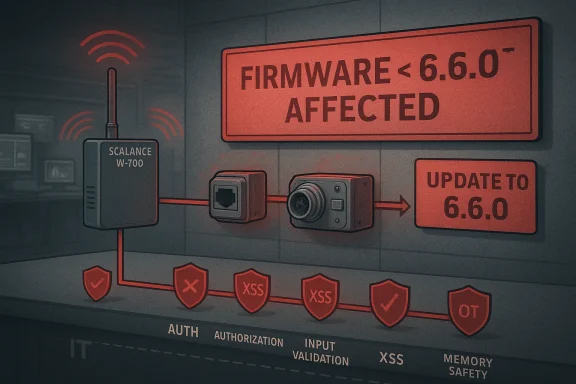
Siemens has issued a significant security advisory for its SCALANCE W-700 IEEE 802.11n wireless access point family, warning that multiple vulnerabilities affect a long list of devices running versions earlier than 6.6.0. The advisory covers models spanning RJ45, M12, SFP, and EEC variants, and the risk profile is broad enough to justify urgent patch planning rather than routine maintenance. CISA’s republication makes clear that Siemens recommends updating to the latest version and that the affected product line is deployed worldwide in sectors including communications, information technology, and critical manufacturing.
Industrial wireless networking gear tends to live in a strange but important place in the stack. It is neither a commodity consumer router nor a deeply specialized PLC, but it can sit directly on the boundary between enterprise IT and operational technology. That makes SCALANCE devices strategically sensitive: they often bridge engineering systems, field networks, and maintenance access paths, so a flaw in the device is rarely isolated to the box itself. Siemens’ advisory for the W-700 family is a reminder that wireless infrastructure in industrial environments is part of the attack surface, not merely a convenience layer.
The current disclosure is notable because it is not about one defect. Instead, it bundles together a series of CVEs stretching across multiple years, including CVE-2020-24588, CVE-2021-3712, CVE-2022-0778, several 2022 issues, and CVE-2023-44373. That pattern suggests an accumulated security debt problem rather than a single coding mistake. In practical terms, when a product family has a long tail of related issues, operators should assume the remediation task is about much more than installing one patch; it is about re-establishing trust in the platform’s maintenance posture.
CISA’s advisory also highlights that Siemens ProductCERT reported the vulnerabilities to the agency, which is typical of coordinated industrial disclosure but still important. It means the vendor and the government body are aligned on the seriousness of the issue, and that the guidance has already crossed from internal vendor response into public operational warning. For industrial defenders, that usually translates into act now, not wait for more context.
There is also a broader historical context here. Industrial networking products increasingly inherit the expectations of modern web services, embedded Linux appliances, and remote management platforms all at once. That creates a layered failure model: authentication logic, web interfaces, crypto handling, memory safety, and input validation can all become part of the same compromise chain. The SCALANCE advisory fits this pattern closely, which is why it matters even if some of the CVEs are older.
In industrial settings, that kind of compromise can have a cascading effect. A modified wireless edge can influence how operators reach machinery, how vendor support systems connect, and how segmentation is enforced. That is why advisories like this should be read as control-plane risk, not merely as device-patch items.
That matters even more here because the advisory touches a product family deployed in critical sectors. A patch that is technically correct but operationally disruptive can still cause problems if it is pushed too aggressively. The right approach is not delay, but validated speed.
The larger lesson is familiar but still important: industrial security is increasingly won or lost at the management layer. When the product that controls connectivity has multiple authentication, authorization, input-validation, and memory-safety problems, the device is no longer just infrastructure; it is part of the threat model. That is why this Siemens advisory should be treated as an urgent operational signal, not simply another firmware notice.
Source: CISA Siemens SCALANCE | CISA
 Background
Background
Industrial wireless networking gear tends to live in a strange but important place in the stack. It is neither a commodity consumer router nor a deeply specialized PLC, but it can sit directly on the boundary between enterprise IT and operational technology. That makes SCALANCE devices strategically sensitive: they often bridge engineering systems, field networks, and maintenance access paths, so a flaw in the device is rarely isolated to the box itself. Siemens’ advisory for the W-700 family is a reminder that wireless infrastructure in industrial environments is part of the attack surface, not merely a convenience layer.The current disclosure is notable because it is not about one defect. Instead, it bundles together a series of CVEs stretching across multiple years, including CVE-2020-24588, CVE-2021-3712, CVE-2022-0778, several 2022 issues, and CVE-2023-44373. That pattern suggests an accumulated security debt problem rather than a single coding mistake. In practical terms, when a product family has a long tail of related issues, operators should assume the remediation task is about much more than installing one patch; it is about re-establishing trust in the platform’s maintenance posture.
