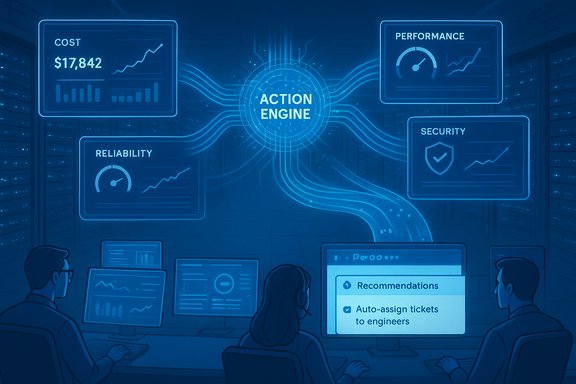
Auckland‑based Spotto has moved its AI‑driven cloud optimisation platform out of beta and into general availability, pitching an Azure‑first tool designed to convert scattered cloud signals into engineer‑ready, billable work for managed service providers (MSPs) and large enterprise IT teams. The commercial release promises continuous tenant scanning, a prioritized “Action Engine” that converts findings into PSA tickets, and proprietary AI models that the company says produce a significant share of optimisation suggestions beyond what Azure’s native tooling surfaces.
Spotto was founded by a team with operational Azure experience — Shaun Webber, Symon Thurlow and Jay Strydom — and explicitly targets the intersection of FinOps, CloudOps and MSP go‑to‑market motions. The founders’ history running and selling Azure‑centric managed services shaped a product ethos focused on turning optimisation into recurring professional services rather than a one‑off savings report. The product has been in active beta with MSPs, SaaS firms and enterprise customers and now enters general availability with functionality that includes multi‑daily scans of connected Azure tenants, consolidated dashboards for cost, security, performance and reliability signals, and integrations into PSA/issue‑tracking systems such as Jira, ConnectWise and Halo. Spotto’s public messaging frames the platform as a way to lower the skill threshold for routine cloud remediation while creating a pipeline of small, high‑margin tasks that can be executed by junior engineers.
Source: ChannelLife Australia https://channellife.com.au/story/sp...-platform-to-boost-azure-efficiency-for-msps/
 Background
Background
Spotto was founded by a team with operational Azure experience — Shaun Webber, Symon Thurlow and Jay Strydom — and explicitly targets the intersection of FinOps, CloudOps and MSP go‑to‑market motions. The founders’ history running and selling Azure‑centric managed services shaped a product ethos focused on turning optimisation into recurring professional services rather than a one‑off savings report. The product has been in active beta with MSPs, SaaS firms and enterprise customers and now enters general availability with functionality that includes multi‑daily scans of connected Azure tenants, consolidated dashboards for cost, security, performance and reliability signals, and integrations into PSA/issue‑tracking systems such as Jira, ConnectWise and Halo. Spotto’s public messaging frames the platform as a way to lower the skill threshold for routine cloud remediation while creating a pipeline of small, high‑margin tasks that can be executed by junior engineers. What Spotto claims to deliver
Continuous, read‑only discovery and multi‑signal analysis
Spotto advertises a continuous scanning model that runs “multiple times per day” across each connected Azure tenant. The platform aggregates telemetry across four core domains:- Cost and FinOps — rightsizing, idle resources, SKU mismatches and tagging gaps.
- Performance — inefficient VM instance types, misconfigured scale sets and autoscaling problems.
- Security — policy drift, missing hardening, misconfigurations exposing risk.
- Reliability — backup gaps, single points of failure, and operational hygiene issues.
Action Engine: signal → context → ticket
Spotto differentiates itself with what it calls an Action Engine: findings are contextualised, prioritised by business impact and estimated effort, and then converted into actionable tickets inside the MSP’s PSA or issue tracker. The goal is to hand engineers “ready‑to‑execute” tasks, complete with the reasoning, business impact, risks and alternatives needed to act quickly and consistently. The company lists Jira, ConnectWise and Halo among integration examples, and public documentation provides a detailed Jira integration guide.AI‑powered recommendations beyond Azure Advisor
A headline claim from Spotto is that roughly one‑third of all optimisation recommendations come from the company’s proprietary AI models rather than Azure Advisor. Spotto says these models are trained on operational experience from large, mission‑critical environments and therefore surface opportunities not visible to native tooling. Each recommendation is accompanied by supporting context — reasoning, risk analysis, alternatives and effort estimates — to support rapid triage and execution. This claim appears consistently in vendor communications and third‑party reporting, though it should be treated as company‑reported until independently validated.Unified insights and workflow embedding
By consolidating cost, performance, security and reliability metrics into a single dashboard, Spotto intends to reduce the investigation time that Azure users currently spend navigating multiple portals and consoles. The combination of consolidated visibility plus automated ticket creation aims to embed cloud governance into existing MSP workflows and help convert optimisation signals into monetisable services.Why MSPs and Azure‑first enterprises should take notice
- Monetisable remediation pipeline: Spotto reframes continuous optimisation as a steady stream of billable, repeatable engineering work rather than a one‑time cost exercise. That aligns with MSP business models that rely on predictable professional services revenue.
- Lowering skill thresholds: The platform’s contextual guidance and effort estimates are designed to let junior engineers implement routine fixes safely, improving utilization without proportionately increasing senior headcount.
- Operational fit: Built‑in PSA integrations and the emphasis on ticket automation reduce friction for MSPs that already manage customer workloads via Jira, ConnectWise or Halo. Placing work into existing pipelines increases the likelihood that findings become billable tasks.
- Azure specificity: By specialising on Microsoft Azure, Spotto claims deeper platform‑specific heuristics than generalist, multi‑cloud FinOps tools — an advantage for organisations with predominantly Azure estates.
