I installed Windows 11 on a 10‑year‑old PC using Rufus’ built‑in bypass options — and it worked, but not magically: Rufus modifies the Windows 11 installer so the setup program skips Microsoft’s hardware gates, while the installed OS remains an unmodified Windows 11 image. This approach gives you a practical path to bring legacy machines forward, but it also carries real tradeoffs — from possible update restrictions and driver incompatibilities to the risk of data loss if you don’t prepare carefully. rosoft tightened Windows 11 compatibility rules at launch and continued to enforce them in later releases. The headline requirements that block many older PCs are TPM 2.0, UEFI Secure Boot, and a restricted list of supported CPUs; minimum RAM and storage thresholds also apply. Microsoft’s enforcement can occur at two points: the booted installer flow and the in‑place upgrade flow (running Setup.exe from a working Windows 10). Installing on unsupported hardware is possible, but Microsoft treats such installs as unsupported — which means potential update gating and no guarantee of stability.
Windows 10 also has an end‑of‑support here: after that date many users will want to move to Windows 11 for continued security updates. That deadline is one of the reasons this bypass method circulates widely — it’s a stopgap to keep older hardware receiving current OS software for longer.
It’s important to be precise: Rufus does not patch the Windows kernel, add hidden drivers, or produce a cracked OS image. Instead, indows 11 installation media** so Setup’s compatibility checks are not run or are neutralized. That means the installer is the thing being tricked; once Windows 11 is installed, it runs as a standard, unmodified copy of Windows 11.
Key technical mechanisms that have been observed and documented in community reporting include:
Mitigations, in short:
If you value cost‑effectiveness and are confident with backups, driver troubleshooting and occasional manual maintenance, Rufus gives a clean, automated route to Windows 11 on many legacy systems. If you need guaranteed support, future feature parity, and the lowest‑risk environment — invest in supported hardware instead.
Windows evolves, and vendor policy changes can alter what’s possible overnight. The installer bypass technique is effective and well‑documented today, but treat it as a pragmatic extension of usable hardware life — not a permanent substitute for supported upgrades. Plan, backup, test, and proceed deliberately.
Source: MakeUseOf I just installed Windows 11 on a 10-year old PC — this method still works
Windows 10 also has an end‑of‑support here: after that date many users will want to move to Windows 11 for continued security updates. That deadline is one of the reasons this bypass method circulates widely — it’s a stopgap to keep older hardware receiving current OS software for longer.
 How Rufus’ bypass actually works — installer modification, not an OS crack
How Rufus’ bypass actually works — installer modification, not an OS crack
It’s important to be precise: Rufus does not patch the Windows kernel, add hidden drivers, or produce a cracked OS image. Instead, indows 11 installation media** so Setup’s compatibility checks are not run or are neutralized. That means the installer is the thing being tricked; once Windows 11 is installed, it runs as a standard, unmodified copy of Windows 11.Key technical mechanisms that have been observed and documented in community reporting include:
- Replacing or neutralizing the installer’s ct (commonly referred to as the appraiser/appraiserres DLL) so the checks aren’t executed during setup. This is the gatekeeper that normally causes the “This PC can’t run Windows 11” message.
- Injecting registry toggles into the installer environment — most often under HKEY_LOCAL_MACHINE\SYSTEM\Setup\LabConfig and sometimes HKEY_LOCAL_MACHINE\SYSTEM\Setup\MoSetup — that tell Setup to bypass TPM, Secure Boot, RAM and CPU checks. Thesual registry bypasses circulated in forums.
- Wrapping the official Setup.exe in a small “installer wrapper” so the modified behavior runs smoothly during an in‑place upgrade scenario; some Rufus builds bundle these changes automatically when you select the option in the Rufus UI.
What you can and cannot expect if you use this method
What it will do for you
- Let you perform an in‑place upgrade from Windows 10 to Windows 11 on many machines that would otherwise be blocked.
- Allow a clean install of Windows 11 from USB on machines missing TPM 2.0 or Secure Boot, or with older CPUs that would normally be rejected by the standard installer.
- Keep your installed OS as a genuine, unaltered Windows 11 build — licensing and activation remain the standard process.