CISA’s advisory also highlights that Siemens ProductCERT reported the vulnerabilities to the agency, which is typical of coordinated industrial disclosure but still important. It means the vendor and the government body are aligned on the seriousness of the issue, and that the guidance has already crossed from internal vendor response into public operational warning. For industrial defenders, that usually translates into act now, not wait for more context.
There is also a broader historical context here. Industrial networking products increasingly inherit the expectations of modern web services, embedded Linux appliances, and remote management platforms all at once. That creates a layered failure model: authentication logic, web interfaces, crypto handling, memory safety, and input validation can all become part of the same compromise chain. The SCALANCE advisory fits this pattern closely, which is why it matters even if some of the CVEs are older.
What Siemens Says Is Affected
The affected inventory is broad. Siemens lists many SCALANCE W-700 IEEE 802.11n devices as vulnerable if they run prior to version 6.6.0, including W721-1, W722-1, W734-1, W738-1, W748-1, W761-1, W774-1, W778-1, W786-1, W786-2, and W788-2 families in several hardware and regional variants. That breadth matters because industrial operators often assume one model name equals one update path, when in reality the same family can have multiple sub-SKUs, regional builds, and packaging differences.Version boundaries matter
The key line in the advisory is the version threshold: anything earlier than 6.6.0 is affected. That creates a clean remediation rule, which is useful, but only if organizations can accurately inventory their devices and confirm the installed firmware. In many real environments, the hardest part is not understanding the advisory; it is finding every device that matches it.The product list is not cosmetic
The list includes more than a handful of variants, such as RJ45, M12, SFP, and EEC configurations. That implies the issue reaches into multiple deployment styles, including machine-embedded installations and harsher industrial settings. When a vulnerability affects both standard and ruggedized hardware, it usually means defenders should review both plant-floor units and more conventional network deployments.Operational takeaway
The most important practical point is that a version check alone is not enough if the organization cannot map the device to a real-world role. A radio module in a manufacturing cell may be just as critical as a network appliance in an engineering office. The advisory’s long device matrix is a strong signal that asset inventory, not just patching, is central to the response.- Verify every SCALANCE W-700 unit against the 6.6.0 boundary.
- Treat regional variants as distinct inventory items.
- Do not assume ruggedized hardware is somehow exempt.
- Prioritize units that sit on production or maintenance pathways.
- Document which devices are internet-reachable, VPN-reachable, or internal-only.
The Vulnerability Landscape
CISA describes the issue as a CVSS Vendor Equipment Vulnerabilities v3 9.1 finding, which places the advisory firmly in high-severity territory. The vulnerability classes are varied: missing authentication for critical function, improper authentication, injection, improper validation of integrity check value, improper input validation, out-of-bounds read, infinite loop, missing authorization, allocation of resources without limits or throttling, and basic XSS. That is a crowded and uncomfortable list because it spans identity, memory safety, input handling, and web abuse.Why multiple CWE classes matter
When a single product family has this many failure modes, the issue is rarely one narrow bug. It usually means the product has several weak control points, and attackers only need one reliable path. For defenders, this changes the remediation mindset from find the patch to assume the platform’s trust boundaries were too loose.High severity does not always mean the same thing in OT
A 9.1 rating is high, but industrial severity is not just about the score. What matters is that these devices are often part of maintenance channels, engineering networks, and wireless access paths that are trusted by design. If an attacker can exploit one of the missing-authentication or authorization flaws, they may not need to touch the downstream industrial assets directly.The most concerning classes
Of the listed weaknesses, missing authentication for critical function and missing authorization are especially serious because they often enable direct control over sensitive behavior. Out-of-bounds read and improper input validation are also important because they can reveal memory contents or destabilize the appliance. Meanwhile, basic XSS and injection suggest browser- or web-interface exposure that could be relevant if administrators manage the devices through a web console.- Authentication failures can be more dangerous than crashes.
- Memory-safety bugs can expose secrets or internal state.
- Web-interface flaws can broaden attack paths beyond direct network access.
- Resource exhaustion bugs can turn into denial-of-service events.
- Multiple bug classes usually indicate systemic engineering debt.
Why This Matters for Industrial Networks
Industrial wireless infrastructure is not just another network segment. In many plants and facilities, access points like the SCALANCE W-700 family are part of the trusted backbone that supports monitoring, engineering access, mobile maintenance, and device connectivity. If the access layer is weak, the attacker’s first step can become the most valuable step.The management plane is the real prize
The obvious mental model is to think of a wireless access point as infrastructure for connectivity. The security reality is more subtle: the management plane can become a pivot point. If a flaw lets an attacker bypass authentication or manipulate device behavior, they may be able to alter network access in ways that are hard to notice until something downstream breaks.In industrial settings, that kind of compromise can have a cascading effect. A modified wireless edge can influence how operators reach machinery, how vendor support systems connect, and how segmentation is enforced. That is why advisories like this should be read as control-plane risk, not merely as device-patch items.
