Windows 10 users who think “it still boots, so I’m fine” are being handed a quietly serious maintenance problem: Microsoft is replacing the Secure Boot certificates that have underpinned Windows’ pre‑boot trust model since 2011, and machines that don’t receive the new certificates will continue to boot but will enter a degraded security state — unable to receive new boot‑level protections, revocation updates, or mitigations for newly discovered pre‑OS threats. com]
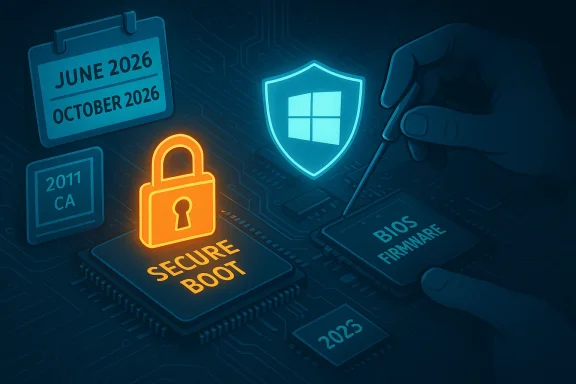
Microsoft and OEMs have been preparing a coordinated refresh of the Secure Boot certificate family because the long‑lived 2011 Microsoft CA certificates embedded in many PC firmwares are expiring in 2026. The replacement certificates (the 2023 family) are already published and shipped in cumulative update packages, and Microsoft has published detailed guidance and a FAQ for the rollout. The change affects certificates stored in the firmware’s KEK (Key Enrollment Key) and DB/DBX databases and therefore lives at the firmware/UEFI layer — before Windows itself starts.
At a glance:
What this does not mean:
Microsoft continues to allow eligible devices to upgrade to Windows 11 for free, but the upgrade is subject to the Windows 11 minimum hardware requirements (TPM 2.0, supported CPU families, UEFI Secure Boot enabled, etc.). For many older PCs, the hardware prerequisites block the free upgrade path and force the user to choose ESU, accept the degraded risk, or replace hardware. Microsoft’s own upgrade FAQ confirms the free upgrade policy for eligible machines.
Practical implications:
This creates a clear two‑tier landscape:
Remaining uncertainties and cautionary notes:
The good news is that Microsoft and major OEMs have published guidance, begun shipping updates, and provided assisted update paths. The bad news is that there are real edge cases — chiefly older hardware and isolated fleets — where the certificate refresh will leave devices unable to receive new pre‑boot protections. For home users and small IT teams, the practical prescription is straightforward: inventory, update firmware, back up keys, and either upgrade to Windows 11 if eligible or enroll in ESU if you must stay on Windows 10 for a limited time.
If you want a short, actionable plan tailored to your specific machines (model list, BIOS versions, or an IT‑facing rollout checklist), post the model numbers and Windows builds you’re responsible for and I’ll turn this guidance into a step‑by‑step remediation playbook you can run this week.
Source: Inbox.lv Windows 10 Users Warned About Danger
 Background / Overview
Background / Overview
Microsoft and OEMs have been preparing a coordinated refresh of the Secure Boot certificate family because the long‑lived 2011 Microsoft CA certificates embedded in many PC firmwares are expiring in 2026. The replacement certificates (the 2023 family) are already published and shipped in cumulative update packages, and Microsoft has published detailed guidance and a FAQ for the rollout. The change affects certificates stored in the firmware’s KEK (Key Enrollment Key) and DB/DBX databases and therefore lives at the firmware/UEFI layer — before Windows itself starts.At a glance:
- Microsoft’s official guidance names specific expiring certificates and their replacement 2023 counterparts and dates.
- The oldest Microsoft KEK and UEFI CA entries begin expiring in June 2026; the Windows production PCA included in firmware has an expiry that extends into October 2026.
- Devices that have the new 2023 certificates installed will continue to receive the full set of Secure Boot protections (DB/DBX updates, bootloader signing, revocations). Systems that do not will still boot, but will no longer be able to receive new pre‑OS revocations and signatures — the “degraded security” state.
