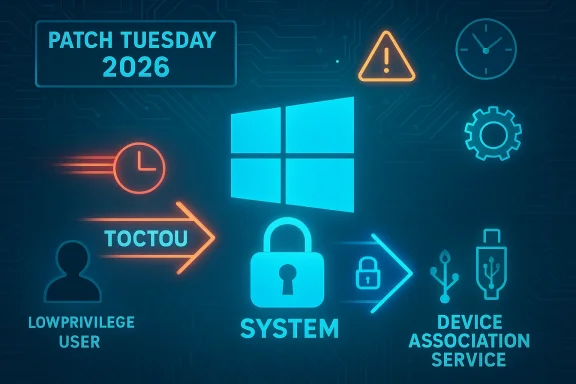
Microsoft’s March 10, 2026 Patch Tuesday closed a race‑condition hole in the Windows Device Association Service that could allow a local, authorized user to escalate privileges to a more powerful account on affected machines, forcing administrators to prioritize testing and deployment of the update across both client and server estates.
The vulnerability, tracked as CVE‑2026‑24296, is an elevation‑of‑privilege (EoP) flaw in the Device Association Service — a Windows service responsible for device pairing and related device‑software orchestration. Microsoft’s advisory describes the root cause as a concurrent execution problem with improper synchronization (a classic race condition) inside the service. The practical effect: under certain timing and access patterns, an attacker with an existing low‑privilege account on the host could manipulate the poorly synchronized shared resource to gain higher privileges locally.
This flaw was disclosed as part of Microsoft’s March 10, 2026 security updates and is rated Important by Microsoft. Multiple independent security outlets and Patch Tuesday summaries reported the issue the day of release and confirmed that patches were made available as part of the monthly rollup. At the time of publication there were no publicly available proof‑of‑concept exploits or confirmed in‑the‑wild exploitation reports for this specific CVE.
Because it touches hardware/driver lifecycle and interacts with device drivers and installers, the service often runs with elevated privileges or interacts with privileged components — which increases the impact if a flaw in its logic allows privilege escalation.
Common consequences of race conditions in privileged services include:
This particular vulnerability also underscores two persistent engineering challenges:
Be proactive: install the update, validate device pairing behavior in your environment, and use this incident as a prompt to review concurrency testing and local privilege exposure across your Windows estate. If you cannot apply the update immediately, harden local privileges and increase monitoring around device and service activity until you can.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The vulnerability, tracked as CVE‑2026‑24296, is an elevation‑of‑privilege (EoP) flaw in the Device Association Service — a Windows service responsible for device pairing and related device‑software orchestration. Microsoft’s advisory describes the root cause as a concurrent execution problem with improper synchronization (a classic race condition) inside the service. The practical effect: under certain timing and access patterns, an attacker with an existing low‑privilege account on the host could manipulate the poorly synchronized shared resource to gain higher privileges locally.This flaw was disclosed as part of Microsoft’s March 10, 2026 security updates and is rated Important by Microsoft. Multiple independent security outlets and Patch Tuesday summaries reported the issue the day of release and confirmed that patches were made available as part of the monthly rollup. At the time of publication there were no publicly available proof‑of‑concept exploits or confirmed in‑the‑wild exploitation reports for this specific CVE.
Why this matters: the Device Association Service and the threat model
What Device Association Service does
The Device Association Service performs tasks such as enumerating nearby devices, handling paired device metadata, and coordinating installation or configuration of device‑related software. It runs as a system component used by pairing flows (Bluetooth, nearby sharing, some driver/installer interactions) and may interact with other kernel or user‑mode components during device setup and provisioning.Because it touches hardware/driver lifecycle and interacts with device drivers and installers, the service often runs with elevated privileges or interacts with privileged components — which increases the impact if a flaw in its logic allows privilege escalation.
Threat model and attacker capabilities
This vulnerability is local: an attacker must have an account on the target system to exploit it. That account could be a standard user, or a less‑privileged service account. In enterprise terms, the class of risks includes:- Malicious or compromised local users (e.g., contractors, temporary accounts).
- Malware that executes under a low‑privilege user context already present on the machine.
- Chained attacks where an initial remote compromise (RCE in an application or user process) gives a foothold and the attacker then escalates via the EoP to gain SYSTEM or other elevated rights.
