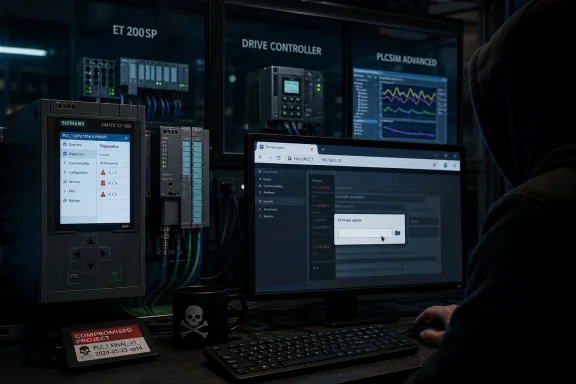
Siemens and CISA warned on May 12 and May 14, 2026, respectively, that the web server in a broad set of SIMATIC S7 PLCs contains three cross-site scripting vulnerabilities affecting S7-1500, ET 200SP, Drive Controller, Software Controller, SIPLUS, and PLCSIM Advanced products. The flaw class is familiar, but the setting is not: this is JavaScript injection in the administrative web surface of industrial controllers. Siemens has issued firmware fixes for some product lines, is preparing more, and says some affected products have no current or planned fix. For operators, the uncomfortable lesson is that the humble embedded web page has become part of the control-system attack surface, not a convenience bolted onto the side.
Cross-site scripting is the kind of vulnerability enterprise security teams have been triaging for decades. On a public website, it can mean stolen cookies, fake forms, or malicious actions performed in a user’s browser session. On a PLC web server, the same basic bug lands in a very different environment: the browser belongs to an engineer, technician, integrator, or administrator who may be authenticated to equipment that drives pumps, production lines, conveyors, packaging systems, or safety-adjacent operations.
That is why this Siemens advisory deserves more attention than the words “web server XSS” might normally receive. The affected products are not obscure one-off appliances. The list spans a large slice of the SIMATIC S7-1500 ecosystem, ET 200SP CPUs, SIPLUS ruggedized variants, Drive Controllers, software controllers, and even SIMATIC S7-PLCSIM Advanced, the simulation tool often used in engineering and testing workflows.
The vulnerabilities are tracked as CVE-2026-25786, CVE-2026-25787, and CVE-2026-25789. Two carry a CVSS 3.1 base score of 9.1, marked critical by the vendor scoring, while the firmware-file-name issue is scored 7.1, high severity. Those scores will raise eyebrows because the first two require a privileged attacker who can download a TIA Portal project to the device, but the scoring reflects what can happen once malicious script runs inside another authenticated web session.
The result is not a Hollywood-style remote takeover of a PLC from the open internet with a single packet. It is more subtle and more realistic: abuse of engineering workflows, authenticated sessions, browser trust, and human handoffs. In industrial environments, subtle is often more dangerous than spectacular because it maps onto how plants actually operate.
The second, CVE-2026-25787, follows the same pattern but in a different place. Here, the vulnerable input is a Technology Object name rendered on the Motion Control Diagnostics page. That matters because motion-control diagnostics are not decorative pages; they are part of the operational and troubleshooting fabric around machines whose behavior may be time-sensitive, expensive, or physically consequential.
The third, CVE-2026-25789, shifts from project metadata to the firmware update page. Siemens says affected devices fail to properly validate and sanitize filenames displayed there. In that scenario, a remote attacker could social-engineer a user into selecting a modified firmware file, triggering malicious JavaScript in the authenticated session without the file even needing to be uploaded.
These three routes tell the same larger story. The vulnerable surface is not a single “forgotten” field buried in an old CGI script. It is input that moves through engineering, diagnostics, and maintenance workflows — exactly the places where industrial security depends on trust boundaries being explicit and boring.
The phrase cross-site scripting can mislead non-web specialists because it sounds like a website problem. In this advisory, it is better understood as an input-validation failure that lets an attacker smuggle browser-executable code into pages served by the controller itself. The PLC becomes the host of the attacker’s script, and the authenticated user’s browser becomes the execution environment.
