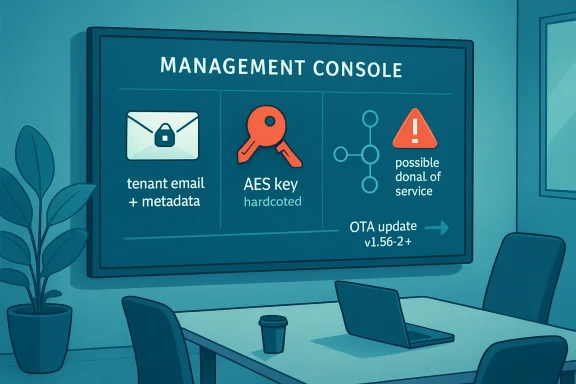
CISA published an industrial-control-system advisory on May 7, 2026, warning that MAXHUB Pivot client application versions before v1.36.2 expose tenant email data and metadata through a hardcoded AES key and may allow unauthorized MQTT device enrollment causing denial of service. The advisory is narrow in product scope but broad in lesson: a device-management client became a cloud-tenant data exposure risk because a secret was shipped where attackers could recover it. MAXHUB says the fix is available through an over-the-air update, and CISA says it has no evidence of public exploitation. That should reassure customers only halfway, because this is exactly the kind of quiet management-plane weakness that ages badly when inventories are incomplete.
MAXHUB Pivot is not just another desktop helper app. It is marketed as a unified device-management system for displays and collaboration hardware, with remote control, firmware delivery, application management, scheduling, analytics, and device operations bundled into one administrative surface. That is convenient for schools, meeting-room operators, managed-service providers, and enterprises with fleets of interactive panels.
Convenience is also why this advisory matters. The more a tool centralizes device operations, the more its client application becomes a trust broker between tenants, devices, cloud services, and administrators. A flaw in that layer does not need to look cinematic to be consequential; it merely has to expose identifiers, weaken tenant boundaries, or let outsiders register noise into a management channel.
CISA’s description of CVE-2026-6411 is blunt. Versions prior to MAXHUB Pivot client application v1.36.2 may allow an attacker to obtain encrypted tenant email addresses and related metadata from any tenant. Because the application contains a hardcoded AES key, that encrypted data can be decrypted into cleartext.
That turns what might otherwise be a lower-grade leak into a design failure. Encryption is not a talisman; it is an engineering contract. If the key is embedded in software distributed to clients, the question becomes not whether a sufficiently motivated attacker can recover it, but how long it takes and how widely the resulting decryptor circulates.
This is one of the oldest failures in software security, and it persists because it is so tempting during product development. A single embedded key simplifies compatibility. It reduces dependency on per-tenant key management, device identity, certificate provisioning, or server-side decryption workflows. It is easy to test and difficult to rotate cleanly after release.
But that simplicity is purchased with future pain. Once a universal key leaks, all data encrypted under it must be treated as exposed. If the same key protects tenant email addresses across customers, the blast radius is not limited to one compromised endpoint. It becomes a product-wide confidentiality issue affecting any tenant data retrievable by the vulnerable flow.
The advisory does not say that passwords, message contents, or device-control credentials are exposed. That distinction matters. But tenant email addresses and associated metadata are not harmless in 2026. They are routing material for phishing, account takeover attempts, social engineering, tenant enumeration, and reconnaissance against organizations that may not even think of collaboration displays as part of their identity perimeter.
MQTT is widely used for lightweight messaging between devices and services. In legitimate device-management systems, it can be a sensible way to coordinate state, telemetry, commands, or enrollment workflows. But messaging protocols become dangerous when identity, authorization, and tenant separation are bolted on too casually.
Unauthorized device enrollment is not merely a nuisance if the management system treats enrolled clients as operational participants. Fake devices can pollute dashboards, consume resources, trigger alerts, confuse inventory, and create administrative uncertainty at precisely the layer teams use to understand their fleets. In a busy AV or facilities environment, a flood of bogus devices can become an availability problem before anyone has time to perform forensics.