What it will not do
- It will not add or emulate TPM or CPU features that the hardware lacks. If a CPU lacks necessary instruction sets enforced by a particular Windows 11 build (for example SSE4.2 enforcement in some updates), the installation may fail or the OS may be unstable. Rufus can only bypass Setup’s checks, not add hardware-level features.
- It will not guarantee future feature updates. Microsoft can and has altered installer logic and update distribution to block unsupported machines from receiving some updates, so an install that works today might be limited later.
Step‑by‑step: How people typically use Rufus to install Windows 11 on an older PC
Below is a condensed but practical flow that reflects how Rufus’ bypass option is commonly used. Use this as a blueprint — not a guaranteed script — and read the on‑screen prompts Rufus presents.- Back everything up (see the dedicated section below).
- Download the officialMicrosoft and save it locally.
- Download and run the latest Rufus executable (portable). Insert an empty USB drive (8–16GB or larger).
- In Rufus:
- Select your USB device and the Windows 11 ISO.
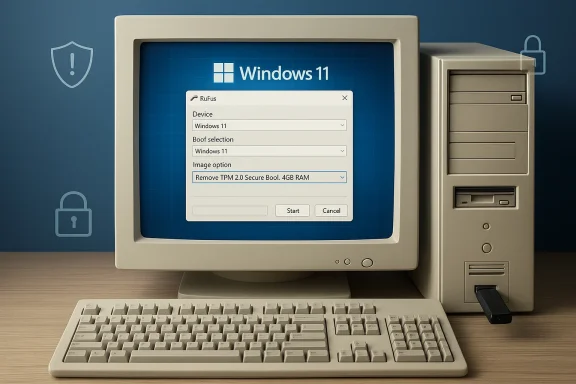
- Let Rufus auto‑populate Partition scheme and Target system (typically GPStart. When Rufus presents the Windows User Experience dialog, check the box that reads like “Remove requirement for TPM 2.0, Secure Boot, 4GB RAM” and any other bypass toggles you want (e.g., local account bypass). Confirm and allow Rufus to write the media.
s, you have two choices: - Run Setup.exe from the USB while in Windows 10 to perform an in‑place upgrade (keeps apps/settings, and gives a 10‑day rollback window).
- Boot from the USB for a clean install (recommended for stability but no rollback).
Back up first — and how to do it properly
This is the non‑negotiable step. If something goes wrong you need a reliable restore point.- Create a full system image backup (not just file copies). Use Windows’ built‑in “Backup and Restore (Windows 7)” system image tool or a tl to capture the entire system drive. Store the image on an external drive (never the same internal disk).
- Export and save your product keys, two‑factor tokens, and any bespoke configuration files.
- Confirm you can boot from recovery media before you begin.
The exact registry toggles and why they matter
Two registry locations are commonly associated with bypass tactics:- HKEY_LOCAL_MACHINE\SYSTEM\Setup\MoSetup
- Create DWORD AllowUpgradesWithUnsupportedTPMOrCPU = 1
- Historically used to allow upgrades when the installer reports unsupported CPU/TPM in the in‑place flow. It was once documented by Microsoft and later became an “undocumented” community workaround.
- HKEY_LOCAL_MACHINE\SYSTEM\Setup\LabConfig
- DWORDs like BypassTPMCheck, BypassSecureBootCheck, BypassRAMCheck, BypassCPUCheck = 1
- These keys are used to tell the booted installer to skip specific hardware checks and are typically what Rufus injects into the installer image.