But “requires privileged access” is not the same as “does not matter.” Industrial networks routinely involve vendors, machine builders, maintenance contractors, remote support sessions, shared engineering stations, offline project files, and change windows where normal separation can blur. A malicious or compromised account with project-download capability can turn an engineering artifact into a trap for the next person who opens the relevant web page.
The social-engineering angle in CVE-2026-25789 is also worth taking seriously. Firmware updates already sit at the uncomfortable intersection of trust, urgency, and procedural complexity. If a user only needs to select a booby-trapped filename for script execution to occur, the attack path starts to look less like pure exploitation and more like a phishing campaign aimed at OT staff.
This is where the CVSS debate becomes less useful than the operational question. A plant manager does not care whether the bug is “really” a 9.1 if exploitation would require a sequence of compromised credentials, unsafe workflows, and an engineer browsing to a specific page. The plant manager cares whether those conditions could exist during a maintenance window at 2 a.m. The honest answer in many environments is yes.
Some entries are affected in all versions. Others are affected below specific firmware lines, notably versions earlier than 2.9.9 or 3.1.6 depending on product family. Siemens has released updates for several affected products and points operators toward current firmware packages, but the remediation picture is uneven: some products have fixes, some are awaiting fixes, some have no current fix, and some have no fix planned.
That unevenness is normal in industrial automation, but it is precisely what makes industrial patching so different from patching a fleet of laptops. A Windows administrator can often push a browser or OS update to thousands of endpoints with phased rings, rollback telemetry, and central compliance reporting. A controls engineer may have to validate a PLC firmware change against a running machine, a safety case, a vendor warranty, a validated recipe, and a production schedule.
The advisory therefore should not be read as a simple “update now” bulletin, even though updating is the right endpoint where supported. It is a map of technical debt embedded in automation fleets. Some devices can be brought to fixed firmware. Others will require compensating controls, narrower access, stricter project governance, and a realistic acceptance that old hardware sometimes remains exposed to new classes of software weakness.
The presence of PLCSIM Advanced in the affected list is also notable. Simulation environments are often treated as less sensitive because they do not directly drive physical outputs. But they sit upstream in the engineering lifecycle, where templates, project files, names, and conventions migrate toward real systems. A poisoned engineering workflow can become a production problem later.
That shift creates a familiar IT security problem in an unfamiliar body. Every dynamic page must safely handle every string it displays. Every place where project data, filenames, object names, or station labels appear becomes an output-encoding problem. The fact that the application is embedded in a PLC does not exempt it from the rules that browser security has enforced elsewhere for a generation.
The danger is not merely that a script could show an alert box or deface a page. In the context of an authenticated session, malicious JavaScript may be able to read page content, interact with forms, send requests as the user, capture session material depending on cookie and browser protections, or trick the user into approving an action. Siemens’ advisory specifically flags risks such as session hijacking or credential theft for the firmware filename scenario.
The web server also creates a bridge between human workflows and device trust. Engineers tend to trust a controller’s own interface more than an arbitrary email attachment. If the malicious content is rendered from the PLC itself, the browser’s address bar may show an expected internal device name or IP address. That is why stored or reflected web-interface bugs in management planes can have outsize impact: they borrow legitimacy from the device.
For WindowsForum readers, the Windows connection is not cosmetic. TIA Portal engineering stations, browser sessions, VPN clients, remote-support tools, and credential stores often live on Windows endpoints. The PLC may be the vulnerable device, but the practical blast radius includes the workstation habits and identity controls of the people who administer it.
The first operational task is inventory. Not a spreadsheet that says “Siemens PLCs,” but a list that captures exact order numbers, firmware versions, hardware generations, SIPLUS variants, software-controller versions, and whether the web server is enabled. The advisory’s long list of order numbers is tedious, but tedious is the price of precision in OT security.
The second task is mapping the role of the web server. If the web interface is enabled only because it was useful during commissioning and nobody turned it off, the risk decision is straightforward. If operators or maintenance teams depend on it for diagnostics, firmware maintenance, or motion-control visibility, disabling it may not be practical, and compensating controls become more important.
The third task is testing. Firmware updates in industrial systems can affect compatibility with engineering projects, communication modules, safety configurations, HMI interactions, and vendor-supported machine states. A rushed patch can create downtime just as surely as an exploit can, which is why industrial cybersecurity has to live inside change management rather than shout at it from across the room.
