Microsoft’s new “Access Fabric” message reframes a familiar problem—tool sprawl and siloed controls—as an architectural shortcoming rather than a procurement one, and argues that only a truly unified, contextual, connected, and continuous access model can close the seams attackers exploit in the age of AI.
The enterprise security landscape has shifted from perimeter defense to a tapestry of identity, device, application, and network signals. Hybrid work, cloud services, and rapid AI adoption have multiplied identities and access paths, producing operational complexity and blind spots. Microsoft’s Security team frames this as a problem of fragmentation: organizations often run multiple identity products and multiple network access products from different vendors, and that fragmentation erodes consistent policy enforcement and real‑time visibility. Microsoft’s position is that defense must evolve from isolated controls into an Access Fabric: a policy and telemetry fabric that continuously evaluates trust across authentication and network layers, enforcing risk‑based access decisions not just at sign‑in but across every session. This approach leans on Zero Trust principles—“never trust, always verify”—and on continuous access evaluation to tighten access the moment context changes.
An integrated Access Fabric would link the identity token, device posture, and network telemetry. When the endpoint connects to the public Wi‑Fi, that signal updates the policy engine, which can immediately reduce privileges or require re‑authentication. Access is continuously re‑evaluated and adapted based on context rather than allowed to expire on a fixed timer. That continuous re‑evaluation is the core operational win of the model.
Access Fabric is not a silver bullet, but it is an important evolution in how teams organize access security for the AI era: move beyond siloed checks to a living, adaptive fabric that evaluates trust continuously and enforces least‑privilege in real time.
Source: Microsoft Access Fabric: A modern approach to identity and network access | Microsoft Security Blog
 Background / Overview
Background / Overview
The enterprise security landscape has shifted from perimeter defense to a tapestry of identity, device, application, and network signals. Hybrid work, cloud services, and rapid AI adoption have multiplied identities and access paths, producing operational complexity and blind spots. Microsoft’s Security team frames this as a problem of fragmentation: organizations often run multiple identity products and multiple network access products from different vendors, and that fragmentation erodes consistent policy enforcement and real‑time visibility. Microsoft’s position is that defense must evolve from isolated controls into an Access Fabric: a policy and telemetry fabric that continuously evaluates trust across authentication and network layers, enforcing risk‑based access decisions not just at sign‑in but across every session. This approach leans on Zero Trust principles—“never trust, always verify”—and on continuous access evaluation to tighten access the moment context changes. What is an Access Fabric?
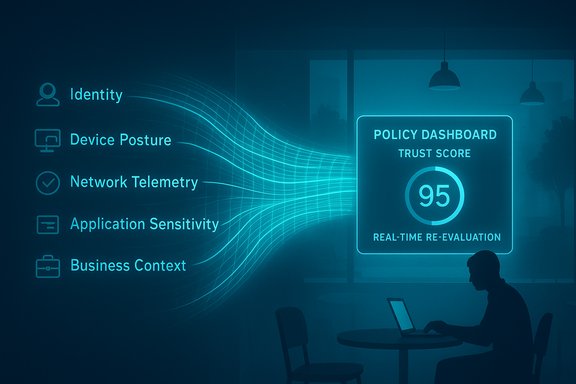
An Access Fabric is not a single product; it is a design pattern and operating model that binds identity, device posture, network telemetry, application sensitivity, and business context into a single decision plane. It emphasizes three core properties:- Contextual: Access decisions consume a rich set of signals—user identity, device health, location and network posture, application sensitivity, and business metadata—so that decisions reflect the moment’s real risk, not a stale token.
- Connected: Controls and telemetry are integrated across identity providers, endpoint management, network enforcement points (SSE, SASE, VPN replacement), and cloud workloads so signals are shared and policies are consistent.
- Continuous: Trust is re‑evaluated during sessions. Policy engines can tighten or revoke access if risk increases (for example when a device moves to an insecure Wi‑Fi). This eliminates “one‑and‑done” authentication lifecycles.
Why Microsoft is pushing this idea now
Two major trends make the Access Fabric pitch timely and persuasive:- AI supercharges offensive capability. Microsoft’s Digital Defense research shows threat actors using AI to craft highly convincing phishing lures and automate intrusion techniques, producing materially higher click‑through and compromise rates. The 2025 Digital Defense Report notes AI‑generated phishing achieved much higher success rates—Microsoft’s telemetry showed a big jump in click rates versus non‑AI attacks.
- Tool sprawl is empirically linked to worse outcomes. Microsoft’s survey work and companion reports find that organizations juggling many identity and network products report more significant breaches; for example, companies using six or more identity and network solutions reported higher breach increases than organizations with fewer, simpler stacks. This strengthens the argument that more point products are not the cure.
