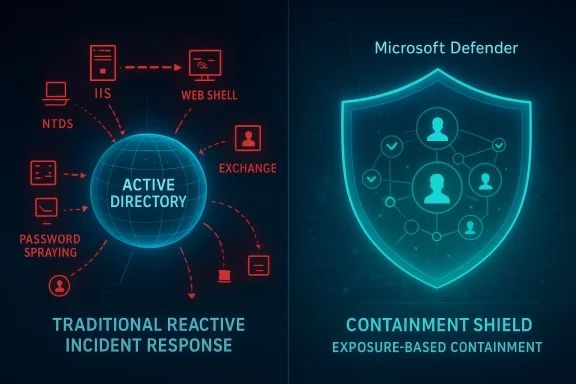
Containing a domain compromise became possible here because Microsoft Defender did something traditional incident response usually cannot do fast enough: it treated exposed credentials as an active containment problem, not just a postmortem cleanup task. In this Microsoft case study, a public-sector intrusion moved from an IIS foothold to directory credential access, Exchange abuse, password spraying, and repeated lateral movement attempts before predictive shielding began blocking the attacker’s next pivots. Once that capability was enabled, Defender stopped waiting for the next malicious action and instead contained context-linked identities as soon as high-confidence exposure signals appeared, sharply reducing the attacker’s ability to expand the breach. The result is a useful blueprint for how predictive shielding can close the speed gap that usually favors identity thieves and domain-compromise operators.
Domain compromise is the moment when a limited foothold stops being a local incident and becomes an enterprise-wide identity crisis. Once an attacker gains control over an Active Directory domain, the environment’s trust fabric itself becomes the weapon: group memberships can be altered, ACLs can be rewritten, Kerberos artifacts can be minted, and policy can be pushed at scale through normal administrative channels. That shift is why defenders treat domain-admin loss as a critical event rather than just another compromised account.
What makes the problem harder is speed. Microsoft’s case study stresses that in many real-world intrusions, domain-level credentials are exposed almost immediately after the initial breach, and the attacker often uses them before defenders have enough visibility to fully scope the damage. That creates a nasty asymmetry: the attacker needs only one successful credential path, while the defender has to inventory, isolate, validate, and restore trust across a live identity platform.
The article’s central argument is that traditional containment is usually too reactive for this kind of campaign. If the defender waits for a credential to be observed doing something obviously malicious, the adversary may already have used it to move into the directory, Exchange, backup systems, or cloud sync infrastructure. Microsoft’s response is to shift from activity-based detection to exposure-based containment, where high-confidence signals of credential theft trigger automated restrictions before the exposed identity is operationalized.
That is the core purpose of predictive shielding inside Microsoft Defender’s automatic attack disruption. It is designed to predict where the attacker will pivot next, identify likely exposed identities, and temporarily contain those identities to block sign-ins and interactive abuse while remediation is underway. Microsoft positions this as an out-of-the-box enhancement for Defender for Endpoint P2 customers who meet the necessary prerequisites.
The significance of the case goes beyond one organization. It shows how modern identity defense is no longer just about locking accounts after compromise; it is about building a response model that can keep up with credential replay, delegated access abuse, and the attacker’s tendency to return with new tooling when the first route is shut down. In that sense, this is not simply a Microsoft feature story. It is a practical demonstration of how defenders can turn the attacker’s own momentum into a containment opportunity.
The Microsoft case study underscores how quickly that threshold can be crossed. The attacker did not linger in a simple one-host scenario. They moved from web shell activity on an IIS server into credential dumping, remote task creation, NTDS-related activity on a domain controller, Exchange delegation changes, and then password spraying and repeated lateral attempts against other servers. The shape of the intrusion is the point: each new credential source widened the blast radius.
This is why the feature matters most in identity-heavy enterprises. A mature attacker does not need to crack every barrier; they only need one privileged seam that gets them past the first layer of containment. If the defender can preemptively contain likely exposed identities before they are abused, the attacker loses the simplest and most scalable path to domain-wide control.
The operator then escalated to NT AUTHORITY\SYSTEM by abusing a Potato-class token impersonation primitive such as BadPotato. That detail is important because SYSTEM on a server is often the gateway to local credential access, service manipulation, and broader post-exploitation flexibility. In practical terms, the attacker had crossed from application-level abuse into host-level control.
