Microsoft’s Windows Admin Center is once again at the center of a larger security lesson: hybrid management tools can become a bridge for attackers, not just a convenience for administrators. The recent flaws disclosed around WAC underscore a point that has been easy to overlook in many environments — if a management plane spans on-premises and cloud, compromise in one direction can often become compromise in the other. Microsoft’s own documentation makes clear that WAC is designed to manage servers anywhere and to integrate deeply with Azure, which is precisely why its attack surface matters so much.
Windows Admin Center was built to modernize server administration, replacing a grab bag of legacy tools with a browser-based console that can manage Windows Servers, clusters, and clients without forcing admins to connect directly to each machine. Microsoft positions it as a locally deployed management tool that can run on private networks, while also offering Azure integration for hybrid estates. That combination is powerful, but it also means the product sits in a sensitive place: close enough to the crown jewels to be useful, and close enough to them to be dangerous if abused.
That design choice was not accidental. Microsoft has spent years pitching WAC as the bridge between datacenter operations and the cloud, emphasizing simplified server management, Azure hybrid services, and support for hyperconverged infrastructure. The same Microsoft documentation also notes that WAC complements broader management stacks rather than replacing them, which is important because it hints at the product’s role as an administrative overlay rather than a standalone niche utility. In practice, overlays often become high-value targets because they concentrate permissions and workflows in one place.
The recent Cymulate research described at Black Hat Asia fits neatly into that reality. According to the researchers, the flaws they found in WAC covered both the on-premises edition and the Azure-connected version, and they argued that this makes hybrid management an attack surface that organizations often under-monitor. Their central warning was not simply that vulnerabilities existed, but that those flaws created cross-boundary abuse paths: on-prem tools could be used against cloud assets, and cloud-managed paths could be used against on-prem resources. That is a much more serious architectural concern than a single product bug.
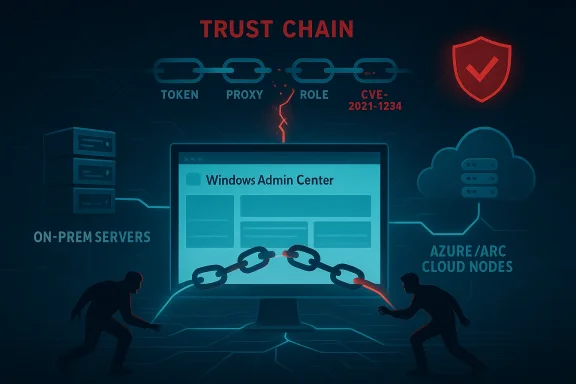
Microsoft’s own Azure-connected WAC documentation helps explain why. The Azure portal version manages Arc-enabled servers through a resource provider, a reverse proxy, a short-lived session flow, and role-based access controls. Those are sensible design elements, but they also create multiple trust transitions, and trust transitions are where many identity and authorization flaws tend to appear. Hybrid systems are especially exposed because they depend on tokens, claims, certificates, proxies, and role mappings all agreeing with one another all the time.
The researchers also reportedly opened with the “This is fine” meme, a visual shorthand for a system that looks calm while sitting in a fire. The symbolism was apt, because hybrid cloud teams often rely on the illusion that control-plane tooling is inherently safer than the assets it manages. In reality, these tools can concentrate blast radius by connecting identity, authorization, and remote execution workflows into a single administrative path. That is why even moderate-looking flaws can have outsized consequences.
That is why the phrase management plane should be treated as a security category, not just an operational one. Security teams often focus on production workloads, data stores, and internet-facing apps, but management tooling can be a shortcut around all of them. If an attacker owns the console used to administer a server, they often no longer need to attack the server in the normal way. That is the essence of a tier zero problem.
This is why hybrid security cannot be treated as a cloud-first or on-prem-first problem. It is a relationship problem. Defenders have to map who can talk to whom, what authority is delegated, how long it lasts, and whether the enforcement point actually verifies every relevant claim. Without that mapping, organizations end up with excellent perimeter controls and a compromised center.
