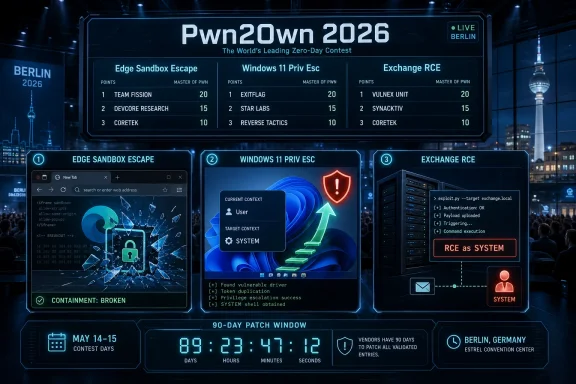
Security researchers at Pwn2Own Berlin 2026 exploited Microsoft Edge, Windows 11, and later Microsoft Exchange at OffensiveCon in Berlin on May 14 and May 15, earning six-figure payouts while starting the contest’s 90-day vendor repair clock for accepted zero-day submissions. The headline is not that Windows “lost” a hacking contest; Pwn2Own is designed to make modern platforms lose under controlled conditions. The sharper point is that Microsoft’s client, browser, and server stack all appeared in the early results of an enterprise-focused event where fully patched systems are the baseline. For Windows admins, the contest is less a spectacle than a preview of the patch-management work now moving toward them.
Pwn2Own has always been a strange public ritual: vendors submit their products to a contest they would rather not headline, researchers show only enough to prove the bug is real, and the public gets a scoreboard before it gets CVEs. That makes the event easy to overread and dangerous to ignore. A successful exploit on stage does not mean attackers are already burning the same chain in the wild, but it does mean a skilled researcher found a reliable path through current defenses.
That distinction matters for Microsoft’s Berlin showing. The first day brought a Microsoft Edge sandbox escape by Cheng-Da Tsai, better known as Orange Tsai, reportedly worth $175,000 after chaining four logic bugs. Windows 11 was hit multiple times through local privilege-escalation demonstrations, each in the familiar but stubborn category where an attacker with limited access seeks higher authority on the machine.
By Day Two, the Microsoft story had moved from desktop containment to server compromise. Orange Tsai reportedly chained three bugs against Microsoft Exchange to gain remote code execution as SYSTEM, a result carrying a $200,000 payout and 20 Master of Pwn points. That is a different kind of result from a browser sandbox escape or a local privilege escalation, but it lands in the same operational inbox: Microsoft customers will eventually need patches, mitigations, detection logic, and an explanation for what risk existed before disclosure.
The contest’s rules are part of the story. Pwn2Own entries are aimed at current, supported, fully patched targets, and accepted bugs enter a coordinated disclosure process that gives vendors a 90-day repair window before technical details are expected to surface. That is the bargain: researchers get recognition and money, vendors get a controlled runway, and defenders get an uncomfortable but useful early warning.
Edge is Chromium-based, but Microsoft’s version is not merely “Chrome with a logo.” Enterprise policy hooks, identity integrations, Defender tie-ins, update channels, and Windows integration make it a Microsoft platform in practice. When a researcher breaks out of Edge’s sandbox at Pwn2Own, the result resonates beyond browser market share because Edge is now a default enterprise application, an identity surface, and a policy enforcement point.
The reported four-bug chain also matters. A single bug can sometimes be dismissed as a mistake in one component; a chain shows how assumptions across components can be composed into a working path. Modern exploitation is often less about one magic flaw than about stitching together logic errors, policy gaps, type confusion, sandbox permissions, and predictable system behavior until a theoretical weakness becomes a reliable demonstration.
For users, the practical lesson is not to abandon Edge in a panic. Chrome, Safari, Firefox, and other major browsers have all had high-profile contest and real-world vulnerabilities. The lesson is that browser isolation is a living security system, not a finished product, and its value depends on rapid updates, careful enterprise policy, and limiting what a browser session can reach once something goes wrong.
