Microsoft’s April 2026 Windows security updates have created an awkward Remote Desktop moment: a security feature designed to make RDP files safer can itself become hard to read on some multi-monitor systems. The confirmed issue affects the new warning dialog shown when users open Remote Desktop connection files, particularly when monitors use different display scaling values such as 100% and 125%. For Windows 11 users and administrators, the practical message is clear: the protection is important, the bug is real, and the workaround is manageable until Microsoft ships a permanent fix.
Microsoft introduced the new Remote Desktop behavior in the April 2026 security update cycle as part of a broader effort to reduce phishing attacks that abuse Remote Desktop Protocol connection files. These files, commonly ending in
The affected Windows 11 updates include KB5083769 for Windows 11 versions 24H2 and 25H2, and KB5082052 for Windows 11 version 23H2. Microsoft’s April wave also brought similar Remote Desktop changes to other supported Windows versions, including Windows 10 and Windows Server releases. The issue is therefore not just a niche Windows 11 annoyance, even if Windows 11 desktops are where many users are likely to notice it first.
The underlying security work is tied to CVE-2026-26151, a Remote Desktop spoofing vulnerability associated with insufficient user-interface warning around dangerous operations. In practical terms, Microsoft is trying to make users pause before an RDP file quietly starts a session that shares local resources with a remote computer. That makes the warning dialog more than cosmetic; it is part of the protective boundary between a normal support workflow and a malicious remote-access lure.
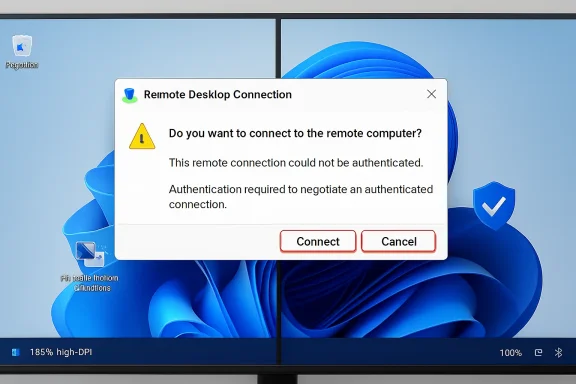
The irony is that the new dialog can display incorrectly on systems with more than one monitor when those displays use different scale settings. Microsoft says the warning window may show overlapping text or partially hidden buttons, making the message difficult to read or interact with. That matters because a security prompt that cannot be clearly read is a weakened security prompt, even when the underlying intent is sound.
This is a shift from trust-by-habit to trust-by-inspection. For years, many users treated RDP files like harmless bookmarks, especially in corporate environments where IT departments distributed them for jump servers, virtual desktops, remote apps, or vendor access. Microsoft is now making the file’s behavior visible at the moment of use.
The protection is most noticeable in two places. First, a one-time educational warning appears the first time a user opens an RDP file after installing the update. Second, an ongoing security dialog appears when RDP files are opened, asking users to review the connection and resource requests before continuing.
Key changes include:
Windows has become far better at mixed-DPI environments over the last decade, but dialog boxes remain a frequent source of trouble when applications or legacy UI components do not respond cleanly to scaling changes. Remote Desktop Connection is a long-lived Windows component, and many of its workflows still carry the design assumptions of earlier desktop eras. When security UI is layered onto that foundation, layout bugs can become immediately visible.
Microsoft describes the symptom as overlapping text or partially hidden buttons in the warning window. That means users may be able to see that a warning exists, but not read all of it or confidently click the intended action. In a security context, that is worse than a normal rendering glitch because it can train people to click through a prompt they do not understand.
The bug is likely to affect users who rely on:
Attackers have increasingly used legitimate file types and built-in Windows capabilities because they blend into normal workflows. An RDP file does not need to look like malware to create risk. If it convinces a user to connect to an attacker-controlled machine while exposing local resources, the damage can happen through trusted Windows functionality.
Microsoft’s security framing reflects this reality. The issue is not simply that RDP exists, or that remote access is dangerous by definition. The issue is that a user may not understand what an RDP file is about to share before the connection starts.
Important local resources can include:
The new warning behavior changes that user experience overnight after patch deployment. Even when everything works, users may see unfamiliar language about publishers, requested settings, and resource sharing. When the dialog is also visually broken, the support desk receives a double hit: confusion about a new security prompt plus complaints that the prompt cannot be read.
