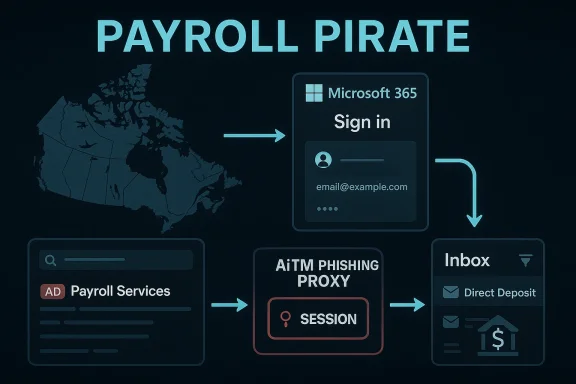
Microsoft’s latest Storm-2755 research is a sharp reminder that payroll fraud has evolved far beyond simple credential theft. In the campaign Microsoft DART analyzed, attackers used malvertising, SEO poisoning, and adversary-in-the-middle (AiTM) phishing to hijack sessions, bypass MFA, and redirect salary payments from Canadian employees to attacker-controlled bank accounts. What makes this case especially notable is the combination of geographic targeting, legitimate-looking login infrastructure, and abuse of business workflows rather than malware-heavy tradecraft. (microsoft.com)
Payroll diversion attacks are not new, but they have become more operationally mature over the past year. Microsoft previously documented a similar “payroll pirate” campaign affecting U.S. universities, where Storm-2657 used phishing, inbox-rule manipulation, and Workday account abuse to redirect employee wages. In that earlier campaign, Microsoft found that the threat actor’s success depended less on exploiting software flaws and more on exploiting identity gaps, weak MFA, and insufficient monitoring between first-party email and third-party HR systems. (microsoft.com)
The new Storm-2755 report shows how these campaigns are adapting. Instead of targeting a single sector, the actor focused on Canadian users and used industry-agnostic search terms to locate victims through search results and ads. That shift matters because it broadens the attack surface and makes defense harder; a campaign no longer needs a sector-specific lure if the adversary can simply wait for users to search for common Microsoft 365 or Office sign-in terms. (microsoft.com)
The timing also says something about where identity abuse is heading. In 2025 and 2026, Microsoft has repeatedly highlighted the rise of AiTM phishing, session hijacking, and token replay as preferred attack paths for financially motivated actors. This reflects a larger pattern: as organizations harden passwords and conventional MFA, attackers increasingly aim at the authenticated session itself rather than the password prompt. (microsoft.com)
That is why this incident lands as more than another phishing story. It is a case study in how attackers now chain together lure delivery, session theft, persistence, discovery, and workflow abuse to convert a single compromised account into direct monetary loss. For defenders, that means the control problem is no longer just “did the user click?” but also “what happened after the user authenticated?” (microsoft.com)
The core of the operation appears to have been session hijacking. Microsoft says victims were directed to a malicious Microsoft 365 sign-in page, where credentials and authentication material were captured in real time. Once the attacker had a valid session, they could operate as if they were the user, including accessing Outlook, profile pages, and downstream HR or payroll systems.
Once the victim clicked through, they landed on a fake Microsoft 365 sign-in page designed to mimic the real one. This is a familiar tactic, but the operational detail here is the real story: Microsoft observed a distinctive sign-in failure sequence, including a 50199 interrupt error before the account was compromised, followed by a user-agent change to Axios while the session ID stayed the same. That combination strongly suggests token replay rather than a brand-new login from scratch.
The report also notes that after roughly 30 days, the stolen tokens would become inactive if the actor did not maintain persistence. That detail is important because it highlights both the limitation and the danger of token replay: the window is finite, but within that window the attacker can do substantial damage, especially if the organization is not watching for low-and-slow activity.
This step is often underappreciated. Attackers do not need to know everything about an organization; they need only enough to find the control point where payroll changes can be approved, hidden, or social-engineered. A few targeted search terms can reveal the relevant team, portal, or workflow path in a large enterprise.