This is also where IT and OT teams often talk past each other. IT sees a critical CVSS score and expects a patch clock. OT sees a production line, a planned shutdown window, and the possibility that a firmware update may require vendor involvement. The right answer is not to ignore the CVSS score, but to translate it into a prioritized maintenance plan that recognizes both cyber risk and process risk.
Project download rights should be treated like privileged production access, not like a convenience granted to every engineering laptop in the room. If an account can push a TIA project to a controller, it can now also be part of a stored web-interface attack chain on vulnerable devices. That privilege deserves named accounts, role separation, logging, and periodic review.
Firmware update rights deserve the same treatment. The filename-based vulnerability is especially awkward because it weaponizes an action that looks like preparation rather than execution. The advisory says malicious script can run without the file being uploaded, which means even “just browsing to select the file” can be enough in the wrong context.
Network controls remain essential but insufficient. CISA repeats the standard ICS guidance: minimize network exposure, keep control systems off the internet, segment control networks from business networks, place systems behind firewalls, and use secure remote access where required. Those controls reduce reachability, but they do not eliminate risks created by compromised internal accounts, shared jump hosts, remote vendors, or engineering workstations that move between trust zones.
The stronger posture is layered. Keep PLC web servers off untrusted networks. Limit who can authenticate. Limit who can download projects. Limit who can update firmware. Control which workstations can reach the web interface. Treat project files and firmware packages as sensitive inputs, not harmless files.
CISA also adds its usual but important caution: organizations should perform impact analysis and risk assessment before deploying defensive measures. In IT, that sentence can sound like a legal footnote. In OT, it is the difference between a controlled mitigation and an accidental outage.
The advisory conversion disclaimer is equally revealing. CISA states that the ICS advisory is a verbatim republication of Siemens’ CSAF advisory, provided as-is to increase visibility. That means asset owners should not assume CISA has independently normalized every product nuance or remediation state. The authoritative technical detail remains Siemens’ ProductCERT material, while CISA supplies the wider national-risk megaphone.
That division of labor is becoming more common as vulnerability disclosure scales. Vendors publish machine-readable advisories, government agencies amplify and standardize them, and operators are left with the hard work of converting dense product matrices into plant-specific action. The better that pipeline gets, the more obvious the remaining bottleneck becomes: asset owners still need reliable inventories and maintenance authority.
For many organizations, this Siemens bulletin will be less a surprise than a diagnostic. If your team can quickly answer which affected order numbers exist in your plants, which firmware versions they run, which web servers are enabled, which accounts can download projects, and which users hold firmware update rights, the advisory is manageable. If not, the vulnerability is only one part of the problem.
The answer is that the attacker with high privileges is not necessarily the victim whose session gets compromised. In stored XSS, the malicious input is planted in one step and triggered later in another. A compromised engineer, malicious contractor, or abused project-download workflow can set the trap; a different authenticated user with broader or different rights can spring it.
That is why scope changes in the CVSS vector matter. The vulnerable component is the web server’s rendering of input, but the impact can extend into the browser session and the privileges of the person viewing the page. Industrial web UIs are often used by people with consequential access, which makes session context more valuable than the apparent simplicity of the bug suggests.
Still, it would be wrong to overstate the advisory as an immediate unauthenticated remote compromise of PLC logic. Siemens’ own descriptions include meaningful prerequisites. The right interpretation is narrower and more useful: the vulnerabilities create dangerous post-authentication and social-engineering paths in environments where the affected web server is reachable and privileged engineering or maintenance workflows are not tightly controlled.
That distinction matters for defenders because it points to the right mitigations. Internet exposure reduction is table stakes, but it will not stop a malicious project name introduced by a compromised engineering account. Browser hardening helps, but it will not fix unsafe server-side output handling. Firmware updates fix the underlying bug where available, but access discipline remains necessary because future bugs will follow the same workflow seams.
If a TIA Portal workstation is domain-joined, patched through enterprise tooling, backed up by IT, or reachable through a Windows jump server, then this advisory crosses the IT/OT boundary. The vulnerable component may be a PLC web server, but the attacker’s practical path may involve phishing a Windows user, stealing a Windows credential, tampering with a project file on a Windows share, or luring an engineer through a browser session.