The problem is particularly relevant for organizations with standardized multi-monitor workstations. Finance, engineering, healthcare administration, operations centers, and IT support teams often use multiple displays with mixed scaling. These are also environments where RDP access may be business-critical.
Enterprises should treat this as a short-term change-management problem rather than a reason to roll back security updates. The safer path is to document the behavior, standardize display scaling where feasible, and review RDP file signing practices. Removing the security update entirely may solve a dialog problem while reopening a larger phishing exposure.
A sensible enterprise response includes:
The consumer scenario is usually simpler than the enterprise one. A user may have a laptop connected to a second monitor, with Windows scaling the internal panel differently from the external display. They open a saved RDP file, see a warning that appears distorted, and wonder whether the update broke Remote Desktop or whether the file itself is suspicious.
The right answer is nuanced. The warning may be legitimate and newly introduced by Microsoft, while the layout problem may be the confirmed display bug. Users should not assume that every warning is harmless simply because the UI looks broken.
For individual users, the immediate checklist is straightforward:
This workaround is simple, but it is not cost-free. Users choose different scaling values because displays have different physical sizes, resolutions, and viewing distances. Forcing uniform scaling may make one screen too small, too large, or less comfortable for everyday use.
The second workaround is keyboard navigation. If the mouse cannot reliably select a visible button, the user can press Tab to move focus through the dialog and Spacebar to activate the highlighted option. That is useful, but it assumes the user can still understand which option has focus and what action is being selected.
A safe temporary process looks like this:
A signed RDP file does not prove that a connection is safe. It proves that the file was signed by a publisher and has not been modified since signing. Users still need to verify that the publisher makes sense and that the remote address is expected.
However, signing gives enterprises a better trust story. If IT distributes RDP files at scale, signing them helps users distinguish approved connection profiles from random attachments or downloads. It also gives security teams a clearer policy hook for endpoint monitoring and user education.
Organizations should now consider:
Security teams often ask for explicit warnings, disabled defaults, and more user consent. Users and administrators often ask for fewer prompts, stable workflows, and less friction. Both sides are right in their own context.
The Remote Desktop change is defensible because the risk is real. A malicious RDP file can be more dangerous than it appears, particularly when it redirects local drives or authentication-related resources. But a warning dialog must be engineered with the same seriousness as the protocol behavior it is trying to mediate.
Microsoft’s challenge is to ensure that the final fix preserves:
The BitLocker issue is especially relevant because it affects trust in the update process. Even if Microsoft says it applies only to a limited set of systems with particular Group Policy conditions, recovery-key prompts can be alarming in managed environments. When users see both BitLocker prompts and Remote Desktop warning changes in the same month, they may perceive the update as broadly unstable.
That perception matters. Patch management is not just technical deployment; it is organizational confidence. If users and help desks believe a monthly update is risky, they may pressure IT teams to pause or defer security rollouts.
For IT departments, April’s update cycle reinforces the need for:
The April changes may actually benefit Microsoft’s cloud-managed offerings over time. If signed, brokered, centrally governed access flows provide a smoother user experience than unmanaged RDP files, organizations may prefer them. That aligns with Microsoft’s broader direction: reduce unmanaged local shortcuts and move more identity, policy, and access decisions into managed platforms.
Third-party vendors also have an opportunity. Privileged access management providers, password vaults, remote support platforms, and virtual desktop brokers can differentiate by handling RDP signing, policy controls, and user prompts more gracefully. If Microsoft’s native client becomes stricter, the ecosystem around it becomes more important.
The market signal is clear:
The second question is how Microsoft refines the security model after user and administrator feedback. If too many organizations attempt to revert the dialog behavior, Microsoft may need to improve policy controls, signing guidance, or trusted-publisher experiences. The goal should be to preserve the anti-phishing protection while reducing unnecessary friction for well-managed environments.
Near-term items to monitor include:
Microsoft’s Remote Desktop warning bug is not the kind of flaw that should send organizations rushing to uninstall April’s security updates. It is a usability defect in a security feature that points to a larger reality: remote access workflows are now part of the phishing battlefield. Once Microsoft fixes the mixed-scaling display problem, the remaining challenge will be cultural as much as technical—making sure users understand what an RDP file can do before they trust it.
