Microsoft’s latest push to “raise the bar” for Windows drivers is one of the clearest, most consequential platform moves in years — it changes not just how drivers are certified and signed, but how much driver code Microsoft expects to live in the kernel at all, and it creates new technical guardrails designed to contain faults before they become system outages.
The impetus for Microsoft’s renewed focus on driver resiliency is both immediate and structural. The company responded to a high-profile July 2024 incident in which a faulty security update from a third‑party endpoint vendor crashed millions of Windows machines worldwide; that event crystallized the risk of third‑party kernel code causing mass outages and accelerated Microsoft’s resiliency plans. Independent reporting and industry reaction tied the outage to the broader push to move fragile, high‑impact logic out of kernel space and build recovery tooling into the platform. Microsoft’s public materials and engineering blogs now describe a multi‑pronged approach that combines policy (higher driver signing and certification requirements), platform changes (expanded in‑box drivers and APIs), and technical constraints (compiler safeguards, driver isolation, DMA‑remapping and other hardware-backed protections). Together these are intended to reduce the amount of third‑party code that runs in kernel mode and to limit the blast radius when things do go wrong.
The transition will not be instantaneous. Expect a hybrid era where inbox drivers handle common scenarios, vendor kernel drivers deliver premium features, and administrators steward devices through more deliberate pilot and rollout practices. For platform reliability — the ability of Windows to survive a misbehaving third‑party binary without becoming unusable — this package of changes materially strengthens the OS. For high‑performance device vendors and professionals who rely on every millisecond of latency or device‑specific features, the vendor driver option remains, but under a more demanding certification and quality regime.
The net effect: Windows 11 is being re‑architected to tolerate third‑party mistakes better, reduce kernel bloat, and centralize baseline compatibility. That’s a sensible direction for a platform that powers critical infrastructure and billions of endpoints — and it’s a structural change the ecosystem has been nudging toward for years. The next 12–24 months will show how effectively Microsoft and its partners translate the plan into production quality, and whether smaller vendors can keep pace with the new requirements.
Microsoft has chosen stability and containment over laissez‑faire kernel access, and that choice will reshape driver development, update flows, and the platform’s attack surface for years to come.
Source: Windows Central https://www.windowscentral.com/micr...ed-on-windows-11-heres-the-important-details/
 Background / Overview
Background / Overview
The impetus for Microsoft’s renewed focus on driver resiliency is both immediate and structural. The company responded to a high-profile July 2024 incident in which a faulty security update from a third‑party endpoint vendor crashed millions of Windows machines worldwide; that event crystallized the risk of third‑party kernel code causing mass outages and accelerated Microsoft’s resiliency plans. Independent reporting and industry reaction tied the outage to the broader push to move fragile, high‑impact logic out of kernel space and build recovery tooling into the platform. Microsoft’s public materials and engineering blogs now describe a multi‑pronged approach that combines policy (higher driver signing and certification requirements), platform changes (expanded in‑box drivers and APIs), and technical constraints (compiler safeguards, driver isolation, DMA‑remapping and other hardware-backed protections). Together these are intended to reduce the amount of third‑party code that runs in kernel mode and to limit the blast radius when things do go wrong. What Microsoft announced — the headline changes
- A higher bar for signed drivers. Microsoft says signed drivers will need to pass many additional certification tests and meet stricter security and resiliency criteria before receiving the platform’s blessing. This updates the historical WHQL/Hardware Dev Center flows with stronger checks.
- Bigger, higher‑quality in‑box drivers and APIs. Microsoft is expanding the set of drivers it ships in Windows and the APIs those drivers expose so OEMs and vendors can rely on standardized, maintained components rather than shipping custom kernel drivers for every device. The company has already publicized work on new class drivers (for example, a low‑latency USB Audio Class 2 driver with ASIO support) and other platform class drivers that lower the need for bespoke kernel code.
- A plan to reduce kernel‑mode code over time. Over the coming years Microsoft expects significant reductions in kernel‑mode footprint across many driver categories — networking, cameras, USB, printers, storage, audio, battery management and others — often by providing an inbox driver, moving logic to user‑mode, or offering standardized extension points. Graphics drivers are explicitly called out as a continued kernel‑mode exception.