The risk AI introduces to access security
AI increases attacker efficiency and quality of lures at scale. Microsoft’s 2025 findings show AI‑assisted phishing achieving higher engagement rates (reported click‑through figures moved from traditional averages to much larger rates in AI‑enabled campaigns), and automated reconnaissance and exploitation scales lateral movement and reconnaissance. The upshot: attackers probe seams quickly and at volume, and human teams alone cannot react fast enough. Because AI enables attackers to chain small, high‑confidence compromises into larger campaigns, a defense that detects and blocks only at discrete boundaries (for example only at authentication time or only inside a corporate VPN) is far more likely to miss the multi‑stage, cross‑layer activity AI empowers. The Access Fabric counters that by making each session and access decision continuously observable and conditionally enforceable.How Access Fabric improves security — a practical scenario
Consider the cafe scenario Microsoft used as a running example: a user signs in on a corporate network, receives a valid token, then moves to a public Wi‑Fi network mid‑session. In a fragmented environment, network telemetry doesn’t reach the identity control plane, so the token remains valid and the user can keep accessing sensitive documents while exposed on an insecure network.An integrated Access Fabric would link the identity token, device posture, and network telemetry. When the endpoint connects to the public Wi‑Fi, that signal updates the policy engine, which can immediately reduce privileges or require re‑authentication. Access is continuously re‑evaluated and adapted based on context rather than allowed to expire on a fixed timer. That continuous re‑evaluation is the core operational win of the model.
Technical anatomy: what components make an Access Fabric practical
A credible Access Fabric needs several building blocks to be effective in real environments:- Unified policy engine and decision plane that can consume signals and push enforcement across identity, endpoint, and network control points.
- Telemetry ingestion and normalization (identity logs, EDR/XDR signals, network telemetry, cloud activity) with sufficient fidelity and low latency. Microsoft cites very large telemetry volumes as one advantage in detection at scale—organizations should treat vendor telemetry claims as directional rather than absolute.
- Lightweight enforcement hooks: APIs, service interceptors, CASB/SSE agents, and network egress controls that can apply step‑up auth, block data egress, or segment traffic in real time.
- Agent and workload identity governance: machine/agent identities require lifecycle controls, short‑lived credentials, and centralized approval flows so autonomous agents can be governed like humans. Microsoft discusses treating agents as first‑class identities in this context.
- Continuous policy evaluation and machine‑aided risk scoring so that the engine can act autonomously on high‑confidence signals to contain risk quickly.
Strengths of the Access Fabric model
- Operational simplicity: One coherent policy plane reduces policy duplication and manual reconciliation across consoles, cutting mean‑time‑to‑detect and mean‑time‑to‑respond.
- Better signal fusion: Identity and network telemetry reinforcing each other improves detection fidelity and reduces false positives when correlations are possible.
- Continuous protection: Real‑time re‑evaluation reduces exposure windows versus static token lifetimes or periodic re‑auth.
- AI‑aware governance: With AI agents and machine identities on the rise, applying the same adaptive controls to non‑human actors reduces a growing blind spot.
Key caveats and risks (what to watch for)
- Vendor dependency and lock‑in. Consolidation into a single vendor fabric can reduce friction but increases strategic dependence. Organizations with multi‑cloud or multi‑vendor requirements must weigh interoperability, exit strategies, and contractual flexibility.
- Telemetry trust and transparency. Vendor claims about signal volume or detection rates are useful but rely on internal measurement methods. Treat vendor metrics as directional and validate against your own telemetry before making architecture decisions based on a specific percentage improvement quoted in marketing.
- Agent and workload sprawl. Treating agents as first‑class identities is necessary, but it also expands the identity surface. Without rigorous lifecycle and governance processes, agent proliferation can create new attack paths.
- Early‑stage features and previews. Many of the tooling and agent‑control features vendors promote are in preview or early access; timelines and semantics can change. Don’t assume GA SLAs or pricing until formally announced.
- Operational maturity requirements. The fabric concept reduces cognitive load for mature teams, but immature SOCs may struggle to tune automated reactions without an initial spike in false positives or mis‑applied step‑up rules. Plan for staged rollouts and policy tuning.
Cross‑referencing the claims — what’s verified and what needs caution
- Microsoft’s assertion that AI has materially increased phishing success is supported by its Digital Defense reporting and corroborated by independent reports in trade press noting higher click‑through rates for AI‑crafted lures. These findings are consistent across multiple observations in 2025 security reporting.