Source: PCWorld Microsoft confirms Remote Desktop bug in April's Windows 11 update
 Background
Background
Microsoft introduced the new Remote Desktop behavior in the April 2026 security update cycle as part of a broader effort to reduce phishing attacks that abuse Remote Desktop Protocol connection files. These files, commonly ending in .rdp, are not merely shortcuts; they can define the remote host, display behavior, authentication options, and local resource redirections that make a remote session feel seamless. That convenience is exactly why administrators use them, and exactly why attackers have become interested in them.The affected Windows 11 updates include KB5083769 for Windows 11 versions 24H2 and 25H2, and KB5082052 for Windows 11 version 23H2. Microsoft’s April wave also brought similar Remote Desktop changes to other supported Windows versions, including Windows 10 and Windows Server releases. The issue is therefore not just a niche Windows 11 annoyance, even if Windows 11 desktops are where many users are likely to notice it first.
The underlying security work is tied to CVE-2026-26151, a Remote Desktop spoofing vulnerability associated with insufficient user-interface warning around dangerous operations. In practical terms, Microsoft is trying to make users pause before an RDP file quietly starts a session that shares local resources with a remote computer. That makes the warning dialog more than cosmetic; it is part of the protective boundary between a normal support workflow and a malicious remote-access lure.
The irony is that the new dialog can display incorrectly on systems with more than one monitor when those displays use different scale settings. Microsoft says the warning window may show overlapping text or partially hidden buttons, making the message difficult to read or interact with. That matters because a security prompt that cannot be clearly read is a weakened security prompt, even when the underlying intent is sound.
What Microsoft Changed in Remote Desktop
A new warning model for RDP files
The April update changes what happens when a user opens an RDP file. Instead of immediately proceeding with a familiar connection flow, Remote Desktop Connection now presents additional warnings that show what the file is asking the client to do. The dialog is meant to expose connection details before the session begins, including requested redirections of local resources.This is a shift from trust-by-habit to trust-by-inspection. For years, many users treated RDP files like harmless bookmarks, especially in corporate environments where IT departments distributed them for jump servers, virtual desktops, remote apps, or vendor access. Microsoft is now making the file’s behavior visible at the moment of use.
The protection is most noticeable in two places. First, a one-time educational warning appears the first time a user opens an RDP file after installing the update. Second, an ongoing security dialog appears when RDP files are opened, asking users to review the connection and resource requests before continuing.
Key changes include:
- A first-launch educational prompt explaining RDP file risks.
- A connection security dialog before the remote session starts.
- Resource redirections disabled by default unless the user enables them.
- Publisher information shown when the RDP file is signed.
- Unknown publisher warnings for unsigned RDP files.
- Explicit user interaction before potentially risky local resources are shared.
The Display Bug: Small UI Fault, Large Usability Impact
Why scaling matters
The confirmed bug appears when a user has multiple monitors with different display scaling settings. A common example is a laptop display at 125% scaling paired with an external monitor at 100%, or a high-DPI display next to a standard office monitor. This is an ordinary modern Windows setup, not an exotic edge case.Windows has become far better at mixed-DPI environments over the last decade, but dialog boxes remain a frequent source of trouble when applications or legacy UI components do not respond cleanly to scaling changes. Remote Desktop Connection is a long-lived Windows component, and many of its workflows still carry the design assumptions of earlier desktop eras. When security UI is layered onto that foundation, layout bugs can become immediately visible.
Microsoft describes the symptom as overlapping text or partially hidden buttons in the warning window. That means users may be able to see that a warning exists, but not read all of it or confidently click the intended action. In a security context, that is worse than a normal rendering glitch because it can train people to click through a prompt they do not understand.
The bug is likely to affect users who rely on:
- Laptop-plus-dock setups with different DPI settings.
- Mixed-resolution monitor arrays in offices and home workstations.
- Ultrawide and high-DPI displays paired with standard monitors.
- Hot desks where monitor profiles change frequently.
- Remote support stations with two or three displays for ticket handling.
- Accessibility scaling where users intentionally enlarge one display.
