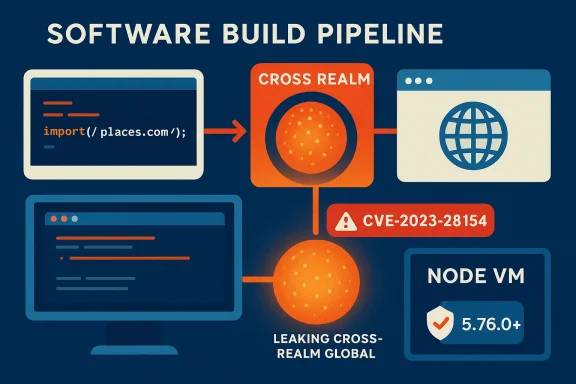
Webpack’s magic comments are small developer conveniences that quietly changed how bundles are named and fetched — but a subtle parsing bug in Webpack 5’s ImportParserPlugin turned those conveniences into a serious attack surface, allowing a crafted untrusted object to reach across JavaScript realms and expose the real global object. Developers who build with Webpack 5 versions earlier than 5.76.0 should treat this as urgent: the vulnerability (CVE-2023-28154) is critical, can be triggered without privileges or user interaction in realistic build-time scenarios, and demands both immediate patching and a reassessment of how build-time inputs are trusted.
Dynamic import() in modern JavaScript supports magic comments — structured comments adjacent to an import call that instruct tooling such as Webpack about chunk names, prefetching, or runtime behavior. Examples include comments like / webpackChunkName: "myChunk" / and / webpackPrefetch: true /. They were designed to be lightweight signals embedded in source code and parsed by the bundler at build time.
Webpack’s ImportParserPlugin is the piece of the bundler that interprets dynamic import() expressions and reads magic comments. In versions of Webpack 5 prior to 5.76.0, that plugin improperly handled objects that came from different JavaScript realms. Specifically, when the plugin processed a magic comment represented by an object, it could blindly enumerate and access properties on that object — and if those properties were getters or otherwise controlled by an attacker from another realm (for example, an iframe, a VM, or another isolated execution context), the act of property access could leak or hand over references to a privileged global object.
The result is a cross-realm object access vulnerability: under certain conditions, an attacker who is able to supply or influence a property of an untrusted object that is later parsed as a magic comment may obtain references to the bundler’s or host’s real global object (globalThis, window, or equivalents), undermining isolation guarantees and opening the door to data leakage or further exploitation.
When a tool like Webpack mistakenly evaluates or accesses properties of objects from a different realm, it can cause values created in that realm — including references to privileged globals — to cross into the host realm. This is the exact problem CVE-2023-28154 exposes: ImportParserPlugin’s handling of magic comment objects allowed property access that could be manipulated to return cross-realm references.
Importantly, the attack does not require the attacker to execute arbitrary code in the build environment — only to control the property behavior of an object that will be parsed as a magic comment. That control can arise in scenarios where code generation or build-time metadata is derived from files, plugins, templates, or other inputs that include unvalidated objects or where third-party tooling provides structured options.
At a high level, the patch implements stricter validation of magic-comment objects and safer enumeration patterns. It validates the type and “plainsness” of objects before processing them, and it avoids invoking arbitrary property accessors. The practical consequence for users is straightforward: upgrade to Webpack 5.76.0 or later.
While the underlying plugin code is complex and precise details are best examined in the upstream patch, the defensive pattern is clear: parse magiccomment data only from same‑realm plain objects (or strings/primitive values), do not access properties via getters, and sanitize or reject any input that cannot be proven inert.
Action checklist (short):
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Dynamic import() in modern JavaScript supports magic comments — structured comments adjacent to an import call that instruct tooling such as Webpack about chunk names, prefetching, or runtime behavior. Examples include comments like / webpackChunkName: "myChunk" / and / webpackPrefetch: true /. They were designed to be lightweight signals embedded in source code and parsed by the bundler at build time.Webpack’s ImportParserPlugin is the piece of the bundler that interprets dynamic import() expressions and reads magic comments. In versions of Webpack 5 prior to 5.76.0, that plugin improperly handled objects that came from different JavaScript realms. Specifically, when the plugin processed a magic comment represented by an object, it could blindly enumerate and access properties on that object — and if those properties were getters or otherwise controlled by an attacker from another realm (for example, an iframe, a VM, or another isolated execution context), the act of property access could leak or hand over references to a privileged global object.
The result is a cross-realm object access vulnerability: under certain conditions, an attacker who is able to supply or influence a property of an untrusted object that is later parsed as a magic comment may obtain references to the bundler’s or host’s real global object (globalThis, window, or equivalents), undermining isolation guarantees and opening the door to data leakage or further exploitation.
What “cross‑realm” means and why it matters
Realms, globals, and expectations
A realm is essentially an isolated JavaScript global environment. Typical examples include:- A top-level browser window or document (window).
- An iframe with a different origin or sandbox attributes.
- A Node.js VM context created with vm.createContext().
- A worker or other isolated runtime.
