Kaspersky’s Global Research and Analysis Team (GReAT) has publicly exposed an active, server‑focused cyberespionage campaign — tracked as PassiveNeuron — that has compromised Internet‑facing Windows Server systems in government, financial and industrial environments across Asia, Africa and Latin America, using bespoke implants alongside commodity tools to establish resilient, low‑noise footholds from December 2024 through at least August 2025.
Kaspersky first documented the activity underlying PassiveNeuron in 2024; after an approximate six‑month lull, the campaign resumed in December 2024 and produced ongoing infections into 2025. The operator(s) consistently prioritized Windows Server hosts — particularly Internet‑facing database and web servers such as Microsoft SQL Server and IIS — rather than user workstations, a notable shift that increases both strategic value and remediation complexity for victims. The disclosure names three primary tools observed in intrusion sets:
Key unresolved questions and risks:
Source: The Express Tribune Kaspersky flags new global cyberespionage wave | The Express Tribune
 Background
Background
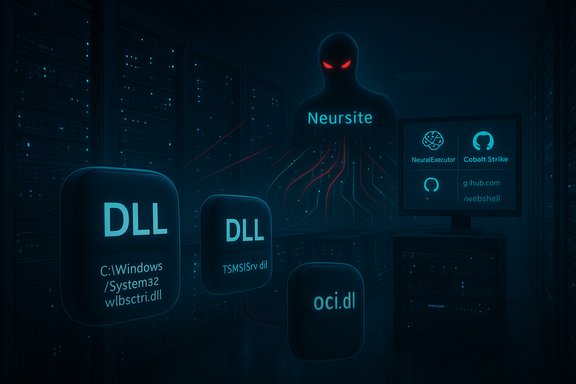
Kaspersky first documented the activity underlying PassiveNeuron in 2024; after an approximate six‑month lull, the campaign resumed in December 2024 and produced ongoing infections into 2025. The operator(s) consistently prioritized Windows Server hosts — particularly Internet‑facing database and web servers such as Microsoft SQL Server and IIS — rather than user workstations, a notable shift that increases both strategic value and remediation complexity for victims. The disclosure names three primary tools observed in intrusion sets:- Neursite — a previously undocumented, modular native (C/C++) backdoor with plugin support and proxying capabilities.
- NeuralExecutor — a new .NET‑based loader/implant that fetches and executes additional .NET assemblies.
- Cobalt Strike — a widespread red‑teaming framework abused for lateral movement and post‑exploitation tasks.
Technical overview: what PassiveNeuron does and how it works
PassiveNeuron is distinguished by a layered loader architecture, sandbox‑avoidance checks and the combination of bespoke implants with commodified tooling. The practical result is a stealthy, resilient espionage foothold that is difficult to surgically remove.Multi‑stage loader chain and Phantom DLL hijacking
The campaign relies heavily on a multi‑stage DLL loader chain. Early stages involve placing malicious DLLs into System32 under names that mimic legitimate libraries (examples observed include C:\Windows\System32\wlbsctrl.dll, TSMSISrv.dll and oci.dll). Those DLLs are often artificially inflated — frequently exceeding 100 MB — by adding large overlay sections to frustrate signature‑based triage and to mask the payload. Because these filenames and locations are expected by Windows services, placing attacker DLLs there leverages a type of Phantom DLL hijacking that yields automatic persistence on boot and during service operation. The loader chain typically:- Deploys on‑disk first‑stage DLLs in System32 that are large and padded.
- Uses second‑stage DLLs or text staging files that contain AES‑encrypted, Base64‑encoded blobs.
- Spawns a legitimate process in a suspended state (examples observed: WmiPrvSE.exe, msiexec.exe), injects shellcode, and maps the final payload into memory.
This redundancy and layered persistence means removing a single file rarely evicts the actor; full reimaging is often the safest remediation.
Neursite: modular native backdoor
Neursite is the campaign’s most feature‑rich implant. It implements classic espionage capabilities:- System reconnaissance (inventory of OS, services, network interfaces).
- Process and file management (spawn/kill processes, read/write files).
- Network proxying/tunnelling to route traffic through compromised hosts (enabling lateral movement and covert exfiltration paths).
- Dynamic plugin loading to extend functionality on demand.
- Flexible communications supporting raw TCP, HTTP/S and SSL with configurable headers and beacon timing.