Why the RDP File Threat Became Urgent
From admin convenience to phishing weapon
RDP files are powerful because they can automate a Remote Desktop session. A legitimate file can point to a known server, set screen behavior, configure gateway options, and request access to local resources such as drives or the clipboard. In the hands of an administrator, that saves time; in the hands of an attacker, it creates a polished lure.Attackers have increasingly used legitimate file types and built-in Windows capabilities because they blend into normal workflows. An RDP file does not need to look like malware to create risk. If it convinces a user to connect to an attacker-controlled machine while exposing local resources, the damage can happen through trusted Windows functionality.
Microsoft’s security framing reflects this reality. The issue is not simply that RDP exists, or that remote access is dangerous by definition. The issue is that a user may not understand what an RDP file is about to share before the connection starts.
Important local resources can include:
- Local drives, which may expose documents, databases, scripts, and cached files.
- Clipboard content, which may include passwords, tokens, or confidential text.
- Smart cards and Windows Hello for Business resources, which can affect authentication.
- WebAuthn and security-key prompts, which can be abused in confusing remote contexts.
- Printers and ports, which may seem mundane but can still leak information.
- Cameras and microphones, which raise obvious privacy concerns.
- USB and Plug and Play devices, which may carry sensitive operational data.
Enterprise Impact: Help Desks, Jump Hosts, and User Training
The admin burden arrives first
Businesses are the most exposed to this bug because businesses use RDP files heavily. Many IT teams distribute saved connection files for help-desk workflows, administrative jump boxes, Remote Desktop Session Host environments, and vendor-managed systems. Those files often exist precisely to simplify repetitive access for users who are not Remote Desktop experts.The new warning behavior changes that user experience overnight after patch deployment. Even when everything works, users may see unfamiliar language about publishers, requested settings, and resource sharing. When the dialog is also visually broken, the support desk receives a double hit: confusion about a new security prompt plus complaints that the prompt cannot be read.
The problem is particularly relevant for organizations with standardized multi-monitor workstations. Finance, engineering, healthcare administration, operations centers, and IT support teams often use multiple displays with mixed scaling. These are also environments where RDP access may be business-critical.
Enterprises should treat this as a short-term change-management problem rather than a reason to roll back security updates. The safer path is to document the behavior, standardize display scaling where feasible, and review RDP file signing practices. Removing the security update entirely may solve a dialog problem while reopening a larger phishing exposure.
A sensible enterprise response includes:
- Notify users that new RDP warnings are expected after April updates.
- Tell users not to ignore unreadable prompts or guess at hidden buttons.
- Standardize monitor scaling on affected workstations where practical.
- Use keyboard navigation when the dialog cannot be clicked reliably.
- Inventory distributed RDP files and remove stale or unnecessary ones.
- Sign internal RDP files where operationally feasible.
- Update help-desk scripts so agents recognize the symptom quickly.
Consumer Impact: Less Common, Still Confusing
Windows 11 Pro users are most likely to notice
Most home users will not encounter this issue often because Remote Desktop hosting is not part of the normal Windows 11 Home experience, and many consumers never open RDP files. Still, Windows 11 Pro users, enthusiasts, students, contractors, and home lab operators often use Remote Desktop to access another PC, a server, a virtual machine, or a work environment. For them, the bug may appear suddenly after patching.The consumer scenario is usually simpler than the enterprise one. A user may have a laptop connected to a second monitor, with Windows scaling the internal panel differently from the external display. They open a saved RDP file, see a warning that appears distorted, and wonder whether the update broke Remote Desktop or whether the file itself is suspicious.
The right answer is nuanced. The warning may be legitimate and newly introduced by Microsoft, while the layout problem may be the confirmed display bug. Users should not assume that every warning is harmless simply because the UI looks broken.
For individual users, the immediate checklist is straightforward:
- Confirm that the RDP file is expected and came from a trusted source.
- Check the remote computer name or address before connecting.
- Avoid enabling local drives unless there is a clear reason.
- Avoid enabling clipboard sharing when connecting to unfamiliar systems.
- Set all monitors to the same scaling value if the dialog is unreadable.
- Use Tab and Spacebar if a button is hidden or hard to click.
The Workarounds: Practical but Imperfect
Uniform scaling is the cleanest temporary fix
Microsoft’s primary workaround is to set the same scale value on all monitors. In Windows 11, that means opening Display settings, selecting each connected display, and choosing the same value under Scale & layout. If every monitor uses 100%, 125%, or another matching value, the warning dialog is more likely to render correctly.This workaround is simple, but it is not cost-free. Users choose different scaling values because displays have different physical sizes, resolutions, and viewing distances. Forcing uniform scaling may make one screen too small, too large, or less comfortable for everyday use.