Technical and security considerations
Permissions model and attack surface
Spotto’s recommended onboarding uses an Entra ID (Azure AD) application with Reader and Billing Reader roles across monitored subscriptions. This is sensible as a least‑privilege starting point, but MSPs and customers should confirm scoping at the resource group level where possible. Any automation that stores API tokens, triggers ticket creation, or enables delegated execution increases the attack surface; insist on encrypted token storage, detailed audit logging and RBAC for automation controls.Read‑only vs automated remediation
While the read‑only model reduces risk during analysis, the real value proposition for MSPs often depends on moving from recommendations to execution. That transition requires strict governance:- Start with monitoring mode only, then enable low‑risk automated actions (e.g., scheduled off‑hours VM shutdowns).
- Require human approvals for non‑idempotent or production‑impacting operations (reboots, configuration rollouts).
- Maintain canary targets and rollback playbooks for any automated changes.
Data handling and compliance
MSPs should verify how Spotto stores telemetry, where that data is located, and what encryption and retention policies are in place. Data residency and deletion clauses should be explicit in contracts, especially for regulated customers. Ask the vendor to confirm that billing telemetry and resource metadata are deleted upon contract termination.Accuracy, noise and the need for validation
Any automated recommendation engine can produce false positives. If recommendations require heavy manual triage, the tool can actually increase operational cost rather than reduce it. Procurement teams should insist on measurable pilot outcomes:- Recommendation acceptance rate (recommendation → accepted → implemented).
- Time‑to‑remediation for recommended actions.
- False‑positive and rollback events.
Competitive landscape and where Spotto fits
The cloud optimisation and FinOps market is crowded, spanning specialist tools, cloud provider native services and broader operations platforms. Key competitive vectors:- Established FinOps and cloud‑cost platforms (multi‑cloud) that offer mature analytics and rightsizing automation.
- Cloud vendor native tools (Azure Cost Management, Azure Advisor) that are free or bundled but can lack consolidated, contextual execution workflows.
- CloudOps platforms that emphasize automation and infrastructure orchestration at scale.
Practical buyer checklist — what to validate during evaluation
- Confirm integration maturity:
- Test Jira integration end‑to‑end (issue creation, field mapping, epic linking, status sync).
- Validate support for ConnectWise and Halo with sample projects.
- Pilot with representative tenants:
- Run Spotto for 30–60 days in monitoring mode across a selection of customers reflecting your architecture diversity.
- Capture recommendation hit rate and time‑to‑implement metrics.
- Validate recommendation provenance:
- Request a breakdown for recommendations: Azure Advisor signal vs Spotto model vs heuristic.
- Ask for concrete examples where Spotto found issues Azure Advisor did not.
- Measure economic value:
- Model time‑to‑first‑billable‑task and payback period based on your MSP labour rate and typical ticket sizes.
- Security and compliance gates:
- Confirm token encryption, audit logging, role separation and data deletion guarantees.
- Test automation controls:
- Start with draft tickets only, then enable automatic ticket creation for low‑risk categories.
- Require human sign‑off for changes affecting production availability.
Operational playbook: staged deployment (recommended)
- Register the Entra ID application and grant Reader + Billing Reader roles for pilot subscriptions.
- Run Spotto in monitoring‑only mode for 30 days; log all recommendations but do not enable automatic tickets.
- Review recommendations with senior engineers; tag those that would be accepted vs ignored.
- Enable automatic ticket creation for a narrow set of high‑confidence, low‑risk actions (e.g., tag fixes, idle VM shutdown drafts).
- Measure acceptance rate, time‑to‑remediate and rollback events for an additional 30 days.
- Expand ticket automation categories where precision is high; keep dangerous actions manual‑approval gated.
- Iterate on playbooks and feed results back to Spotto for model tuning.
Product roadmap and what to watch for
Spotto says it will continue to develop deeper automation, better forecasting, more sophisticated anomaly detection and additional PSA integrations. The company also markets a Chrome extension (Autopilot for Azure) that surfaces recommendations inside the Azure Portal, signaling an interest in reducing context switching for engineers. Buyers should watch:- Improvements in model explainability and confidence scoring.
- The vendor’s published metrics for recommendation precision/recall.
- New enterprise security certifications or compliance attestations.
- Expansion of two‑way PSA sync and support for other common MSP tooling.
Risks and red flags
- Vendor‑reported metrics: Claims like “one‑third of recommendations come from Spotto’s models” require independent validation. Ask for anonymised evidence and sample outputs before buying.
- Alert fatigue: If recommendation precision is low, engineers will ignore the tool and ROI will evaporate.
- Integration brittleness: Variable maturity across PSAs may force custom work that erodes the intended low‑friction value.
- Automation risk: Enabling remediation without adequate approvals can introduce production incidents; staged rollouts are essential.
Conclusion
Spotto’s GA release is a clear tactical move: target Azure‑first MSPs and enterprise cloud teams with an operator‑led product that aims to turn optimisation signals into predictable, billable work. For Azure‑centric MSPs struggling to monetise FinOps and CloudOps, the platform’s emphasis on continuous scanning, contextualised recommendations and PSA embedding is compelling. Third‑party reporting and the vendor’s own materials consistently highlight the same core value proposition: convert telemetry into work that can be sold and executed reliably by existing engineering teams. However, the most important verification step is hands‑on: validate recommendation precision, measure real time‑to‑remediation, and pilot two‑way PSA workflows in representative customer estates. Treat headline percentages and model claims as vendor‑reported until they survive objective tests in your environment. With disciplined pilots, clear governance and staged automation, Spotto could be an effective addition to an MSP’s toolkit for Azure optimisation — but the economics and safety of that addition will only be proven under real operating conditions.Source: ChannelLife Australia https://channellife.com.au/story/sp...-platform-to-boost-azure-efficiency-for-msps/