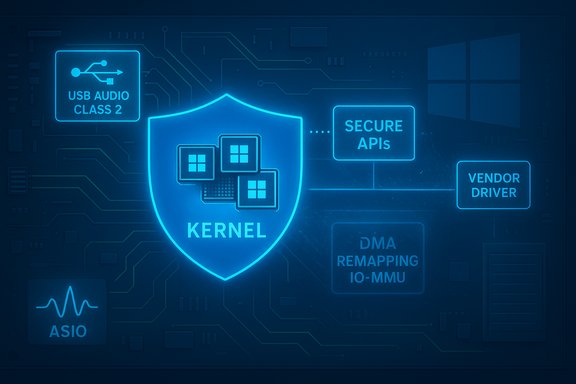
- Practical kernel guardrails. Microsoft will add mandatory compiler safeguards to constrain driver behavior, introduce driver isolation to limit crash blast radius, and adopt DMA‑remapping / IO‑MMU protections to prevent accidental or malicious driver access to kernel memory. These are engineering controls intended to make buggy or malicious drivers far less likely to cause system‑wide failures.
- Windows will still support third‑party kernel drivers. Microsoft is careful to say partners may still ship kernel‑mode drivers where Windows lacks an inbox replacement; the move is meant to reduce kernel drivers, not to ban them. Graphics drivers, for example, will continue operating in kernel mode.
Why this matters now: the resiliency context
The July 2024 security‑software update failure — commonly referenced in industry coverage — dramatically illustrated what can happen when widely deployed kernel‑level code misbehaves: millions of devices crashed, critical services were disrupted, and large organizations incurred major operational and financial losses. Coverage by major outlets documented the scale and fallout, and regulators and enterprise customers took notice. Microsoft’s Resiliency Initiative and the new driver focus directly address that class of systemic risk by changing platform expectations and adding recovery tooling. Microsoft’s official messaging frames the work as learning from that incident: build mechanisms to prevent a single vendor bug from producing a large‑scale outage and make it far easier to remediate devices that do fail to boot. Those platform investments include Quick Machine Recovery (Windows RE‑driven automated recovery flows), stronger rollout safeguards for high‑risk updates, and private previews to help security vendors move components out of the kernel.Technical deep dive: the new guardrails explained
1. Mandatory compiler safeguards
Microsoft plans to require changes in how kernel drivers are compiled so the generated binaries follow more constrained, auditable patterns. The goal is to catch unsafe constructs early and to eliminate classes of vulnerabilities (for example, certain unbounded memory accesses or unsafe control‑flow patterns) by leveraging tooling and compiler enforcement. This echoes wider industry moves to combine static enforcement with safer memory models. The new compiler rules don’t replace code reviews or runtime checks, but they increase the cost of shipping risky binaries.2. Driver isolation
Driver isolation means running third‑party drivers in separate protection domains so a misbehaving driver can be restarted, disabled or sandboxed without taking down the kernel. There are multiple implementation patterns (process isolation, lightweight VM or microkernel‑style driver servers, or driver host processes). By isolating drivers, Windows can limit the “blast radius” — a single buggy network or storage driver would no longer be able to crash the whole system. This is not new research; similar isolation approaches have been explored for years — what matters now is Microsoft’s commitment to ship and enforce isolation at scale for important driver classes.3. DMA‑remapping and IO‑MMU protections
Direct Memory Access (DMA) remains a powerful capability for device performance but also a potential attack or crash vector if devices can write directly into kernel memory. Microsoft is requiring or encouraging DMA‑remapping via the platform’s IO‑MMU (IOMMU) features — this prevents devices (and therefore their drivers) from being able to touch arbitrary kernel addresses. The hardware-backed remapping closes a classic avenue for both accidental corruption and targeted exploitation.4. Expanded inbox drivers and APIs
Instead of every vendor shipping custom kernel drivers, Microsoft is building more and better inbox drivers (class drivers) and richer user‑mode APIs. A concrete example is Microsoft’s new USB Audio Class 2 in‑box driver that includes a native ASIO interface and low‑latency modes — code Microsoft is developing with partners and publishing on GitHub as a reference implementation. Making high‑quality class drivers available reduces pressure on vendors to ship kernel code for common functionality.What this actually changes for driver authors and OEMs
- Drivers that previously had to be kernel‑mode to hit functionality or performance targets will face two incentives to change: Microsoft’s inbox alternatives (fewer reasons to ship bespoke kernel code) and a higher certification bar for any signed kernel driver.
- Vendors who still need kernel behavior (for advanced features or performance parity) can continue to ship kernel drivers, but they will need to meet stricter certification, toolchain and testing expectations. Some vendors may opt instead to ship user‑mode components plus a minimal kernel shim, or to invest in optimized inbox‑compatible drivers.
- OEMs will gain a larger set of Microsoft‑provided drivers in the OS image, potentially simplifying factory imaging and reducing driver bloat. That can be a net benefit for stability and servicing, but it will shift more of the maintenance burden for baseline drivers to Microsoft and raise the importance of rapid vendor collaboration on feature or bug fixes.
- Security and endpoint vendors will be asked (and in some program contexts required) to adopt safer deployment and update practices; Microsoft plans private previews and migration guidance for vendors to move high‑risk logic out of kernel mode. This is a major evolution in the vendor‑platform relationship for AV/EDR products.
How the platform and update model will behave (practical implications)
- Windows Update and Microsoft’s driver catalog will become the default channel for high‑quality drivers; Microsoft says it’s cleaning up legacy and expired entries to reduce risk and improve matching. That reduces accidental installs of outdated or incompatible kernel code in many cases. Administrators should expect more targeted inbox and Windows Update delivery of drivers, and OEMs should coordinate publishing to ensure devices receive appropriate binaries.
- Microsoft’s servicing and rollout tooling (safeguards, pilot rings, targeted rollout tokens) will play a more central role when distributing driver updates and security partner patches. That mirrors the “safe deployment” model Microsoft is promoting for security vendors.
- For enterprises and IT pros: expect to validate new driver builds in pilot rings, maintain refined rollback plans, and monitor Windows Update for targeted offers. Do not assume Windows Update always has the newest vendor feature driver; Microsoft’s catalog often favors broadly compatible packages. If you need vendor‑specific features, keep a vendor delivery path ready.
Strengths of Microsoft’s approach
- Systemic reduction in catastrophic risk. By constraining kernel‑mode surface area and adding containment, Microsoft reduces the chance that a single third‑party bug causes a mass outage. The CrowdStrike episode made this painfully obvious; the new strategy specifically targets that problem class.
- Better out‑of‑box experiences. Expanding in‑box drivers for common devices (audio, USB, printers, cameras) reduces dependency on vendor downloads and improves plug‑and‑play reliability across Windows 11 installs. The announced USB Audio Class 2/ASIO class driver is an example of a practical win for users.
- Clearer testing and rollout discipline. The emphasis on improved update deployment patterns, pilot rings, and rollback tooling should reduce upgrade regressions and make Windows updates safer at scale.
Risks, limitations and unanswered questions
- Feature tradeoffs. Class drivers are rarely as feature‑complete as manufacturer‑optimized drivers. Vendors that previously relied on full kernel‑mode stacks to expose special hardware features, firmware hooks, or DSP pipelines may find inbox drivers insufficient for premium use cases. That could split the market between inbox‑compatible devices (which “just work”) and vendor‑tuned devices for professionals.
- Performance sensitivity. For very high‑performance or ultra‑low‑latency scenarios, user‑mode alternatives or inbox drivers may not initially match vendor kernel drivers. Microsoft’s approach accepts a hybrid world — inbox drivers for baseline compatibility and vendor drivers for the last mile of performance — but that means some users will still need vendor drivers and vendors must remain committed to supporting them.
- Vendor burden and schedule friction. The new requirements and stricter certification rules raise the bar for driver authors. While that increases quality, it also increases the testing, toolchain and certification overhead for vendors — especially smaller firms — which could slow driver releases or reduce device features if vendors cannot or will not invest.
- Compatibility and fragmentation risk. If Microsoft’s inbox drivers evolve faster on some branches (for example, Windows 11 platform images targeted at specific silicon), OEMs might ship variant images or vendor drivers tied to those images, creating additional complexity for IT and support teams. Microsoft has used targeted platform images in the past, and those models can complicate servicing and management unless communication is crisp.
- Enforcement and telemetry opacity. The effectiveness of the new certification and safeguard model depends on Microsoft’s ability to enforce standards and to get telemetry about driver behavior. The industry will watch for transparency in both testing criteria and how Microsoft applies rollout holds when driver issues surface.
- Timelines and scope remain partly fuzzy. Microsoft has committed previews and private partner programs, and many of these changes will be phased in over years. Specific ship dates for each inbox driver, compiler change, or enforcement policy vary by class and partner readiness; that creates a transition period where both old and new models must coexist.
Practical recommendations — what stakeholders should do now
- For driver authors and ISVs:
- Audit kernel code and evaluate moving non‑critical logic to user mode.
- Start adopting Microsoft’s inbox driver APIs where possible and engage early with the Windows Hardware Dev Center for certification guidance.
- Update toolchains and test against the new compiler safeguards once private previews are available.
- For OEMs:
- Coordinate on device catalog entries and validate factory images against Microsoft’s expanded inbox driver set.
- Pilot inbox driver replacements on representative hardware and maintain vendor‑supplied drivers for premium features where necessary.
- For enterprise IT:
- Strengthen pilot rings and validation cycles for driver updates and feature updates.
- Prepare rollback/runbook procedures for driver‑related incidents and consider using protected servicing channels (WSUS/Intune) to control driver distribution.
- For security vendors:
- If you operate kernel‑mode components, engage Microsoft’s private previews to test migration paths to user mode and adopt the safe deployment practices Microsoft champions.
- For power users and consumers:
- Rely on Windows Update for stable, broadly compatible drivers for most devices, but keep vendor sites available for device‑specific optimizations (games, audio, capture hardware).
- When troubleshooting driver problems, inspect Device Manager details and prefer vendor support channels for hardware that needs specialized features.
Final analysis — balancing stability, innovation and vendor choice
Microsoft’s driver‑resiliency strategy is a pragmatic, technically credible response to a systemic problem: too much trusted code running at the highest privilege, deployed rapidly by a diverse vendor ecosystem. By combining stricter signing and certification rules, expanding inbox drivers, and adding technical containment (compiler checks, driver isolation and DMA remapping), Microsoft reduces the odds that a single vendor bug will cascade into a large‑scale outage. That’s a clear win for enterprise reliability and for everyday users who value stability. At the same time, the approach recognizes that device vendors will continue to need space to innovate. Microsoft’s stated intention to allow third‑party kernel drivers where the platform lacks functionality preserves vendor freedom, but it also raises the bar: kernel drivers will face stricter scrutiny, and vendors must invest more in testing and certification. That tradeoff favors larger vendors or those willing to align with Microsoft’s new processes, and it will likely reshape how smaller OEMs approach driver development.The transition will not be instantaneous. Expect a hybrid era where inbox drivers handle common scenarios, vendor kernel drivers deliver premium features, and administrators steward devices through more deliberate pilot and rollout practices. For platform reliability — the ability of Windows to survive a misbehaving third‑party binary without becoming unusable — this package of changes materially strengthens the OS. For high‑performance device vendors and professionals who rely on every millisecond of latency or device‑specific features, the vendor driver option remains, but under a more demanding certification and quality regime.
The net effect: Windows 11 is being re‑architected to tolerate third‑party mistakes better, reduce kernel bloat, and centralize baseline compatibility. That’s a sensible direction for a platform that powers critical infrastructure and billions of endpoints — and it’s a structural change the ecosystem has been nudging toward for years. The next 12–24 months will show how effectively Microsoft and its partners translate the plan into production quality, and whether smaller vendors can keep pace with the new requirements.
Microsoft has chosen stability and containment over laissez‑faire kernel access, and that choice will reshape driver development, update flows, and the platform’s attack surface for years to come.
Source: Windows Central https://www.windowscentral.com/micr...ed-on-windows-11-heres-the-important-details/