NeuralExecutor: .NET loader with dead‑drop resolver
NeuralExecutor functions as a flexible .NET runtime loader that retrieves and executes additional .NET assemblies from command‑and‑control (C2) infrastructure. Early samples contained embedded C2 addresses and were protected with ConfuserEx obfuscation; later variants implemented a dead‑drop resolver by pulling encrypted configuration blobs from public developer platforms (notably GitHub raw content), extracting a delimited Base64/AES payload, decrypting it, and using it to resolve live C2 addresses. This technique blends C2 resolution traffic into otherwise legitimate developer flows and complicates takedown efforts.Cobalt Strike and commodity tooling
Alongside bespoke implants, the operators deployed Cobalt Strike beacons for rapid lateral movement, privilege escalation and hands‑on‑keyboard tasks. The mixing of custom and commodity tooling is operationally efficient — bespoke implants provide stealth and longevity while Cobalt Strike speeds exploitation and post‑compromise activity — but it also increases the potential for detection where organizations have robust telemetry capturing network beacons and behavioral anomalies.Infection chain: typical initial access and escalation patterns
Kaspersky’s telemetry — and corroborating industry reporting — shows multiple initial access vectors, with a recurring theme: abuse of server‑side services to obtain remote command execution.- Microsoft SQL Server abuse: at least one documented intrusion used Microsoft SQL to execute OS commands and stage an ASPX web shell. Attackers leveraged SQL‑level execution (for example, xp_cmdshell) or administrative credentials to write Base64‑encoded ASPX web shells via PowerShell or VBS stagers. When web shell writes were detected and blocked, operators pivoted to the more covert DLL loader chain described above.
- Web application weaknesses and credential compromise: where SQL injection, vulnerable CMS components or stolen credentials were available, operators used them to plant initial web shells or get remote command execution.
- Escalation to loaders and implants: successful initial footholds were followed by attempts to deploy ASPX web shells and, if those attempts failed or were detected, attackers shifted to the multi‑stage DLL chain that ultimately delivered Neursite, NeuralExecutor or Cobalt Strike. The progression from noisy web shells (a realistic detection opportunity) to layered loaders explains the campaign’s long dwell times in some victim environments.
Victimology and operational objectives
Observed victims include government, financial and industrial organizations in Asia, Africa and Latin America, indicating a geographically strategic focus rather than opportunistic mass targeting. The emphasis on servers — particularly database and web infrastructure — suggests objectives aligned with sustained intelligence collection: credential theft, architectural reconnaissance, and the establishment of covert proxying/exfiltration channels. Compromise of a single Internet‑facing server frequently yields disproportionately high leverage: access to databases, authentication systems, and administrative tooling can enable broad lateral movement and domain compromise.Attribution: clues, caveats and Kaspersky’s assessment
Kaspersky’s analysis highlights several artifacts that point toward Chinese‑language tradecraft (e.g., overlaps in infrastructure and the GitHub dead‑drop technique previously observed in other Chinese‑linked operations). However, the vendor explicitly assigns low confidence to direct attribution and warns that some artifacts — such as Cyrillic strings or reused PDB paths — can be intentionally planted as false flags. Independent industry reporting echoes this cautious stance: overlapping TTPs and shared tooling are useful for correlation but insufficient for definitive attribution without corroborating intelligence. Treat all attribution signals as probabilistic, not conclusive.Detection, hunting and immediate response playbook
The campaign’s layered persistence and sandbox‑avoidance techniques require a behavior‑centric approach. Below are practical, prioritized steps for detection and response that organizations should adopt immediately.High‑signal hunting indicators
- Search for abnormally large DLLs in C:\Windows\System32 (many PassiveNeuron artifacts were padded to >100 MB). These inflated overlays are a high‑value indicator of compromise.
- Audit SQL Server logs for unusual calls to xp_cmdshell or other OS‑execution stored procedures, and anomalous execution of sp_executesql that writes files or executes OS commands.
- Hunt for unexpected ASPX files in web roots and anomalous POST traffic to management endpoints, especially flows that carry Base64 or hex blobs.
- Monitor outbound requests from server hosts to public developer endpoints (raw GitHub blobs, cloud storage buckets) that might be used as dead‑drop resolvers.
- Detect suspicious process injection patterns: suspended legitimate processes (WmiPrvSE.exe, msiexec.exe) that are followed by unmapped PE payloads in memory.
Immediate incident response sequence (recommended)
- Preserve volatile evidence (memory images, EDR telemetry, SQL/IIS logs) and isolate suspected hosts from the network while maintaining forensic captures.
- Assume broader compromise: rotate exposed credentials and service account keys that the server could access.
- Use EDR/Sysmon-based queries to hunt for inflated DLLs, web shells, unexpected child processes and outbound dead‑drop traffic.
- If confirmed, plan full rebuilds from trusted golden images rather than incremental artifact removal; the layered loader chain and redundant persistence mean surgical deletions often fail.
- Notify relevant stakeholders and consider coordinated takedown measures for revealed C2 infrastructure with law enforcement and hosting providers.
Practical hardening checklist for Windows Server owners
- Harden Internet‑exposed servers:
- Restrict management ports (SQL/TCP, RDP) to allow‑listed IPs or require VPN/Jumphost access.
- Disable xp_cmdshell and other OS‑execution capabilities in SQL Server unless strictly necessary and audited.
- Apply vendor patches promptly and keep server software (IIS, SQL Server, web frameworks) up to date.
- Increase visibility:
- Deploy Sysmon, EDR with memory capture, and forward SQL/IIS logs to SIEM for long‑term correlation.
- Implement file‑integrity monitoring for System32 and web document roots, and hunt for unusually large binaries.
- Network controls:
- Enforce egress filtering and block or flag outbound connections to public developer endpoints from servers that should not be pulling such content.
- Segment server roles to limit lateral movement opportunities if a host is compromised.