For administrators, this is where defaults deserve a second look. Edge is often allowed to reach intranet applications, cloud admin portals, password managers, device enrollment pages, and line-of-business systems. If a browser is treated as both the main work surface and a trusted internal client, a sandbox escape becomes more than a browser team’s problem.
That is why the repeated Windows 11 demonstrations are significant. On Day One, Angelboy and TwinkleStar03 reportedly used an improper access-control issue to escalate privileges, while Marcin Wiązowski and Kentaro Kawane added separate Windows 11 privilege-escalation wins. On Day Two, Siyeon Wi reportedly added another Windows 11 local privilege-escalation result using an integer overflow, though at a reduced payout that suggests contest-specific scoring or collision factors may have affected the award.
The important detail is not merely that Windows 11 “was hacked.” It is that multiple researchers reached the same broad target class through separate demonstrations. A single privilege-escalation bug can be a one-off defect. Several accepted local elevation results suggest a broader surface area where the operating system’s compatibility, driver model, services, permissions, and legacy assumptions continue to offer attack paths.
Windows has improved dramatically over the last two decades. Kernel hardening, virtualization-based security, credential isolation, exploit mitigations, signed drivers, and hardware-backed features have raised the cost of compromise. But Windows also carries an enormous burden: decades of application compatibility, enterprise manageability, third-party drivers, shell extensions, endpoint agents, and administrative tooling that all need privileged interaction somewhere.
That is the paradox of Windows 11 security. Microsoft can build a more locked-down OS, but its customer base still expects the OS to run old applications, support complex endpoint agents, talk to mixed infrastructure, and remain manageable at scale. Local privilege escalation lives in those seams, where ideal architecture collides with enterprise reality.
Orange Tsai’s reported $200,000 Exchange chain was therefore bound to draw attention. Remote code execution as SYSTEM is a severe outcome in any server product. In Exchange, it evokes a familiar defensive nightmare: a communications platform that is often deeply integrated with identity, mail flow, compliance systems, archives, mobile access, and hybrid Microsoft 365 environments.
The result does not mean every Exchange server is immediately exposed to an active exploit. Pwn2Own does not publish the chain on the day of the win, and the vendor disclosure process exists precisely to avoid handing attackers a playbook. Still, security teams should treat the result as a planning signal rather than a curiosity. If Exchange is in the environment, especially on-premises Exchange, it belongs on the watch list for upcoming Microsoft advisories and emergency change windows.
This is also where the move to cloud services does not fully erase the problem. Many organizations still maintain Exchange Server for hybrid management, specialized workflows, compliance reasons, or migration inertia. A server that is “only there for hybrid” can still be a high-value asset if it is reachable, privileged, and connected to identity or mail infrastructure.
Microsoft has spent years trying to reduce Exchange’s on-premises blast radius through guidance, emergency mitigation tools, cumulative update requirements, and cloud migration pressure. Pwn2Own’s Exchange result is a reminder that the platform’s security story is still not just about code quality. It is about how much legacy infrastructure remains deployed, how quickly organizations can patch it, and whether they have reduced exposure before the next emergency arrives.
That timeline is generous compared with active exploitation, but tight compared with enterprise change management. Microsoft has to reproduce the bugs, identify root causes, produce fixes, test regressions, coordinate across affected components, and ship updates through channels that reach consumer PCs, managed endpoints, servers, and cloud-connected environments. Customers then have to absorb those fixes without breaking business-critical software.
The 90-day period also creates an information gap. Defenders know that accepted vulnerabilities exist, but not exactly where they sit or how exploitable they are outside the contest setup. That gap is frustrating by design. Too much detail would help attackers; too little detail leaves administrators with little to do beyond hardening basics and preparing for patches.
This is where mature security teams separate signal from noise. They do not need exploit code to act on the broad categories. Browser sandbox escapes argue for strict browser update enforcement, reduced exposure of sensitive internal apps, and stronger isolation between browsing and administration. Windows privilege escalations argue for least privilege, endpoint detection coverage, credential protection, and rapid OS patch testing. Exchange remote code execution argues for exposure review, segmentation, logging, and readiness for out-of-band action if Microsoft escalates.