The point is not that every writable folder is fatal. The point is that administrative platforms should assume their installation paths are hostile because they are so attractive to lower-privileged attackers already on the box. WAC, by design, is close to administrative power, so any local misconfiguration can become a platform-wide issue faster than it would for ordinary software. That is especially true where the product is used as a gateway into more valuable environments.
This is one reason cloud identity bugs are so dangerous in hybrid contexts. They do not merely expose data; they can expose administrative reach. If an attacker can re-use or forge a session artifact, they may bypass the expected trust chain and interact with managed resources as though they were the legitimate operator. That is exactly the sort of error that collapses the line between “cloud convenience” and “cloud compromise.”
For defenders, Arc is neither the problem nor the solution by itself. The problem is that when Arc-enabled systems, Azure roles, and admin tooling are tied together, a validation flaw in one place can become a privilege bridge somewhere else. The upside is operational simplification; the downside is a more connected attack graph. Every integration makes life easier for administrators and slightly easier for attackers too.
This creates a security paradox. The more an enterprise modernizes around hybrid admin tooling, the more it can accidentally create a single strategic choke point. That does not mean enterprises should abandon these tools; it means they should treat them as sensitive infrastructure and not as ordinary IT utilities. The right comparison is not “useful versus useless,” but critical versus casual.
SMBs also tend to defer upgrades when a management tool is “working fine.” That is risky in this case because WAC is not just a viewer; it is an execution and orchestration point. Patching it should be treated with the same seriousness as patching a domain controller, backup server, or remote access system. In practical terms, convenience should never be allowed to outrank containment.
The fact that the flaws were assigned CVEs and remediated is important, but CVEs are the beginning of a response, not the end. A well-run security program should ask what made the bugs possible, which access assumptions were wrong, and whether the same code patterns exist in other hybrid management products. In other words: fix the bug, then fix the habit.
The competitive effect is not limited to security marketing. It may also drive more pressure for clearer separation between management interfaces and privileged execution, stronger attestation of managed resources, and tighter defaults around installation paths and service accounts. In a market where trust is a selling point, security design becomes product differentiation. That is both a technical and commercial reality.
Microsoft’s own positioning of WAC suggests the product will remain strategically important. It is built for server management anywhere, integrates with Azure, and supports hybrid operations by design. That means the burden is now on defenders to adopt a “trust but verify” posture that is far more skeptical than the convenience story WAC was originally marketed with. Convenience is not the enemy; complacency is.
Source: theregister.com Hybrid clouds have two attack surfaces – so watch both
 Background
Background
Windows Admin Center was built to modernize server administration, replacing a grab bag of legacy tools with a browser-based console that can manage Windows Servers, clusters, and clients without forcing admins to connect directly to each machine. Microsoft positions it as a locally deployed management tool that can run on private networks, while also offering Azure integration for hybrid estates. That combination is powerful, but it also means the product sits in a sensitive place: close enough to the crown jewels to be useful, and close enough to them to be dangerous if abused.That design choice was not accidental. Microsoft has spent years pitching WAC as the bridge between datacenter operations and the cloud, emphasizing simplified server management, Azure hybrid services, and support for hyperconverged infrastructure. The same Microsoft documentation also notes that WAC complements broader management stacks rather than replacing them, which is important because it hints at the product’s role as an administrative overlay rather than a standalone niche utility. In practice, overlays often become high-value targets because they concentrate permissions and workflows in one place.
The recent Cymulate research described at Black Hat Asia fits neatly into that reality. According to the researchers, the flaws they found in WAC covered both the on-premises edition and the Azure-connected version, and they argued that this makes hybrid management an attack surface that organizations often under-monitor. Their central warning was not simply that vulnerabilities existed, but that those flaws created cross-boundary abuse paths: on-prem tools could be used against cloud assets, and cloud-managed paths could be used against on-prem resources. That is a much more serious architectural concern than a single product bug.
Microsoft’s own Azure-connected WAC documentation helps explain why. The Azure portal version manages Arc-enabled servers through a resource provider, a reverse proxy, a short-lived session flow, and role-based access controls. Those are sensible design elements, but they also create multiple trust transitions, and trust transitions are where many identity and authorization flaws tend to appear. Hybrid systems are especially exposed because they depend on tokens, claims, certificates, proxies, and role mappings all agreeing with one another all the time.