The most useful contribution from IT is not to barge into the control room with a patch mandate. It is to help OT teams reduce the surrounding attack surface. That means privileged access management, remote-access hygiene, workstation isolation, browser policy, credential protection, logging, and change-control evidence that is usable during an incident.
Windows Defender Application Control, application allow-listing, hardened jump hosts, separate administrative accounts, and carefully scoped remote access all become relevant even when the CVE lives inside Siemens firmware. So does the mundane work of keeping VPN appliances, browsers, and engineering laptops current. Attack chains do not respect organizational charts.
The advisory is also a reminder that OT web interfaces should not be casually reachable from general corporate networks. If any user on the business LAN can browse to a PLC web server, segmentation has already failed in spirit even if a firewall diagram says otherwise. Access should be brokered, logged, and limited to roles that actually need it.
Good asset inventory in this context is not just device discovery. Passive network tools can help, but they may not capture everything needed for a firmware decision. Operators need the engineering context: project ownership, machine criticality, maintenance windows, vendor dependencies, safety certifications, web server status, user roles, and whether a firmware upgrade has already been qualified for that installation.
That inventory should also include the human side. Who is authorized to download TIA projects? Who can perform firmware updates? Which contractor accounts exist? Which shared accounts are still in use because “the machine builder set it up that way”? These questions are uncomfortable because they expose operational shortcuts, but the Siemens advisory turns those shortcuts into exploit conditions.
A mature response would rank affected devices not only by CVSS but by exposure and workflow. A vulnerable controller with its web server disabled and no routine browser access sits in a different risk category than a vulnerable controller whose web interface is used weekly by multiple technicians through a shared jump host. The same CVE can represent very different operational risk.
This is the part of OT security that rarely fits into a dashboard. The organization needs enough technical inventory to know which firmware applies, enough process knowledge to know when it can be installed, and enough security governance to reduce risk while waiting. Without all three, advisories become unread PDFs in a compliance folder.
Siemens’ latest SIMATIC S7 web server advisory is not a reason to panic, but it is a reason to retire the idea that PLC security is only about ladder logic, protocol filtering, and physical cabinets. The control system now includes the web page, the browser, the Windows engineering station, the project file, the firmware filename, and the user who clicks through a maintenance task under time pressure. The operators who will fare best are the ones who treat those pieces as one system before the next advisory forces them to.
Source: CISA Siemens SIMATIC S7 PLC Web Server | CISA
 The Browser Has Entered the Control Room
The Browser Has Entered the Control Room
Cross-site scripting is the kind of vulnerability enterprise security teams have been triaging for decades. On a public website, it can mean stolen cookies, fake forms, or malicious actions performed in a user’s browser session. On a PLC web server, the same basic bug lands in a very different environment: the browser belongs to an engineer, technician, integrator, or administrator who may be authenticated to equipment that drives pumps, production lines, conveyors, packaging systems, or safety-adjacent operations.That is why this Siemens advisory deserves more attention than the words “web server XSS” might normally receive. The affected products are not obscure one-off appliances. The list spans a large slice of the SIMATIC S7-1500 ecosystem, ET 200SP CPUs, SIPLUS ruggedized variants, Drive Controllers, software controllers, and even SIMATIC S7-PLCSIM Advanced, the simulation tool often used in engineering and testing workflows.
The vulnerabilities are tracked as CVE-2026-25786, CVE-2026-25787, and CVE-2026-25789. Two carry a CVSS 3.1 base score of 9.1, marked critical by the vendor scoring, while the firmware-file-name issue is scored 7.1, high severity. Those scores will raise eyebrows because the first two require a privileged attacker who can download a TIA Portal project to the device, but the scoring reflects what can happen once malicious script runs inside another authenticated web session.
The result is not a Hollywood-style remote takeover of a PLC from the open internet with a single packet. It is more subtle and more realistic: abuse of engineering workflows, authenticated sessions, browser trust, and human handoffs. In industrial environments, subtle is often more dangerous than spectacular because it maps onto how plants actually operate.