Patch Tuesday may eventually absorb some of these fixes, or Microsoft may move faster if severity and exploitability demand it. Until CVEs and advisories arrive, nobody outside the disclosure circle should pretend to know the exact remediation path. But the direction of travel is obvious: the contest has turned future Microsoft security updates from routine maintenance into items that deserve close reading.
OpenAI Codex, Anthropic Claude Code, Cursor, LiteLLM, LM Studio, Chroma, Megatron Bridge, and NVIDIA Container Toolkit results show how quickly AI-adjacent tooling has become contest-worthy. These products and frameworks are not peripheral toys in every organization anymore. They are creeping into developer workflows, internal automation, model experimentation, and data pipelines, often faster than security teams can build governance around them.
But Microsoft still mattered because it remains the connective tissue of many environments. Edge is the browser users open by default. Windows 11 is the endpoint platform for employees and administrators. Exchange remains a critical mail and identity-adjacent server in many deployments. SharePoint was also on the schedule, even though at least one reported Day Two attempt did not land within the allotted time.
That combination made Microsoft’s presence qualitatively different from a single AI tool getting popped. AI targets may be newer and more fashionable, but Microsoft targets sit at the center of daily operations. An exploit in a coding agent can be severe in a development environment; an exploit chain touching Edge, Windows, or Exchange speaks to the baseline infrastructure many companies assume will simply be there and keep working.
There is a second-order point here for WindowsForum readers. The future of Windows security will not be argued only inside Windows. It will be shaped by browsers, identity systems, AI agents, developer tools, hypervisors, containers, GPUs, and cloud services that sit around Windows endpoints. Pwn2Own Berlin’s target list reads like a map of that convergence.
But defenders should resist ranking risk by payout alone. Prize amounts are shaped by contest design, target category, difficulty, collision rules, and strategic incentives. A $30,000 local privilege escalation can matter enormously in a real intrusion if it turns phishing access into domain compromise. A $175,000 browser escape is eye-catching, but its real-world impact depends on the rest of the chain and the victim’s environment.
The better reading is categorical. Browser sandbox escape means a containment layer failed. Local privilege escalation means post-compromise hardening still has seams. Server-side remote code execution means exposed enterprise infrastructure may carry a direct path to high privilege. AI and developer-tool bugs mean the software supply chain and development workstation are becoming richer targets.
That category-based reading also helps avoid the annual Pwn2Own panic cycle. The event is not evidence that every product is hopeless. It is evidence that high-value software, when placed under financial incentive and expert scrutiny, yields flaws. That should not shock anyone who has watched software security for more than a year.
The useful response is discipline. Track vendor advisories. Test patches quickly. Reduce unnecessary exposure. Keep browsers and endpoints current. Audit who has local admin rights. Review Exchange exposure. Make sure security tools can see process behavior, privilege changes, child processes, suspicious PowerShell, and authentication anomalies. None of that is glamorous, but it is how contest findings eventually become less dangerous in production.
The Berlin results do not invalidate that strategy. In fact, the need for exploit chains proves that defenses are doing real work. Attackers and researchers increasingly need multiple bugs, clever logic paths, and environment-specific techniques to get high-value outcomes. That is a better world than the era of single trivial memory corruptions yielding instant remote compromise.
But complexity is also the enemy. Every new mitigation creates assumptions. Every compatibility exception creates a seam. Every enterprise management feature becomes a potential crossing point between low privilege and high privilege. Every hybrid deployment increases the number of places where identity, mail, endpoints, and cloud control planes touch.
This is why Microsoft’s hardest security problem is not merely writing fewer bugs. It is reducing the number of places where bugs compose into chains. A sandbox escape is rarely just a sandbox problem. A privilege escalation is rarely just a permissions mistake. An Exchange RCE is rarely just one parser bug in isolation. Modern compromise lives in composition.
For customers, that means buying into Microsoft’s security ecosystem does not remove the need for architecture. Defender, Intune, Entra ID, Edge policies, Windows security baselines, and Exchange guidance are tools, not guarantees. The difference between a contained incident and a major compromise often comes down to whether those tools were configured coherently before the exploit existed.