That kind of rule manipulation is a hallmark of payroll fraud and broader BEC activity. The attacker does not necessarily need to delete everything; it is enough to make the right message vanish from the user’s line of sight. Once the user stops seeing direct deposit alerts, the attacker gains time to complete the financial manipulation. (microsoft.com)
What makes this especially troublesome is that the attack did not depend on any vulnerability in the payroll platform itself. As Microsoft emphasized in the earlier Workday-related campaign, the issue is the abuse of trusted workflows and insufficient identity protections, not a flaw in the SaaS provider. That distinction matters because it widens the problem beyond a single application vendor. (microsoft.com)
The most important control is to move away from reusable second factors that can be intercepted in real time. Microsoft specifically points to FIDO2/WebAuthn, passkeys, and similar phishing-resistant methods because they bind authentication to a legitimate origin and reduce the value of intercepted credentials or OTPs. In this case, the attacker’s success depended on being able to replay a session that was already authenticated. (microsoft.com)
The key analytical insight is that no single alert tells the whole story. A token replay incident may look like a strange user-agent, a geolocation mismatch, a mailbox rule, or a payroll update depending on where you start looking. Only correlation across identity, email, and SaaS events exposes the full chain. (microsoft.com)
For Canadian organizations, the lesson is especially urgent because payroll, HR, and identity tools often span multiple jurisdictions and service providers. That creates a fragmented trust environment in which email, SSO, and payroll systems each look normal in isolation while the overall workflow is being abused. The attacker only needs one weak link in that chain.
The most important strategic shift for organizations is to treat identity as a live security boundary, not a one-time authentication event. If a user’s session, device posture, inbox rules, and payroll modifications are not continuously evaluated together, attackers will keep finding room to move. That is the real lesson of Storm-2755.
What to watch next:
Source: Microsoft Investigating Storm-2755: “Payroll pirate” attacks targeting Canadian employees | Microsoft Security Blog
 Background
Background
Payroll diversion attacks are not new, but they have become more operationally mature over the past year. Microsoft previously documented a similar “payroll pirate” campaign affecting U.S. universities, where Storm-2657 used phishing, inbox-rule manipulation, and Workday account abuse to redirect employee wages. In that earlier campaign, Microsoft found that the threat actor’s success depended less on exploiting software flaws and more on exploiting identity gaps, weak MFA, and insufficient monitoring between first-party email and third-party HR systems. (microsoft.com)The new Storm-2755 report shows how these campaigns are adapting. Instead of targeting a single sector, the actor focused on Canadian users and used industry-agnostic search terms to locate victims through search results and ads. That shift matters because it broadens the attack surface and makes defense harder; a campaign no longer needs a sector-specific lure if the adversary can simply wait for users to search for common Microsoft 365 or Office sign-in terms. (microsoft.com)
The timing also says something about where identity abuse is heading. In 2025 and 2026, Microsoft has repeatedly highlighted the rise of AiTM phishing, session hijacking, and token replay as preferred attack paths for financially motivated actors. This reflects a larger pattern: as organizations harden passwords and conventional MFA, attackers increasingly aim at the authenticated session itself rather than the password prompt. (microsoft.com)
That is why this incident lands as more than another phishing story. It is a case study in how attackers now chain together lure delivery, session theft, persistence, discovery, and workflow abuse to convert a single compromised account into direct monetary loss. For defenders, that means the control problem is no longer just “did the user click?” but also “what happened after the user authenticated?” (microsoft.com)
What Microsoft Says Storm-2755 Did
Microsoft describes Storm-2755 as a financially motivated threat actor that specifically targeted Canadian employees and attempted to divert salary payments to attacker-controlled accounts. The campaign was not centered on one employer or one vertical; instead, it used broad geographic targeting, with Canadian identity and payroll processes acting as the common denominator. That is a meaningful escalation because it suggests the actor was optimizing for scale and reuse rather than narrow, highly customized spear-phishing.The core of the operation appears to have been session hijacking. Microsoft says victims were directed to a malicious Microsoft 365 sign-in page, where credentials and authentication material were captured in real time. Once the attacker had a valid session, they could operate as if they were the user, including accessing Outlook, profile pages, and downstream HR or payroll systems.
Why the campaign stands out
The most important distinction is that the actor was not simply stealing passwords. It was replaying tokens and maintaining active sessions, which allowed the threat actor to bypass traditional MFA protections that are not phishing-resistant. That shift is critical because the stolen session becomes a far more durable asset than a password alone. (microsoft.com)- Geographic targeting rather than vertical targeting.