What Happened at Black Hat Asia
The immediate trigger for the current discussion was Cymulate’s Black Hat Asia talk, where Ilan Kalendarov and Ben Zamir described four WAC-related CVEs: CVE-2025-64669, CVE-2026-20965, CVE-2026-23660, and CVE-2026-32196. The Register reported that Microsoft had already fixed the flaws and that there were no signs of active exploitation at the time of the talk. That matters, because this is not a panic story about an in-the-wild outbreak; it is a design-story about what happens when admin tooling becomes too trusted.Why the talk mattered
What made the presentation resonate was not just the bug count, but the direction of the risk. The researchers framed WAC as a two-way attack surface, meaning compromise could start in the cloud and move inward, or start on-prem and move outward. That is a sharper warning than the usual “patch your server” guidance, because it means defenders have to think in both threat models simultaneously. In hybrid estates, the management plane is not just a convenience layer; it is a transit layer for privilege.The researchers also reportedly opened with the “This is fine” meme, a visual shorthand for a system that looks calm while sitting in a fire. The symbolism was apt, because hybrid cloud teams often rely on the illusion that control-plane tooling is inherently safer than the assets it manages. In reality, these tools can concentrate blast radius by connecting identity, authorization, and remote execution workflows into a single administrative path. That is why even moderate-looking flaws can have outsized consequences.
The four vulnerabilities in context
Cymulate said one flaw involved insecure directory permissions in the on-premises WAC installation, allowing an attacker to place malicious files beside the application. Another class of issue involved token handling in the Azure-connected path, where proof-of-possession logic reportedly failed to validate all fields. The researchers’ claim was that the POP token could be reused or forged in a way that enabled takeover of managed tenant VMs and Arc resources. Those are serious allegations, but the broader takeaway is even more important: identity and file-system mistakes can become remote-control mistakes when they sit inside an admin plane.- On-prem WAC created local file placement risk.
- Azure-connected WAC introduced token-validation risk.
- Arc-managed resources expanded the blast radius.
- The combined picture pointed to cross-domain privilege abuse.
Why Hybrid Management Tools Are So Sensitive
Hybrid management software sits in an awkward but powerful spot between endpoint administration, identity, and cloud orchestration. WAC can reach servers, clusters, VMs, and Arc-managed machines, and Microsoft explicitly describes it as a tool for managing infrastructure running anywhere. That breadth is what makes it useful, but it is also what makes it dangerous when the trust chain fails.The trust-chain problem
Every administrative platform depends on layers of trust: the installer must be trusted, the gateway must be trusted, the token must be trusted, the session must be trusted, and the target system must trust the control plane. If any one of those layers is too permissive, attackers can often pivot from “we got a foothold” to “we are now the administrator.” WAC is especially exposed because it is designed to connect privileged systems across environments that are otherwise separated by network boundaries.That is why the phrase management plane should be treated as a security category, not just an operational one. Security teams often focus on production workloads, data stores, and internet-facing apps, but management tooling can be a shortcut around all of them. If an attacker owns the console used to administer a server, they often no longer need to attack the server in the normal way. That is the essence of a tier zero problem.
Cloud-to-on-prem and on-prem-to-cloud
Microsoft’s Azure WAC flow uses a resource provider, Azure role assignments, and short-lived access sessions to connect from the portal into the target machine. That makes sense from an architecture standpoint, but it also means the identity boundary is doing a lot of work. If the tokens or session validation are weak, an attacker can potentially use the portal path to reach the machine; if local WAC is weak, an attacker can potentially use that local control point to move into cloud-managed territory.This is why hybrid security cannot be treated as a cloud-first or on-prem-first problem. It is a relationship problem. Defenders have to map who can talk to whom, what authority is delegated, how long it lasts, and whether the enforcement point actually verifies every relevant claim. Without that mapping, organizations end up with excellent perimeter controls and a compromised center.