This is why CISA’s CVSS vector lands at 7.3 high severity rather than in the “interesting but minor” category. The vulnerability is network exploitable, low complexity, requires no privileges, and requires no user interaction. Confidentiality, integrity, and availability impacts are each rated low, but the combination is what counts: tenant information exposure plus the ability to disturb tenant operations.
MAXHUB is not alone in this shift. The entire meeting-room and digital-signage market has moved toward centralized management because customers demanded it. IT teams want one console to update panels, push applications, wake displays, schedule tasks, and troubleshoot rooms without dispatching a technician. Vendors answered with cloud-connected management planes.
That trend makes sense operationally, but it changes the risk model. These products sit at the intersection of physical spaces, user identity, network segmentation, cloud administration, and device lifecycle management. A vulnerable client application in that ecosystem is not equivalent to a broken screensaver utility; it is part of a chain that administrators may rely on to maintain working rooms and public-facing displays.
The advisory’s “Information Technology” sector label undersells the practical reach. MAXHUB Pivot may be deployed in education, healthcare administration, local government, corporate campuses, hospitality, houses of worship, and managed AV environments. The affected software is globally deployed, and the vendor’s headquarters location is listed as the United States. A worldwide footprint means patch lag will be uneven.
The messy part is fleet reality. Device-management clients are often installed across rooms, panels, appliances, jump boxes, administrator workstations, staging devices, and forgotten lab units. Some are online and managed. Others are offline, firewalled, powered down, or installed during pilot deployments nobody has inventoried in months.
Administrators should therefore treat the version number as a verification task, not a press-release checkbox. The goal is not to know that MAXHUB issued a fix. The goal is to know which systems in your environment run Pivot, which build they run, whether the OTA update completed, and whether any devices remain pinned to older software because of network policy, proxy behavior, maintenance windows, or failed update jobs.
This is especially important because CISA says the vulnerable versions are those before v1.36.2. That line is precise enough for action. If you cannot produce a list of Pivot clients and their versions, you do not yet know whether you are exposed.
The temptation in AV and collaboration deployments is to carve exceptions. Meeting rooms need to work. Displays need cloud access. Vendors need support channels. Facilities teams need dashboards. Executives notice broken conference rooms faster than they notice overbroad outbound messaging permissions.
That is how device-management systems drift into privileged limbo. They are too operationally important to break, too specialized for general endpoint teams to own fully, and too cloud-connected to fit neatly into old segmentation diagrams. When a vulnerability lands, nobody wants to discover that the asset owner is “probably the AV integrator” and the patch owner is “maybe desktop engineering.”
CISA also reminds organizations to perform impact analysis and risk assessment before deploying defensive measures. That caveat matters here. Blocking MQTT or cloud endpoints blindly could interrupt legitimate device management. The right response is not panic isolation; it is controlled validation, version enforcement, network review, and monitoring for suspicious enrollment behavior.
Hardcoded-key vulnerabilities occupy an awkward space in disclosure timelines. Once the advisory explains the class of issue, reverse engineers know where to look. If vulnerable binaries remain available or installed, attackers can attempt to recover the key and reproduce the data access path. The existence of a fixed version does not erase old clients from the world.
There is also a difference between mass exploitation and quiet abuse. Tenant email addresses and metadata are reconnaissance assets. An attacker might use them to sharpen phishing campaigns, identify customers of a vendor ecosystem, map organizational tenants, or test enrollment noise without triggering dramatic alarms. The result may not look like a ransomware outbreak; it may look like better-targeted social engineering weeks later.
That is why defenders should avoid the false binary of “exploited” versus “not exploited.” The operational question is whether the weakness is reachable in your environment and whether you have logs capable of showing abnormal access or enrollment activity. If the answer to either is uncertain, the advisory deserves more than a routine patch note.
