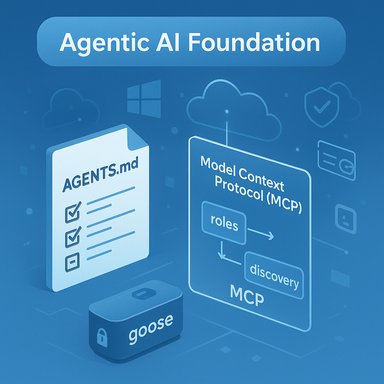
The Linux Foundation, joined by industry heavyweights including Microsoft, OpenAI, Anthropic and Block, today announced the formation of the Agentic AI Foundation (AAIF) — a vendor-neutral steward intended to accelerate open standards, interoperability and governance for agentic AI, and to house three donated cornerstone projects: Anthropic’s Model Context Protocol (MCP), Block’s goose framework, and OpenAI’s AGENTS.md convention.
Agentic AI — systems that plan, act, and orchestrate across tools and services in pursuit of goals on behalf of users — has moved rapidly from research demos to production pilots over the past 12–18 months. That maturation has exposed the same hard infrastructure problem that marked the early web and cloud eras: heterogeneous proprietary implementations make scale, composition, and safety difficult without shared interfaces and governance. The AAIF aims to provide an open, community-driven home where protocols, reference implementations and standards for agentic workflows can evolve under transparent rules. The foundation launches as part of the Linux Foundation’s collaborative-project model and will operate as a directed fund under the Linux Foundation umbrella. Founding organizers and early platinum members list major cloud and AI vendors — a fact that makes AAIF both powerful and politically consequential.
Conclusion
The Agentic AI Foundation establishes a neutral, open staging ground for the next phase of AI: agents that act, coordinate and automate across a distributed web of tools and services. By donating MCP, goose and AGENTS.md to the Linux Foundation, industry leaders have created a fast path toward interoperability and community-driven evolution. The coming months will test whether AAIF can translate those initial strengths into durable neutrality, enforceable security practices, and truly global standards — or whether governance, measurement and fragmentation challenges will blunt its promise. The technical momentum is real; turning that momentum into a safe, open, and equitable agentic web is the work now underway.
Source: Redmondmag.com Linux Foundation Launches Agentic AI Foundation with Microsoft, OpenAI and Anthropic -- Redmondmag.com
 Background
Background
Agentic AI — systems that plan, act, and orchestrate across tools and services in pursuit of goals on behalf of users — has moved rapidly from research demos to production pilots over the past 12–18 months. That maturation has exposed the same hard infrastructure problem that marked the early web and cloud eras: heterogeneous proprietary implementations make scale, composition, and safety difficult without shared interfaces and governance. The AAIF aims to provide an open, community-driven home where protocols, reference implementations and standards for agentic workflows can evolve under transparent rules. The foundation launches as part of the Linux Foundation’s collaborative-project model and will operate as a directed fund under the Linux Foundation umbrella. Founding organizers and early platinum members list major cloud and AI vendors — a fact that makes AAIF both powerful and politically consequential. What is the Agentic AI Foundation (AAIF)?
The AAIF is a governance and stewardship body tailored for the agent era of AI. Its stated mission is to accelerate open-source development of agentic infrastructure, encourage interoperability between agent implementations, and provide neutral governance to prevent single-vendor lock-in. The foundation begins life with three donated projects (MCP, goose, AGENTS.md) and a multi-tier membership structure that spans platinum, gold and silver organizational supporters. Why this matters: open protocols historically lowered the cost of entry, increased security scrutiny, and created ecosystems where independent tooling could flourish. AAIF attempts to replicate that dynamic for agentic AI — standardizing how agents discover tools, share context and follow explicit project guidance so that agents from different vendors can safely cooperate.The three cornerstone projects — what they do and why they were donated
Anthropic’s Model Context Protocol (MCP)
- What it is: MCP is a lightweight, HTTP/JSON-based protocol for exposing tools (capabilities such as file access, databases, search or application actions) to language models and agent runtimes. It defines roles (hosts, clients, servers), transports and a tool discovery model to simplify secure tool invocation across local and remote environments.
- Adoption and scale claims: Anthropic and multiple independent outlets report that MCP now has more than 10,000 public MCP servers, and that the protocol is supported by major products including Claude, ChatGPT, Microsoft Copilot, VS Code and Gemini. These deployment figures are corroborated by both Anthropic’s announcement and independent coverage in trade press. That scale is notable: it means the protocol is already operating at real-world breadth rather than being a lab curiosity.
- Why donate it: Anthropic frames MCP’s donation as a move to ensure the protocol remains vendor-neutral, community-driven and governed openly — a pattern familiar from other foundational projects that grew faster when stewarded by neutral entities.
- Technical and security implications: MCP’s openness reduces integration friction but also introduces new security vectors (prompt injection, tool poisoning, runtime privilege abuse). Microsoft’s Windows team and other platform vendors have already begun to specify host-level controls — e.g., central registries, proxy-mediated communication, tool-level authorization, code-signing and runtime isolation — to mitigate those risks when MCP is used on desktops or in enterprise environments. These are active, platform-level mitigations that signal how critical security-by-default is for MCP deployments.
