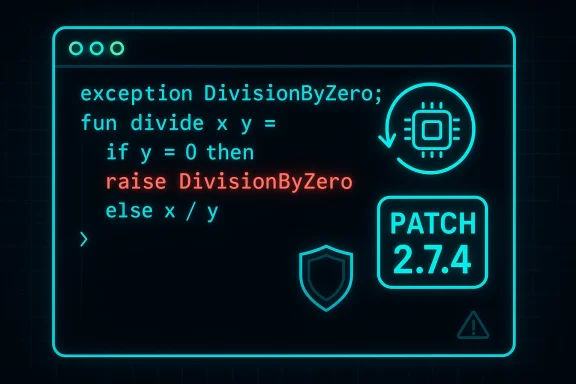
An innocuous-looking three-character input — the Standard ML token exception — quietly exposed a logic flaw in the popular Python syntax-highlighting library Pygments, allowing attackers to force an infinite loop in the SML lexer and cause a denial-of-service condition across any system that performs untrusted highlighting with the affected releases. The bug, tracked as CVE-2021-20270, affects Pygments versions >= 1.5 and < 2.7.4 and was fixed in the 2.7.4 release; public advisories and upstream commits make the technical root cause and remediation path clear. (advisories.gitlab.com) (github.com)
Pygments is a widely used, general-purpose syntax highlighter written in Python and embedded in many server-side applications: documentation generators, code-hosting front ends, wikis, forum software, and web-based editors. Because it executes language lexers on user-supplied code, it must parse arbitrary inputs quickly and robustly; any error in a lexer can translate directly into a service’s availability problem. The SML (Standard ML) lexer in Pygments introduced in earlier releases contained a regular-expression based rule that, under specific input, would never advance the internal parsing state and therefore loop indefinitely. The vulnerability was disclosed publicly in March 2021 and is cataloged in standard vulnerability databases.
The practical exploit is trivial to construct: a file composed only of the token "exception" — syntactically plausible as an SML fragment — is sufficient to trigger the lexer’s broken control flow and hang the highlighting routine. This type of input is small, easily delivered, and requires no authentication or privileges, which makes the vulnerability a low-effort, high-impact availability risk for any service that highlights untrusted SML code without sandboxing or resource limits.
Practical steps for operations teams:
For defenders, the path is clear:
The SML-lexer infinite loop is a compact illustration of how subtle control-flow assumptions in pattern-based parsers can cause outsized operational impact. The vulnerability was fixed upstream with a small code correction and packaged by major distributions; the real risk remains in unpatched deployments and in systems that highlight untrusted code without resource isolation. If your service highlights user code, treat this as a reminder: small libraries can produce large outages, and engineering controls like sandboxing and timeouts are as essential as code fixes in keeping services robust.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Pygments is a widely used, general-purpose syntax highlighter written in Python and embedded in many server-side applications: documentation generators, code-hosting front ends, wikis, forum software, and web-based editors. Because it executes language lexers on user-supplied code, it must parse arbitrary inputs quickly and robustly; any error in a lexer can translate directly into a service’s availability problem. The SML (Standard ML) lexer in Pygments introduced in earlier releases contained a regular-expression based rule that, under specific input, would never advance the internal parsing state and therefore loop indefinitely. The vulnerability was disclosed publicly in March 2021 and is cataloged in standard vulnerability databases.The practical exploit is trivial to construct: a file composed only of the token "exception" — syntactically plausible as an SML fragment — is sufficient to trigger the lexer’s broken control flow and hang the highlighting routine. This type of input is small, easily delivered, and requires no authentication or privileges, which makes the vulnerability a low-effort, high-impact availability risk for any service that highlights untrusted SML code without sandboxing or resource limits.
What went wrong: technical root cause
Lexer mechanics and lookahead traps
Pygments lexers are implemented as sets of regular-expression rules and state transitions. The SML lexer used a lookahead-only pattern that was mistakenly included in a state where the lookahead could transition — effectively creating an unreachable exit condition for certain inputs. When the lexer entered that state on input like "exception", the regular-expression engine matched the lookahead but the state machine did not advance to a new consuming rule; instead the same state and pattern were re-evaluated on the same input, producing an infinite loop. The upstream commit that fixed the bug explains the issue succinctly: a lookahead-only pattern was included where it shouldn’t have been, and the patch replaced the lookahead with a direct match so that the lexer consumes input and advances correctly. (github.com)The fix in code
The upstream fix — committed to the Pygments repository and included in the 2.7.4 release — makes relatively small but crucial changes to the SML lexer rules:- It replaces the lookahead-only pattern that matched
exceptionwithout consuming with a direct token match that consumes the word. - It simplifies the state transitions for the SML lexer to ensure that state pop/push operations happen predictably after the keyword is recognized.
