Microsoft’s decision to shift the Sentinel/telemetry migration timeline and related monitoring deprecations toward a January 2027 end-of-support window is the most consequential infrastructure calendar call many enterprise ops teams will face this year — and it arrived after a wave of customer feedback that forced Microsoft to extend the runway and clarify migration guidance for hybrid monitoring.
Microsoft announced a deprecation of vendor-maintained System Center Operations Manager (SCOM) management packs for several SQL-related workloads and a strong recommendation to migrate telemetry to Azure Monitor, Azure Arc, and Log Analytics. The deprecation notice set January 2026 as the formal deprecation announcement and January 2027 as the End of Support date for those management packs — effectively giving enterprises a limited window to rearchitect monitoring for SQL Server Reporting Services (SSRS), Power BI Report Server (PBIRS), and SQL Server Analysis Services (SSAS).
That vendor messaging later prompted Microsoft to push the implied migration/deprecation pressure in official guidance, effectively aligning deadlines with a 2027 EoS target while responding to customer concerns about the pace, cost, and complexity of moving on‑prem telemetry to the cloud. The move acknowledges that many larger or regulated organizations needed more time and clearer migration playbooks.
However, the migration model also introduces new operational and security considerations:
The vendor can make migrations easier by:
For Windows operations teams, the imperative is immediate: inventory, pilot, and govern. Use the extra time to validate ingestion profiles, rebuild critical alerts, and engage procurement early. Treat the migration as a program rather than a one‑off project — because it will touch security, finance, compliance, and daily operations. Those who act now will convert a forced migration into an opportunity to modernize observability; those who delay risk a last-minute scramble and a potentially expensive transition as the January 2027 gate approaches.
Source: Windows Report https://windowsreport.com/microsoft...ion-deadline-to-2027-after-customer-feedback/
 Background
Background
Microsoft announced a deprecation of vendor-maintained System Center Operations Manager (SCOM) management packs for several SQL-related workloads and a strong recommendation to migrate telemetry to Azure Monitor, Azure Arc, and Log Analytics. The deprecation notice set January 2026 as the formal deprecation announcement and January 2027 as the End of Support date for those management packs — effectively giving enterprises a limited window to rearchitect monitoring for SQL Server Reporting Services (SSRS), Power BI Report Server (PBIRS), and SQL Server Analysis Services (SSAS).That vendor messaging later prompted Microsoft to push the implied migration/deprecation pressure in official guidance, effectively aligning deadlines with a 2027 EoS target while responding to customer concerns about the pace, cost, and complexity of moving on‑prem telemetry to the cloud. The move acknowledges that many larger or regulated organizations needed more time and clearer migration playbooks.
Why this matters now
For decades, SCOM management packs provided a product-aware, on‑premises monitoring model: discovery, pre-built rule sets, health models, and remediation runbooks baked into a single console. Shifting from this to a cloud-centric telemetry model is not purely technical — it changes procurement, operations budgets, security posture, and compliance workflows. The calendar Microsoft set makes the choice urgent: treat January 2027 as a gate when vendor updates and compatibility promises end for those MPs.What Microsoft actually announced (clarified)
- Deprecation announcement for SCOM management packs covering SSRS, PBIRS, and SSAS: announced January 2026.
- End of Support for those management packs: January 2027 — after which Microsoft will not provide updates, fixes, or security patches for the affected MPs.
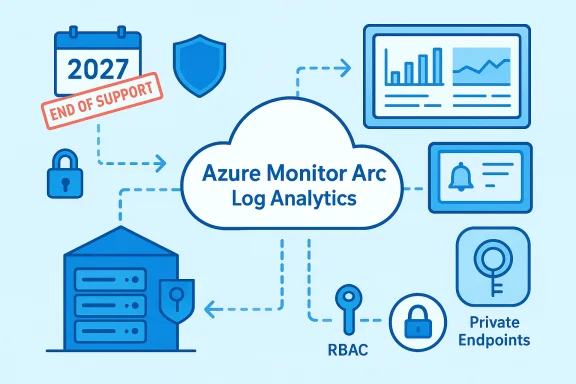
- Recommended migration path: Azure Arc to register on‑prem machines, Azure Monitor Agent (AMA) to collect telemetry, and Log Analytics workspaces for ingestion and alerting. Microsoft positions Azure Monitor + Arc + Log Analytics as the supported hybrid observability stack.
The customer backlash — themes and realities
Customer feedback that prompted Microsoft’s softer, more explicit 2027 runway centered on several concrete points:- Operational effort: Converting mature SCOM runbooks, management pack logic, and product-aware alerts into Data Collection Rules (DCRs), KQL queries, and Azure Monitor alerts is a non‑trivial engineering task for teams with thousands of monitors.