Siemens’ Advisory Is Really Three Stories, Not One
The first vulnerability, CVE-2026-25786, concerns the PLC or station name as rendered on the web interface’s communication parameters page. A user authorized to download a TIA project can reportedly inject malicious script by manipulating that name. When a legitimate user with appropriate rights later views the affected page, the script executes in that user’s web session.The second, CVE-2026-25787, follows the same pattern but in a different place. Here, the vulnerable input is a Technology Object name rendered on the Motion Control Diagnostics page. That matters because motion-control diagnostics are not decorative pages; they are part of the operational and troubleshooting fabric around machines whose behavior may be time-sensitive, expensive, or physically consequential.
The third, CVE-2026-25789, shifts from project metadata to the firmware update page. Siemens says affected devices fail to properly validate and sanitize filenames displayed there. In that scenario, a remote attacker could social-engineer a user into selecting a modified firmware file, triggering malicious JavaScript in the authenticated session without the file even needing to be uploaded.
These three routes tell the same larger story. The vulnerable surface is not a single “forgotten” field buried in an old CGI script. It is input that moves through engineering, diagnostics, and maintenance workflows — exactly the places where industrial security depends on trust boundaries being explicit and boring.
The phrase cross-site scripting can mislead non-web specialists because it sounds like a website problem. In this advisory, it is better understood as an input-validation failure that lets an attacker smuggle browser-executable code into pages served by the controller itself. The PLC becomes the host of the attacker’s script, and the authenticated user’s browser becomes the execution environment.
The Prerequisites Lower the Noise but Not the Risk
The first two CVEs require an attacker who is authenticated and authorized to download a TIA project into the affected product. That is not nothing. In a well-run industrial environment, TIA Portal project download rights should be limited, audited, and unavailable from ordinary corporate workstations.But “requires privileged access” is not the same as “does not matter.” Industrial networks routinely involve vendors, machine builders, maintenance contractors, remote support sessions, shared engineering stations, offline project files, and change windows where normal separation can blur. A malicious or compromised account with project-download capability can turn an engineering artifact into a trap for the next person who opens the relevant web page.
The social-engineering angle in CVE-2026-25789 is also worth taking seriously. Firmware updates already sit at the uncomfortable intersection of trust, urgency, and procedural complexity. If a user only needs to select a booby-trapped filename for script execution to occur, the attack path starts to look less like pure exploitation and more like a phishing campaign aimed at OT staff.
This is where the CVSS debate becomes less useful than the operational question. A plant manager does not care whether the bug is “really” a 9.1 if exploitation would require a sequence of compromised credentials, unsafe workflows, and an engineer browsing to a specific page. The plant manager cares whether those conditions could exist during a maintenance window at 2 a.m. The honest answer in many environments is yes.
The Affected-Product List Is the Message
The advisory’s product list is enormous, and that is itself the point. It includes SIMATIC S7-1500 CPUs from lower-end 1511 models through 1518 variants, failsafe “F” models, technology “T” and “TF” models, ET 200SP CPUs, ET 200pro-related models, Drive Controllers, Open Controllers, Software Controllers, Linux Software Controller variants, SIPLUS industrialized versions, and S7-PLCSIM Advanced.Some entries are affected in all versions. Others are affected below specific firmware lines, notably versions earlier than 2.9.9 or 3.1.6 depending on product family. Siemens has released updates for several affected products and points operators toward current firmware packages, but the remediation picture is uneven: some products have fixes, some are awaiting fixes, some have no current fix, and some have no fix planned.
That unevenness is normal in industrial automation, but it is precisely what makes industrial patching so different from patching a fleet of laptops. A Windows administrator can often push a browser or OS update to thousands of endpoints with phased rings, rollback telemetry, and central compliance reporting. A controls engineer may have to validate a PLC firmware change against a running machine, a safety case, a vendor warranty, a validated recipe, and a production schedule.
The advisory therefore should not be read as a simple “update now” bulletin, even though updating is the right endpoint where supported. It is a map of technical debt embedded in automation fleets. Some devices can be brought to fixed firmware. Others will require compensating controls, narrower access, stricter project governance, and a realistic acceptance that old hardware sometimes remains exposed to new classes of software weakness.