- It adds a default fallback (a
#pop) in the error path to ensure the lexer always exits a special state instead of spinning.
Timelines and public disclosure
- The vulnerability was publicly recorded and assigned CVE-2021-20270 in March 2021, with NVD and several vendor advisories cataloging the problem and affected versions.
- Pygments pushed fixes into the project and released version 2.7.4 (release date recorded as January 12, 2021 in the projeccludes the SML lexer fix among other updates. Distribution and downstream advisories followed as packagers rebuilt and published patched packages.
- Several OS and distribution security trackers recorded the issue and published coordination messages; Debian, Alpine, and other packaging ecosystems issued updates to their Pygments packages covering the fix.
Impact: availability, exploitation scenarios, and reach
Severity and CVSS
The community-assigned severity for CVE-2021-20270 is High (CVSS 3.1 score around 7.5) because the vulnerability is remotely exploitable without authentication, requires no special privileges, and results in availability loss only — i.e., denial of service by hanging the highlighting process. The lack of confidentiality or integrity impact keeps this from being an arbitrary code execution issue, but the ease of exploitation amplifies operational risk for web-facing services that perform syntax highlighting on user content. (advisories.gitlab.com)Realistic exploitation scenarios
- Public code-rendering pages (forum posts, pastebins, documentation platforms) that automatically highlight user-supplied code can be forced into long-running highlights and thus tie up worker threads/processes. A small stream of malicious uploads can saturate available CPU and threads and cause total denial of service for legitimate users.
- Continuous integration (CI) systems or documentation pipelines that synthesize highlighted previews of submitted code snippets may be blocked indefinitely, stalling build pipelines or documentation runs until manual intervention.
- Services that expose syntax-highlighting functionality over an API (for example, "render this code to HTML") can be trivially abused by unauthenticated callers crafting minimal payloads.
Who’s affected
Any application or service that includes a vulnerable Pygments package and that highlights untrusted SML input is at risk. Examples include but are not limited to:- Wiki engines or documentation sites that use Pygments directly or via plugins.
- Web-based code viewers and paste services that accept raw source files.
- Internal tooling (CI logs, code review previews) that renders source code into HTML.
- Third-party packages or vendor applications that embed Pygments as part of their web UI stack.
Detection and verification
Detecting whether an environment is vulnerable and has exploitable exposure involves two complementary checks:- Inventory the installed Pygments package version across your environment. The vulnerability affects Pygments versions starting at 1.5 up to and including 2.7.3; the fixed version is 2.7.4. If your environment has any Pygments release in the affected range, assume the lexer bug exists. ﹙Indicator: package metadata via pip, distro package managers, or container images.﹚ (advisories.gitlab.com)
- Test highlighting paths safely in a sandbox. Where practical, run a controlled test in a resource-limited sandboxed process: feed the literal string "exception" to the SML highlighting code and observe whether processing completes or the worker stalls. If the highlighting call never returns or consumes unbounded CPU, the instance is exploitable. Caveat: do not run this test on production worker pools without process-level timeouts and resource limits — the test is intended for isolated verification only.
Mitigation and remediation (practical guidance)
The primary and simplest remediation is to upgrade Pygments to a patched release. The official guidance from project and packaging advisories is unambiguous: update to Pygments 2.7.4 or later. (advisories.gitlab.com)Practical steps for operations teams:
- Inventory:
- List systems and container images that include Pygments packages.
- Identify applications that call Pygments on untrusted input (web UI components, pastebins, API endpoints).
- Upgrade:
- For Python-managed deployments: pin and install Pygments >= 2.7.4 (or the latest secure release).
- For OS-packaged installations: apply distro security updates (Debian/Alpine/Red Hat updates have patches and new package releases).
- Rebuild and redeploy containers or artifacts after dependency upgrades.
- Apply runtime mitigations until upgrades are possible:
- Enforce per-request CPU and time limits for highlighting calls (worker process timeouts or thread-level watchdogs).
- Run syntax highlighting inside an isolated process or container with strict resource limits (cgroups, systemd slices, or sandboxing).
- Validate and filter input: drop or reject SML content entirely if your service does not need to support SML highlighting.
- Harden exposure:
- If highlighting is exposed via external APIs, require authentication or rate-limiting for calls that accept arbitrary code.
- Move syntax highlighting into a separate service or queue with bounded concurrency to contain failure domains.