- Skills gap: SCOM skillsets (MP lifecycle, rule authoring) differ from Azure skills (KQL, DCR design, workspace governance). Training and role changes are required.
- Cost shock: Moving from license-based SCOM costs to consumption-based Azure Monitor ingestion introduces financial uncertainty. Customers worried about telemetry volume, retention, and unpredictable bills.
- Compliance and data residency: For regulated or air‑gapped environments, forwarding telemetry to Azure raises legal and policy questions; some environments cannot egress telemetry without bespoke architecture.
- Timing collisions: Many enterprises face parallel migrations (OS upgrades, SQL version changes, cloud projects) that compress available engineering bandwidth. The original push felt like “too many deadlines at once.”
Technical implications for monitoring and security
Moving telemetry to Azure Monitor and centralizing it with Log Analytics has clear technical upsides: richer analytics, better integration with cloud-native security tooling (for example, Defender for Cloud and Microsoft Sentinel), and a single hybrid control plane via Azure Arc. These are strengths Microsoft highlights.However, the migration model also introduces new operational and security considerations:
- Larger attack surface for telemetry: Forwarding event logs, counters, and host metadata to the cloud centralizes sensitive metadata and increases the need for strong identity controls, RBAC, encryption, and network segmentation. Enterprises must treat telemetry as a sensitive asset.
- Telemetry governance becomes critical: Without careful DCR design and retention policies, ingestion costs and noise increase. Telemetry tagging, retention tiers, and pre-ingestion filtering become operational necessities.
- Feature parity is mixed: Some organizations will find Azure Monitor and Workbooks more flexible; others will miss SCOM’s product-aware, management‑pack-driven model for certain on‑prem workflows. Expect gaps that require rework or third‑party bridges.
Cost — the elephant in the room
One of the most frequently reported customer concerns is the shift from predictable license costs to consumption-based pricing. Microsoft’s Log Analytics pricing is governed by ingestion volume, retention duration, and optional commitment tiers. Key cost levers to consider:- Data Collection Rules (DCRs) that reduce noisy counters and send only essential telemetry.
- Commitment tiers for Log Analytics (pre-purchased ingestion) to cap or predict costs.
- Telemetry sampling and aggregation to reduce raw ingestion volumes.
- Procurement conversations with Microsoft or CSP partners for migration credits, commitment discounts, or managed-ingestion offers.
Migration strategies: practical paths and trade-offs
There is no single correct path; the right approach depends on compliance needs, scale, and risk tolerance. Below are pragmatic options with trade-offs.1. Full Azure migration (recommended by Microsoft)
- Arc-enable servers.
- Install Azure Monitor Agent (AMA).
- Define DCRs and send telemetry to Log Analytics.
- Recreate critical alerts as Azure Monitor alerts and build Workbooks for dashboards.
Benefits: centralized analytics, modern tooling, Sentinel integration.
Risks: cost uncertainty, retraining, and potential feature gaps if SCOM’s MPs offered unique capabilities.
2. Hybrid approach (staged)
- Keep SCOM as fallback on certain critical on‑prem systems.
- Pilot Azure Monitor on a representative subset; measure ingestion and build parity for highest-value monitors.
Benefits: phased migration, less operational risk.
Risks: longer dual support, duplicated effort.
3. Third‑party / on‑prem alternatives
- Use vendors like Splunk, Datadog, Dynatrace, or private SIEMs that offer on‑prem collectors or private deployments.
Benefits: some vendors offer mature on‑prem options and may replicate product-aware monitoring.
Risks: licensing differences, integration work, potential long-term vendor lock‑in or complexity.
4. Preserve SCOM in an unsupported state (short-term)
- Continue running existing SCOM MPs beyond EoS.
Benefits: buys time.
Risks: no security updates, no compatibility guarantees with future Windows/SQL, and accumulating technical debt.
A pragmatic migration playbook (90–540 days)
- Inventory & classification (weeks 0–6)
- Catalog SSRS/PBIRS/SSAS instances: OS, SQL version, network zone, compliance posture.
- Classify workloads: migration-eligible, constrained, or blocked.
- Pilot & measurement (90 days)
- Arc-enable a representative set and install AMA.
- Send telemetry to a Log Analytics workspace and measure real ingestion.
- Reimplement top 10–20 SCOM rules as DCRs and Alerts.
- Cost modeling and governance (weeks 6–16)
- Run scenarios (conservative/expected/high volume).
- Explore commitment tiers and procurement options.
- Implement telemetry tagging, retention tiers, and RBAC.
- Rebuild & automation (3–9 months)
- Convert runbooks to Azure Automation or Azure Functions.
- Tune DCRs to send required counters only.
- Rollout & decommission (6–18 months)
- Gradually onboard production servers.