The repetition of the same fixed version is notable. It suggests v1.36.2 is not merely a routine maintenance release but a security baseline for Pivot deployments. Organizations that postponed the earlier password-recovery fix now face a second reason to move, and a stronger argument that anything older than v1.36.2 should be treated as out of policy.
To be fair, repeated advisories do not automatically mean a vendor is uniquely negligent. Security researchers often inspect products in clusters, and once one management platform draws attention, related weaknesses may surface in quick succession. Coordinated disclosure can make a product look worse in the short term while making customers safer in the long term.
Still, enterprise buyers should pay attention to how vendors respond after the advisory. The questions now are about transparency, update reliability, version visibility, key rotation, tenant isolation, and whether MAXHUB can explain what data was accessible, how the server side has been hardened, and whether any compensating controls were added beyond the client update.
MAXHUB Pivot’s function makes that risk sharper. If Pivot is used to manage fleets, the client application itself may exist wherever those fleets are administered. That can include central IT, regional support teams, AV contractors, facilities groups, and classrooms. In some organizations, the people who can update the software may not be the same people who receive CISA advisories.
This is where patch management programs often reveal their blind spots. Windows endpoints might be tightly governed through Intune, Configuration Manager, or another management stack, while AV utilities live outside the standard catalog. If Pivot was installed manually, downloaded from a support page, or bundled with a deployment package, it may not appear in normal software compliance reports.
Administrators should resist the urge to solve this with email alone. A “please update MAXHUB Pivot” notice is weaker than a query against endpoint inventory, a check of installed application versions, and a change ticket that records completion. Security advisories should end in evidence, not vibes.
CISA’s advisory says encrypted tenant email addresses and related metadata from any tenant may be obtainable. Even with low confidentiality impact in the CVSS score, the phrase “any tenant” should make SaaS security teams wince. Cross-tenant exposure is the kind of flaw that undermines confidence disproportionate to the raw sensitivity of the fields involved.
Email addresses are also more valuable in context than in isolation. A tenant email tied to a device-management ecosystem can reveal vendor adoption, administrative domains, room technology choices, or managed-service relationships. In the hands of an attacker, that can inform pretexting: a message about a Pivot update, a bogus support ticket, or a fake device-enrollment notice becomes more believable when aimed at a real tenant contact.
The appropriate remediation therefore cannot be only “ship a new client.” MAXHUB should also have rotated affected cryptographic material where applicable, reviewed server-side authorization paths, monitored for anomalous access, and ensured that legacy clients cannot continue using the broken path. Customers may not see all of that work, but they should ask whether it happened.
A vulnerable client with embedded secrets is a reminder that management utilities deserve the same scrutiny as endpoint agents and remote-access tools. If it can enroll devices, push apps, update firmware, or reach tenant metadata, it belongs in the privileged software inventory. It should be updated, monitored, and restricted accordingly.
Windows administrators should check whether Pivot is deployed through standard software distribution or installed ad hoc. If the latter, now is the time to bring it into policy. That means application inventory, version detection, update packaging if OTA is insufficient, and removal from systems that no longer need it.
The principle extends beyond MAXHUB. The modern Windows admin workstation is often a nest of vendor consoles: camera systems, signage platforms, room schedulers, access-control utilities, printer fleets, UPS dashboards, and collaboration hardware managers. Any one of them can become the weakest administrative bridge if left outside normal patch discipline.
That means per-tenant or per-device credentials, server-enforced authorization, narrowly scoped tokens, key rotation, certificate-backed identity, and telemetry that can distinguish legitimate enrollment from fabricated noise. It also means product teams must threat-model the boring parts of device management, not just the glamorous login screen. Enrollment flows, metadata endpoints, message brokers, and update channels are where operational products often leak trust.
The denial-of-service angle reinforces that point. A management system is not secure merely because attackers cannot take over an admin account. If they can fill a tenant with unauthorized devices, jam operational workflows, or force administrators to distrust their own inventory, they have already degraded the service.