The On-Premises Exposure
The on-premises issue reported by Cymulate is the easiest to grasp because it maps to a classic Windows security failure: writable application directories and privileged code execution are a toxic mix. According to the researchers, the WAC directory on the local installation was not write-protected sufficiently, allowing an attacker to place malicious content next to the application. Microsoft’s WAC documentation shows the product is deployed locally on Windows Server or Windows 10 and can act as a gateway, which makes local installation security especially important.Why directory permissions still matter
Directory permissions can sound mundane, but in practice they are one of the most reliable paths to privilege escalation when software later loads or executes files from those locations. A writable folder near a trusted binary can become an execution foothold if update processes, uninstall routines, or helper components run with elevated rights. That is why basic file-system hygiene remains a first-class security control, even in 2026. Old-school problems still produce modern breaches.The point is not that every writable folder is fatal. The point is that administrative platforms should assume their installation paths are hostile because they are so attractive to lower-privileged attackers already on the box. WAC, by design, is close to administrative power, so any local misconfiguration can become a platform-wide issue faster than it would for ordinary software. That is especially true where the product is used as a gateway into more valuable environments.
Local foothold, systemic impact
Once an attacker can abuse a local WAC installation, the real danger is not merely the machine itself. It is the possibility that the machine is the operator’s launchpad into servers, clusters, or cloud-connected resources. In a hybrid environment, one compromised management node may be enough to reach multiple target classes. That makes local privilege escalation in WAC more than a host issue; it becomes an estate issue.- Writable admin directories can become execution vectors.
- Local compromise can become management-plane compromise.
- Management-plane compromise can become estate-wide compromise.
- Hybrid tooling magnifies the consequences of simple misconfigurations.
The Azure-Connected Exposure
The Azure-connected path is more subtle and, arguably, more alarming. Microsoft describes WAC in the Azure portal as using the Microsoft.HybridConnectivity resource provider, a reverse-proxy style connection, and short-lived access sessions tied to Azure permissions. Cymulate’s reported flaw centered on token validation, especially the proof-of-possession mechanism that was supposed to ensure the token was bound to the right resource. If that binding is incomplete, forged or reused tokens can create a counterfeit identity lane.Token validation as a control plane
Tokens are only as strong as their validation rules. If a system checks some fields but not all, it can be tricked into accepting a credential that was never meant for that resource or that moment. In WAC’s Azure-connected architecture, that means the identity boundary is not just about logging in; it is about proving that the caller is authorized for a specific target, at a specific time, under a specific delegated path. Weakness there can make a tenant-wide issue out of what should have been a machine-local one.This is one reason cloud identity bugs are so dangerous in hybrid contexts. They do not merely expose data; they can expose administrative reach. If an attacker can re-use or forge a session artifact, they may bypass the expected trust chain and interact with managed resources as though they were the legitimate operator. That is exactly the sort of error that collapses the line between “cloud convenience” and “cloud compromise.”
Arc makes the blast radius larger
The fact that Azure Arc-managed systems were part of the story matters a great deal. Microsoft’s own WAC-in-Azure documentation says the product can manage Arc-enabled servers and that the Azure portal experience is tightly linked to the Arc resource model. That means the vulnerable trust path is not limited to a single device type or a narrow use case. It touches a broader hybrid-management ecosystem that many organizations now use to unify operations.For defenders, Arc is neither the problem nor the solution by itself. The problem is that when Arc-enabled systems, Azure roles, and admin tooling are tied together, a validation flaw in one place can become a privilege bridge somewhere else. The upside is operational simplification; the downside is a more connected attack graph. Every integration makes life easier for administrators and slightly easier for attackers too.
The Bigger Message for Enterprises
Enterprises are the most obvious audience for this warning because they are the organizations most likely to run hybrid estates at scale. Microsoft’s own materials emphasize WAC’s role in centralizing management, handling Windows Server infrastructure, and integrating with Azure services. That centrality is precisely why a WAC flaw should be read as a platform risk rather than a single-product issue.Operational convenience versus security concentration
Large organizations adopt tools like WAC because they reduce toil. They cut down on remote desktop sprawl, reduce console switching, and make it easier to administer servers from a browser. But every time a company consolidates operations, it also consolidates permissions, session state, and logging paths. That makes a compromise in the management plane much more efficient for the attacker than a compromise scattered across dozens of separate tools.This creates a security paradox. The more an enterprise modernizes around hybrid admin tooling, the more it can accidentally create a single strategic choke point. That does not mean enterprises should abandon these tools; it means they should treat them as sensitive infrastructure and not as ordinary IT utilities. The right comparison is not “useful versus useless,” but critical versus casual.