Risks, real‑world pitfalls, and mitigations
1) Future updates may be withheld or blocked
Microsoft has signaled — and in some cases implemented — stricter enforcement in later Windows 11 builds and feature updates. That means a machine that boots Windows 11 today may be excluded from future major updates or put onto a different update channel. Plan for this: if long‑term update fidelity is essential, consider replacing or upgrading hardware instead.2) Driver and stability issues
Older hardware vendors may not provide drivers validated for modern Windows 11 builds. Expect to spend time updating chipset, storage, Wi‑Fi, and GPU drivers after an upgrade. Test hardware functionality (audio, netwer management) thoroughly. Keep driver installers handy.3) Security tradeoffs
By bypassing TPM and Secure Boot checks you may be installing Windows in an environment with reduced hardware‑rooted protections — this is especially relevant for features that rely on TPM, like BitLocker key protection and Windows Hello security. If you must run on such hardware, compensate with other security controls (full disk encryption using software that doesn’t require TPM, stricter account controls, network segmentation).4) Activation and licensing
Using Rufus and a modified installer does not automatically void licensing — Windows activation is handled the same way after install. But if you move a license tied to specific hardware, activation issues can arise; be prepared to re‑activate or contact Microsoft support if needed. This is not a recommendation to use non‑genuine keys — always use legitimate licenses.5) Manufacturer and OEM support
Valve your driver and firmware support expectations: OEMs rarely support Windows on hardware beyond the lifecycle they publish. If your PC is critical for work, weigh the cost of unplanned downtime and driver hunts against the price of a modest hardware upgrade.Mitigations, in short:
- Full system image backup
- Driver packages downloaded pre‑upgrade
- Create recovery USB/media and test it
- Post‑install snapshot or image once the system is stable
What the community and independent reporting say
Major independent outlets and active community threads have documented both the mechanism and the outcomes:- Ars Technica walked through the registry and Rufus paths and confirmed that MoSetup and LabConfig toggles are central to the manual and automated bypasses. The piece also notes that the MoSetup key sometimes only appears after an initial failed install, and that you can create it yourself.
- GHacks and numerous Windows community posts explain the ongoing cat‑and‑mouse dynamic: Microsoft may close some bypass routes in future builds while other methods persist, and enforcement tightened in certain releases (notably around the 24H2 timeframe). That means the bypass’s longevity is not guaranteed.
- Community archives and forum threads documenting Rufus’ installer wrapper and the 0‑byte appraiser replacement show how the tool automates what used to be a manual ISO hack, and users report widespread success on many olderts about specific legacy CPUs and instruction set enforcement.
A realistic decision framework: when to use the Ro upgrade hardware
Ask yourself the following questions before you proceed:- Is this machine essential for daily work or business continuity?
- If yes, prefer hardwarertified replacement; unsupported installs add risk.
- Do you need long‑term Windows Update and feature fidelity?
- If yes, unsupported installs are not ideal — you may be excluded from future updates.
- Ie healthy (fast storage, upgradable RAM, compatible drivers available)?
- If yes and you need temporary life extension for the hardware, the Rufus route can be economical.
- Have you created a tested recovery image and verified backups?
- If no, stop — backup before you proceed.
Practical example: what I did (concise, reproducible)
- Prepared a full image backup of the drive to an external disk. Confirmed recovery media could boot and restore the image.
- Downloaded the official Windows 11 ISO from Microsoft to a fast local folder.
- Launched Rufus (latest portable), selected the ISO, clicked Start, and checked Remove TPM / Secure Boot / 4GB RAM when prompted. Let Rufus finish writing the USB.
- Booted from the USB and chose Clean Install. After a couple of reboots and driver installs (chipset and storage drivers), the system came up stable. I then took a fresh image of the resulting install.
Final verdict — who should consider it
The Rufus installer bypass is a powerful, practical tool for enthusiasts, labs, hobbyists and small‑scale deployments that need to extend the serviceable life of older PCs. It is not a universal solution and shouldn’t be the first choice for mission‑critical machines, enterprise fleets, or users who require uninterrupted, fully supported Windows update channels.If you value cost‑effectiveness and are confident with backups, driver troubleshooting and occasional manual maintenance, Rufus gives a clean, automated route to Windows 11 on many legacy systems. If you need guaranteed support, future feature parity, and the lowest‑risk environment — invest in supported hardware instead.
Windows evolves, and vendor policy changes can alter what’s possible overnight. The installer bypass technique is effective and well‑documented today, but treat it as a pragmatic extension of usable hardware life — not a permanent substitute for supported upgrades. Plan, backup, test, and proceed deliberately.
Source: MakeUseOf I just installed Windows 11 on a 10-year old PC — this method still works