Security teams sometimes treat availability as a lesser impact than confidentiality. In device-management environments, availability and integrity are inseparable. A management plane that cannot tell real devices from fake ones is not just noisy; it is less useful at the exact moment defenders need clarity.
Administrators should treat the following as the operational core of the story:
Source: CISA MAXHUB Pivot Client Application | CISA
 The Management Console Became the Attack Surface
The Management Console Became the Attack Surface
MAXHUB Pivot is not just another desktop helper app. It is marketed as a unified device-management system for displays and collaboration hardware, with remote control, firmware delivery, application management, scheduling, analytics, and device operations bundled into one administrative surface. That is convenient for schools, meeting-room operators, managed-service providers, and enterprises with fleets of interactive panels.Convenience is also why this advisory matters. The more a tool centralizes device operations, the more its client application becomes a trust broker between tenants, devices, cloud services, and administrators. A flaw in that layer does not need to look cinematic to be consequential; it merely has to expose identifiers, weaken tenant boundaries, or let outsiders register noise into a management channel.
CISA’s description of CVE-2026-6411 is blunt. Versions prior to MAXHUB Pivot client application v1.36.2 may allow an attacker to obtain encrypted tenant email addresses and related metadata from any tenant. Because the application contains a hardcoded AES key, that encrypted data can be decrypted into cleartext.
That turns what might otherwise be a lower-grade leak into a design failure. Encryption is not a talisman; it is an engineering contract. If the key is embedded in software distributed to clients, the question becomes not whether a sufficiently motivated attacker can recover it, but how long it takes and how widely the resulting decryptor circulates.
A Hardcoded Key Is a Security Boundary Written in Pencil
The vulnerability is categorized under CWE-327, “Use of a Broken or Risky Cryptographic Algorithm,” but the practical sin is broader than algorithm choice. A hardcoded symmetric key inside a client application is a shared secret with no meaningful secrecy once the binary is in adversarial hands. Every installed copy is potentially a key escrow service for attackers.This is one of the oldest failures in software security, and it persists because it is so tempting during product development. A single embedded key simplifies compatibility. It reduces dependency on per-tenant key management, device identity, certificate provisioning, or server-side decryption workflows. It is easy to test and difficult to rotate cleanly after release.
But that simplicity is purchased with future pain. Once a universal key leaks, all data encrypted under it must be treated as exposed. If the same key protects tenant email addresses across customers, the blast radius is not limited to one compromised endpoint. It becomes a product-wide confidentiality issue affecting any tenant data retrievable by the vulnerable flow.
The advisory does not say that passwords, message contents, or device-control credentials are exposed. That distinction matters. But tenant email addresses and associated metadata are not harmless in 2026. They are routing material for phishing, account takeover attempts, social engineering, tenant enumeration, and reconnaissance against organizations that may not even think of collaboration displays as part of their identity perimeter.
The MQTT Angle Makes This More Than a Privacy Bug
The second half of the advisory is the part administrators should not skim past. CISA says an attacker may be able to cause a denial-of-service condition by enrolling multiple unauthorized devices into a tenant via MQTT, potentially disrupting tenant operations. That sentence moves the issue from information disclosure into operational integrity.MQTT is widely used for lightweight messaging between devices and services. In legitimate device-management systems, it can be a sensible way to coordinate state, telemetry, commands, or enrollment workflows. But messaging protocols become dangerous when identity, authorization, and tenant separation are bolted on too casually.
Unauthorized device enrollment is not merely a nuisance if the management system treats enrolled clients as operational participants. Fake devices can pollute dashboards, consume resources, trigger alerts, confuse inventory, and create administrative uncertainty at precisely the layer teams use to understand their fleets. In a busy AV or facilities environment, a flood of bogus devices can become an availability problem before anyone has time to perform forensics.
This is why CISA’s CVSS vector lands at 7.3 high severity rather than in the “interesting but minor” category. The vulnerability is network exploitable, low complexity, requires no privileges, and requires no user interaction. Confidentiality, integrity, and availability impacts are each rated low, but the combination is what counts: tenant information exposure plus the ability to disturb tenant operations.