Windows endpoints are comparatively easy to patch in well-managed environments, but only comparatively. Browser updates can be fast, yet enterprise deferrals, kiosk systems, virtual desktops, offline machines, and tightly controlled application stacks can slow rollout. Windows cumulative updates still require testing and reboot coordination. Exchange updates remain more sensitive because server patching can involve schema expectations, cumulative update prerequisites, backups, transport behavior, and high-availability planning.
The hardest part is prioritization. If Microsoft eventually ships fixes for several Pwn2Own-derived bugs in the same cycle as dozens of unrelated vulnerabilities, administrators will need to identify which updates map to these contest results and whether exploitation is considered more likely. Microsoft’s advisories may not always say “this was the Pwn2Own bug” in a way that satisfies every security team, but patterns in product, impact, and timing will matter.
Organizations that wait for perfect clarity will be late. The better posture is to prepare now: know where Edge update enforcement may fail, know which Windows 11 devices are outside normal rings, know whether any Exchange servers are internet-facing, and know who can approve emergency changes. Pwn2Own does not give defenders exploit details, but it does give them a reason to check whether the patching machinery still works.
There is also a communications task. Security teams will need to explain why a contest result from May can become an urgent patch item weeks or months later. Business leaders often treat vulnerability news as either immediate crisis or irrelevant noise. Pwn2Own sits in between: not necessarily an emergency today, but a credible warning that concrete fixes are coming.
For Edge, administrators should ensure update channels are not stuck, policies do not delay critical browser patches unnecessarily, and privileged administration is not performed casually from the same browser context used for general web activity. For Windows 11, organizations should tighten local administrator rights, maintain endpoint telemetry, and verify that security baselines are actually applied rather than merely documented. For Exchange, the question is even simpler: if it exists, why does it exist, who owns it, how exposed is it, and how quickly can it be patched?
Home users have a simpler version of the same problem. Keep Windows Update enabled, keep Edge current even if it is not the primary browser, avoid running day-to-day as an administrator where possible, and do not treat “fully patched” as a permanent state. Fully patched on May 14 was still good enough to be a Pwn2Own target; fully patched after Microsoft ships fixes will mean something different.
The contest also argues for humility around security marketing. No vendor’s “secure by default” claim survives contact with a skilled researcher and a meaningful prize pool without caveats. That is not cynicism; it is how defensive engineering improves. Public, rewarded failure is healthier than private, criminal discovery.
For WindowsForum readers, the concrete reading is this:
Source: WinBuzzer Windows 11 and Microsoft Edge Hacked at Pwn2Own Berlin 2026
 Pwn2Own Turned Microsoft’s Defense-in-Depth Story Into a Live Demo
Pwn2Own Turned Microsoft’s Defense-in-Depth Story Into a Live Demo
Pwn2Own has always been a strange public ritual: vendors submit their products to a contest they would rather not headline, researchers show only enough to prove the bug is real, and the public gets a scoreboard before it gets CVEs. That makes the event easy to overread and dangerous to ignore. A successful exploit on stage does not mean attackers are already burning the same chain in the wild, but it does mean a skilled researcher found a reliable path through current defenses.That distinction matters for Microsoft’s Berlin showing. The first day brought a Microsoft Edge sandbox escape by Cheng-Da Tsai, better known as Orange Tsai, reportedly worth $175,000 after chaining four logic bugs. Windows 11 was hit multiple times through local privilege-escalation demonstrations, each in the familiar but stubborn category where an attacker with limited access seeks higher authority on the machine.
By Day Two, the Microsoft story had moved from desktop containment to server compromise. Orange Tsai reportedly chained three bugs against Microsoft Exchange to gain remote code execution as SYSTEM, a result carrying a $200,000 payout and 20 Master of Pwn points. That is a different kind of result from a browser sandbox escape or a local privilege escalation, but it lands in the same operational inbox: Microsoft customers will eventually need patches, mitigations, detection logic, and an explanation for what risk existed before disclosure.
The contest’s rules are part of the story. Pwn2Own entries are aimed at current, supported, fully patched targets, and accepted bugs enter a coordinated disclosure process that gives vendors a 90-day repair window before technical details are expected to surface. That is the bargain: researchers get recognition and money, vendors get a controlled runway, and defenders get an uncomfortable but useful early warning.