- Maintain SCOM as a fallback for critical systems until parity is validated.
- Long-term governance (ongoing)
- Reassess telemetry needs annually and maintain an “escape hatch” for systems that must remain off-cloud.
Governance, security, and compliance checklist
- Enforce private endpoints and private link where policy requires minimized egress.
- Document telemetry flows, retention, and access control for compliance audits.
- Apply RBAC to Log Analytics workspaces and enforce least‑privilege for telemetry consumers.
- Maintain encryption in transit and at rest; verify key management practices.
- Implement telemetry cost governance: tag sources, set alerts for ingestion spikes, and automate DCR lifecycle.
- Preserve runbooks and incident playbooks during the migration to prevent response regressions.
Real-world constraints: who struggles most?
- Regulated industries (finance, healthcare, government) with strict data residency rules and air‑gapped systems will face the highest friction and require bespoke secure bridging or third‑party solutions.
- Large enterprises with thousands of monitors and complex SCOM MPs will face the steepest engineering lift due to the sheer volume of rules to reimplement.
- Organizations with limited cloud skills may stall unless they invest in training or partner with managed service providers (MSPs) who specialize in telemetry migration.
What Microsoft can do (and what they already did)
Microsoft’s initial approach — deprecate on‑prem MPs and recommend Azure replacements — was a strong strategic nudge. Customer reaction forced the vendor to clarify timelines and provide more explicit guidance, effectively giving organizations until January 2027 to make technical and procurement decisions. The extension is not a reversal of strategy; it’s a pragmatic concession to real-world migration friction.The vendor can make migrations easier by:
- Publishing more granular, workload-specific migration playbooks and conversion templates for common SCOM MPs.
- Offering limited-time migration credits or predictable commitment tiers to ease cost transitions.
- Providing hardened private connectivity patterns for regulated customers.
Practical recommendations for IT leaders (immediate actions)
- Treat January 2027 as a hard planning gate: build your migration calendar and budget around it.
- Launch a production pilot within the next 30–60 days to measure ingestion, test DCRs, and quantify costs.
- Create a cross-functional migration council (security, DBAs, procurement, platform owners) to align priorities and procurement cadence.
- Run telemetry hygiene: identify and remove low-value counters and logs before migration to reduce ingestion.
- Negotiate early with Microsoft account teams, CSPs, or managed partners for pricing and migration assistance.
Known unknowns and unverifiable claims (caution)
- Exact month-by-month cost impacts for any single estate are unverifiable without a production pilot; published price lists cannot predict ingestion behavior in real systems. Any headline cost estimate should be treated as provisional until validated with real telemetry.
- Feature parity claims between SCOM MPs and Azure Monitor are partially subjective. Some teams will find Azure Monitor superior; others will find gaps. These are operationally dependent and must be evaluated with functional parity tests.
The bigger picture: vendor lifecycles and cloud-first strategy
Microsoft’s move is consistent with a longer-term trend: vendors are consolidating development effort on cloud-native services and reducing investment in product-specific on‑prem artifacts. That’s beneficial in terms of innovation velocity and integrated security features, but it also forces enterprises to adjust operational models and to budget for recurring consumption costs rather than one-time licenses. The January 2027 deadline is a tactical milestone in a strategic pivot that was underway for years.Checklist: What to do in the next 90 days (step-by-step)
- Inventory: catalog all SCOM MPs and dependent systems.
- Pilot: Arc-enable a representative set and measure Log Analytics ingestion.
- Reimplement: rebuild the top 10–20 critical alerts as DCRs and validate incident flow.
- Governance: set retention and RBAC policies; tag telemetry sources for cost allocation.
- Procurement: open conversations with Microsoft or partners about commitment tiers, migration credits, or managed ingestion options.
Conclusion
Microsoft’s extension and clarification of the Sentinel/telemetry migration timeline to a January 2027 End of Support — following strong customer feedback — is a practical acknowledgment that large, regulated, and complex estates need more time and clearer playbooks to transition away from SCOM management packs. The move does not eliminate the underlying strategic push toward Azure Monitor, Azure Arc, and Log Analytics; rather, it buys the enterprise community a predictable runway to plan, pilot, and execute a migration that balances capability gains against cost, compliance, and operational risk.For Windows operations teams, the imperative is immediate: inventory, pilot, and govern. Use the extra time to validate ingestion profiles, rebuild critical alerts, and engage procurement early. Treat the migration as a program rather than a one‑off project — because it will touch security, finance, compliance, and daily operations. Those who act now will convert a forced migration into an opportunity to modernize observability; those who delay risk a last-minute scramble and a potentially expensive transition as the January 2027 gate approaches.
Source: Windows Report https://windowsreport.com/microsoft...ion-deadline-to-2027-after-customer-feedback/