The threat actor also deployed Mimikatz to dump logon secrets from LSASS, SAM, and related sources. Once that happens, the attacker no longer needs to rely solely on local privilege escalation; they can harvest usable credentials and replay them against other systems. This is where the incident’s logic begins to shift from host compromise to identity compromise.
This is also the stage where host-scoped containment still makes sense. Blocking the malicious device, isolating the server, and preventing further credential theft can be highly effective before the attacker reaches domain-level assets. After that, however, the response needs to evolve from endpoint containment to identity containment, because the stolen material itself can travel independently of the original machine.
This is the point at which the incident becomes much harder to contain in a conventional way. Once directory credential material is extracted, the attacker can return to the environment repeatedly, use valid accounts, and pivot across authentication paths that defenders still need to keep running. The blog is blunt that at this stage, the first malicious action already surfaced the entire Active Directory credential set, making simple host cleanup insufficient.
That means the breach was no longer just about file servers or domain credentials. It became a confidentiality, privilege, and business-process problem all at once. In many organizations, Exchange is still a central repository of human and machine trust signals, which makes delegated mailbox access a potent multiplier for further compromise.
The adversary then launched a broad password spray from the originally compromised IIS server and gained access to at least 14 servers through password reuse. That detail matters because it illustrates how stolen or guessed credentials can still be operationally powerful even when defenders have some active blocking in place. Once multiple credentials are in circulation, the attacker has options.
The attacker also attempted remote credential dumping against multiple domain controllers and another IIS server using domain and service principals. That behavior reveals a critical truth: once the adversary has enough identities, they stop acting like a single operator and start acting like a distributed authentication campaign. Containment must keep pace with that mobility.
The mechanism is straightforward but strategically powerful. Defender detects post-breach activity associated with credential exposure, evaluates which high-privilege identities were likely affected, and contains those identities to reduce lateral movement and high-impact identity operations. The idea is not to punish the account; it is to remove the attacker’s ability to use it in the narrow window before a full response is complete.
The case study suggests the system also uses context-linked identities. In practice, that means accounts active on the same compromised surfaces can be contained together, not just the single account directly tied to the latest alert. This is a major step up from older account-only workflows, because real attackers rarely stay within one credential boundary once they find a rich host.
At one point, the attacker was operating with Schema Admin context, which is exactly the sort of credential state that can turn a difficult incident into an existential one. Microsoft notes that the subsequent activity was repeatedly contained, forcing the adversary to keep changing tactics rather than consolidating control. That is a strong sign that the defender’s containment logic was following the blast radius rather than staying fixed on a single host.
Microsoft says the account used for this pivot was later contained, limiting further movement. This is a good example of why identity response must be coordinated across platforms. It is not enough to protect the domain controller if the synchronization plane can be used as a second door into the same trust ecosystem.
Microsoft says attack disruption repeatedly severed the attacker’s sessions and blocked new sign-ins. On July 28, 2025, the campaign lost momentum and stopped. That end state is important because it demonstrates that disruption can have cumulative effect: even if it does not stop the first theft event, it can eventually deprive the adversary of usable operating room.
That is a key conceptual win for predictive shielding. The goal is not merely to block a single login event. It is to make the attacker’s whole post-compromise workflow progressively less reliable until the campaign becomes too inefficient to continue. That is a very different model from the old “detect, alert, and clean up” cadence.
That matters because the best defenders do not treat domain compromise as a mystery event. They treat it as a repeatable sequence with recognizable stages and characteristic pressure points. Predictive shielding is most valuable at the stage where the sequence is still reversible.
It also helps explain where predictive shielding adds the most value. The feature is strongest when the attack relies on valid accounts, repeated pivots, and cross-system credential reuse. Those behaviors are common in ATT&CK-mapped identity campaigns, which makes the Microsoft approach especially relevant for enterprise defenders who live in that threat class every day.
There is also the broader governance issue of automation trust. Teams will need to decide when they are comfortable letting a platform preemptively contain accounts tied to suspicious hosts, especially in large organizations where account ownership is messy and critical tasks are often performed by a small number of elevated identities. The promise is strong, but the operational discipline around it will determine whether it becomes a force multiplier or a new source of friction.