Collaboration Hardware Is Now Enterprise Infrastructure
A decade ago, many organizations treated conference-room gear as expensive furniture with HDMI ports. That view is no longer defensible. Modern collaboration displays, videobars, room systems, signage panels, and interactive boards run operating systems, connect to cloud services, receive firmware updates, install apps, authenticate users, and report telemetry.MAXHUB is not alone in this shift. The entire meeting-room and digital-signage market has moved toward centralized management because customers demanded it. IT teams want one console to update panels, push applications, wake displays, schedule tasks, and troubleshoot rooms without dispatching a technician. Vendors answered with cloud-connected management planes.
That trend makes sense operationally, but it changes the risk model. These products sit at the intersection of physical spaces, user identity, network segmentation, cloud administration, and device lifecycle management. A vulnerable client application in that ecosystem is not equivalent to a broken screensaver utility; it is part of a chain that administrators may rely on to maintain working rooms and public-facing displays.
The advisory’s “Information Technology” sector label undersells the practical reach. MAXHUB Pivot may be deployed in education, healthcare administration, local government, corporate campuses, hospitality, houses of worship, and managed AV environments. The affected software is globally deployed, and the vendor’s headquarters location is listed as the United States. A worldwide footprint means patch lag will be uneven.
The Patch Is Straightforward; Proving Coverage Is Not
MAXHUB recommends upgrading the Pivot client application to v1.36.2 or newer. The remediation is available through an OTA update, and users already running v1.36.2 or later are not affected. That is the clean part of the story.The messy part is fleet reality. Device-management clients are often installed across rooms, panels, appliances, jump boxes, administrator workstations, staging devices, and forgotten lab units. Some are online and managed. Others are offline, firewalled, powered down, or installed during pilot deployments nobody has inventoried in months.
Administrators should therefore treat the version number as a verification task, not a press-release checkbox. The goal is not to know that MAXHUB issued a fix. The goal is to know which systems in your environment run Pivot, which build they run, whether the OTA update completed, and whether any devices remain pinned to older software because of network policy, proxy behavior, maintenance windows, or failed update jobs.
This is especially important because CISA says the vulnerable versions are those before v1.36.2. That line is precise enough for action. If you cannot produce a list of Pivot clients and their versions, you do not yet know whether you are exposed.
CISA’s Familiar Hardening Advice Still Applies
CISA’s recommended practices read like standard industrial-control-system guidance: minimize network exposure, keep control-system devices off the public Internet, place remote systems behind firewalls, isolate them from business networks, and use secure remote access methods such as VPNs when remote access is required. It is familiar language because it remains depressingly relevant.The temptation in AV and collaboration deployments is to carve exceptions. Meeting rooms need to work. Displays need cloud access. Vendors need support channels. Facilities teams need dashboards. Executives notice broken conference rooms faster than they notice overbroad outbound messaging permissions.
That is how device-management systems drift into privileged limbo. They are too operationally important to break, too specialized for general endpoint teams to own fully, and too cloud-connected to fit neatly into old segmentation diagrams. When a vulnerability lands, nobody wants to discover that the asset owner is “probably the AV integrator” and the patch owner is “maybe desktop engineering.”
CISA also reminds organizations to perform impact analysis and risk assessment before deploying defensive measures. That caveat matters here. Blocking MQTT or cloud endpoints blindly could interrupt legitimate device management. The right response is not panic isolation; it is controlled validation, version enforcement, network review, and monitoring for suspicious enrollment behavior.
No Known Exploitation Is Not a Comfort Blanket
Both CISA and MAXHUB say they are not aware of public exploitation targeting this issue at the time of publication. That is useful information, but it should not be read as proof of safety. Absence of known exploitation often means only that nobody has reported seeing it, not that nobody has tried.Hardcoded-key vulnerabilities occupy an awkward space in disclosure timelines. Once the advisory explains the class of issue, reverse engineers know where to look. If vulnerable binaries remain available or installed, attackers can attempt to recover the key and reproduce the data access path. The existence of a fixed version does not erase old clients from the world.