The Edge Sandbox Escape Was the Flashiest Result Because Browsers Are Still the Front Door
The Edge result drew attention because browsers are where security architecture meets user habit. Microsoft can harden Windows, push SmartScreen warnings, promote memory safety, and isolate renderer processes, but the browser remains the place where arbitrary content arrives all day. A sandbox escape is therefore not just another bug class; it is a statement about a boundary Microsoft depends on heavily.Edge is Chromium-based, but Microsoft’s version is not merely “Chrome with a logo.” Enterprise policy hooks, identity integrations, Defender tie-ins, update channels, and Windows integration make it a Microsoft platform in practice. When a researcher breaks out of Edge’s sandbox at Pwn2Own, the result resonates beyond browser market share because Edge is now a default enterprise application, an identity surface, and a policy enforcement point.
The reported four-bug chain also matters. A single bug can sometimes be dismissed as a mistake in one component; a chain shows how assumptions across components can be composed into a working path. Modern exploitation is often less about one magic flaw than about stitching together logic errors, policy gaps, type confusion, sandbox permissions, and predictable system behavior until a theoretical weakness becomes a reliable demonstration.
For users, the practical lesson is not to abandon Edge in a panic. Chrome, Safari, Firefox, and other major browsers have all had high-profile contest and real-world vulnerabilities. The lesson is that browser isolation is a living security system, not a finished product, and its value depends on rapid updates, careful enterprise policy, and limiting what a browser session can reach once something goes wrong.
For administrators, this is where defaults deserve a second look. Edge is often allowed to reach intranet applications, cloud admin portals, password managers, device enrollment pages, and line-of-business systems. If a browser is treated as both the main work surface and a trusted internal client, a sandbox escape becomes more than a browser team’s problem.
Windows 11 Took the Quieter Hits That Often Matter Most
The Windows 11 results were less cinematic than a browser escape, but they may be more familiar to defenders. Local privilege escalation is the old workhorse of post-compromise operations. It does not usually provide the first foothold, but it can turn a limited foothold into persistence, credential access, security-tool tampering, and lateral movement.That is why the repeated Windows 11 demonstrations are significant. On Day One, Angelboy and TwinkleStar03 reportedly used an improper access-control issue to escalate privileges, while Marcin Wiązowski and Kentaro Kawane added separate Windows 11 privilege-escalation wins. On Day Two, Siyeon Wi reportedly added another Windows 11 local privilege-escalation result using an integer overflow, though at a reduced payout that suggests contest-specific scoring or collision factors may have affected the award.
The important detail is not merely that Windows 11 “was hacked.” It is that multiple researchers reached the same broad target class through separate demonstrations. A single privilege-escalation bug can be a one-off defect. Several accepted local elevation results suggest a broader surface area where the operating system’s compatibility, driver model, services, permissions, and legacy assumptions continue to offer attack paths.
Windows has improved dramatically over the last two decades. Kernel hardening, virtualization-based security, credential isolation, exploit mitigations, signed drivers, and hardware-backed features have raised the cost of compromise. But Windows also carries an enormous burden: decades of application compatibility, enterprise manageability, third-party drivers, shell extensions, endpoint agents, and administrative tooling that all need privileged interaction somewhere.
That is the paradox of Windows 11 security. Microsoft can build a more locked-down OS, but its customer base still expects the OS to run old applications, support complex endpoint agents, talk to mixed infrastructure, and remain manageable at scale. Local privilege escalation lives in those seams, where ideal architecture collides with enterprise reality.
Exchange Made the Contest Feel Less Like a Desktop Story
The Day Two Exchange result changed the mood because Exchange is not just another Microsoft product. For many administrators, Exchange carries scar tissue. The platform’s history includes high-impact server-side vulnerability waves, emergency mitigations, rushed patch cycles, internet-exposed deployments, hybrid identity complexity, and long-tail remediation problems that outlast the first advisory.Orange Tsai’s reported $200,000 Exchange chain was therefore bound to draw attention. Remote code execution as SYSTEM is a severe outcome in any server product. In Exchange, it evokes a familiar defensive nightmare: a communications platform that is often deeply integrated with identity, mail flow, compliance systems, archives, mobile access, and hybrid Microsoft 365 environments.