It will also be worth watching how customers operationalize the feature in hybrid environments. Organizations with on-prem AD, Exchange, Entra Connect, backup platforms, and legacy service accounts may benefit the most, but they are also the most likely to face account-ownership complexity and dependency issues. The harder the environment, the more valuable the protection — and the more careful the rollout.
The Microsoft case study is persuasive because it shows the difference between simply seeing an attack and actively shrinking its future. When domain compromise becomes a race against credential reuse, the defender’s edge comes from making the attacker’s next move unavailable before it becomes obvious. That is the strategic promise of predictive shielding, and it is likely to become more important as identity remains the primary battleground in enterprise security.
Source: Microsoft Containing a domain compromise: How predictive shielding shut down lateral movement | Microsoft Security Blog
 Overview
Overview
Domain compromise is the moment when a limited foothold stops being a local incident and becomes an enterprise-wide identity crisis. Once an attacker gains control over an Active Directory domain, the environment’s trust fabric itself becomes the weapon: group memberships can be altered, ACLs can be rewritten, Kerberos artifacts can be minted, and policy can be pushed at scale through normal administrative channels. That shift is why defenders treat domain-admin loss as a critical event rather than just another compromised account.What makes the problem harder is speed. Microsoft’s case study stresses that in many real-world intrusions, domain-level credentials are exposed almost immediately after the initial breach, and the attacker often uses them before defenders have enough visibility to fully scope the damage. That creates a nasty asymmetry: the attacker needs only one successful credential path, while the defender has to inventory, isolate, validate, and restore trust across a live identity platform.
The article’s central argument is that traditional containment is usually too reactive for this kind of campaign. If the defender waits for a credential to be observed doing something obviously malicious, the adversary may already have used it to move into the directory, Exchange, backup systems, or cloud sync infrastructure. Microsoft’s response is to shift from activity-based detection to exposure-based containment, where high-confidence signals of credential theft trigger automated restrictions before the exposed identity is operationalized.
That is the core purpose of predictive shielding inside Microsoft Defender’s automatic attack disruption. It is designed to predict where the attacker will pivot next, identify likely exposed identities, and temporarily contain those identities to block sign-ins and interactive abuse while remediation is underway. Microsoft positions this as an out-of-the-box enhancement for Defender for Endpoint P2 customers who meet the necessary prerequisites.
The significance of the case goes beyond one organization. It shows how modern identity defense is no longer just about locking accounts after compromise; it is about building a response model that can keep up with credential replay, delegated access abuse, and the attacker’s tendency to return with new tooling when the first route is shut down. In that sense, this is not simply a Microsoft feature story. It is a practical demonstration of how defenders can turn the attacker’s own momentum into a containment opportunity.
Why Domain Compromise Changes the Game
A domain compromise is not merely “more severe” than a workstation compromise; it is categorically different. A single trusted identity can become a control plane for the rest of the network, especially if the attacker reaches privileged administrative accounts or directory secrets. From that point on, the attacker can stop behaving like an intruder and start behaving like an administrator, which makes many normal controls less useful.The Microsoft case study underscores how quickly that threshold can be crossed. The attacker did not linger in a simple one-host scenario. They moved from web shell activity on an IIS server into credential dumping, remote task creation, NTDS-related activity on a domain controller, Exchange delegation changes, and then password spraying and repeated lateral attempts against other servers. The shape of the intrusion is the point: each new credential source widened the blast radius.
Why identity infrastructure is a special target
Identity infrastructure cannot simply be shut off in the middle of an incident. Domain controllers, authentication services, service principals, backup systems, and directory synchronization paths are production dependencies, so responders have to preserve business continuity while simultaneously restoring trust. That makes domain compromise a uniquely painful balance between containment and availability.- Domain controllers are too central to simply power down.
- Service accounts often have broad and under-documented reach.
- Restoration usually requires sequential cleanup work.
- Credential artifacts can be reused faster than manual response teams can move.
- Trust recovery often needs krbtgt rotation, ACL validation, and GPO cleanup.