The second workaround is keyboard navigation. If the mouse cannot reliably select a visible button, the user can press Tab to move focus through the dialog and Spacebar to activate the highlighted option. That is useful, but it assumes the user can still understand which option has focus and what action is being selected.
A safe temporary process looks like this:
- Open Settings from the Start menu.
- Go to System and then Display.
- Select each connected monitor.
- Set the same Scale value for every display.
- Reopen the RDP file and verify the warning dialog is readable.
- If the dialog remains difficult to use, navigate with Tab and select with Spacebar only after confirming the visible text and focus state.
RDP File Signing Becomes More Important
Trust signals are now part of the workflow
One of the quieter consequences of the April update is that RDP file signing becomes more visible. An unsigned file may show an unknown-publisher warning, even if it was created internally by a trusted administrator. That can be annoying, but it also exposes a long-standing weakness in many organizations: internal remote-access shortcuts often circulate without strong provenance.A signed RDP file does not prove that a connection is safe. It proves that the file was signed by a publisher and has not been modified since signing. Users still need to verify that the publisher makes sense and that the remote address is expected.
However, signing gives enterprises a better trust story. If IT distributes RDP files at scale, signing them helps users distinguish approved connection profiles from random attachments or downloads. It also gives security teams a clearer policy hook for endpoint monitoring and user education.
Organizations should now consider:
- Signing approved RDP files with a trusted certificate.
- Replacing old connection files that no longer point to valid systems.
- Publishing RDP files through managed portals rather than email attachments.
- Training users to question unknown publishers instead of normalizing them.
- Auditing redirection settings before distributing files.
- Documenting when local resources should remain disabled.
Security Versus Usability: Microsoft’s Familiar Trade-Off
Better protection can still produce friction
This incident highlights a recurring Windows challenge: Microsoft must harden widely used legacy workflows without breaking habits built over decades. Remote Desktop Connection is not a new cloud app where every screen can be redesigned in isolation. It is a deeply embedded administrative tool used across Windows clients, servers, virtual desktop stacks, and third-party management workflows.Security teams often ask for explicit warnings, disabled defaults, and more user consent. Users and administrators often ask for fewer prompts, stable workflows, and less friction. Both sides are right in their own context.
The Remote Desktop change is defensible because the risk is real. A malicious RDP file can be more dangerous than it appears, particularly when it redirects local drives or authentication-related resources. But a warning dialog must be engineered with the same seriousness as the protocol behavior it is trying to mediate.
Microsoft’s challenge is to ensure that the final fix preserves:
- Clear layout across mixed-DPI displays.
- Reliable keyboard accessibility for all dialog controls.
- Readable warning text in high-contrast and scaled environments.
- Consistent behavior across Windows 10, Windows 11, and Windows Server.
- Manageable enterprise policy controls without encouraging unsafe bypasses.
- Minimal unnecessary prompting for trusted, signed enterprise workflows.
Patch Tuesday Context: One Issue Among Several
April’s update wave was busy
The Remote Desktop warning issue did not arrive in isolation. Microsoft’s April 2026 update cycle also included Secure Boot certificate-related work, BitLocker recovery scenarios for some systems with specific policy configurations, servicing stack updates, and quality fixes. For administrators, the RDP bug is another item on an already crowded post-patch checklist.The BitLocker issue is especially relevant because it affects trust in the update process. Even if Microsoft says it applies only to a limited set of systems with particular Group Policy conditions, recovery-key prompts can be alarming in managed environments. When users see both BitLocker prompts and Remote Desktop warning changes in the same month, they may perceive the update as broadly unstable.
That perception matters. Patch management is not just technical deployment; it is organizational confidence. If users and help desks believe a monthly update is risky, they may pressure IT teams to pause or defer security rollouts.
For IT departments, April’s update cycle reinforces the need for:
- Pilot rings before broad deployment.
- Hardware diversity in test groups, including mixed-DPI monitor setups.
- BitLocker recovery readiness before Secure Boot-related changes.
- RDP workflow testing for signed and unsigned files.
- Clear user communications before visible security prompts appear.