- Operational hygiene:
- Maintain golden images and rehearse fast rebuild playbooks to minimize downtime and residual persistence.
- Rotate service account and certificate material after incident containment.
- Run adversary emulation tests that specifically target server stacks and DLL loader scenarios.
What makes PassiveNeuron particularly dangerous — and where defenders have an edge
PassiveNeuron’s strengths:- Precision: MAC whitelists and scheduled activation windows reduce accidental exposure to detection tools and sandboxes, keeping telemetry footprints small.
- Resilience: Multi‑stage loaders and dynamic plugins mean killing a process or deleting a file rarely removes access entirely.
- Blending: Use of public clouds and GitHub as dead‑drop resolvers helps C2 traffic blend into legitimate developer flows, complicating traditional network blocklists.
- Early noisy stages (web shell attempts) are detectable. Kaspersky observed repeated, somewhat naive web shell installation attempts that were blocked in several cases — these represent actionable detection opportunities. Rapid response at these noisy stages can prevent escalation to the layered loader chain.
- Behavioral telemetry (memory capture, process injection detection, and network flow analysis) is effective against the campaign’s multi‑stage techniques because it can spot the behavior of an implant rather than rely on brittle file hashes.
- Good network hygiene (egress filtering, least privilege, segmented management access) raises the cost and complexity of achieving an operational foothold, undermining the campaign’s attack model.
Verification and independent corroboration
Kaspersky’s SecureList technical write‑up and official press release provide the most detailed, primary vendor analysis of PassiveNeuron. Multiple independent industry sources — including technical news outlets and security trade press — have reproduced and validated the core technical findings: the timeline from December 2024 to August 2025, the server‑centric victimology, the presence of Neursite and NeuralExecutor, the multi‑stage DLL loader chain and the use of GitHub dead‑drops and Cobalt Strike. Where attribution is claimed or hinted at, vendors consistently flag low confidence and emphasize that some artifacts may be deliberate false flags. Readers and defenders should therefore treat attribution as tentative and prioritize technical containment over geopolitical speculation.Critical analysis: strengths, risks and unanswered questions
PassiveNeuron is a textbook example of a modern espionage operator that has made conscious decisions to target high‑leverage infrastructure, invest in evasion and persistence, and selectively mix bespoke implants with commodity tools to accelerate operations. The campaign’s design choices — MAC‑based whitelisting, large padded DLLs, dead‑drop resolvers — all reduce noisy telemetry and extend dwell time, giving the adversary time to harvest credentials and map networks.Key unresolved questions and risks:
- The exact initial exploitation vector(s) remain partially opaque in public reporting. While Microsoft SQL abuse and web shell staging are documented, the full set of exploited vulnerabilities or credential vectors has not been enumerated publicly for every intrusion. That gap matters because it affects prioritization for patching and hunt scope.
- Attribution remains low confidence. While there are overlaps with Chinese‑language tradecraft in some operational choices, deliberate false flags (Cyrillic strings, reused PDB paths) and shared tooling across many groups reduce the evidentiary weight of these signals. Do not let attribution uncertainty delay containment and technical response.
- The use of public developer platforms as dead‑drop resolvers complicates network detection and takedown. Organizations should treat unusual server-origin requests to GitHub/raw developer endpoints as potentially malicious and apply contextual policy controls.
Recommendations for IT leaders and SOC teams (prioritized)
- Immediately audit and restrict Internet exposure for SQL Server, IIS and other server management ports; require VPN or bastion host access for administrative operations.
- Hunt now for inflated DLLs in System32 and for ASPX web shells; escalate any findings for forensic memory capture and isolation.
- Enable and centralize SQL/IIS logging, enable Sysmon and deploy EDR policies that capture memory on suspicious injections and between process creation events.
- Review egress policies to flag or block server hosts pulling raw content from public dev platforms unless explicitly required.
- Prepare rebuild playbooks and golden images; assume full reimaging if Neursite/NeuralExecutor presence is confirmed to prevent orphaned loaders from persisting.
- Coordinate with hosting providers and law enforcement for takedown assistance when viable C2 infrastructure is identified.
Conclusion
PassiveNeuron is a sophisticated, server‑centric espionage campaign that underscores a central operational truth: Internet‑facing servers remain the highest‑leverage targets for advanced threat actors. The campaign’s blend of bespoke implants (Neursite, NeuralExecutor), commodity tooling (Cobalt Strike), multi‑stage loaders and public dead‑drop resolvers produces a resilient, stealthy foothold capable of extended espionage and lateral movement. Defensive success depends on rapid detection of the campaign’s early noisy activity, robust behavioral telemetry capable of surfacing in‑memory and process injection activity, strict network egress controls, and an operational readiness posture that favors full rebuilds over piecemeal cleanup. Kaspersky’s disclosure and independent industry reporting provide concrete technical indicators and hunting playbooks; immediate action by server owners and SOC teams will materially reduce the risk that a PassiveNeuron‑style compromise becomes an enduring, high‑value espionage foothold.Source: The Express Tribune Kaspersky flags new global cyberespionage wave | The Express Tribune