When a tool like Webpack mistakenly evaluates or accesses properties of objects from a different realm, it can cause values created in that realm — including references to privileged globals — to cross into the host realm. This is the exact problem CVE-2023-28154 exposes: ImportParserPlugin’s handling of magic comment objects allowed property access that could be manipulated to return cross-realm references.
Why build tooling is a high-value target
Build-time tooling runs with different privileges and access than runtime code delivered to users. A compromised build process can:- Leak secrets or configuration values used during build-time (API keys, tokens, credentials).
- Insert malicious code into produced bundles, affecting all downstream consumers.
- Abuse elevated runtime contexts (CI runners, local developer machines, or build servers) to proliferate access.
How the vulnerability works — the gist
Magic comments as objects
Magic comments are parsed by the bundler. In Webpack’s plugin internals, code paths interpreting magic comments accepted objects that represented parsed key/value pairs for magic directives. When ImportParserPlugin iterated over the keys and read values, it did not sufficiently validate that the object was a simple, same‑realm plain object. That allowed crafted objects with getters or accessor properties (which execute code when accessed) to run in their originating realm and return references that should not normally be handed to the host.Attack vector: controlled property access
An attacker who can control a property of an object that is passed — directly or indirectly — as a magic comment can craft that property so its accessor returns a reference to a global object or otherwise bridges realms. For example, a getter could return globalThis, a Window, or another sensitive object. When Webpack’s parser reads that property, it receives the returned value and may incorporate it into internal data structures or generated code, effectively leaking or transferring that reference.Importantly, the attack does not require the attacker to execute arbitrary code in the build environment — only to control the property behavior of an object that will be parsed as a magic comment. That control can arise in scenarios where code generation or build-time metadata is derived from files, plugins, templates, or other inputs that include unvalidated objects or where third-party tooling provides structured options.
Why simple defenses failed
Typical object checks like Object.keys() or basic enumeration methods may still trigger getters and cause cross-realm access. Proper defense requires distinguishing plain objects created in the current realm from objects coming from other realms, and avoiding invocation of any user-provided accessors while reading metadata. The fix must be defensive: treat magic comment input as data, not as code to be evaluated.The fix and how Webpack resolved it
Webpack maintainers released a patched series starting with version 5.76.0 that addresses the vulnerability. The remediation centers on refusing to treat cross-realm objects as trusted magic comment input and ensuring that the parser does not invoke attacker-controlled getters or accessors while extracting magic comment values.At a high level, the patch implements stricter validation of magic-comment objects and safer enumeration patterns. It validates the type and “plainsness” of objects before processing them, and it avoids invoking arbitrary property accessors. The practical consequence for users is straightforward: upgrade to Webpack 5.76.0 or later.
While the underlying plugin code is complex and precise details are best examined in the upstream patch, the defensive pattern is clear: parse magiccomment data only from same‑realm plain objects (or strings/primitive values), do not access properties via getters, and sanitize or reject any input that cannot be proven inert.
Risk assessment: who is exposed and how likely is exploitation?
Environments at high risk
- CI/CD and build servers that accept untrusted inputs as part of the build graph. For example, pipelines that generate imports or magic comment metadata from repository content that includes user-contributed or third-party data are at higher risk.
- Multi-tenant build environments that process code from many projects (shared hosted builders, cloud-based build services) where an attacker may submit a package or project that causes the bundler to parse crafted objects.
- Projects that programmatically construct magic comment objects at build time using external data sources, templates, or plugin-provided functions.
- Tools or plugins that inject magic comment metadata from user input or third-party content.
Environments at lower risk
- Typical single-user developer environments where source code is fully controlled and not influenced by untrusted data.
- Minimalistic builds that do not use dynamic import() magic comments or use them exclusively with literal comment strings rather than programmatically built objects.
Exploitability and impact
CVE-2023-28154 received a critical severity and a high CVSS rating because exploitation requires low complexity and no privileges, and successful exploitation can result in high confidentiality and integrity impact. That said, exploitation typically requires a chain — an attacker must be able to supply or influence the untrusted object that ends up parsed as a magic comment. In many real-world setups, that requires either:- A public-facing service that processes untrusted content into build-time artifacts, or
- Inclusion of third-party contributed code or metadata that is not validated before being fed to Webpack.
Practical mitigation steps — immediate and medium-term
If your build environment uses Webpack 5 anywhere in the affected range (>= 5.0.0 and < 5.76.0):- Upgrade immediately
- Update Webpack to version 5.76.0 or later in every project, CI/CD pipeline, and container image that runs builds.
- In npm: npm install --save-dev webpack@^5.76.0 or pin package.json to "webpack": ">=5.76.0".
- In Yarn: yarn add --dev webpack@^5.76.0.
- Ensure Docker images or build toolboxes used in CI are rebuilt with the updated version.
- Audit transitive dependencies and vendored tooling
- Some tools bundle or vendor a specific version of Webpack. Audit build-related tools (browserslist tooling, framework CLIs, bundler wrappers) and ensure they do not pull an older vulnerable copy.
- Update monorepo package locks and regenerate lockfiles to ensure transitive updates are applied consistently.