The defender’s timing problem
The article’s most important operational point is that defenders are racing against a clock they rarely control. A compromised credential may be used minutes after exposure, but the security team often still has to corroborate evidence, determine scope, and decide whether blocking the account will break business workflows. Predictive shielding exists to compress that decision cycle.This is why the feature matters most in identity-heavy enterprises. A mature attacker does not need to crack every barrier; they only need one privileged seam that gets them past the first layer of containment. If the defender can preemptively contain likely exposed identities before they are abused, the attacker loses the simplest and most scalable path to domain-wide control.
The Initial Foothold: IIS, Web Shells, and SYSTEM
The attack began with a familiar but still effective pattern: exploitation of an internet-facing IIS server through a file-upload flaw, followed by deployment of a web shell. That first step matters because public-facing applications still remain one of the cleanest routes from the internet to an internal foothold. Once the web shell was in place, the attacker could issue commands, enumerate the environment, and begin privilege escalation.The operator then escalated to NT AUTHORITY\SYSTEM by abusing a Potato-class token impersonation primitive such as BadPotato. That detail is important because SYSTEM on a server is often the gateway to local credential access, service manipulation, and broader post-exploitation flexibility. In practical terms, the attacker had crossed from application-level abuse into host-level control.
From web shell to high-value host control
Microsoft notes that the attacker used the compromised IIS service account to attempt password resets on high-impact identities. That tactic is significant because it avoids some of the telltale traces of direct credential dumping and instead leans on administrative workflow abuse. It is also a reminder that attackers often prefer the easiest path to trust, not the most glamorous exploit.The threat actor also deployed Mimikatz to dump logon secrets from LSASS, SAM, and related sources. Once that happens, the attacker no longer needs to rely solely on local privilege escalation; they can harvest usable credentials and replay them against other systems. This is where the incident’s logic begins to shift from host compromise to identity compromise.
- Public-facing application exploitation provided initial access.
- Token impersonation raised the attacker to SYSTEM.
- Password reset attempts targeted high-value identities.
- Mimikatz unlocked credential material on the host.
- Local success quickly became an identity problem.
Why early containment is different from late containment
Microsoft’s commentary makes an important distinction: if predictive shielding had existed at this stage, the intrusion might have been stopped before it expanded beyond the first host. That is the classic containment window defenders want, because it keeps the incident bounded at the edge rather than inside the directory. Once the attacker reaches directory credentials, the problem becomes exponentially more expensive.This is also the stage where host-scoped containment still makes sense. Blocking the malicious device, isolating the server, and preventing further credential theft can be highly effective before the attacker reaches domain-level assets. After that, however, the response needs to evolve from endpoint containment to identity containment, because the stolen material itself can travel independently of the original machine.
The First Pivot: Directory Secrets and Exchange Abuse
Within 24 hours, the attacker had moved from the initial server compromise into NTDS collection on a domain controller. Microsoft describes the operator remotely creating a scheduled task on the domain controller, triggering snapshot-style directory activity, and packaging the output with makecab.exe. That is a classic sign that the attacker wanted offline access to directory secrets at scale, not just a single account.This is the point at which the incident becomes much harder to contain in a conventional way. Once directory credential material is extracted, the attacker can return to the environment repeatedly, use valid accounts, and pivot across authentication paths that defenders still need to keep running. The blog is blunt that at this stage, the first malicious action already surfaced the entire Active Directory credential set, making simple host cleanup insufficient.
Exchange delegation as force multiplier
The attacker also planted a Godzilla web shell on Exchange Server and used privileged context to enumerate accounts with ApplicationImpersonation role assignments. They then used Add-MailboxPermission to grant broad mailbox access to a delegated principal. This is especially dangerous because mailbox access can reveal planning, password reset workflows, external communications, and other information that helps the attacker expand operational insight.That means the breach was no longer just about file servers or domain credentials. It became a confidentiality, privilege, and business-process problem all at once. In many organizations, Exchange is still a central repository of human and machine trust signals, which makes delegated mailbox access a potent multiplier for further compromise.
Why defenders lose ground here
The danger of directory credential exposure is not simply that one account is lost. It is that the attacker now has a catalog of routes, and every one of those routes can be tested faster than a human incident team can complete a full trust review. That is why Microsoft frames this as a race between exposure and containment.- NTDS access implies broad directory-level impact.
- Exchange delegation can reveal sensitive identity and business data.