- SEO poisoning and malvertising for initial victim discovery.
- AiTM phishing to capture authenticated sessions.
- Inbox-rule abuse to suppress HR notifications.
- Manual payroll manipulation when social engineering did not fully succeed.
Initial Access Through Search and Phishing
Microsoft says Storm-2755 likely drew victims in with SEO poisoning and malvertising, pushing an actor-controlled domain to the top of search results for generic queries such as “Office 365” or common typos like “Office 265.” That matters because it turns ordinary search behavior into an initial-access vector. Instead of waiting for a user to respond to a suspicious email, the attacker meets the user at the moment of need: when they are actively searching for a login page.Once the victim clicked through, they landed on a fake Microsoft 365 sign-in page designed to mimic the real one. This is a familiar tactic, but the operational detail here is the real story: Microsoft observed a distinctive sign-in failure sequence, including a 50199 interrupt error before the account was compromised, followed by a user-agent change to Axios while the session ID stayed the same. That combination strongly suggests token replay rather than a brand-new login from scratch.
Why the user-agent change matters
The change to Axios is not because Axios itself is malicious. Rather, it appears to be the HTTP client used by the attacker’s infrastructure to relay or replay authentication material after capture. In practical terms, defenders should treat an unexpected shift in user-agent, combined with session continuity, as a clue that the attacker is operating through an existing token rather than authenticating normally.- Monitor for impossible travel and nonstandard geolocation.
- Look for sign-ins that show a token replay pattern.
- Treat an unusual user-agent transition as a high-priority signal.
- Correlate browser, token, and mailbox activity together, not in isolation. (microsoft.com)
Session Hijacking and Persistence
Microsoft’s analysis shows that Storm-2755 relied on authenticated sessions to stay inside environments after the initial compromise. The company observed non-interactive sign-ins to OfficeHome and recurring activity tied to the Axios user-agent roughly every 30 minutes until remediation revoked the tokens. That pattern is exactly why token theft is so attractive to attackers: it lets them behave like a legitimate user without repeatedly prompting for credentials.The report also notes that after roughly 30 days, the stolen tokens would become inactive if the actor did not maintain persistence. That detail is important because it highlights both the limitation and the danger of token replay: the window is finite, but within that window the attacker can do substantial damage, especially if the organization is not watching for low-and-slow activity.
Persistence methods that increase risk
Microsoft observed that in some cases the actor also changed passwords or MFA settings, creating a more durable foothold. That is a sign that the campaign was not merely opportunistic; it was built to preserve access if the primary session expired. A single token may be temporary, but a newly enrolled MFA factor can make the compromise much more resilient. (microsoft.com)- Non-interactive sign-ins can indicate token replay.
- Repeated activity at consistent intervals can suggest automated session maintenance.
- Password resets and MFA reconfiguration can extend attacker dwell time.
- Session revocation is necessary, but insufficient on its own if identity settings remain compromised. (microsoft.com)
Discovery Inside the Organization
After gaining access, Storm-2755 conducted discovery activity to locate payroll and HR processes. Microsoft says the threat actor searched intranet resources for terms including payroll, HR, human, resources, finance, account, and admin. That tells us the actor was looking for the fastest route from a mailbox or portal compromise to a salary diversion event.This step is often underappreciated. Attackers do not need to know everything about an organization; they need only enough to find the control point where payroll changes can be approved, hidden, or social-engineered. A few targeted search terms can reveal the relevant team, portal, or workflow path in a large enterprise.
Social engineering the payroll workflow
Microsoft also observed email subject lines such as “Question about direct deposit” being used consistently across compromised users. The point was to pressure HR or finance staff into making manual changes on the attacker’s behalf, reducing the amount of hands-on keyboard activity the adversary needed inside the environment. That is classic business email compromise logic, but with a sharper payroll objective.- Discovery was aimed at human workflows, not just data.
- Subject lines were crafted to trigger HR or finance action.
- Manual approvals were used as a substitute for deeper account compromise.
- The attacker preferred process abuse over noisy exploitation.