- Fast internal knowledge-base updates when Microsoft adds known issues.
Competitive and Market Implications
Remote access remains a contested space
Remote Desktop is built into Windows, which gives Microsoft an enormous installed base advantage. But enterprises increasingly compare built-in RDP workflows with Azure Virtual Desktop, Windows 365, VPN-backed admin tools, privileged access platforms, browser-based remote access, and third-party remote support products. Any friction in core RDP behavior pushes some organizations to reassess how they deliver remote access.The April changes may actually benefit Microsoft’s cloud-managed offerings over time. If signed, brokered, centrally governed access flows provide a smoother user experience than unmanaged RDP files, organizations may prefer them. That aligns with Microsoft’s broader direction: reduce unmanaged local shortcuts and move more identity, policy, and access decisions into managed platforms.
Third-party vendors also have an opportunity. Privileged access management providers, password vaults, remote support platforms, and virtual desktop brokers can differentiate by handling RDP signing, policy controls, and user prompts more gracefully. If Microsoft’s native client becomes stricter, the ecosystem around it becomes more important.
The market signal is clear:
- Unmanaged RDP files are becoming less acceptable in mature environments.
- Signed connection artifacts will matter more for user trust.
- Privileged access tooling can reduce user-facing confusion.
- Cloud PC and virtual desktop platforms gain a security narrative.
- Legacy workflows will face more scrutiny as phishing techniques evolve.
Strengths and Opportunities
Microsoft’s April Remote Desktop changes are easy to criticize because of the display bug, but the underlying security direction is strong. The update addresses a real attack path, gives users more visibility into RDP file behavior, and creates an opportunity for organizations to clean up remote-access practices that should have been formalized years ago.- Stronger default security because requested redirections are turned off unless approved.
- Better user awareness through first-launch education and recurring connection warnings.
- Improved phishing resistance for attacks that rely on confusing RDP file behavior.
- More pressure to sign RDP files, improving provenance and internal trust signals.
- Clearer administrator workflows for auditing what connection files actually request.
- A useful forcing function for retiring stale, undocumented, or risky RDP shortcuts.
- A chance to modernize remote access through managed portals, privileged access systems, or cloud desktops.
Risks and Concerns
The risks are not limited to the visual bug itself. The bigger concern is that users may become irritated by a security feature before they understand why it exists, which could undermine the very behavior Microsoft wants to encourage. A warning that appears broken can become a warning that users blindly bypass.- Unreadable security prompts may cause users to approve actions without understanding them.
- Mixed-DPI environments are common, especially among professionals who use external monitors.
- Help desks may face avoidable ticket volume if organizations do not communicate the change.
- Unsigned internal RDP files may create warning fatigue even when they are legitimate.
- Temporary workarounds can reduce accessibility if uniform scaling makes one monitor uncomfortable.
- Registry or policy bypasses may weaken protections if deployed too broadly.
- Patch confidence may suffer when the issue is combined with other April update concerns.
What to Watch Next
Microsoft says it will address the Remote Desktop warning display problem in a future Windows update. The most important question is whether that fix arrives as a preview update, an out-of-band correction, or part of a future cumulative release. Organizations with heavy RDP usage should watch release notes closely rather than assume the issue will disappear silently.The second question is how Microsoft refines the security model after user and administrator feedback. If too many organizations attempt to revert the dialog behavior, Microsoft may need to improve policy controls, signing guidance, or trusted-publisher experiences. The goal should be to preserve the anti-phishing protection while reducing unnecessary friction for well-managed environments.
Near-term items to monitor include:
- A cumulative update that fixes mixed-scaling dialog layout.
- Any expansion of the known issue to additional Windows builds.
- Updated Microsoft guidance for RDP file signing and enterprise deployment.
- Vendor updates from privileged access and remote support platforms.
- New phishing campaigns adapting to the changed warning behavior.
Microsoft’s Remote Desktop warning bug is not the kind of flaw that should send organizations rushing to uninstall April’s security updates. It is a usability defect in a security feature that points to a larger reality: remote access workflows are now part of the phishing battlefield. Once Microsoft fixes the mixed-scaling display problem, the remaining challenge will be cultural as much as technical—making sure users understand what an RDP file can do before they trust it.
Source: PCWorld Microsoft confirms Remote Desktop bug in April's Windows 11 update