Technical analysis: what the advisory tells us — and what it doesn’t
The core bug: a race condition
Microsoft’s advisory characterizes the flaw as concurrent execution using shared resource with improper synchronization. In practical terms, that typically means two or more execution paths access and modify the same memory or state without sufficient locks or atomic operations, creating a narrow timing window in which an attacker can alter the state and cause the process to behave unexpectedly.Common consequences of race conditions in privileged services include:
- Bypassing of access checks (TOCTOU — time‑of‑check to time‑of‑use).
- Corruption of in‑memory data structures that later cause privileged operations to use attacker‑controlled input.
- Thread‑safety problems that lead to privileged code running with attacker‑controlled parameters.
Attack surface and constraints
From the available description we can infer constraints on exploitation:- Attackers need local code execution under a non‑privileged identity to attempt the race.
- Successful exploitation will likely require accurate timing or repeated attempts to hit the race window — operations that typically involve loops, threads, or triggering service actions on demand.
- Because the bug sits in a service that interacts with devices, device presence or simulated device operations may be part of the exploitation trigger set.
What is verifiable now — and what remains uncertain
Verified claims:- Microsoft published an advisory for CVE‑2026‑24296 on March 10, 2026 and provided patches as part of that day’s security updates.
- Security summaries from multiple independent outlets listed the issue as an Important privilege‑escalation vulnerability affecting the Device Association Service.
- The root cause was described by Microsoft as a race condition due to improper synchronization of shared resources.
- There are no public proof‑of‑concepts or technical write‑ups released at the time of publication.
- There is no confirmed active exploitation in the wild printed by Microsoft or other coordinating bodies at the time of the rollout.
- Specific function names, DLLs, or driver interactions that would enable a vulnerability reproduction are not published in the advisory.
Severity assessment and real‑world impact
Microsoft classifies the vulnerability as Important rather than Critical, reflecting its local‑only attack vector and the absence (so far) of remote exploitation mechanics. The typical mitigation priority for this profile is medium to high:- For public clouds, shared‑host environments, or systems where multiple low‑privilege users have accounts, prioritize immediate patching.
- On tightly controlled single‑user endpoints where access is limited and EDR is active, patches should still be applied within the normal update cycle but with lower emergency priority than active zero‑days or remote RCEs.
- Networks with a history of lateral movement or insufficient segmentation should treat EoP fixes as high priority because privilege escalation can enable domain compromise or ransomware deployment.
- Endpoint compromise + EoP = rapid lateral escalation to SYSTEM or service accounts, enabling persistent backdoors.
- Compromised developer or build machines could use local EoP to tamper with build artifacts or signing keys.
- Shared kiosk or lab systems with multiple low‑privilege users are attractive targets because an attacker needs only one foothold.
Detection, hunting, and forensic guidance
Because the vulnerability is a timing/race issue within a service, direct detection of an exploit attempt is non‑trivial. However, defenders can adopt the following pragmatic approaches:- Monitor Event Logs for service crashes, repeated restarts, or anomalous failure codes associated with the Device Association Service or associated DLLs (commonly shown in the System and Application logs). Unusual spikes in service‑related errors around device enumeration, pairing, or installer flows warrant investigation.
- Search process creation logs and EDR telemetry for privileged processes originating from unprivileged contexts in close temporal proximity to device pairing events.
- Hunt for suspicious use of local scheduled tasks, service creation, or modifications to driver or device installation paths that occur after a non‑privileged user session activity.
- Where available, enable and collect thread‑level ETW traces around the Device Association Service to capture race windows and anomalous access patterns — though this requires experienced diagnostics teams and careful performance considerations.
- Look for Windows Event IDs indicating service crashes or restarts with service name matching DeviceAssociationService.
- Filter process creation events that show SYSTEM‑level processes spawned by user processes or by previously non‑privileged services.
- Correlate device install events (DriverFrameworks‑UserMode / PnP logs) with privilege changes or suspicious process elevations.
Mitigation and patching strategy
The single most effective mitigation is to install Microsoft’s March 10, 2026 security updates which include the fix for CVE‑2026‑24296. Operational steps:- Identify affected systems.
- Use your patch management system to enumerate which clients and servers received the March 10, 2026 updates and flag machines that have not.
- Prioritize workstations and servers that are accessible to many distinct user accounts or that host sensitive services.
- Test before broad deployment.