The presence of PLCSIM Advanced in the affected list is also notable. Simulation environments are often treated as less sensitive because they do not directly drive physical outputs. But they sit upstream in the engineering lifecycle, where templates, project files, names, and conventions migrate toward real systems. A poisoned engineering workflow can become a production problem later.
Industrial Web Servers Are No Longer Read-Only Wallpaper
For years, many embedded web servers in industrial devices were treated as secondary interfaces: status pages, diagnostics, a quick way to confirm a setting without launching a full engineering suite. That mental model is increasingly obsolete. Web servers now sit beside APIs, user-management features, diagnostic panels, firmware update workflows, and sometimes write-capable operations.That shift creates a familiar IT security problem in an unfamiliar body. Every dynamic page must safely handle every string it displays. Every place where project data, filenames, object names, or station labels appear becomes an output-encoding problem. The fact that the application is embedded in a PLC does not exempt it from the rules that browser security has enforced elsewhere for a generation.
The danger is not merely that a script could show an alert box or deface a page. In the context of an authenticated session, malicious JavaScript may be able to read page content, interact with forms, send requests as the user, capture session material depending on cookie and browser protections, or trick the user into approving an action. Siemens’ advisory specifically flags risks such as session hijacking or credential theft for the firmware filename scenario.
The web server also creates a bridge between human workflows and device trust. Engineers tend to trust a controller’s own interface more than an arbitrary email attachment. If the malicious content is rendered from the PLC itself, the browser’s address bar may show an expected internal device name or IP address. That is why stored or reflected web-interface bugs in management planes can have outsize impact: they borrow legitimacy from the device.
For WindowsForum readers, the Windows connection is not cosmetic. TIA Portal engineering stations, browser sessions, VPN clients, remote-support tools, and credential stores often live on Windows endpoints. The PLC may be the vulnerable device, but the practical blast radius includes the workstation habits and identity controls of the people who administer it.
Patching a PLC Is a Maintenance Project, Not a Click
Siemens’ clearest remediation is to update affected products to fixed firmware where available. For many S7-1500 and ET 200SP products, the advisory points to version 2.9.9 or later. For other families, including certain higher-end S7-1500 and Drive Controller lines, it points to version 3.1.6 or later. That version split matters because asset owners cannot responsibly treat “S7-1500” as a single patch target.The first operational task is inventory. Not a spreadsheet that says “Siemens PLCs,” but a list that captures exact order numbers, firmware versions, hardware generations, SIPLUS variants, software-controller versions, and whether the web server is enabled. The advisory’s long list of order numbers is tedious, but tedious is the price of precision in OT security.
The second task is mapping the role of the web server. If the web interface is enabled only because it was useful during commissioning and nobody turned it off, the risk decision is straightforward. If operators or maintenance teams depend on it for diagnostics, firmware maintenance, or motion-control visibility, disabling it may not be practical, and compensating controls become more important.
The third task is testing. Firmware updates in industrial systems can affect compatibility with engineering projects, communication modules, safety configurations, HMI interactions, and vendor-supported machine states. A rushed patch can create downtime just as surely as an exploit can, which is why industrial cybersecurity has to live inside change management rather than shout at it from across the room.
This is also where IT and OT teams often talk past each other. IT sees a critical CVSS score and expects a patch clock. OT sees a production line, a planned shutdown window, and the possibility that a firmware update may require vendor involvement. The right answer is not to ignore the CVSS score, but to translate it into a prioritized maintenance plan that recognizes both cyber risk and process risk.
The Temporary Fix Is Really Access Discipline
Where fixed firmware is not available, Siemens recommends restricting who can download TIA projects and who can use firmware update rights. Those recommendations may sound obvious, but they are more than boilerplate. The exploit paths described in the advisory depend heavily on who is allowed to introduce or select untrusted project and firmware-related content.Project download rights should be treated like privileged production access, not like a convenience granted to every engineering laptop in the room. If an account can push a TIA project to a controller, it can now also be part of a stored web-interface attack chain on vulnerable devices. That privilege deserves named accounts, role separation, logging, and periodic review.
Firmware update rights deserve the same treatment. The filename-based vulnerability is especially awkward because it weaponizes an action that looks like preparation rather than execution. The advisory says malicious script can run without the file being uploaded, which means even “just browsing to select the file” can be enough in the wrong context.
