Arpio’s Azure launch promises to close a glaring gap for enterprises pursuing consistent, cloud-native disaster recovery across multi‑cloud estates, bringing its automated, application‑aware DR platform — long focused on AWS — into Microsoft Azure environments with the same orchestration-first approach the company has promoted for years.
Arpio’s public materials indicate the platform supports cloud‑native replication and cross‑subscription orchestration in Azure, but enterprise buyers should validate which Azure resources are supported natively (PaaS services, managed identities, Blob/ADLS preservation, etc.) in their own environment before assuming complete coverage. The company’s prior AWS competency suggests broad coverage there, and the Azure announcement follows the same playbook, but product documentation should be verified for customer‑specific services.
Analyst and buyer‑guide material shows customers still rely on a mix of native and third‑party services to cover functional gaps: ASR for VM failover, Azure Backup for long‑term retention, and specialist vendors for orchestration or cyber recovery. Arpio’s bid is to be that orchestration layer for cloud‑native apps across AWS and Azure — an attractive proposition if the platform lives up to its coverage claims.
However, the practical value for any specific organization will turn on the granular support matrix for Azure services, the platform’s behavior in complex hybrid scenarios, and transparent cost modeling for replication and testing. Buyers should treat the announcement as a strong reason to test Arpio in a proof‑of‑concept and to insist on documented coverage and runbooks rather than accepting marketing parity claims at face value.
Arpio’s announcement that it now supports Azure completes an important piece of the company’s multi‑cloud story: it positions Arpio as a single orchestration layer for enterprises that can — in principle — validate, test and run application recoveries across AWS and Azure from the same control plane. The promise is compelling and technically aligned with modern best practices; the onus now shifts to rigorous, real‑world validation of service coverage, performance, security and cost before organizations commit to operationalizing Arpio as the foundation of their cloud resilience strategy.
Source: Morningstar https://www.morningstar.com/news/pr...re-delivering-best-in-class-cloud-resilience/
 Background
Background
Why this matters now
Cloud outages, ransomware, accidental deletions and configuration mistakes have repeatedly exposed how brittle many cloud recovery strategies still are. Enterprises are increasingly running mixed estates across AWS and Azure, and they need a single policy surface and automation layer that can validate recovery, execute failover, and meet aggressive RTO/RPO targets without manual runbooks. Arpio’s announcement positions the company as a multi‑cloud DR orchestrator that treats Azure as a first‑class target rather than an afterthought.Short primer: cloud‑native DR vs. legacy backup
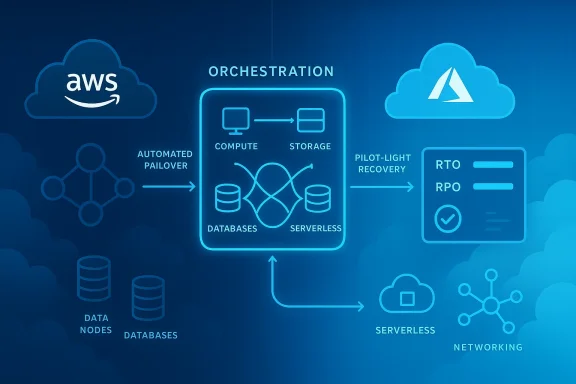
Legacy DR tools and traditional backup products were designed for physical datacenters: they assume static networking, block‑level images and long maintenance windows. Cloud‑native DR instead requires automated dependency mapping, cross‑account/tenant orchestration, and the ability to spin up application stacks — networking, IAM, autoscaling, load balancers, and data — in an isolated recovery environment quickly and non‑disruptively. Arpio’s messaging — “built for the cloud, not retrofitted” — is explicitly framed around these differences.What Arpio announced
- The company has extended its automated disaster recovery capabilities to Microsoft Azure, adding support for full‑application recovery of Azure workloads.
- Arpio emphasizes continuous, automated replication to maintain a low‑cost “pilot light” recovery environment synchronized with production, enabling more aggressive RTO and RPO targets.
- The platform claims comprehensive support for enterprise cloud architectural patterns and the ability to orchestrate non‑disruptive tests and rapid spin‑ups of recovery environments.
- Arpio says Azure support is available immediately to new and existing customers.