- Deploy the update to a representative sample of endpoints (user workstations, admin hosts, build machines) and verify device pairing flows, device drivers, and any custom installers used in your environment.
- Pay special attention to systems that integrate with non‑standard device management tools, as device‑management components may interact with the Device Association Service.
- Roll out in controlled waves.
- Use staged rollout windows with monitoring and rollback plans.
- Include post‑patch verification checks: service state, device enumeration functionality, and EDR baseline behavior.
- If immediate patching is impossible, apply temporary mitigations.
- Consider restricting local account creation and enforcing stricter privileged access controls.
- Limit who can pair devices by Group Policy or configuration management if your environment allows — particularly on shared systems.
- Harden endpoint controls: disable unnecessary local admin rights, apply application allowlisting, and ensure EDR signatures/policies are up to date.
- Validate post‑patch telemetry.
- After deployment, run hunts for pre‑ and post‑patch anomalies to detect whether the vulnerability was exploited before patching.
- If the update causes issues in your environment (service failures, device pairing regressions), document the failure mode, collect relevant logs, and open a support case with the vendor. Always preserve system images before rolling back security updates in production.
Recommended triage priority matrix
- High priority (apply within 24‑48 hours):
- Multi‑user servers and shared endpoints (public kiosks, lab machines).
- Systems used by developers, build servers, or CI hosts.
- Machines with lateral access to domain controllers or network shares.
- Medium priority (apply within 3–7 days):
- Standard corporate desktops where local admin rights are restricted and EDR is present.
- Lower priority (apply within normal cycle, 2–4 weeks):
- Isolated single‑user devices with limited network access and strict endpoint controls.
Broader context: why EoP bugs still matter
Privilege elevation bugs like CVE‑2026‑24296 are not glamorous compared to remote code execution or supply‑chain compromises, but they remain one of the most widely used building blocks for real‑world intrusions. Attackers frequently assemble playbooks where an initial foothold via a user‑level bug or stolen credential is converted into full system control through EoP flaws. In modern incident response, the speed at which you can install fixes for EoP vulnerabilities often determines whether an intruder can convert a limited breach into a full domain compromise.This particular vulnerability also underscores two persistent engineering challenges:
- Services performing complex device and driver interactions are inherently dangerous attack surfaces because they mediate between user‑initiated flows and privileged kernel or driver components.
- Race conditions are often only revealed under heavy concurrency, specific hardware configurations, or after code paths are exercised in production scale, which is why they show up in mature products long after initial release.
For developers and engineers: defensive coding reminders
For product teams and developers, CVE‑2026‑24296 should be a refresher on concurrency hygiene:- Use well‑tested synchronization primitives (critical sections, mutexes, interlocked operations) when sharing mutable state across threads.
- Prefer immutable data handed across thread boundaries where feasible — copy on write or pass by reference to const structures.
- Apply formal code reviews and concurrency testing (stress tests, fuzzers that include concurrency models) for services that operate at elevated privileges.
- Consider using static analysis tools that can detect common thread‑safety violations and race windows early in the development cycle.
What defenders should do next: a checklist
- Apply Microsoft’s March 10, 2026 updates on a prioritized schedule, and confirm patch status via your management tools.
- Hunt for early indicators and correlate device/service anomalies with pre‑patch activity.
- Ensure endpoint protection and logging remain enabled and that you retain historical telemetry to detect exploitation attempts predating the patch.
- Review local account management policies and minimize the number of low‑privilege accounts that can log on locally.
- Document the patch rollout, problems encountered, and outcomes for future post‑incident audits.
Closing assessment
CVE‑2026‑24296 is a textbook example of a moderate‑impact but operationally significant elevation‑of‑privilege bug: local exploitability reduces its immediacy compared with network remote code execution issues, yet in the wrong environment it can be the link that converts a limited intrusion into full system compromise. Microsoft’s timely patching in the March 10, 2026 release gives defenders a clear remediation path. Organizations should treat this update as a priority for shared, multi‑user, or high‑value systems, and incorporate the event into their ongoing privilege‑management and patch‑deployment playbooks.Be proactive: install the update, validate device pairing behavior in your environment, and use this incident as a prompt to review concurrency testing and local privilege exposure across your Windows estate. If you cannot apply the update immediately, harden local privileges and increase monitoring around device and service activity until you can.
Source: MSRC Security Update Guide - Microsoft Security Response Center