Defense Evasion and Email Suppression
A major part of the campaign was defense evasion through inbox-rule abuse. Microsoft says Storm-2755 created rules to move messages containing keywords such as “direct deposit” or “bank” into the compromised user’s conversation history, effectively hiding HR correspondence and suppressing visible warnings. This is a simple trick, but a powerful one, because it keeps the victim from seeing the very messages that might expose the compromise.That kind of rule manipulation is a hallmark of payroll fraud and broader BEC activity. The attacker does not necessarily need to delete everything; it is enough to make the right message vanish from the user’s line of sight. Once the user stops seeing direct deposit alerts, the attacker gains time to complete the financial manipulation. (microsoft.com)
Timing as an evasion tactic
Microsoft also observed token renewal around 5:00 AM in the user’s local time zone, when legitimate reauthentication was less likely. That is a small detail with big implications: attackers know that human attention patterns matter, and they deliberately schedule activity to avoid interrupting the user or triggering an immediate response. Quiet hours are attacker hours.- Inbox rules can hide warnings without breaking mail flow.
- Off-hours activity reduces the chance of user detection.
- Deletion, movement, and suppression all matter as indicators.
- Email investigation should include rule creation, not just message delivery. (microsoft.com)
Impact on Payroll and HR Systems
The end goal was straightforward: redirect payroll to an attacker-controlled account. Microsoft says the compromise led to direct financial loss in at least one case, where the attacker used the stolen session to manipulate direct deposit details through HR software. That is the practical consequence of payroll pirate attacks: they turn identity compromise into payroll theft.What makes this especially troublesome is that the attack did not depend on any vulnerability in the payroll platform itself. As Microsoft emphasized in the earlier Workday-related campaign, the issue is the abuse of trusted workflows and insufficient identity protections, not a flaw in the SaaS provider. That distinction matters because it widens the problem beyond a single application vendor. (microsoft.com)
Why HR and payroll software are high-value targets
Payroll platforms often contain the data attackers need to complete a fraud loop: employee identity, bank details, approval routes, and notification patterns. If an attacker can access both email and HR systems, they can often orchestrate a believable change without needing to breach finance directly. In that sense, payroll software becomes the last mile of identity abuse. (microsoft.com)- Payroll systems carry high-trust financial data.
- Email confirms or conceals payroll changes.
- HR staff may be conditioned to process direct-deposit requests quickly.
- Attackers use the organization’s own procedures against it.
Mitigation Strategy: What Actually Helps
Microsoft’s recommended defenses line up around a few clear themes: phishing-resistant MFA, session revocation, Conditional Access, inbox-rule monitoring, and stronger device compliance enforcement. That is the right playbook because the attack is not just a phishing problem; it is an identity, mail, and SaaS workflow problem. (microsoft.com)The most important control is to move away from reusable second factors that can be intercepted in real time. Microsoft specifically points to FIDO2/WebAuthn, passkeys, and similar phishing-resistant methods because they bind authentication to a legitimate origin and reduce the value of intercepted credentials or OTPs. In this case, the attacker’s success depended on being able to replay a session that was already authenticated. (microsoft.com)
Operational priorities for defenders
The response sequence matters almost as much as the control set. First, revoke tokens and active sessions. Then remove malicious inbox rules, reset passwords, review MFA registrations, and confirm that payroll or direct-deposit data has been restored. If you leave the session alive, the attacker may retain a foothold even after a password change. (microsoft.com)- Revoke active sessions and tokens immediately.
- Remove suspicious inbox rules and mail-forwarding behavior.
- Reset passwords and re-register MFA with phishing-resistant methods.
- Audit recent payroll and bank-account changes.
- Review device joins, OAuth consent, and unusual sign-in patterns.
Detection, Hunting, and Microsoft Defender Coverage
One of the strongest parts of the report is its emphasis on practical detection. Microsoft maps the campaign to observed Defender and Entra signals, including unusual OAuth device code activity, possible AiTM detection, atypical travel, and suspicious inbox-rule creation. That gives defenders a usable starting point rather than a purely descriptive threat note.The key analytical insight is that no single alert tells the whole story. A token replay incident may look like a strange user-agent, a geolocation mismatch, a mailbox rule, or a payroll update depending on where you start looking. Only correlation across identity, email, and SaaS events exposes the full chain. (microsoft.com)
Useful hunting angles
Organizations should hunt for session anomalies, especially around the OfficeHome app, mailbox rules involving direct deposit and bank, and any payroll-related modification events in Workday or similar SaaS systems. Microsoft also notes that Defender for Cloud Apps can correlate Exchange Online and third-party SaaS activity, which is especially valuable when the attacker is moving between first-party and external services. (microsoft.com)- Focus on non-interactive sign-ins.