- Scheduled tasks provide stealthier execution on domain controllers.
- Offline directory material enables repeated attempts.
- The attacker can now pivot with valid identities, not just malware.
Scale, Reuse, and the Password-Spraying Phase
The next phase shows the practical cost of delayed containment. Weeks later, the attacker returned with tools such as secretsdump and PsExec, and Defender repeatedly disrupted the abused accounts used in those attempts. That is a sign that automatic attack disruption was helping, but it was still reacting to already-exposed identities rather than preventing the first reuse of those credentials.The adversary then launched a broad password spray from the originally compromised IIS server and gained access to at least 14 servers through password reuse. That detail matters because it illustrates how stolen or guessed credentials can still be operationally powerful even when defenders have some active blocking in place. Once multiple credentials are in circulation, the attacker has options.
Why credential reuse is so dangerous
Password spraying is effective because organizations still rely on weak reuse patterns, especially across service accounts and human accounts that are difficult to rotate. Even when multi-factor authentication and modern policies exist, older systems and service dependencies can create exceptions that attackers happily exploit. The Microsoft case shows how one compromised host can become the launchpad for an enterprise-wide authentication test.The attacker also attempted remote credential dumping against multiple domain controllers and another IIS server using domain and service principals. That behavior reveals a critical truth: once the adversary has enough identities, they stop acting like a single operator and start acting like a distributed authentication campaign. Containment must keep pace with that mobility.
Automatic attack disruption, but not yet predictive
Microsoft says its attack disruption controls were active and did block sessions and sign-ins, but the attacker had already accumulated credential material earlier in the campaign. This is the exact “speed gap” the company wants predictive shielding to address. In other words, the feature is not about replacing detection; it is about moving the containment line earlier in the kill chain.- Password spraying exploited credential reuse at scale.
- Multiple servers were reached through valid but compromised identities.
- Domain controllers remained a priority target.
- Automatic disruption helped, but it was still behind the attacker’s first reuse attempts.
- The attack showed why exposure-based blocking is more powerful than abuse-based blocking.
Predictive Shielding: How Exposure-Based Containment Works
Predictive shielding is Microsoft’s answer to the moment when an attacker has not yet fully operationalized stolen credentials but is clearly positioned to do so. Rather than waiting until a sign-in or lateral move looks malicious, Defender looks for high-confidence signals of credential theft on a device and then infers which identities may have been exposed there. That lets the system act before the adversary can meaningfully pivot.The mechanism is straightforward but strategically powerful. Defender detects post-breach activity associated with credential exposure, evaluates which high-privilege identities were likely affected, and contains those identities to reduce lateral movement and high-impact identity operations. The idea is not to punish the account; it is to remove the attacker’s ability to use it in the narrow window before a full response is complete.
What makes the shielding “predictive”
The word predictive is doing a lot of work here. Microsoft is not claiming perfect foresight; it is using high-confidence behavioral and contextual signals to estimate where the attacker’s next move will be. That distinction matters because the value of the feature comes from risk-based anticipation, not magical certainty.The case study suggests the system also uses context-linked identities. In practice, that means accounts active on the same compromised surfaces can be contained together, not just the single account directly tied to the latest alert. This is a major step up from older account-only workflows, because real attackers rarely stay within one credential boundary once they find a rich host.
Why this matters for domain admins and tier-0 accounts
The article specifically calls out the protection of high-privilege identities such as domain admins. That is where predictive shielding becomes most consequential, because one exposed admin credential can collapse hours or days of defensive work into a single malicious sign-in. If the platform can contain a domain admin before abuse, it can prevent the usual catastrophic jump into policy, directory, and trust manipulation.- It blocks likely exposed identities before they are used.
- It reduces attacker options at the moment of opportunity.
- It can contain context-linked accounts, not just one account.
- It helps preserve business continuity by avoiding whole-system shutdowns.
- It is designed to narrow the blast radius while investigation continues.