The result does not mean every Exchange server is immediately exposed to an active exploit. Pwn2Own does not publish the chain on the day of the win, and the vendor disclosure process exists precisely to avoid handing attackers a playbook. Still, security teams should treat the result as a planning signal rather than a curiosity. If Exchange is in the environment, especially on-premises Exchange, it belongs on the watch list for upcoming Microsoft advisories and emergency change windows.
This is also where the move to cloud services does not fully erase the problem. Many organizations still maintain Exchange Server for hybrid management, specialized workflows, compliance reasons, or migration inertia. A server that is “only there for hybrid” can still be a high-value asset if it is reachable, privileged, and connected to identity or mail infrastructure.
Microsoft has spent years trying to reduce Exchange’s on-premises blast radius through guidance, emergency mitigation tools, cumulative update requirements, and cloud migration pressure. Pwn2Own’s Exchange result is a reminder that the platform’s security story is still not just about code quality. It is about how much legacy infrastructure remains deployed, how quickly organizations can patch it, and whether they have reduced exposure before the next emergency arrives.
The 90-Day Clock Is the Real Product Roadmap Now
The most important date in the story is not only May 14 or May 15. It is the disclosure clock that began once the bugs were accepted. Under Pwn2Own’s normal model, vendors receive the vulnerability details and have 90 days to produce fixes before technical information may be disclosed.That timeline is generous compared with active exploitation, but tight compared with enterprise change management. Microsoft has to reproduce the bugs, identify root causes, produce fixes, test regressions, coordinate across affected components, and ship updates through channels that reach consumer PCs, managed endpoints, servers, and cloud-connected environments. Customers then have to absorb those fixes without breaking business-critical software.
The 90-day period also creates an information gap. Defenders know that accepted vulnerabilities exist, but not exactly where they sit or how exploitable they are outside the contest setup. That gap is frustrating by design. Too much detail would help attackers; too little detail leaves administrators with little to do beyond hardening basics and preparing for patches.
This is where mature security teams separate signal from noise. They do not need exploit code to act on the broad categories. Browser sandbox escapes argue for strict browser update enforcement, reduced exposure of sensitive internal apps, and stronger isolation between browsing and administration. Windows privilege escalations argue for least privilege, endpoint detection coverage, credential protection, and rapid OS patch testing. Exchange remote code execution argues for exposure review, segmentation, logging, and readiness for out-of-band action if Microsoft escalates.
Patch Tuesday may eventually absorb some of these fixes, or Microsoft may move faster if severity and exploitability demand it. Until CVEs and advisories arrive, nobody outside the disclosure circle should pretend to know the exact remediation path. But the direction of travel is obvious: the contest has turned future Microsoft security updates from routine maintenance into items that deserve close reading.
AI Targets Stole Some Oxygen, but Microsoft Remained the Enterprise Center of Gravity
Berlin 2026 was not a Windows-only event. The contest’s target list reflected the industry’s current anxieties: AI coding agents, local inference tools, NVIDIA components, virtualization, browsers, servers, Linux workstations, and cloud-native/container software all sat in the prize pool. That breadth is important because enterprise attack surfaces no longer map neatly to operating systems.OpenAI Codex, Anthropic Claude Code, Cursor, LiteLLM, LM Studio, Chroma, Megatron Bridge, and NVIDIA Container Toolkit results show how quickly AI-adjacent tooling has become contest-worthy. These products and frameworks are not peripheral toys in every organization anymore. They are creeping into developer workflows, internal automation, model experimentation, and data pipelines, often faster than security teams can build governance around them.
But Microsoft still mattered because it remains the connective tissue of many environments. Edge is the browser users open by default. Windows 11 is the endpoint platform for employees and administrators. Exchange remains a critical mail and identity-adjacent server in many deployments. SharePoint was also on the schedule, even though at least one reported Day Two attempt did not land within the allotted time.