- Look for uncommon user-agents like Axios in auth logs.
- Hunt for inbox rules created after suspicious sign-ins.
- Correlate mail activity with payroll or HR edits.
- Review suspicious device joins and OAuth consent events.
Why This Matters for Canada and for Everyone Else
Although the campaign specifically targeted Canadian users, the implications are broader. Geographic targeting is often a sign that an attacker has found a profitable combination of language, regional payroll norms, and likely identity providers. Once that formula works in one market, there is every reason to think it can be adapted elsewhere.For Canadian organizations, the lesson is especially urgent because payroll, HR, and identity tools often span multiple jurisdictions and service providers. That creates a fragmented trust environment in which email, SSO, and payroll systems each look normal in isolation while the overall workflow is being abused. The attacker only needs one weak link in that chain.
Enterprise and consumer impact differ
For enterprises, the primary risk is financial fraud at scale, plus the possibility of lateral abuse if the same compromised identity can access other cloud tools. For employees, the damage is more personal and immediate: lost wages, time spent disputing payroll changes, and exposure of personal financial data. In other words, a single compromise can hurt both the organization’s controls and the worker’s paycheck. (microsoft.com)- Regional targeting can still have global lessons.
- SaaS workflows create cross-border complexity.
- Employee trust is part of the attack surface.
- Payroll fraud is both an IT and an HR problem.
Strengths and Opportunities
Microsoft’s report is strong because it translates a complicated identity attack into concrete defensive action. It also shows how cloud logs, SaaS audit trails, and identity telemetry can be stitched together to expose a campaign that might otherwise hide inside normal business activity. That creates an opportunity for organizations to improve not just detection, but trust in their payroll processes. (microsoft.com)- The campaign description is operationally specific and actionable.
- The report ties identity abuse to payroll fraud in a clear chain.
- Defender and Entra detections give security teams a practical starting point.
- CAE and phishing-resistant MFA directly reduce attacker value.
- Inbox-rule hunting closes a common visibility gap.
- Cross-service correlation improves incident scoping.
- The attack pattern is reusable across many SaaS environments, so hardening one area can pay off broadly. (microsoft.com)
Risks and Concerns
The biggest concern is that this attack pattern is both simple to repeat and hard to notice early. Once attackers can hijack a session, hide mail, and alter payroll details, the organization may not realize anything is wrong until money has already been diverted. That makes speed of detection, not just prevention, a critical issue.- Legacy MFA remains vulnerable to real-time phishing and token theft.
- Payroll and HR teams may trust email-based change requests too readily.
- Session replay can survive password changes if tokens are not revoked.
- Inbox rules can conceal the strongest warning signs.
- Cross-platform logging gaps make investigations slower.
- Human review of payroll changes is often too late or too manual.
- Regional or sector-specific targeting can lull defenders into thinking they are outside the risk zone. (microsoft.com)
Looking Ahead
The next phase of payroll pirate activity will likely involve even more refinement around session theft, attacker infrastructure, and workflow manipulation. Microsoft’s telemetry already shows that adversaries are learning to combine phishing, token replay, and business process abuse into a single playbook that scales across targets. That means defenders should expect variation, not repetition, in the next wave.The most important strategic shift for organizations is to treat identity as a live security boundary, not a one-time authentication event. If a user’s session, device posture, inbox rules, and payroll modifications are not continuously evaluated together, attackers will keep finding room to move. That is the real lesson of Storm-2755.
What to watch next:
- Wider adoption of phishing-resistant MFA and passkeys.
- More aggressive token revocation and CAE-based response workflows.
- Better alerting on inbox-rule creation and mail suppression.
- Broader correlation between email, identity, and HR SaaS telemetry.
- Copycat campaigns in other countries or industries using the same basic playbook. (microsoft.com)
Source: Microsoft Investigating Storm-2755: “Payroll pirate” attacks targeting Canadian employees | Microsoft Security Blog