Block’s goose framework
- What it is: goose is an open-source, local-first agent framework from Block designed to connect language models to deterministic local operations (editing files, running tests, installing dependencies) and remote APIs, while remaining model-agnostic and extensible. It is available as desktop and CLI tooling, and its repository and documentation are public under an Apache-2.0 license.
- Role inside AAIF: goose supplies an opinionated runtime and UX for building productive, secure development agents — essentially a practical reference implementation that demonstrates integration patterns with MCP and multi-model strategies. Donating goose gives the community a concrete, open template for on-machine agent workflows.
- Observed strengths: goose’s local-first architecture, model-agnostic design and developer ergonomics reduce friction for engineering use cases (code migrations, scaffolding, debugging). Its design choices — local logs, session storage, and explicit runtime isolation guidance — are already aligned with security best practices for agentic tooling.
OpenAI’s AGENTS.md
- What it is: AGENTS.md is a lightweight Markdown convention for encoding project-specific guidance that coding agents can read to understand repository policies, test commands, files to avoid, and other operational context. It’s deliberately simple: human-readable, git-native and easy to adopt across repositories.
- Adoption claims and measurement discrepancies: OpenAI reports AGENTS.md has been adopted by more than 60,000 open-source projects and agent frameworks since its release in August 2025. Several outlets independently reported adoption figures in the tens of thousands, though reporting varies (some outlets referenced ~40,000 projects). This difference likely reflects timing, definition of “adoption” (repositories referencing the file vs. actively used in agent tooling), and measurement methodology. The base fact — large, rapid uptake — is corroborated by multiple vendor statements, but exact counts should be viewed as estimates rather than an immutable metric.
- Why this matters: AGENTS.md provides a portable, readable contract between projects and autonomous dev tools. Standardizing this reduces accidental misbehavior, helps with reproducibility and allows organizations to express safety or compliance constraints in a git-native way.
Membership, governance and what “neutral stewardship” actually looks like
The AAIF’s initial membership roster spans the major cloud providers, hyperscalers and many enterprise software vendors. Platinum members announced at launch include Amazon Web Services, Anthropic, Block, Bloomberg, Cloudflare, Google, Microsoft and OpenAI, with multiple gold- and silver-tier members from across the enterprise landscape. That membership breadth is designed to guarantee wide visibility and influence from the start. Under the Linux Foundation’s model, AAIF will apply open-governance norms: public contribution processes, neutral maintainership, and collaborative steering committees. In practice, that means vendor contributions are accepted into foundation repositories and are subject to community review, while foundation officers and technical steering bodies adjudicate spec evolution and release cadence. This structure has guided successful projects such as Kubernetes and PyTorch — but applying it to agentic AI raises unique governance questions (discussed below).Why the AAIF matters for enterprises and Windows users
- Standardized tool plumbing reduces integration cost. Enterprises building agentic use-cases (help desks, RPA-like automation, developer copilot pipelines) gain from predictable ways to expose capabilities and secure them. MCP’s widespread use in tooling promises to lower integration effort and shorten time-to-value for agents that must interact with business systems.
- Platform-level security models are being built proactively. Microsoft’s Windows 11 plans to include a central MCP registry, proxy-mediated enforcement, tool-level consent and runtime isolation — all designed to make MCP safer by default on the desktop. Those choices indicate major platforms will not only adopt protocols but will require secure deployment primitives before enabling agents broadly.
- A neutral foundation can accelerate interoperability. By codifying conventions (AGENTS.md) and hosting reference runtimes (goose), the AAIF creates a shared base for tooling vendors, cloud providers and enterprises to build interoperable agents instead of proprietary stacks. That improves portability and lowers vendor lock-in risk.
Critical analysis — strengths, trade-offs, and risks
Strengths
- Rapid convergence on common interfaces. The speed with which MCP, AGENTS.md and goose moved from internal prototypes to widely used artifacts shows the industry’s appetite for compatibility. Early adoption by major platforms (Copilot, ChatGPT, Gemini, VS Code) multiplies that effect and creates positive network externalities.
- Security-by-default design signals. Major OS and platform vendors are embedding security controls (e.g., registry vetting, code signing, isolation proxies). Those system-level safeguards are essential because agentic workflows can, by design, perform actions that change system state. Platform enforcement will matter a great deal for enterprise trust.
- Open governance with industry buy-in. Housing these projects under the Linux Foundation brings a well-understood governance model and resources for long-term maintenance and cross-vendor collaboration. That lowers the risk that critical infra will be controlled by a single corporate interest.
Trade-offs and risks
- Vendor influence vs. genuine neutrality. The AAIF’s founding membership reads like a who’s-who of the cloud AI industry. While that broad participation has immediate benefits, it raises the governance hazard that large contributors could, informally or procedurally, steer standards to favor existing commercial offerings. Ensuring board and steering committees include independent voices and clear conflict-of-interest policies will be central to credible neutrality.