There is also a difference between mass exploitation and quiet abuse. Tenant email addresses and metadata are reconnaissance assets. An attacker might use them to sharpen phishing campaigns, identify customers of a vendor ecosystem, map organizational tenants, or test enrollment noise without triggering dramatic alarms. The result may not look like a ransomware outbreak; it may look like better-targeted social engineering weeks later.
That is why defenders should avoid the false binary of “exploited” versus “not exploited.” The operational question is whether the weakness is reachable in your environment and whether you have logs capable of showing abnormal access or enrollment activity. If the answer to either is uncertain, the advisory deserves more than a routine patch note.
The Earlier Pivot Flaw Makes This a Pattern Worth Watching
This is not the first recent security blemish tied to MAXHUB Pivot. A prior issue, CVE-2025-53704, involved a weak password recovery mechanism affecting versions before v1.36.2 and was also addressed by upgrading to v1.36.2 or later. That earlier bug carried account-takeover implications.The repetition of the same fixed version is notable. It suggests v1.36.2 is not merely a routine maintenance release but a security baseline for Pivot deployments. Organizations that postponed the earlier password-recovery fix now face a second reason to move, and a stronger argument that anything older than v1.36.2 should be treated as out of policy.
To be fair, repeated advisories do not automatically mean a vendor is uniquely negligent. Security researchers often inspect products in clusters, and once one management platform draws attention, related weaknesses may surface in quick succession. Coordinated disclosure can make a product look worse in the short term while making customers safer in the long term.
Still, enterprise buyers should pay attention to how vendors respond after the advisory. The questions now are about transparency, update reliability, version visibility, key rotation, tenant isolation, and whether MAXHUB can explain what data was accessible, how the server side has been hardened, and whether any compensating controls were added beyond the client update.
The Real Risk Is Inventory Debt
Every vulnerability story eventually becomes an asset-management story. The worst exposures are rarely the systems everyone remembers. They are the trial installation in a training room, the management client on a retired technician laptop, the staging device in a closet, or the branch-office display still checking in through an exception nobody documented.MAXHUB Pivot’s function makes that risk sharper. If Pivot is used to manage fleets, the client application itself may exist wherever those fleets are administered. That can include central IT, regional support teams, AV contractors, facilities groups, and classrooms. In some organizations, the people who can update the software may not be the same people who receive CISA advisories.
This is where patch management programs often reveal their blind spots. Windows endpoints might be tightly governed through Intune, Configuration Manager, or another management stack, while AV utilities live outside the standard catalog. If Pivot was installed manually, downloaded from a support page, or bundled with a deployment package, it may not appear in normal software compliance reports.
Administrators should resist the urge to solve this with email alone. A “please update MAXHUB Pivot” notice is weaker than a query against endpoint inventory, a check of installed application versions, and a change ticket that records completion. Security advisories should end in evidence, not vibes.
The Tenant Boundary Is the Product
Cloud management products rise or fall on tenant separation. Customers are trusting the vendor not only to run a service, but to ensure that one organization’s identifiers, devices, logs, commands, and administrative workflows cannot bleed into another’s. That boundary is not a feature; it is the product.CISA’s advisory says encrypted tenant email addresses and related metadata from any tenant may be obtainable. Even with low confidentiality impact in the CVSS score, the phrase “any tenant” should make SaaS security teams wince. Cross-tenant exposure is the kind of flaw that undermines confidence disproportionate to the raw sensitivity of the fields involved.
Email addresses are also more valuable in context than in isolation. A tenant email tied to a device-management ecosystem can reveal vendor adoption, administrative domains, room technology choices, or managed-service relationships. In the hands of an attacker, that can inform pretexting: a message about a Pivot update, a bogus support ticket, or a fake device-enrollment notice becomes more believable when aimed at a real tenant contact.