- Harden CI and build inputs
- Avoid processing untrusted content into build-time metadata. If your build pipeline consumes external inputs, sanitize and validate them as inert strings only.
- Treat any metadata used to generate magic comments as untrusted and enforce it be plain JSON or primitives — never executable accessors or objects with getters.
- Enforce policies and scanning
- Add SCA (software composition analysis) checks to flag vulnerable Webpack versions in your dependency graph.
- Enable automatic Dependabot or equivalent alerts to surface when packages need urgent upgrading.
- Review plugins, templates, and code generation
- Inspect build-time plugins or templates that produce magic comment objects. Replace programmatic object construction with literal comment strings or ensure strict validation.
- Avoid using libraries that fill magic comment options with functions or callbacks that might be influenced by external data.
- Limit build privileges and secrets exposure
- Use the principle of least privilege: do not expose secrets to build containers unless absolutely necessary.
- Isolate build runners, avoid running builds on multi-tenant VMs that process untrusted code, and keep secrets out of environments where untrusted build artifacts are processed.
- Monitor for suspicious activity
- Monitor CI logs and artifact generation for unexpected changes to chunk naming or runtime generation that could indicate tampering.
- Instrument builds to detect when non-primitive magic comment metadata appears.
Developer guidance: coding patterns to avoid and preferred alternatives
- Do not programmatically construct magic comment objects from unvalidated inputs. If you must compute chunk names or flags at build time, only allow plain strings or booleans derived from recommended-safe sources.
- Prefer literal magic comment syntax embedded in source where possible. Comments like / webpackChunkName: "user-profile" / are inert strings and not susceptible to getter evaluation.
- If using tooling that generates magic comments (for example, a plugin that determines chunk names from file metadata), ensure it emits literal comments and never objects that would be parsed by the bundler at runtime.
- Audit and upgrade third-party libraries that interact with magic comments; a small plugin that tries to help chunk naming can inadvertently pass unsafe objects into Webpack.
Detection and verification: how to confirm you are patched
- Check Webpack version
- Inspect package.json and lockfile to confirm webpack resolves to 5.76.0 or higher across all relevant projects and build images.
- For CI and Docker images, run a version check inside the build container to verify the installed package.
- Search build artifacts
- If you have archived build logs or bundles produced with older Webpack versions, inspect them for unexpected runtime behavior or injected runtime references that indicate cross-realm values.
- Use SCA tooling
- Run vulnerability scans against your codebase and dependency graph. Many SCA services will flag CVE-2023-28154 when an affected Webpack version is present.
- Sanity-check third-party tools
- For frameworks and CLIs (for example, framework scaffolds that include their own bundling toolchains), verify they have released updates that ship with fixed webpack versions.
Long-term lessons for secure build systems
This bug is a textbook example of how seemingly benign developer features can become attack surfaces. Maintain a security mindset for the build pipeline:- Treat build-time metadata and plugin inputs as untrusted when they can be influenced externally.
- Run build tools in isolated environments with limited access to secrets and elevated machine resources.
- Apply defense-in-depth: even after patching, harden other layers (CI configuration, plugin vetting, dependency pinning).
- Require reproducible builds and signed artifacts where possible, so build output integrity is easier to verify.
Notable strengths of the fix and remaining caveats
Strengths
- The upstream fix is precise and targeted: by validating object types and preventing accessor invocation, Webpack eliminates the root cause without removing magic comment functionality for normal, safe use cases.
- The remediation is backward compatible for legitimate uses: literal magic comments and plain objects from the same realm continue to work.
- Publishing a clear patched version (5.76.0 and later) allows organizations to apply a straightforward upgrade across projects.
Caveats and residual risks
- Transitive and vendorized copies of Webpack can be overlooked. Frameworks, CLIs, or plugins that bundle their own version may remain vulnerable until those tools update.
- Some large monorepos or enterprise build images cache older dependencies. If Docker layers or build caches are not rebuilt, older vulnerable versions can persist.
- The exploitability in a given environment depends on how build-time data is fed into Webpack. Teams must perform a threat model analysis to ascertain whether untrusted magic comment inputs are plausible in their systems.
- Public proof-of-concept code exists in some analysis and research write-ups; publishing details further increases the need for responsible patching.
Final assessment and call to action
CVE-2023-28154 is a critical reminder that developer tooling is part of your attack surface. A seemingly trivial parsing path for magic comments became a vector for cross-realm global object access, and exploitation requires surprisingly little privilege in the right conditions. The mitigation is clear and implementable: upgrade to Webpack 5.76.0 or later, audit transitive dependencies and build images, sanitize build-time inputs, and tighten CI isolation.Action checklist (short):
- Upgrade Webpack to 5.76.0+ everywhere now.
- Rebuild CI images and Docker layers so patched versions are actually used.
- Audit vendorized or bundled copies of Webpack in third-party tools.
- Sanitize or reject programmatic magic comment inputs derived from external sources.
- Add SCA checks to detect and block vulnerable versions in your dependency graph.
- Isolate build runners and minimize exposure of secrets during builds.
Source: MSRC Security Update Guide - Microsoft Security Response Center