceleration on critical hosts that cannot be patched immediately, balancing the performance cost against the stability risk.
- Centralize kernel logs so transient oops traces do not get lost during auto-reboots.
Engineering analysis: why the fix is low risk yet important
Kernel maintainers prefer minimal, contract-preserving edits for correctness issues. This fix meets those criteria:- It does not alter normal behavior when copy helpers succeed in full.
- It hardens corner-case semantics, ensuring partial results are not misinterpreted as success.
- The minimal code change footprint makes the patch straightforward to backport into stable vendor kernels and reduces the likelihood of regressions.
Operational risks and long tail
Vendor/OEM lag and embedded devices
Upstream merges do not automatically reach every vendor or embedded image. Devices with vendor‑forked kernels (appliances, embedded platforms, some cloud images) can remain vulnerable longer because backport cycles vary. For such devices, coordinate with vendors for patched images or apply network/isolation compensations until the vendor image is available.Detection challenges
Kernel oops traces can be noisy and transient; hosts that auto-reboot on panic may lose crucial indicators unless logs and crash dumps are centrally collected. Organizations without centralized kernel telemetry might miss incidents entirely. Prioritize log aggregation and crash-dump capture in high‑value or multi‑tenant host fleets.Chaining potential
Although this patch addresses a correctness/availability defect, resource faults and kernel oopses are commonly exploited as stepping stones in multi‑stage attacks. An attacker with a foothold could combine timing, resource exhaustion, or other local primitives with kernel instability to try and escalate. That risk elevates the priority for patching in cloud and multi‑tenant contexts.Practical checklist for system administrators
- Inventory: Find hosts with vhost/vringh enabled (lsmod | grep vhost; check kernel config and packages).
- Map: Confirm whether YOUR kernel package includes the upstream commit(s) that implement the equality check (check package changelog or vendor advisory).
- Patch: Schedule and deploy the vendor-supplied kernel update that includes the fix; reboot hosts into the patched kernel.
- Validate: Reproduce representative virtio I/O workloads in a staging environment and verify the absence of the earlier oops traces. Monitor kernel logs for at least one maintenance cycle (7–14 days).
- Compensate: If immediate patching is impossible, migrate untrusted guests off unpatched hosts, or disable vhost acceleration where feasible. Maintain centralized kernel logging and crash-dump retention.
Final analysis and verdict
This is a small, low-risk upstream fix that closes a correctness gap in a privileged kernel datapath. Its operational importance is highest for hosts that perform virtualization for multiple tenants, cloud providers, and any environment where untrusted guests can exercise the vhost path. The fix is narrowly scoped (replace a negative check with an equality check) and is straightforward for distributions and vendors to backport — which means remediation is simple in principle but may be delayed in practice by vendor maintenance cycles for some embedded or OEM kernels.Prioritization guidance:
- Treat multi‑tenant hypervisor hosts and cloud compute nodes as high priority for patching.
- Treat single‑tenant and hardened desktops as normal maintenance updates.
- Assume no public, authoritative evidence of exploitation at disclosure, but do not use that as an excuse to delay remediation: kernel availability faults are valuable primitives to attackers and warrant prompt action.
Appendix: quick commands and short reminders
- Check module and kernel: lsmod | grep vhost ; uname -r.
- Search kernel logs: journalctl -k --since "YYYY-MM-DD HH:MM" | grep -iE "vhost|vring|copy_to_iter|copy_from_iter".
- Patch and reboot: install the kernel package that includes the upstream stable commit(s); reboot is required for kernel updates to take effect.
Concluding statement: small code changes in privileged code paths matter. This fix — enforcing exact byte-copy semantics for copy_to_iter/copy_from_iter in vhost/vringh — is modest in size but high in practical value: it removes a class of silent partial-copy failures that can destabilize virtualization hosts, and it should be applied promptly in production virtualization infrastructure.
Source: MSRC Security Update Guide - Microsoft Security Response Center