Development and security engineering lessons
1) Lexers are code with state — test edge cases
Regular-expression-driven lexers are expressive but fragile. Non-consuming lookaheads and nested state transitions can interact in surprising ways. This vulnerability illustrates that syntactic validity does not imply safe parsing — a valid SML token can be a pathological input for a buggy state machine. Tests should include not only valid-language coverage but also minimal, boundary, and malformed inputs intended to exercise state-machine edges.2) Assume untrusted inputs will be malicious
Any time your service renders user content — whether for display or for processing — assume an attacker will explore minimal, high-impact payloads. Small inputs that are easy to generate and transport (single keywords, single-character payloads) are especially attractive to attackers because they are cheap to deliver at scale.3) Add timeouts and resource confinement as first-class defenses
Even with correct code, regular-expression engines and lexers can exhibit worst-case behavior on crafted inputs (e.g., ReDoS). Engineering controls that limit runtime and enforce resource caps on content-processing workers are direct, pragmatic defenses that complement code fixes.4) Keep dependencies small and scan them continuously
Syntax highlighters are often pulled in indirectly through documentation tooling, static site generators, or web frameworks. Use software composition analysis (SCA) in CI and enforce dependency pinning and automated updates so packaged versions do not age silently in production. GitLab, OS vendors, and many SCA tools list CVE-2021-20270 and similar issues for Pygments; integrate those feeds into your pipeline. (advisories.gitlab.com)Supply-chain implications and downstream exposure
Because Pygments is embedded in many projects and distributions, the exposure wasn't limited to standalone Pygments installations. Distributors and downstream products that vendor a copy of Pygments or ship it inside larger appliances retained the flaw until they updated their packages. Advisories from GitLab, Debian, Alpine, and others documented the affected ranges and flagged upgrades or mitigations. This is a classic supply-chain case: a small library bug translated into systemic exposure across many unrelated products. Administrators should treat third-party product advisories as part of their patching priority list and validate that vendor-supplied images have been rebuilt against patched Pygments packages. (advisories.gitlab.com)How to prioritize response in your environment
- Critical: any externally facing application that highlights user-submitted code should be patched first. These endpoints are easiest to probe and abuse.
- High: internal CI/CD and doc-building pipelines that process external pull requests or that run on shared infrastructure — these can be attacked via PRs or contributed content.
- Medium: offline or admin-only documentation renderers and systems isolated from untrusted inputs, which still warrant inventory and patching but are lower operational risk.
Known limitations and open questions
- This vulnerability is an availability-only issue; it does not enable remote code execution or data exfiltration on its own. However, availability failures can have downstream business impacts and can be chained with other tactics in a multi-stage attack.
- The exploit is trivial to craft and therefore practical to run at scale; that combination is why the vulnerability received a high impact score despite being limited to DoS.
- While the upstream fix and packaged updates are straightforward, the persistence of older versions in long-lived containers, appliance images, or vendor stacks means exposure can persist for months in some environments. Administrators must assume latent risk until they confirm upgrades.
Final analysis: risk versus fix complexity
From a remediation standpoint, CVE-2021-20270 is a low-cost, high-value fix: upgrading Pygments to 2.7.4 (or later) resolves the problem with a small code change that the project committed and tested. From an operational standpoint, however, the real-world cost can be higher because the library is embedded across many images and products. The core lessons are operational, not technical: treat content-processing code as an execution-safety surface, enforce resource constraints around it, and keep dependency inventories and patch processes current.For defenders, the path is clear:
- Patch immediately where feasible (Pygments >= 2.7.4).
- Where patching is delayed, enforce mitigations like input filtering, timeouts, and sandboxing.
- Use SCA tooling and CVE feeds in CI to prevent vulnerable versions from slipping back into production.
- Treat syntax-highlighting workflows as potentially hostile and design for graceful degradation.
Checklist for operators (actionable summary)
- Identify all hosts, containers, and applications that include Pygments.
- Verify installed version; if < 2.7.4, mark as vulnerable. (advisories.gitlab.com)
- Patch to Pygments 2.7.4 or later, rebuild artifacts, and redeploy.
- Add per-request CPU/time limits around highlight-rendering calls.
- Run highlighting in an isolated process or sandbox with strict resource caps.
- Temporarily reject or rate-limit SML code highlighting if SML support is not required.
- Integrate SCA/CVE scanning into CI to prevent regressions.
The SML-lexer infinite loop is a compact illustration of how subtle control-flow assumptions in pattern-based parsers can cause outsized operational impact. The vulnerability was fixed upstream with a small code correction and packaged by major distributions; the real risk remains in unpatched deployments and in systems that highlight untrusted code without resource isolation. If your service highlights user code, treat this as a reminder: small libraries can produce large outages, and engineering controls like sandboxing and timeouts are as essential as code fixes in keeping services robust.
Source: MSRC Security Update Guide - Microsoft Security Response Center