Recommended enterprise stance
Security teams should inventory where WAC is installed, how it is exposed, which identities can access it, and whether Azure-connected deployments are using the least-privilege roles possible. They should also verify whether local administrators, service accounts, and managed identities are crossing boundaries in ways that widen compromise paths. A hybrid management plane that is not explicitly modeled is a management plane that is already partly blind.- Inventory every WAC deployment.
- Separate on-prem, Azure, and Arc access paths.
- Minimize privileges assigned to WAC administrators.
- Audit token flows and role assignments regularly.
- Treat the management plane as tier zero infrastructure.
What Consumers and Small Businesses Should Take Away
Smaller organizations may think this story is only for enterprise SOCs, but that would be a mistake. Microsoft says WAC is designed for single servers and clusters as well as larger environments, and many small businesses use it because it is inexpensive, browser-based, and relatively easy to deploy. That means the same architecture concerns apply even when the network is modest.SMBs often have less segmentation
Small and midsize businesses frequently have flatter networks, fewer identity controls, and less formal separation between admin workstations and production systems. In that environment, a compromise of the management plane can be even more damaging because there are fewer layers between the attacker and the data. If WAC is the easiest path to manage servers, it may also become the easiest path to own them. That is not a product flaw alone; it is an architectural habit.SMBs also tend to defer upgrades when a management tool is “working fine.” That is risky in this case because WAC is not just a viewer; it is an execution and orchestration point. Patching it should be treated with the same seriousness as patching a domain controller, backup server, or remote access system. In practical terms, convenience should never be allowed to outrank containment.
Simpler environments still need hard boundaries
Even without complex Azure integrations, WAC’s local deployment model can be abused if permissions are weak. The best defense for small organizations is to keep the management host as isolated as possible, restrict who can log in, and avoid running the admin plane on the same machine as broad-purpose user workloads. Simplicity helps, but only if it comes with discipline.- Keep WAC on dedicated management systems where possible.
- Avoid broad local admin rights.
- Patch on a strict schedule, not when convenient.
- Restrict cloud integration to what is genuinely needed.
- Monitor for unusual identity reuse across cloud and on-prem systems.
Microsoft’s Position and the Patch Reality
Microsoft has already fixed the flaws described by the researchers, and the reporting indicates the vulnerabilities were handled through responsible disclosure. That is the good news: the company appears to have responded, and there is no public sign of active exploitation at the time of writing. The less comforting news is that the fix does not erase the architecture lesson, and it certainly does not remove the possibility that similar mistakes exist elsewhere.Patch cycles are necessary but not sufficient
Patching closes known holes, but hybrid-cloud management problems are often systemic. If a product’s architecture makes it easy for token checks, session trust, or file permissions to drift out of alignment, then the next bug may not look like the last one. That means defenders need more than patch management; they need exposure management, privilege review, and identity-path mapping. The point is to reduce the odds of the next control-plane flaw becoming a cross-boundary event.The fact that the flaws were assigned CVEs and remediated is important, but CVEs are the beginning of a response, not the end. A well-run security program should ask what made the bugs possible, which access assumptions were wrong, and whether the same code patterns exist in other hybrid management products. In other words: fix the bug, then fix the habit.
Responsible disclosure still matters
Cymulate’s handling of the issue, according to its own write-up and the conference reporting, fits the model of responsible disclosure that the industry depends on. The security community benefits when researchers disclose bugs, vendors patch them, and defenders get a chance to close the window before exploitation scales. That process does not make the problem trivial; it makes it survivable. That distinction matters.- Vendor patches reduce immediate risk.