What Secure Boot is, and why these certificates matter
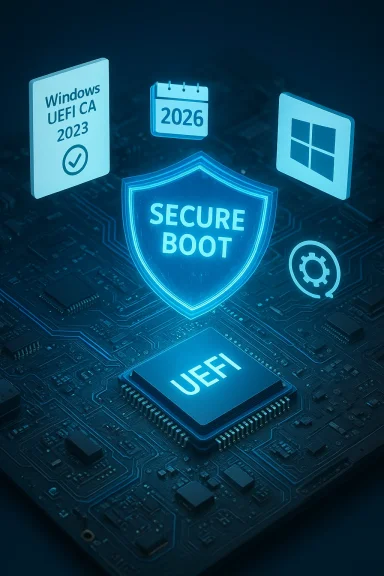
UEFI Secure Boot in two sentences
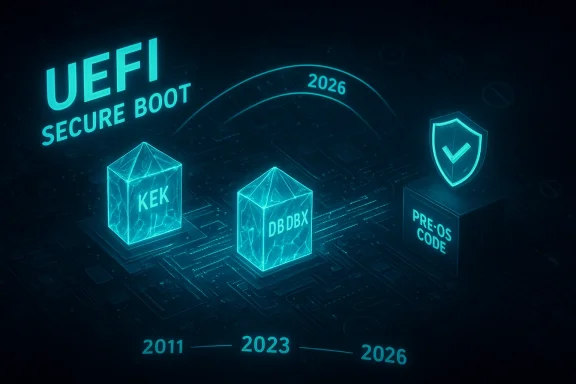
Secure Boot is a UEFI firmware security feature that prevents unauthorized/pre‑tampered code (bootkits, rogue UEFI drivers, unsigned bootloaders) from running before the OS. It does this by verifying the digital signatures of pre‑boot components against a set of trusted certificates (KEK, DB entries), and by applying revocations in DBX. If the signing keys used to vouch for pre‑OS code are no longer valid or cannot be updated, new boot‑level threats cannot be mitigated.Which certificates are expiring and when
Microsoft’s guidance lists the affected certificates (with precise dates):- Microsoft Corporation KEK CA 2011 — expires in June 2026, replaced by Microsoft Corporation KEK 2K CA 2023.
- Microsoft UEFI CA 2011 (two entries) — expire in June 2026, replaced by Microsoft UEFI CA 2023 and Microsoft Option ROM UEFI CA 2023.
- Microsoft Windows Production PCA 2011 — has an expiration in October 2026, replaced by Windows UEFI CA 2023. OEM vendor pages, such as HP’s advisory, list matching dates and map the new certificates to KEK/DB storage locations.
How the refresh is delivered — and where it can break down
Three delivery channels
- Firmware (UEFI/BIOS) updates from OEMs — the preferred and most robust path is an OEM firmware update that adds the new 2023 certificates directly into the platform store. Many OEMs have already published BIOS updates with the necessary CA entries for supported models.
- Windows cumulative updates (LCUs) that include the certificate payload — Microsoft has included the new certificates in cumulative updates; these updates can assist on some devices by writing the new keys if firmware allows it and if the device meets Microsoft’s update eligibility signals. But this mechanism is not guaranteed on every device and has prerequisites (Windows build support, diagnostic data sharing, and update delivery conditions).
- Manual OEM or IT administrator action — for offline, air‑gapped, or managed fleets, admins may need to push firmware updates or use vendor tooling to implant the 2023 certificates before expiry dates.
Common failure modes
- Unsupported or obsolete firmware: Older platforms (often 2017 and earlier) may never receive a vendor BIOS update. Vendors typically stop firmware servicing after a certain support window; those machines will likely keep the old CA entries and therefore cannot be updated to the 2023 family.
- Secure Boot disabled: If Secure Boot is disabled in firmware, the Windows‑side patch cannot update the firmware’s signature stores. Those systems must have Secure Boot reenabled and a firmware path that accepts the new keys.
- Air‑gapped or tightly firewalled devices: Microsoft’s assisted update mechanisms depend on telemetry and update channels; machines that do not send diagnostic data or are blocked from reaching Microsoft may be excluded from the automatic assist.
- Third‑party tool or driver conflicts: Certain anti‑cheat stacks, virtualization drivers, or older third‑party loaders sometimes interact poorly with Secure Boot changes — vendors and IT teams must test these scenarios. Community and trade press have already flagged gaming anti‑cheat as an area to watch.
What “degraded security state” actually means for Windows 10 users
Microsoft’s own KB is explicit: a device that still only contains the 2011 CA entries after the expiry windows will continue to boot and run, and will keep receiving standard OS updates (if the OS is still covered by the update pipeline), but it will not be able to receive new pre‑OS protections such as DBX revocations or bootloader signing changes. In practice this increases long‑term risk because attackers who find new boot‑level vulnerabilities will have more opportunity on devices that cannot be changed at the firmware trust level.What this does not mean:
- It is not an immediate “bricking” or mass‑outage event: machines will still boot and can still run normal workloads.
- It is not necessarily only a Windows 10 problem: the certificate refresh touches the entire UEFI ecosystem; Windows 11 systems generally follow the same technical update path, but newer Windows 11 devices and Secured-core models have higher default settings that make the transition simpler for those devices.