- Security is a moving target. Protocols that enable agents to act are also high-impact attack surfaces. While Windows and cloud vendors are proposing security controls, the distributed nature of MCP servers — many hosted by third parties — means that attack surface management and supply-chain risk remain significant. Continuous, independent security auditing, standardized compliance tests and registries with provenance controls will be necessary.
- Measurement and transparency of “adoption” metrics. Public adoption counts (10,000 MCP servers, 40k–60k AGENTS.md projects) are useful signals but reflect differing measurement methods and time windows. Projects and vendors should publish clear methodologies for how they count servers, repos or active deployments so the community can interpret growth signals responsibly. Until then, these figures are best treated as directional rather than definitive.
- Fragmentation risk. Even with MCP, AGENTS.md and goose, other competing protocols and conventions (A2A/Agent2Agent projects, agentgateway, AGNTCY-type infrastructure) are also maturing under Linux Foundation projects or independent repos. The agentic landscape could fragment into multiple overlapping standards unless AAIF actively coordinates with other open groups and clarifies interoperability pathways.
Practical implications for Windows admins, developers and enterprise architects
- Windows 11 admins should expect a new MCP service model. Microsoft’s preview and registry plans mean enterprises will soon have the option to whitelist vetted MCP servers, apply tool-level consent policies, and audit agent actions — a substantial change from ad-hoc tooling today. Preparing internal compliance and change-control processes to handle agent permissions will avoid surprises when agentic tooling is enabled.
- Dev teams should consider adopting AGENTS.md. Encoding project policies and test commands in a canonical file helps agents behave predictably when performing code changes or builds. It is a low-friction, git-native change that pays immediate dividends in consistency and safety for agent-driven automation. Given AGENTS.md’s rapid uptake, expect many agent frameworks to read this file by default.
- Platform and security teams must align on registry and vetting processes. If enterprises plan to run internal MCP servers or expose internal tools, they should design signing, immutable tool definitions, and automated security testing into their MCP CI/CD pipelines so their entries can satisfy enterprise-grade registries when those registries become formalized.
Broader strategic context: geopolitics, competition, and standards
Open standards have strategic ramifications. Several commentators note that the U.S. tech stack faces competitive pressure from global open-weight models and Chinese open-source contributions. The AAIF can be read as a defensive and offensive play: defensive in preventing proprietary fragmentation in Western ecosystems, and offensive in encouraging open, interoperable infrastructure that can compete with alternative global stacks. Whether AAIF becomes a genuine global commons or a Western-standardized enclave will depend on governance, inclusivity and outreach to a global developer base.What to watch next (immediate milestones and signals)
- AAIF governance charter and steering committee composition — will independent and academic voices be represented, and how will conflict-of-interest rules be enforced?
- Publication of MCP compliance and interoperability test suites — to make implementations auditable and verifiable.
- Releases and roadmaps for AGENTS.md and goose under AAIF control — watch for formal spec versions, versioning rules and deprecation timelines.
- Microsoft’s registry rollout and policy enforcement timelines for Windows 11 — these will materially affect the desktop’s agent risk profile and adoption path.
- Inter-project coordination (Agent2Agent, Agentgateway, AGNTCY) — either complementary or competing standards will determine whether agentic middleware converges or fragments.
Final assessment
The AAIF launch is a meaningful, real-world step toward an interoperable agentic ecosystem. The combination of a widely adopted protocol (MCP), a practical local-first runtime (goose), and a simple, git-native guidance convention (AGENTS.md) gives the community a powerful toolkit. Platform vendors’ early moves to bake security and registries into operating systems are prudent and necessary. However, the initiative is not risk-free. Concentrated industry sponsorship raises governance questions that must be addressed transparently. Security design and supply-chain controls must keep pace with adoption, and community-confirmable metrics are required to make adoption claims meaningful. Finally, active coordination across parallel open-agent projects will determine whether agentic AI becomes a truly open, composable ecosystem or a set of competing silos. For enterprises and Windows-centric administrators, the practical takeaway is clear: the agentic era is arriving in measurable ways, and preparation — in security policy, registry governance, and repository-level agent guidance — will determine whether that arrival increases productivity or introduces avoidable risk. The AAIF, for better and worse, will be one of the central institutions shaping that future.Conclusion
The Agentic AI Foundation establishes a neutral, open staging ground for the next phase of AI: agents that act, coordinate and automate across a distributed web of tools and services. By donating MCP, goose and AGENTS.md to the Linux Foundation, industry leaders have created a fast path toward interoperability and community-driven evolution. The coming months will test whether AAIF can translate those initial strengths into durable neutrality, enforceable security practices, and truly global standards — or whether governance, measurement and fragmentation challenges will blunt its promise. The technical momentum is real; turning that momentum into a safe, open, and equitable agentic web is the work now underway.
Source: Redmondmag.com Linux Foundation Launches Agentic AI Foundation with Microsoft, OpenAI and Anthropic -- Redmondmag.com