- Responsible disclosure preserves defender time.
- CVEs document the issue, but not the whole lesson.
- The real challenge is preventing recurrence in adjacent systems.
Competitive and Market Implications
There is also a broader market story here. Microsoft is not the only vendor in the hybrid management space, and the report’s emphasis on WAC raises questions about whether comparable tools from other vendors may have similar trust-boundary issues. The Register noted that Cymulate expressed interest in looking at other hybrid cloud management platforms, including Nutanix and VMware. That is sensible, because once one class of product reveals a pattern, it is worth checking the rest of the category for the same shape of weakness.Why rivals should care
If hybrid management tools are increasingly seen as attack surfaces, then vendors will be pushed to prove stronger identity validation, better isolation of local components, and more rigorous cross-environment authorization logic. That could influence product design, sales messaging, and third-party assessments across the sector. No vendor wants its management plane to be seen as the shortest route to a breach.The competitive effect is not limited to security marketing. It may also drive more pressure for clearer separation between management interfaces and privileged execution, stronger attestation of managed resources, and tighter defaults around installation paths and service accounts. In a market where trust is a selling point, security design becomes product differentiation. That is both a technical and commercial reality.
The likely direction of travel
Expect more scrutiny of administrative overlays, especially products that bridge local infrastructure and cloud portals. Security teams are already asking for exposure management across the full hybrid stack, and Microsoft itself has been pushing visibility across on-prem, cloud, and hybrid environments. That means the bar is rising: products will increasingly be judged not only by what they can manage, but by how safely they manage the management plane.- More demands for stronger token validation.
- More scrutiny of admin tooling permissions.
- More vendor pressure to document trust boundaries.
- More interest in cross-workload attack-path mapping.
Strengths and Opportunities
The most constructive way to read the WAC story is not as a panic-inducing incident, but as a reminder that hybrid management can be hardened if organizations treat it as critical infrastructure. Microsoft’s response and the researchers’ disclosure show that the ecosystem can still surface and patch serious flaws before they become active campaigns. The opportunity now is to use this episode to improve how hybrid estates are designed, monitored, and governed.- Better visibility into management-plane dependencies.
- Stronger segmentation between admin hosts and production systems.
- Improved token validation and attestation logic in hybrid tools.
- More disciplined patching for control-plane software.
- Expanded exposure management across cloud and on-prem assets.
- Tighter role engineering for Azure-connected administrative paths.
- Greater security awareness around local installation permissions.
Risks and Concerns
The major concern is that many organizations will patch the specific CVEs and move on without revisiting the structural issue: hybrid management tools concentrate power. That creates a lingering risk that other products, extensions, or adjacent services contain similar trust failures that have not yet been found. In other words, the visible bug may be fixed while the underlying pattern remains.- Overconfidence after patching the named CVEs.
- Unmodeled identity bridges between cloud and on-prem systems.
- Excessive privilege granted to WAC operators and service accounts.
- Inconsistent logging across management-plane components.
- Weak local permissions on admin tooling directories.
- Delayed detection if attackers abuse legitimate tokens.
- Blind spots in organizations that treat hybrid tooling as low risk.
Looking Ahead
The most important next question is whether this becomes a one-off WAC lesson or the start of a broader audit of hybrid management products. If the latter happens, expect more research into token handling, installer permissions, proxy trust models, and cloud-to-on-prem handoff logic. The industry has already learned that identity bugs in cloud services can be catastrophic; the next step is accepting that admin planes deserve the same scrutiny.Microsoft’s own positioning of WAC suggests the product will remain strategically important. It is built for server management anywhere, integrates with Azure, and supports hybrid operations by design. That means the burden is now on defenders to adopt a “trust but verify” posture that is far more skeptical than the convenience story WAC was originally marketed with. Convenience is not the enemy; complacency is.
- Expect more vendor and researcher attention on hybrid management planes.
- Expect security teams to map identity flows more aggressively.
- Expect more discussion of tier zero admin tooling.
- Expect tighter scrutiny of Azure-connected orchestration and Arc integrations.
Source: theregister.com Hybrid clouds have two attack surfaces – so watch both