That combination made Microsoft’s presence qualitatively different from a single AI tool getting popped. AI targets may be newer and more fashionable, but Microsoft targets sit at the center of daily operations. An exploit in a coding agent can be severe in a development environment; an exploit chain touching Edge, Windows, or Exchange speaks to the baseline infrastructure many companies assume will simply be there and keep working.
There is a second-order point here for WindowsForum readers. The future of Windows security will not be argued only inside Windows. It will be shaped by browsers, identity systems, AI agents, developer tools, hypervisors, containers, GPUs, and cloud services that sit around Windows endpoints. Pwn2Own Berlin’s target list reads like a map of that convergence.
Leaderboards Reward Spectacle, but Defenders Should Read the Categories
The contest scoreboard naturally turns researchers into protagonists. Orange Tsai and DEVCORE led much of the Microsoft narrative because the Edge and Exchange wins were large, clean, and easy to explain. The Master of Pwn points make that storyline even more compelling, especially when one researcher can rack up huge awards across different Microsoft products.But defenders should resist ranking risk by payout alone. Prize amounts are shaped by contest design, target category, difficulty, collision rules, and strategic incentives. A $30,000 local privilege escalation can matter enormously in a real intrusion if it turns phishing access into domain compromise. A $175,000 browser escape is eye-catching, but its real-world impact depends on the rest of the chain and the victim’s environment.
The better reading is categorical. Browser sandbox escape means a containment layer failed. Local privilege escalation means post-compromise hardening still has seams. Server-side remote code execution means exposed enterprise infrastructure may carry a direct path to high privilege. AI and developer-tool bugs mean the software supply chain and development workstation are becoming richer targets.
That category-based reading also helps avoid the annual Pwn2Own panic cycle. The event is not evidence that every product is hopeless. It is evidence that high-value software, when placed under financial incentive and expert scrutiny, yields flaws. That should not shock anyone who has watched software security for more than a year.
The useful response is discipline. Track vendor advisories. Test patches quickly. Reduce unnecessary exposure. Keep browsers and endpoints current. Audit who has local admin rights. Review Exchange exposure. Make sure security tools can see process behavior, privilege changes, child processes, suspicious PowerShell, and authentication anomalies. None of that is glamorous, but it is how contest findings eventually become less dangerous in production.
Microsoft’s Security Pitch Now Has to Survive Its Own Complexity
Microsoft’s modern security pitch is broad and ambitious. Windows 11 leans on hardware requirements, TPM-backed features, virtualization-based security, secured-core PCs, Smart App Control, Defender, identity protections, and a cloud intelligence layer. Edge leans on Chromium hardening, sandboxing, site isolation, reputation checks, and enterprise controls. Exchange, where still deployed, sits behind years of patching guidance and hardening recommendations.The Berlin results do not invalidate that strategy. In fact, the need for exploit chains proves that defenses are doing real work. Attackers and researchers increasingly need multiple bugs, clever logic paths, and environment-specific techniques to get high-value outcomes. That is a better world than the era of single trivial memory corruptions yielding instant remote compromise.
But complexity is also the enemy. Every new mitigation creates assumptions. Every compatibility exception creates a seam. Every enterprise management feature becomes a potential crossing point between low privilege and high privilege. Every hybrid deployment increases the number of places where identity, mail, endpoints, and cloud control planes touch.
This is why Microsoft’s hardest security problem is not merely writing fewer bugs. It is reducing the number of places where bugs compose into chains. A sandbox escape is rarely just a sandbox problem. A privilege escalation is rarely just a permissions mistake. An Exchange RCE is rarely just one parser bug in isolation. Modern compromise lives in composition.
For customers, that means buying into Microsoft’s security ecosystem does not remove the need for architecture. Defender, Intune, Entra ID, Edge policies, Windows security baselines, and Exchange guidance are tools, not guarantees. The difference between a contained incident and a major compromise often comes down to whether those tools were configured coherently before the exploit existed.