Network controls remain essential but insufficient. CISA repeats the standard ICS guidance: minimize network exposure, keep control systems off the internet, segment control networks from business networks, place systems behind firewalls, and use secure remote access where required. Those controls reduce reachability, but they do not eliminate risks created by compromised internal accounts, shared jump hosts, remote vendors, or engineering workstations that move between trust zones.
The stronger posture is layered. Keep PLC web servers off untrusted networks. Limit who can authenticate. Limit who can download projects. Limit who can update firmware. Control which workstations can reach the web interface. Treat project files and firmware packages as sensitive inputs, not harmless files.
CISA’s Republication Turns a Vendor Notice Into an Operator Test
CISA’s May 14 republication of Siemens ProductCERT advisory SSA-688146 is not merely a mirror. It puts the issue into the American critical-infrastructure context, calling out sectors including Chemical, Energy, Food and Agriculture, and Water and Wastewater, with worldwide deployment. That framing matters because SIMATIC systems are deeply embedded in the mixed public-private machinery that keeps industrial services running.CISA also adds its usual but important caution: organizations should perform impact analysis and risk assessment before deploying defensive measures. In IT, that sentence can sound like a legal footnote. In OT, it is the difference between a controlled mitigation and an accidental outage.
The advisory conversion disclaimer is equally revealing. CISA states that the ICS advisory is a verbatim republication of Siemens’ CSAF advisory, provided as-is to increase visibility. That means asset owners should not assume CISA has independently normalized every product nuance or remediation state. The authoritative technical detail remains Siemens’ ProductCERT material, while CISA supplies the wider national-risk megaphone.
That division of labor is becoming more common as vulnerability disclosure scales. Vendors publish machine-readable advisories, government agencies amplify and standardize them, and operators are left with the hard work of converting dense product matrices into plant-specific action. The better that pipeline gets, the more obvious the remaining bottleneck becomes: asset owners still need reliable inventories and maintenance authority.
For many organizations, this Siemens bulletin will be less a surprise than a diagnostic. If your team can quickly answer which affected order numbers exist in your plants, which firmware versions they run, which web servers are enabled, which accounts can download projects, and which users hold firmware update rights, the advisory is manageable. If not, the vulnerability is only one part of the problem.
The Severity Score Hides a Human Workflow Attack
The two critical CVEs use a vector that includes network attack vector, low complexity, high privileges required, no user interaction, changed scope, and high impact to confidentiality, integrity, and availability. That combination can feel contradictory at first glance. How can something require high privileges but still be critical?The answer is that the attacker with high privileges is not necessarily the victim whose session gets compromised. In stored XSS, the malicious input is planted in one step and triggered later in another. A compromised engineer, malicious contractor, or abused project-download workflow can set the trap; a different authenticated user with broader or different rights can spring it.
That is why scope changes in the CVSS vector matter. The vulnerable component is the web server’s rendering of input, but the impact can extend into the browser session and the privileges of the person viewing the page. Industrial web UIs are often used by people with consequential access, which makes session context more valuable than the apparent simplicity of the bug suggests.
Still, it would be wrong to overstate the advisory as an immediate unauthenticated remote compromise of PLC logic. Siemens’ own descriptions include meaningful prerequisites. The right interpretation is narrower and more useful: the vulnerabilities create dangerous post-authentication and social-engineering paths in environments where the affected web server is reachable and privileged engineering or maintenance workflows are not tightly controlled.
That distinction matters for defenders because it points to the right mitigations. Internet exposure reduction is table stakes, but it will not stop a malicious project name introduced by a compromised engineering account. Browser hardening helps, but it will not fix unsafe server-side output handling. Firmware updates fix the underlying bug where available, but access discipline remains necessary because future bugs will follow the same workflow seams.