The Second Pivot: Alternative Credential Paths
Once the high-value identities were pre-contained, the attacker shifted to other routes, including Apache Tomcat servers. They compromised three Tomcat instances, dropped the Godzilla web shell again, and used Invoke-Mimikatz to harvest additional credentials. That pattern tells you something important about attacker psychology: if one path is blocked, they do not stop, they simply hunt for another one.At one point, the attacker was operating with Schema Admin context, which is exactly the sort of credential state that can turn a difficult incident into an existential one. Microsoft notes that the subsequent activity was repeatedly contained, forcing the adversary to keep changing tactics rather than consolidating control. That is a strong sign that the defender’s containment logic was following the blast radius rather than staying fixed on a single host.
Microsoft Entra Connect as a high-value bridge
The attacker also used Impacket WmiExec to reach Microsoft Entra Connect servers and try to extract synchronization credentials. That target is especially notable because Entra Connect sits at the intersection of on-premises identity and cloud identity, making it a bridge rather than just another server. If that bridge falls, attackers can potentially move from the local directory into the cloud trust path.Microsoft says the account used for this pivot was later contained, limiting further movement. This is a good example of why identity response must be coordinated across platforms. It is not enough to protect the domain controller if the synchronization plane can be used as a second door into the same trust ecosystem.
Why context-linked containment matters
A purely reactive model would have to rediscover each new credential source separately. Predictive shielding instead appears to map likely exposure across the surfaces where the attacker had already been operating. That means one compromised machine can lead to a broader containment set, which is exactly what defenders need when the adversary is already moving laterally.- Tomcat became an alternate credential source.
- Schema Admin access raised the stakes dramatically.
- Entra Connect introduced cloud identity implications.
- The attacker kept searching for fresh paths once major accounts were contained.
- Each new pivot increased the value of context-aware containment.
The Final Phase: Exhaustion, MiniDumps, and Shutdown
By the final phase, the threat actor was attempting more desperate credential-access activity, including a full LSASS dump on a file-sharing server using comsvcs.dll MiniDump under a domain user account. They also returned to NTDS-related activity, which suggests they were still searching for a path to fresh credential material even after multiple containment actions had fired.Microsoft says attack disruption repeatedly severed the attacker’s sessions and blocked new sign-ins. On July 28, 2025, the campaign lost momentum and stopped. That end state is important because it demonstrates that disruption can have cumulative effect: even if it does not stop the first theft event, it can eventually deprive the adversary of usable operating room.
What “lost momentum” actually means
In practical incident-response terms, “lost momentum” means the attacker could no longer maintain a stable credential supply line. When valid accounts get contained faster than they can be operationalized, the adversary is forced into repeated fallback attempts. Each fallback increases noise, increases detection opportunities, and reduces the odds that the operator can preserve stealth.That is a key conceptual win for predictive shielding. The goal is not merely to block a single login event. It is to make the attacker’s whole post-compromise workflow progressively less reliable until the campaign becomes too inefficient to continue. That is a very different model from the old “detect, alert, and clean up” cadence.
Why the ending matters for defenders
This incident illustrates that containment can be strategic rather than binary. The attacker was not necessarily destroyed immediately, but their options were increasingly constrained until the operation faded. That matters because many defenders still define success too narrowly, as if the only good outcome is an instant stop. In reality, degradation can be the decisive win.- Sessions were severed repeatedly.
- New sign-ins were blocked.
- Credential supply became unreliable.
- Alternate pivots were contained in sequence.
- The campaign eventually collapsed under its own friction.
MITRE ATT&CK Mapping and Tradecraft Lessons
Microsoft’s ATT&CK mapping shows a very complete post-exploitation chain, and that breadth is part of the lesson. The campaign included Exploit Public-Facing Application, web shell persistence, PowerShell execution, privilege escalation through token impersonation, LSASS and NTDS credential access, scheduled tasks, remote admin shares, WMI, password spraying, mailbox collection, web-based command and control, file cleanup, and account manipulation. In other words, this was not a single exploit; it was a full identity-compromise workflow.That matters because the best defenders do not treat domain compromise as a mystery event. They treat it as a repeatable sequence with recognizable stages and characteristic pressure points. Predictive shielding is most valuable at the stage where the sequence is still reversible.
A practical reading of the ATT&CK chain
The presence of T1053.005 Scheduled Task, T1003.003 NTDS, T1110.003 Password Spraying, and T1098 Account Manipulation tells a coherent story: the attacker wanted durable access, broad credential reach, and the ability to keep testing new routes after being blocked. Those are exactly the behaviors that move a breach from annoying to catastrophic.- Web shell deployment enabled remote command execution.