The Patch Window Is Shorter Than It Looks for Enterprise IT
Ninety days sounds like a long time until a fix lands in a production estate with thousands of machines, multiple rings, application dependencies, maintenance windows, and business owners who remember the last broken update. The Pwn2Own clock is vendor-facing, but its second half becomes customer-facing very quickly. Once Microsoft ships, the operational clock starts.Windows endpoints are comparatively easy to patch in well-managed environments, but only comparatively. Browser updates can be fast, yet enterprise deferrals, kiosk systems, virtual desktops, offline machines, and tightly controlled application stacks can slow rollout. Windows cumulative updates still require testing and reboot coordination. Exchange updates remain more sensitive because server patching can involve schema expectations, cumulative update prerequisites, backups, transport behavior, and high-availability planning.
The hardest part is prioritization. If Microsoft eventually ships fixes for several Pwn2Own-derived bugs in the same cycle as dozens of unrelated vulnerabilities, administrators will need to identify which updates map to these contest results and whether exploitation is considered more likely. Microsoft’s advisories may not always say “this was the Pwn2Own bug” in a way that satisfies every security team, but patterns in product, impact, and timing will matter.
Organizations that wait for perfect clarity will be late. The better posture is to prepare now: know where Edge update enforcement may fail, know which Windows 11 devices are outside normal rings, know whether any Exchange servers are internet-facing, and know who can approve emergency changes. Pwn2Own does not give defenders exploit details, but it does give them a reason to check whether the patching machinery still works.
There is also a communications task. Security teams will need to explain why a contest result from May can become an urgent patch item weeks or months later. Business leaders often treat vulnerability news as either immediate crisis or irrelevant noise. Pwn2Own sits in between: not necessarily an emergency today, but a credible warning that concrete fixes are coming.
The Windows Admin’s Real Advantage Is Boring Preparedness
The practical response to Berlin is not panic, and it is not smug dismissal. It is boring preparedness, which is still the most underrated advantage defenders have. The exploit chains are private for now, but the affected product families are not.For Edge, administrators should ensure update channels are not stuck, policies do not delay critical browser patches unnecessarily, and privileged administration is not performed casually from the same browser context used for general web activity. For Windows 11, organizations should tighten local administrator rights, maintain endpoint telemetry, and verify that security baselines are actually applied rather than merely documented. For Exchange, the question is even simpler: if it exists, why does it exist, who owns it, how exposed is it, and how quickly can it be patched?
Home users have a simpler version of the same problem. Keep Windows Update enabled, keep Edge current even if it is not the primary browser, avoid running day-to-day as an administrator where possible, and do not treat “fully patched” as a permanent state. Fully patched on May 14 was still good enough to be a Pwn2Own target; fully patched after Microsoft ships fixes will mean something different.
The contest also argues for humility around security marketing. No vendor’s “secure by default” claim survives contact with a skilled researcher and a meaningful prize pool without caveats. That is not cynicism; it is how defensive engineering improves. Public, rewarded failure is healthier than private, criminal discovery.
The Berlin Scoreboard Leaves a Patch Tuesday Shadow
The immediate facts are clear enough, even while the technical details remain sealed. Microsoft Edge suffered a sandbox-escape demonstration. Windows 11 suffered multiple local privilege-escalation demonstrations. Microsoft Exchange suffered a high-value remote-code-execution demonstration as SYSTEM. The contest paid large rewards, and the disclosure clock is now running.For WindowsForum readers, the concrete reading is this:
- Microsoft’s Pwn2Own Berlin 2026 exposure spans browser, endpoint, and server layers rather than one isolated product line.
- The Edge result matters because sandbox escapes attack one of the main assumptions behind safe daily browsing.
- The Windows 11 results matter because local privilege escalation is often the bridge between initial access and meaningful compromise.
- The Exchange result matters because remote code execution as SYSTEM on mail infrastructure is the kind of outcome administrators cannot afford to treat casually.
- The 90-day disclosure window means defenders should expect future advisories and should validate patching workflows before fixes arrive.
- The absence of public exploit details lowers immediate copycat risk, but it does not reduce the need to prepare.
Source: WinBuzzer Windows 11 and Microsoft Edge Hacked at Pwn2Own Berlin 2026