The appropriate remediation therefore cannot be only “ship a new client.” MAXHUB should also have rotated affected cryptographic material where applicable, reviewed server-side authorization paths, monitored for anomalous access, and ensured that legacy clients cannot continue using the broken path. Customers may not see all of that work, but they should ask whether it happened.
The Windows Angle Is the Admin Workstation
For WindowsForum readers, the immediate concern may not be the display panel itself but the Windows machines and admin workflows around it. Device-management clients often live on the same endpoints used for broader IT administration. Those machines may have privileged browser sessions, VPN access, RMM tools, password managers, and vendor portals.A vulnerable client with embedded secrets is a reminder that management utilities deserve the same scrutiny as endpoint agents and remote-access tools. If it can enroll devices, push apps, update firmware, or reach tenant metadata, it belongs in the privileged software inventory. It should be updated, monitored, and restricted accordingly.
Windows administrators should check whether Pivot is deployed through standard software distribution or installed ad hoc. If the latter, now is the time to bring it into policy. That means application inventory, version detection, update packaging if OTA is insufficient, and removal from systems that no longer need it.
The principle extends beyond MAXHUB. The modern Windows admin workstation is often a nest of vendor consoles: camera systems, signage platforms, room schedulers, access-control utilities, printer fleets, UPS dashboards, and collaboration hardware managers. Any one of them can become the weakest administrative bridge if left outside normal patch discipline.
A Small Advisory With a Large Design Lesson
The obvious lesson is to upgrade to v1.36.2 or later. The more important lesson is that client-side cryptography cannot rescue a design that exposes universal secrets. If tenant data is retrievable by clients, the authorization model must assume clients are hostile, inspectable, and eventually reverse engineered.That means per-tenant or per-device credentials, server-enforced authorization, narrowly scoped tokens, key rotation, certificate-backed identity, and telemetry that can distinguish legitimate enrollment from fabricated noise. It also means product teams must threat-model the boring parts of device management, not just the glamorous login screen. Enrollment flows, metadata endpoints, message brokers, and update channels are where operational products often leak trust.
The denial-of-service angle reinforces that point. A management system is not secure merely because attackers cannot take over an admin account. If they can fill a tenant with unauthorized devices, jam operational workflows, or force administrators to distrust their own inventory, they have already degraded the service.
Security teams sometimes treat availability as a lesser impact than confidentiality. In device-management environments, availability and integrity are inseparable. A management plane that cannot tell real devices from fake ones is not just noisy; it is less useful at the exact moment defenders need clarity.
The Version Number That Should Drive the Change Ticket
This advisory is concrete enough to turn into action without overdramatizing it. The affected product is MAXHUB Pivot client application before v1.36.2. The vulnerability is CVE-2026-6411. The reported exposure includes tenant email addresses and metadata decryptable because of a hardcoded AES key, plus possible denial of service through unauthorized MQTT device enrollment.Administrators should treat the following as the operational core of the story:
- Organizations running MAXHUB Pivot client application versions earlier than v1.36.2 should upgrade to v1.36.2 or newer through the vendor’s OTA update path.
- Teams should verify the installed Pivot client version across administrator workstations, staging systems, managed-room environments, and any devices used by AV or facilities staff.
- Security teams should review logs and tenant records for unusual device enrollment activity, especially unexpected MQTT-linked registrations or sudden growth in device counts.
- Network owners should confirm that Pivot-related systems are not unnecessarily exposed to the Internet and that remote access follows established firewall, segmentation, and VPN controls.
- Procurement and IT governance teams should ask MAXHUB how cryptographic keys were rotated, how legacy clients are handled, and what server-side protections now prevent cross-tenant data access.
- Incident-response teams should remember that exposed tenant email addresses and metadata can fuel phishing and reconnaissance even if no public exploitation has been reported.
Source: CISA MAXHUB Pivot Client Application | CISA