Wireless changes the exposure profile
Wireless devices are inherently different from cabled appliances because they expand the set of places from which an attacker might attempt contact. That does not mean every radio becomes remotely exploitable, but it does mean the attack surface includes both local RF environments and adjacent network segments. In other words, the access point is already operating at the boundary where trust assumptions are weaker.- Wireless infrastructure can widen the practical attack surface.
- Management interfaces often matter more than the radio itself.
- Segmentation is only effective if the device honors it correctly.
- Maintenance workflows can become unintended attack paths.
- One compromised access device can affect many downstream endpoints.
Enterprise versus plant-floor impact
For enterprise teams, the issue is often about operational continuity and network hygiene. For plant-floor teams, it is about uptime, determinism, and avoiding disruptions to workflows that depend on stable connectivity. The same flaw can look like a patching headache in one environment and a potential production risk in another. That is why this advisory deserves cross-functional attention from IT, OT, and engineering teams alike.Patch Significance and Siemens’ Guidance
Siemens’ primary recommendation is straightforward: update to the latest version. The fixed release identified in the advisory is 6.6.0, and that gives operators a concrete target. But the simplicity of the instruction should not be mistaken for simplicity of execution. In industrial environments, patching usually means maintenance windows, compatibility checks, and rollback planning.Why “latest” still needs validation
Industrial firmware updates are never just about copying a file onto a device. Teams need to confirm whether the update changes wireless behavior, affects existing client associations, or alters anything in the device’s security configuration. A good rollout process will test the upgrade in a staging or representative environment before mass deployment.That matters even more here because the advisory touches a product family deployed in critical sectors. A patch that is technically correct but operationally disruptive can still cause problems if it is pushed too aggressively. The right approach is not delay, but validated speed.
How to interpret the general recommendations
CISA repeats the standard ICS advice: minimize network exposure, isolate control system networks behind firewalls, and use VPNs carefully when remote access is required. Those recommendations can sound generic, but they become highly relevant when the vulnerable device is a network boundary component. If the access point is reachable from broad internal networks, then even a small flaw can become a larger operational risk.Practical remediation sequence
- Inventory every SCALANCE W-700 device.
- Confirm firmware version and sub-model.
- Identify devices below 6.6.0.
- Test firmware compatibility in a controlled environment.
- Schedule deployment in prioritized waves.
- Verify post-update behavior and configuration integrity.
- Reduce exposure while patching is staged.
- Patch first where devices support business-critical operations.
- Segment devices that cannot be updated immediately.
- Review management access paths before and after deployment.
- Recheck whether any web interfaces are externally exposed.
- Preserve configuration backups before making changes.
Threat Modeling the Advisory
The advisory’s mix of issues creates several plausible attacker goals. One is outright unauthorized access to device functions. Another is denial of service, either by exhausting resources or triggering instability through malformed input. A third is information disclosure, which can help attackers map the device or prepare a follow-on exploit chain.Direct compromise versus support-path abuse
The most obvious concern is direct exploitation over the network. But industrial gear is often also vulnerable through support and maintenance pathways, where admin accounts, remote management services, or browser-based dashboards are used routinely. A flaw that looks “local” in one context may still be reachable in a managed production environment because the management plane is effectively always trusted.Why denial of service matters more in OT
A denial-of-service condition on an access point is not just inconvenient in an industrial context. If wireless connectivity is used for engineering access, sensors, or maintenance tasks, a device outage can create operational interruptions well beyond the immediate device. That is why resource exhaustion and infinite loop conditions should not be waved away as merely theoretical.Web and browser exposure
The inclusion of basic XSS signals that at least some attack surface may involve a web interface or browser-mediated workflow. In practice, that widens the threat model because a successful attack may not require deep protocol knowledge if the device is administered through a web console. That is especially concerning when administrators reuse the same browser and network segment across multiple industrial systems.- Direct compromise can alter device behavior.
- Denial of service can interrupt plant operations.
- Information disclosure can enable follow-on attacks.
- Web weaknesses may expose admin sessions.
- Resource-limits bugs can make devices unstable under pressure.
Operational Priorities for Defenders
For security teams, the immediate job is not to panic, but to sort devices by exposure and criticality. The advisory affects a broad installed base, so the response should be structured and evidence-driven. Start with the devices that are easiest to reach and hardest to replace.What to check first
The first question is whether any W-700 devices are running firmware earlier than 6.6.0. The second is where those devices sit in the network topology. The third is whether they are reachable from business networks, engineering laptops, or remote support channels that expand the attack surface.Why segmentation still matters
Even if the firmware is vulnerable, segmentation can reduce the blast radius. A tightly controlled network boundary can make exploitation harder and limit the downstream consequences if one device is compromised. That is why Siemens’ and CISA’s recommendations overlap so strongly with long-standing ICS defense-in-depth principles.Enterprise and OT coordination
This is a case where network teams and operations teams need to work together. IT may own routing, firewall rules, and remote access controls, while OT may own device maintenance windows and uptime requirements. If those groups do not coordinate, the result is often either delayed patching or an unsafe rushed update.- Identify exposure paths before patching.