Windows Admins Should Care Even If They Never Touch Ladder Logic
A Windows administrator may look at a Siemens PLC advisory and assume it belongs to someone else. In many organizations, that assumption is how OT incidents begin. The Windows estate often supplies the engineering workstation, the domain accounts, the VPN, the remote desktop gateway, the browser, the endpoint detection agent, and the file shares where project and firmware packages live.If a TIA Portal workstation is domain-joined, patched through enterprise tooling, backed up by IT, or reachable through a Windows jump server, then this advisory crosses the IT/OT boundary. The vulnerable component may be a PLC web server, but the attacker’s practical path may involve phishing a Windows user, stealing a Windows credential, tampering with a project file on a Windows share, or luring an engineer through a browser session.
The most useful contribution from IT is not to barge into the control room with a patch mandate. It is to help OT teams reduce the surrounding attack surface. That means privileged access management, remote-access hygiene, workstation isolation, browser policy, credential protection, logging, and change-control evidence that is usable during an incident.
Windows Defender Application Control, application allow-listing, hardened jump hosts, separate administrative accounts, and carefully scoped remote access all become relevant even when the CVE lives inside Siemens firmware. So does the mundane work of keeping VPN appliances, browsers, and engineering laptops current. Attack chains do not respect organizational charts.
The advisory is also a reminder that OT web interfaces should not be casually reachable from general corporate networks. If any user on the business LAN can browse to a PLC web server, segmentation has already failed in spirit even if a firewall diagram says otherwise. Access should be brokered, logged, and limited to roles that actually need it.
The Real Fix Is an Inventory That Can Survive a Crisis
Every industrial advisory eventually collides with the same question: do you know what you have? Siemens’ affected list is too detailed for guesswork. The difference between an all-versions-affected product and a product fixed in 2.9.9 or 3.1.6 may depend on an order number suffix and a firmware branch.Good asset inventory in this context is not just device discovery. Passive network tools can help, but they may not capture everything needed for a firmware decision. Operators need the engineering context: project ownership, machine criticality, maintenance windows, vendor dependencies, safety certifications, web server status, user roles, and whether a firmware upgrade has already been qualified for that installation.
That inventory should also include the human side. Who is authorized to download TIA projects? Who can perform firmware updates? Which contractor accounts exist? Which shared accounts are still in use because “the machine builder set it up that way”? These questions are uncomfortable because they expose operational shortcuts, but the Siemens advisory turns those shortcuts into exploit conditions.
A mature response would rank affected devices not only by CVSS but by exposure and workflow. A vulnerable controller with its web server disabled and no routine browser access sits in a different risk category than a vulnerable controller whose web interface is used weekly by multiple technicians through a shared jump host. The same CVE can represent very different operational risk.
This is the part of OT security that rarely fits into a dashboard. The organization needs enough technical inventory to know which firmware applies, enough process knowledge to know when it can be installed, and enough security governance to reduce risk while waiting. Without all three, advisories become unread PDFs in a compliance folder.
The Siemens Web Server Bug Leaves Operators With a Short Checklist and a Long Memory
The practical response is not mysterious, but it does demand coordination across controls engineering, IT security, operations, and vendors. Treat the advisory as a workflow-security issue first and a firmware issue second, because many sites will spend more time managing access and exposure than installing patches.- Verify whether any affected SIMATIC S7-1500, ET 200SP, Drive Controller, Software Controller, SIPLUS, Open Controller, or PLCSIM Advanced products exist in the environment.
- Record exact order numbers, hardware variants, firmware versions, and web server status before deciding whether version 2.9.9, version 3.1.6, or no available fix applies.
- Update to Siemens’ fixed firmware where available, but test changes through normal OT validation and maintenance procedures before touching production equipment.
- Restrict TIA Portal project-download rights to trusted, named personnel and treat those rights as privileged production access.
- Restrict firmware update permissions to instructed personnel and control the source, naming, storage, and handling of firmware files.
- Reduce web-interface exposure through segmentation, firewall rules, jump-host controls, VPN hygiene, and removal of unnecessary browser access from business networks.
Siemens’ latest SIMATIC S7 web server advisory is not a reason to panic, but it is a reason to retire the idea that PLC security is only about ladder logic, protocol filtering, and physical cabinets. The control system now includes the web page, the browser, the Windows engineering station, the project file, the firmware filename, and the user who clicks through a maintenance task under time pressure. The operators who will fare best are the ones who treat those pieces as one system before the next advisory forces them to.
Source: CISA Siemens SIMATIC S7 PLC Web Server | CISA