The Windows 10 support angle: ESU, free Windows 11 upgrades, and what users should know
Microsoft ended broad support for Windows 10 on October 14, 2025. To receive official security updates after that date, consumer devices must enroll in the Windows 10 Extended Security Updates (ESU) program or upgrade to an eligible Windows 11 device. Microsoft’s consumer ESU pathway includes a no‑cost option if device settings are synced to a Microsoft account, alternatives tied to Microsoft Rewards, and a paid $30 option per device; ESU coverage extends through October 13, 2026.Microsoft continues to allow eligible devices to upgrade to Windows 11 for free, but the upgrade is subject to the Windows 11 minimum hardware requirements (TPM 2.0, supported CPU families, UEFI Secure Boot enabled, etc.). For many older PCs, the hardware prerequisites block the free upgrade path and force the user to choose ESU, accept the degraded risk, or replace hardware. Microsoft’s own upgrade FAQ confirms the free upgrade policy for eligible machines.
Practical implications:
- If your Windows 10 PC meets Windows 11 hardware requirements, upgrading is the simpler long‑term security path and automatically handles the certificate update in most cases.
- If your device does not meet Windows 11 requirements, ESU can buy a year of extended security updates; ESU enrollment also ties to update delivery eligibility that, in practice, increases the chance of receiving Microsoft’s assisted certificate updates — but ESU is not an indefinite fix.
OEMs and real‑world rollout: what hardware vendors are saying
Major OEMs have published guidance and lists of supported platforms with BIOS versions that include the new 2023 certificates. For example, HP’s advisory maps platform release years to approximate BIOS rollout windows and calls out that platforms released in 2017 and earlier may not receive a related BIOS update because they are out of vendor support. That mirrors the reality in other vendor advisories: newer, still‑supported models get firmware, older models often do not.This creates a clear two‑tier landscape:
- Supported, recently shipped models — will likely receive a BIOS/UEFI update or accept Microsoft’s assisted update and thus remain fully supported for Secure Boot protections.
- Older or unsupported models — may be stuck with 2011 CA entries indefinitely and therefore cannot receive future pre‑OS protections even if Windows itself is patched (via ESU or other servicing).
A practical checklist for Windows 10 users and small IT teams
If you manage one or more Windows PCs, act now — the window to prepare is measured in months, not years. The following prioritized checklist is designed to be practical for home users and small IT teams.- Inventory: Identify all PCs and record model, firmware/BIOS version, Windows build, and Secure Boot status (enabled/disabled).
- Back up BitLocker keys and user data: Export BitLocker recovery keys and verify you can recover, because firmware or OS changes can trigger BitLocker recovery prompts.
- Check Windows update status: Ensure devices are on a supported Windows 10 build and that cumulative updates through mid‑2025 and later are installed (the 2023 certificate payloads were included in updates shipped in 2025).
- Enable Secure Boot (if it’s safe and compatible): Devices with Secure Boot disabled will neither be protected nor be updated with the new certificates automatically. Reenable only after verifying compatibility with required drivers.
- Visit OEM support pages and install firmware updates: Use vendor tools (HP Support Assistant, Dell Command Update, Lenovo Vantage) to find and install BIOS/UEFI updates that include the 2023 CA entries. If a vendor does not publish an update for the model, treat that device as unlikely to receive the certificate refresh.
- Consider the Windows 11 free upgrade path where eligible: Run Microsoft’s PC Health Check or the vendor’s compatibility tool and plan upgrades for supported machines.
- If staying on Windows 10, enroll in ESU if you meet eligibility and want a one‑year safety net through Oct 13, 2026. Enroll early rather than after an incident.
- For fleets, pilot firmware and OS updates on representative hardware and test every critical third‑party component (anti‑cheat, VPN, custom drivers) for compatibility.
Risks, edge cases, and notable technical details
Edge cases to watch
- Air‑gapped lab machines: If offline, these machines will not receive the Microsoft-assisted update and must be updated via vendor firmware or manual key injection.
- Custom or self‑managed UEFI chains: Systems running nonstandard boot flows (dual‑boot, custom boot loaders, certain Linux distributions with signed shim loaders) should be tested for compatibility after key replacement because the new CA semantics can change trust decisions.
- Gaming and anti‑cheat: Some anti‑cheat kernels and low‑level drivers interact with boot verification and have historically created compatibility hurdles during Secure Boot changes. Test before rolling out widely if you manage gaming rigs.