- Remove unnecessary management reachability.
- Use controlled maintenance windows.
- Back up configuration data before updates.
- Validate that the device remains operational after remediation.
Industry and Market Implications
This kind of advisory has consequences beyond the affected product line. Siemens is one of the best-known names in industrial infrastructure, and when a major vendor publishes a broad firmware advisory, customers notice. Rivals notice too, because the disclosure reinforces a market-wide reality: industrial networking products are now expected to meet a much higher security bar than they did a decade ago.Competitive pressure on industrial vendors
Vendors compete not only on features and performance, but on patch cadence, disclosure quality, and clarity of remediation. A detailed advisory with a fixed version and a clean vulnerability taxonomy is better than a vague notice, but it still signals security debt. Other vendors will be judged against this standard, especially when customers compare how quickly and cleanly they can remediate high-risk flaws.Customer expectations are rising
Industrial buyers increasingly expect the same transparency they get from enterprise software vendors. They want clear version thresholds, explicit affected-model lists, and actionable mitigation advice. The fact that this advisory includes so many specific model numbers is a plus from an operational standpoint, but it also underscores how much trust modern industrial networks place in device firmware quality.The long tail of embedded security
The presence of CVEs from multiple years highlights an uncomfortable truth: industrial devices often carry a long tail of vulnerabilities that can remain relevant long after initial disclosure. That is partly because firmware update cycles are slower, and partly because devices may stay in service for years. The market reality is that “good enough for shipping” is no longer good enough for critical infrastructure.- Security maturity is becoming a procurement issue.
- Fixed-version clarity matters as much as the vulnerability count.
- Long-lived embedded devices accumulate risk over time.
- Patch transparency influences customer confidence.
- Industrial wireless gear is now judged like any other critical platform.
Strengths and Opportunities
The most positive aspect of this advisory is that Siemens gives defenders a clear, actionable path to closure. The version boundary is specific, the affected product list is explicit, and the remediation recommendation is simple enough to translate into change management quickly. That clarity is valuable in industrial environments where ambiguity is often the biggest obstacle to timely action.- Clear fixed version: 6.6.0 provides a concrete target.
- Detailed affected list: operators can map devices more accurately.
- High-severity signal: the 9.1 score supports urgent prioritization.
- Multiple weakness classes identified: defenders can build broader detection and hardening plans.
- Opportunity for inventory cleanup: teams can reconcile model names, sub-variants, and deployment roles.
- Segmentation improvements: network changes can reduce exposure during and after patching.
- Policy review: this is a good moment to reassess who can administer wireless infrastructure.
Risks and Concerns
The biggest risk is complacency. Because the devices are industrial and the advisory includes a familiar update path, some organizations may assume the issue is straightforward enough to defer. That would be a mistake, because a high-severity flaw in a wireless edge device can affect both reachability and trust in ways that are hard to unwind after the fact.- Patch lag can leave exposed devices in service too long.
- Mixed hardware variants may complicate remediation.
- Wireless exposure can make reachability broader than teams expect.
- Management-plane compromise can cascade into downstream access issues.
- Weak logging can make post-incident analysis difficult.
- Overreliance on perimeter controls can hide the real risk.
- Legacy deployments may resist rapid upgrade cycles.
Looking Ahead
The next thing to watch is how quickly organizations can move from awareness to remediation. In industrial environments, a patch is only useful if it is validated and deployed without destabilizing operations, so the real timeline will depend on maintenance windows, device ownership, and network segmentation maturity. The advisory itself gives defenders a clear target; the question is how fast they can hit it.What to watch next
- Whether Siemens publishes any follow-up technical detail on the individual CVEs.
- How quickly operators move affected devices to 6.6.0.
- Whether any deployment-specific compatibility issues appear during patching.
- Whether organizations use the advisory to tighten management-plane exposure.
- Whether additional industrial advisories show the same pattern of accumulated weaknesses.
The larger lesson is familiar but still important: industrial security is increasingly won or lost at the management layer. When the product that controls connectivity has multiple authentication, authorization, input-validation, and memory-safety problems, the device is no longer just infrastructure; it is part of the threat model. That is why this Siemens advisory should be treated as an urgent operational signal, not simply another firmware notice.
Source: CISA Siemens SCALANCE | CISA