- PowerShell and WMI were used for flexible, low-friction management abuse.
- Password spraying expanded the useful identity set.
- NTDS and LSASS access supplied fresh credential material.
- Account manipulation helped sustain access and broaden privileges.
Why ATT&CK still matters in the age of automation
There is a temptation to think automated defense makes technique mapping less important. The opposite is true. The more sophisticated the response engine, the more the defender needs good taxonomy to understand what it is actually seeing. ATT&CK gives responders a shared language for attack shape, and that language is still useful when the machine is doing part of the triage.It also helps explain where predictive shielding adds the most value. The feature is strongest when the attack relies on valid accounts, repeated pivots, and cross-system credential reuse. Those behaviors are common in ATT&CK-mapped identity campaigns, which makes the Microsoft approach especially relevant for enterprise defenders who live in that threat class every day.
Strengths and Opportunities
Predictive shielding is compelling because it moves containment earlier without requiring defenders to guess blindly. It turns stolen-credential exposure into a first-class response signal, which is a much better fit for modern identity attacks than waiting for obvious abuse. The case study also shows that the feature can meaningfully disrupt an attacker’s ability to keep finding fresh pivots, which is exactly what a mature enterprise wants from automated defense.- It shortens the time between credential exposure and containment.
- It reduces reliance on manual scoping during the most chaotic phase of response.
- It can block context-linked identities, not just the originally flagged account.
- It helps preserve business continuity by avoiding broad infrastructure shutdowns.
- It is especially valuable for domain admins and other tier-0 identities.
- It can force attackers into slower, noisier fallback behaviors.
- It integrates naturally with existing automatic attack disruption workflows.
Risks and Concerns
The obvious risk is false containment. If automated shielding blocks a legitimate high-privilege account during a business-critical process, the operational impact could be serious. That makes the quality of the exposure signal and the scope of context-linking absolutely critical, especially in environments with tightly scheduled administrative work or fragile legacy dependencies.- Over-containment could disrupt production identity workflows.
- Under-containment could allow a compromised admin to pivot.
- Context-linked identity logic may be hard to tune in complex enterprises.
- Legacy systems can create false confidence in account ownership and use.
- Hybrid identity bridges such as Entra Connect widen the blast radius.
- Response teams may still need manual cleanup after automated blocking.
- Attackers may shift to alternate credential sources if one route is closed.
There is also the broader governance issue of automation trust. Teams will need to decide when they are comfortable letting a platform preemptively contain accounts tied to suspicious hosts, especially in large organizations where account ownership is messy and critical tasks are often performed by a small number of elevated identities. The promise is strong, but the operational discipline around it will determine whether it becomes a force multiplier or a new source of friction.
What to Watch Next
The most important thing to watch is how Microsoft expands the prediction logic behind shielding. The case study hints that the platform will keep broadening its use of context-linked identities and exposure signals, which could make containment more precise over time. If Microsoft can do that without introducing operational drag, the feature may become a standard part of enterprise identity defense rather than a niche enhancement.It will also be worth watching how customers operationalize the feature in hybrid environments. Organizations with on-prem AD, Exchange, Entra Connect, backup platforms, and legacy service accounts may benefit the most, but they are also the most likely to face account-ownership complexity and dependency issues. The harder the environment, the more valuable the protection — and the more careful the rollout.
Key signals to monitor
- Broader support for context-linked identity containment.
- Better precision around credential-exposure detection.
- Enterprise guidance for hybrid identity and synchronization servers.
- Reduced attacker dwell time in identity-heavy intrusions.
- Fewer successful password-spraying follow-ons after initial host compromise.
- More case studies showing pre-abuse containment of privileged accounts.
The Microsoft case study is persuasive because it shows the difference between simply seeing an attack and actively shrinking its future. When domain compromise becomes a race against credential reuse, the defender’s edge comes from making the attacker’s next move unavailable before it becomes obvious. That is the strategic promise of predictive shielding, and it is likely to become more important as identity remains the primary battleground in enterprise security.
Source: Microsoft Containing a domain compromise: How predictive shielding shut down lateral movement | Microsoft Security Blog
Last edited: