A newly reported OCFS2 filesystem vulnerability described as "relax BUG to ocfs2_error in __ocfs2_move_extent" highlights a recurring class of Linux kernel filesystem defects where aggressive kernel assertions escalate recoverable metadata inconsistencies into host‑crashing kernel BUGs; available analyses show maintainers addressed the issue with minimal, defensive changes aimed at avoiding ASSERT‑style panics while forcing the kernel to re-read authoritative on‑disk metadata, but the exact CVE mapping in public trackers requires careful verification for your distribution and vendor.
Background
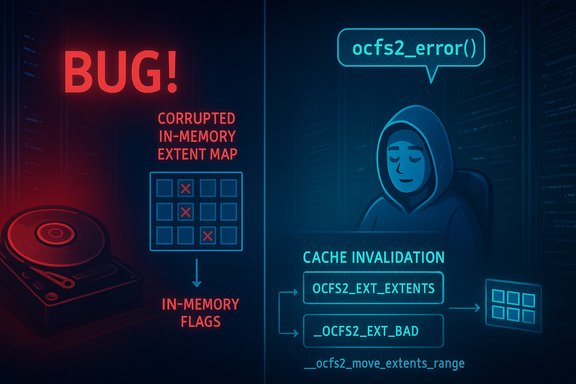
OCFS2 (Oracle Cluster File System 2) is a cluster-aware filesystem used in shared‑block storage setups and various appliances. The vulnerability under discussion stems from a race and cache‑consistency problem that can leave in‑memory extent metadata inconsistent with the on‑disk state after extent‑move or defragmentation operations. When downstream code assumes a cached flag that no longer matches the on‑disk extent, kernel assertions can be triggered, producing an OOPS or panic. This fault mode is primarily an availability problem rather than a straightforward remote code execution vector.The phrasing "relax BUG to ocfs2_error in __ocfs2_move_extent" indicates a remediation strategy where a hard kernel BUG (which aborts execution) is converted to an error return path that lets the filesystem handle the inconsistency more gracefully. Several independent analyses of the underlying OCFS2 defect describe complementary or adjacent fixes such as clearing extent‑map cache entries after moves so subsequent operations re‑read authoritative on‑disk flags instead of consulting stale memory.
Overview of the bug class
What went wrong — a concise technical summary
The issue manifests when a file operation creates a reflinked/refcounted extent and a subsequent extent‑move or defragment operation updates the on‑disk extent flags (for example, clearing a refcounted bit). If the in‑memory extent map cache is not invalidated, later operations that consult that cache may misinterpret the current on‑disk semantics and hit an assertion such as BUG_ON(!(rec->e_flags & OCFS2_EXT_REFCOUNTED). That assertion was the immediate cause of kernel OOPSes in reported reproductions.Two separate but related defense patterns are visible in vendor and upstream fixes:
- Avoiding ASSERT/BUG when encountering a recoverable meta‑state mismatch and returning an explicit error code (e.g., ocfs2_error so callers can clean up or retry; and
- Clearing or invalidating cache entries for extents that were moved or mutated so that subsequent operations will re‑read the current on‑disk metadata instead of relying on stale cached flags.
Why this is not a remote network exploit
The vulnerability requires local interaction with the filesystem or the ability to supply a crafted disk image that will be opened/mounted on the target host. In most practical attack models an adversary must either:- Mount or cause the host to mount or process a crafted block device or loopback image, or
- Run local operations (or untrusted tenant workloads in multi‑tenant environments) that can create the specific timing and operations pattern (reflink + move/defrag + subsequent write) to reach the inconsistent state.
Deeper technical analysis
Code path and triggering sequence (reconstructed)
- A reflink or copy‑on‑write operation (e.g., via copy_file_range or fallocate variants that create shared extents) produces an extent on disk with a refcount flag such as OCFS2_EXT_REFCOUNTED.
- An extent‑move or defragment operation executes on that same region. The on‑disk extent record is updated (for example, clearing the refcounted bit) but the in‑memory extent map cache entry is not invalidated.
- A subsequent write or COW operation consults the stale in‑memory cache and believes the extent is still refcounted. This mismatch leads the refcount‑handling code to execute with incorrect assumptions and eventually hit an assertion (e.g., BUG_ON) intended to catch impossible states.
Why ASSERTs are harmful here
Kernel BUG or BUG_ON are designed as last‑resort invariants in code assumed never to fail in correctly behaving systems. When user‑visible or external inputs can trigger transient inconsistencies — especially in the presence of complex concurrency, sharing, and on‑disk/off‑memory representation differences — asserting to a full kernel panic is a poor trade‑off for robustness in production systems. Converting the assertion to a controlled error path (for example ocfs2_error avoids taking down the whole host and gives the filesystem code a chance to recover, notify users, and avoid data loss beyond the crash itself.The fix(es): what maintainers changed
Upstream and vendor patches described in public analysis converge on two complementary directions:- Replace or relax kernel fatal assertions in the affected code path with explicit error returns that let callers abort the operation gracefully rather than triggering an OOPS. This is the "relax BUG to ocfs2_error" approach in the title.
- Add cache invalidation or small synchronization steps after extent move/defragment operations so the in‑memory extent map cache is refreshed and cannot present stale flags to subsequent operations. Clearing these cache entries forces later operations to consult on‑disk metadata and rebuild correct, consistent in‑memory structures.
Why these changes are reasonable
- Reducing blast radius: Replacing BUG with a controlled error reduces the chance of a complete host outage from a single malformed image or a transient race.
- Localizing change: Invalidating the relevant cache entries is a narrowly scoped fix with low regression risk — it doesn’t change the semantics of extents, only when the cached view is considered authoritative.
- Backport friendliness: Small diffs are easier for downstream vendors and embedded OEMs to apply to older kernel branches, accelerating patch rollout across a diverse ecosystem.
Affected systems and realistic exposure
- Systems that mount OCFS2 volumes — especially clustered storage nodes and appliances — are directly in scope. Inventorying hosts for OCFS2 usage (lsmod | grep ocfs2 and findmnt -t ocfs2) is the first practical step to determine exposure.
- Multi‑tenant or shared infrastructure that accepts untrusted images (CI/CD runners, VM import services, image ingestion pipelines) has elevated risk because adversaries or careless tenants can supply crafted images that trigger the sequence.
- Embedded appliances, OEM kernels, and vendor forks may lag in applying upstream stable backports and represent a long tail of exposure. Confirm vendor advisories for these products rather than assuming upstream patches propagate instantly.
Detection, triage and hunting
Kernel logs and crash signatures to look for
- Search dmesg and journalctl -k for oops/panic traces with stack frames mentioning OCFS2 functions such as ocfs2_refcount_cal_cow_clusters, __ocfs2_move_extents_range, ocfs2_move_extent, and ocfs2_defrag_extent. These traces often include the original assertion message.
- Monitor for repeated OCFS2 BUG messages or kernel OOPS patterns on storage nodes and any host that processes untrusted images. Centralized log systems should alert on such anomalies.
Practical hunt steps
- Inventory OCFS2 usage: lsmod | grep ocfs2; findmnt -t ocfs2; check uname -r and vendor kernel package details.
- If a crash occurs, preserve full kernel logs, dmesg output, and any involved disk images or loopback files; copy them to an isolated forensic host rather than remounting them on production systems. If available, capture vmcore/kdump for deep analysis.
- Add telemetry to alert on multiple matching oops traces or repeated OCFS2-related BUG entries in a short window.
Remediation and mitigation — an operational playbook
Definitive remediation: install vendor‑supplied kernel updates that include the upstream patch(s) and reboot hosts into the patched kernel. Kernel filesystem fixes require rebooting into fixed kernels to take effect. Confirm vendor package changelogs reference the upstream commit IDs or the CVE mapping that your vendor provides.Short‑term compensating controls when immediate patching is impossible:
- Restrict who can mount or import filesystem images and limit loopback device usage to trusted operators.
- Isolate hosts that run OCFS2 services from untrusted workloads, or move image inspection to hardened, disposable VMs until patched.
- Temporarily disable or avoid aggressive defragmentation or extent‑moving operations (e.g., certain FITRIM/defrag paths) on higher‑value hosts.
- Ramp up telemetry and alerting on OCFS2 kernel messages and preserve crash artifacts for vendor triage.
- Identify a pilot set: a single storage node and a dependent service that can tolerate a brief outage.
- Deploy the vendor kernel update, reboot the pilot, and execute a smoke test that exercises reflink, move/defrag and write flows.
- Monitor kernel logs for 24–72 hours for any residual OCFS2 errors.
- If clean, expand to a larger staging group, then production, preserving rollback images for each stage.
Risk assessment and critical analysis
Strengths of the remediation approach
- Surgical fixes reduce regression risk. Small changes that either return errors instead of BUGs or invalidate small cache windows are far less likely to introduce regressions that destabilize production filesystems. This aids vendor backporting.
- Operationally pragmatic. Converting hard asserts into recoverable error paths keeps hosts online and allows administrators to triage without urgent reboots in many cases.
Residual risks and caveats
- Vendor propagation lag. Embedded vendors and OEMs often delay backports; the long tail of devices and images may remain vulnerable until vendors ship updates. Operators should not assume fixed unless their vendor advisory or package changelog explicitly states so.
- Potential for missed semantics. While invalidating caches is a low‑risk remedy, it does not change the underlying fragility that allowed an assertion to be reachable; future code paths could reveal adjacent races if not comprehensively audited.
- Escalation claims require caution. Historically, some kernel availability bugs have later shown escalation vectors, but current public analysis treats this OCFS2 defect primarily as a DoS/availability issue; claims of privilege escalation or RCE remain unverified until a credible proof‑of‑concept surfaces. Operators should treat such claims skeptically and demand PoC evidence.
Vendor coordination and patch verification
- Obtain the official vendor or distribution advisory mapping (for example, Debian, Ubuntu, Red Hat, SUSE, or your chosen vendor). The stable kernel commit IDs referenced by vendors are the authoritative proof that a kernel package contains the upstream fix.
- Validate package changelogs and kernel package metadata — do not assume kernel version numbers alone prove inclusion of a specific commit; check the changelog or the vendor advisory’s commit mapping.
- For custom or embedded kernels, plan to backport the minimal upstream patch and run dedicated QA; stable‑tree backports may not apply cleanly across versions and can require small adjustments.
What could not be verified and a cautionary note
The user‑provided Microsoft Security Response Center link returned a "page not found" result when supplied as input to this analysis. The aggregated advisory corpus searched for this article did not show a direct, authoritative mapping for CVE‑2025‑68364 to the described OCFS2 change in the files available for review. Administrators should therefore cross‑check their vendor’s public security advisories, distribution trackers, or the upstream kernel stable commit log to confirm the exact CVE mapping, commit hash, and package level backport for their environment before declaring hosts patched. Treat any CVE identifier in isolation as potentially ambiguous until vendor or distribution metadata ties it to a commit or package.Final recommendations — concise checklist
- Inventory: Identify hosts that load OCFS2 or mount OCFS2 volumes and prioritize multi‑tenant or storage nodes.
- Verify: Check vendor/distro advisories or kernel package changelogs for the upstream fix or CVE mapping before assuming coverage.
- Patch: Apply vendor kernel updates that include the fix, and plan rolling reboots with a pilot group and monitoring window.
- Mitigate: If immediate patching isn’t possible, restrict image mounts, isolate untrusted workloads, defer defragment/move ops, and strengthen telemetry for OCFS2 OOPS detection.
- Preserve evidence: On any crash, preserve dmesg, journal, vmcore/kdump and involved disk images for vendor triage.
Converting hard assertions into recoverable error paths and ensuring cache coherence after mutating operations represents a pragmatic, low‑risk remediation for filesystem correctness bugs like the OCFS2 extent move failure discussed here. Administrators should prioritize patching based on actual exposure — presence of OCFS2 mounts and acceptance of untrusted images — and verify vendor advisories and package changelogs before marking systems as remediated. Until vendor mappings are confirmed for any CVE identifier you encounter, treat specific CVE-to-package claims with caution and demand commit-level evidence for final closure.
Source: MSRC Security Update Guide - Microsoft Security Response Center