- The survey result that organizations using six or more identity/network products report larger increases in significant breaches comes from Microsoft’s “Secure Employee Access in the Age of AI” research (survey of ~300 security leaders) and is referenced in multiple Microsoft posts and partner commentary. This is a valid vendor survey result but should be contextualized: it’s self‑reported survey data and may reflect correlations rather than causal proof. Independent third‑party studies of tool sprawl and operational risk provide supporting evidence for the general claim that complexity increases risk, but exact percentages depend on methodology. Treat the 79% figure as a vendor‑reported survey outcome rather than an independently audited industry metric.
- The oft‑quoted efficacy of MFA (multi‑factor authentication) in preventing account compromise—Microsoft and subsequent academic analyses show very large reductions in successful account takeover when MFA is used. Multiple independent studies find MFA reduces risk by well over 90%; results vary by MFA type and dataset. The precise blocking percentage depends on how attacks are measured (automated vs targeted attacks), but the direction and magnitude—MFA dramatically reduces account compromise risk—are well supported.
How an Access Fabric maps to existing architectures (Zero Trust, SASE, SSE, CASB)
- Access Fabric is a complement to Zero Trust; it operationalizes Zero Trust by making trust decisions continuous and cross‑layer. Zero Trust is the security philosophy; Access Fabric is an architectural approach to enact it across identity and network domains.
- SASE and SSE provide network and egress controls (routing, inspection, DLP, CASB functions). An Access Fabric expects to integrate these enforcement points with identity telemetry and policy decisions, not replace them. In practice, a Fabric will often orchestrate decisions across SASE/SSE policy enforcement points.
- CASB and DLP are important policy enforcement and data governance elements within the fabric; the Fabric coordinates decisions (for example: require DLP quarantine + step‑up authentication when a sensitive document is exfiltrated).
Concrete implementation steps for Windows and Microsoft‑centric environments
- Inventory and consolidate:
- Map identity providers, conditional access policies, SSO integrations, and network enforcement points.
- Identify duplicate or overlapping controls; target consolidation where it reduces administrative overhead without compromising redundancy.
- Centralize decisioning:
- Deploy or configure a unified policy engine (for many organizations this will be Entra Conditional Access plus an XDR/SIEM that can ingest identity and network telemetry).
- Ensure APIs and connectors link network telemetry, endpoint posture, and app sensitivity into the policy engine.
- Adopt continuous access evaluation:
- Move from long‑lived tokens to short‑lived credentials and step‑up flows; implement session re‑evaluation for high‑risk resources.
- Govern agents and workloads:
- Treat non‑human identities as first‑class objects: catalog them, apply lifecycle controls, and use short‑lived credentials where possible.
- Harden end points and MFA:
- Enforce phishing‑resistant MFA for all privileged and admin access; consider hardware or platform authenticators for the highest assurance. MFA remains one of the highest‑return controls.
- Start small, scale fast:
- Pilot continuous re‑evaluation on a small set of high‑value applications to tune policies and automation playbooks, then expand. Monitor user impact and refine step‑up triggers.
- Validate and measure:
- Define KPIs: mean‑time‑to‑detect, mean‑time‑to‑contain, reduction in privileged sessions without MFA, and false positive rates. Use these to justify broader rollouts.
Operational and governance recommendations
- Maintain a vendor‑neutral integration layer where possible to avoid lock‑in. Use open standards (OIDC, SAML, SCIM, eBPF/NetFlow for telemetry) to preserve mobility.
- Keep humans in the loop for edge cases. Automate low‑risk responses but ensure escalation pathways and audit trails for high‑impact remediations.
- Run tabletop exercises that simulate cross‑layer failures (identity compromise followed by network egress attempts) to validate that the fabric’s automated responses behave as expected.
- Treat telemetry claims conservatively. Validate vendor detection claims against your own telemetry and threat landscape before retiring overlapping controls.
Conclusion: what Access Fabric means for WindowsForum readers
The Access Fabric concept reframes a practical problem: security in 2025 is not solved by piling on more point products; it is solved by fusing signals, operating a single decision plane, and treating access as a continuous, contextual activity. For Windows administrators and security leads, the prescription is familiar—embrace identity as the control plane, enforce phishing‑resistant MFA and short‑lived credentials, treat agents as governed identities, and invest in telemetry integration and policy automation—but the Access Fabric gives those recommendations a single operational name and a roadmap for integration. The model’s strengths—improved detection, faster containment, and smoother user experience—are real. The tradeoffs—vendor dependency risk, governance complexity for agents, and the need for operational maturity—are also real. Organizations should pilot the fabric approach on critical apps, validate vendor claims against internal telemetry, and prioritize governance to prevent agent sprawl and hidden dependency.Access Fabric is not a silver bullet, but it is an important evolution in how teams organize access security for the AI era: move beyond siloed checks to a living, adaptive fabric that evaluates trust continuously and enforces least‑privilege in real time.
Source: Microsoft Access Fabric: A modern approach to identity and network access | Microsoft Security Blog