What administrators must be realistic about
- Updating certificates does not magically restore firmware‑level security on hardware with known device vulnerabilities (bugs in the firmware itself, hardware bugs, or insecure option ROMs). The certificate refresh preserves the trust model but does not fix firmware implementation issues.
- There is a human and logistics cost to remediating older fleets: coordinating vendors, scheduling BIOS updates, staging rollbacks, and making sure BitLocker recovery keys are accessible are nontrivial tasks for small IT teams. The KBs and vendor advisories recommend pilot testing and a phased rollout.
How accurate is the “Windows 10 users are in danger” framing?
The tabloid framing that “Windows 10 users are warned about danger” captures a legitimate underlying technical risk — loss of the ability to update pre‑OS trust — but it’s an alarmist simplification if presented without nuance. The real situation is layered:- The risk is real and measurable: certificates expire, and without the 2023 family some devices cannot accept future DB/DBX updates. That materially reduces the platform’s ability to protect the earliest stages of boot. That is not speculative.
- For many users the transition will be seamless: devices that are maintained with Windows updates and current OEM firmware will be updated automatically or during routine firmware servicing. Microsoft and several OEMs have publicly stated they will assist and have already shipped many updates.
- The greatest danger is concentrated: older hardware, air‑gapped or heavily managed machines, and systems on which administrators have disabled Secure Boot are the ones thable to boot‑level threats and will require intervention.
What we validated and where uncertainty remains
I validated the core technical claims against Microsoft’s published KB “Windows Secure Boot certificate expiration and CA updates,” which lists the expiring certificates, the replacement 2023 certificates, and the practical impacts (June and October 2026 timelines). I cross‑checked those facts against Microsoft cumulative update notes and vendor advisories (example: HP’s guidance), and against independent press coverage from established outlets that tracked the same KB and vendor advisories.Remaining uncertainties and cautionary notes:
- Microsoft’s assisted update mechanism has deployment heuristics (diagnostic telemetry, CFR rollouts) that can change; the exact list of KB numbers and package names used for the assisted deployment may evolve. For precise operational planning, administrators should rely on Microsoft’s official KB change logs and vendor pages rather than third‑party summaries.
- Some press pieces have reported binaries that suggest Windows 10 non‑ESU systems will not receive the full automatic pathway; Microsoft’s KB emphasizes that customers are ultimately responsible for ensuring their devices can accept the elective update. That means the line between “will be updated” and “may not be updated” depends on device configuration and vendor support. Treat statements that say “all Windows 10 devices will be left behind” as overstated; treat statements that say “many devices need proactive action” as accurate.
Bottom line — what every Windows 10 user should do in the next 60–120 days
- Check whether your PC meets Windows 11 requirements; if it does, upgrade to Windows 11 (free for eligible devices) as the simplest long‑term fix. Back up data first.
- If you must remain on Windows 10, enroll in ESU if you qualify and want vendor patches through October 13, 2026 — but don’t treat ESU as a permanent solution.
- Visit your OEM’s support site and install the offered BIOS/UEFI updates that include the 2023 Secure Boot CA entries. If your vendor does not provide an update for your model, assume the device will not receive the firmware‑level certificate refresh and plan accordingly.
- Ensure Secure Boot is enabled where appropriate, back up BitLocker recovery keys, and test recovery procedures.
- For IT administrators: inventory, pilot, coordinate with vendors, and keep in mind anti‑cheat and third‑party boot components when you test. The Secure Boot refresh is a large cross‑industry operation; treat it as scheduled maintenance, not a surprise outage.
Final assessment
The Secure Boot certificate refresh is one of the most consequential platform‑level maintenance operations for Windows in recent memory. It is not a sudden disaster that will immediately strand millions of PCs; rather, it is a scheduled expiration that transforms what would otherwise be a quiet maintenance chore into an imperative for proactive update management. Systems that remain unpatched — because they are on unsupported firmware, have Secure Boot disabled, or are offline — will slowly accumulate risk because they cannot receive future pre‑OS mitigations.The good news is that Microsoft and major OEMs have published guidance, begun shipping updates, and provided assisted update paths. The bad news is that there are real edge cases — chiefly older hardware and isolated fleets — where the certificate refresh will leave devices unable to receive new pre‑boot protections. For home users and small IT teams, the practical prescription is straightforward: inventory, update firmware, back up keys, and either upgrade to Windows 11 if eligible or enroll in ESU if you must stay on Windows 10 for a limited time.
If you want a short, actionable plan tailored to your specific machines (model list, BIOS versions, or an IT‑facing rollout checklist), post the model numbers and Windows builds you’re responsible for and I’ll turn this guidance into a step‑by‑step remediation playbook you can run this week.
Source: Inbox.lv Windows 10 Users Warned About Danger