What the announcement actually means (technical breakdown)
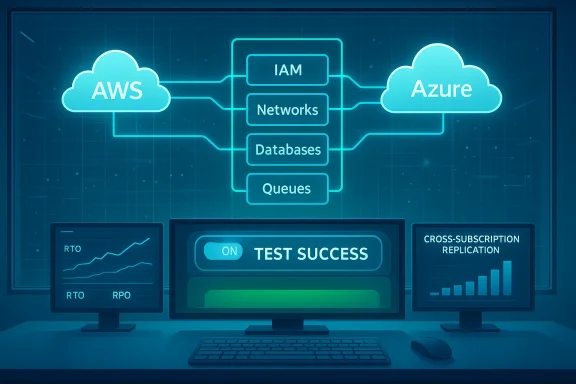
Application‑aware orchestration
Arpio’s core differentiator is orchestration: instead of only protecting volumes or VM images, it claims to map application dependencies and recover the whole application stack. That includes:- Identity and access controls (IAM/Entra ID roles)
- Network topology and security groups
- Platform services (managed databases, message queues, storage)
- Compute and autoscaling policies
Continuous replication and pilot‑light strategy
Arpio promotes continuous automated replication so a minimal recovery environment (pilot light) remains synchronized with production. Pilot‑light reduces standby costs while keeping recovery state current; in practice, this requires rigorous replication coverage for storage, databases, and configuration.Arpio’s public materials indicate the platform supports cloud‑native replication and cross‑subscription orchestration in Azure, but enterprise buyers should validate which Azure resources are supported natively (PaaS services, managed identities, Blob/ADLS preservation, etc.) in their own environment before assuming complete coverage. The company’s prior AWS competency suggests broad coverage there, and the Azure announcement follows the same playbook, but product documentation should be verified for customer‑specific services.
Non‑disruptive testing and validation
A core operational benefit claimed is the ability to run safe, frequent DR tests that spin up recovery environments while production continues uninterrupted. This capability is a real differentiator when compared to manual failover testing that requires long maintenance windows. Arpio’s platform rhetoric and product pages describe test‑mode validation and automated health checks; customers must confirm whether those tests cover database consistency, external integrations, and slice‑level performance characteristics for their critical services.How Arpio’s Azure expansion compares to native and third‑party alternatives
Native Azure options: Azure Site Recovery and Azure Backup
Microsoft provides native services: Azure Site Recovery (ASR) for orchestrated failover and Azure Backup for long‑term retention. ASR is tightly integrated with Azure and handles replication and failover for VMs and some on‑premises scenarios, but it is primarily an infrastructure replication tool and has documented limitations (for example, retention and replication policies designed around VM recovery rather than application‑aware orchestration). Microsoft’s own community guidance highlights ASR’s design focus on recovery points rather than long‑term backup retention, and customers often pair ASR with other backup tools to meet retention and application‑consistency requirements.Established DR vendors: Zerto, Veeam, Rubrik and others
Third‑party vendors have broadened cloud capabilities in recent years, but many originated in virtualization or on‑prem backup paradigms and incrementally added cloud support. Zerto is recognized for continuous data protection and replication but may lack long‑term backup and has been criticized for cost and complexity in cloud contexts. Veeam and Rubrik have strong data protection pedigrees and multi‑cloud strategies, but their platform architectures and customer experiences vary. Buyers should assess whether those platforms offer the same level of application orchestration across AWS and Azure as Arpio claims to provide.What Arpio brings that’s different
Arpio markets itself as a DR orchestrator built specifically for cloud‑native architectures, focused on application‑aware recovery rather than incremental additions to backup stacks. The company’s AWS recognition (AWS Resilience Software Competency) underscores a validated depth of AWS integration, and the Azure launch is positioned as parity for Microsoft workloads. For organizations whose priorities are rapid, tested application recovery across clouds, a single orchestrator can reduce operational complexity and governance drift.Strengths and opportunities
- Application‑focused automation: Orchestrating the full application stack is the right mental model for cloud DR and avoids the “restore a VM and hope the app works” problem. This reduces recovery time and manual error during failover.
- Non‑disruptive testing: Frequent, realistic testing materially improves confidence in DR posture and helps security and compliance teams demonstrate recoverability. Arpio’s promise to spin up test recoveries quickly is operationally valuable.
- Multi‑cloud governance: Managing DR policies consistently across AWS and Azure from a single control plane simplifies compliance, audits, and runbook consolidation — a major win for enterprises with hybrid and multi‑cloud footprints.
- Proven AWS pedigree: Arpio’s AWS competency and track record with native AWS resources provide credibility that the company can manage complex cloud recovery scenarios at scale.
Key risks, caveats, and verification checklist
Arpio’s launch delivers credible capabilities, but buyers must perform due diligence. The following areas deserve specific attention:- Coverage matrix — Verify exactly which Azure services and resource types are supported.
- Does Arpio support recovery for managed PaaS services (Azure SQL Managed Instance, Cosmos DB), platform features (Private Endpoints, Service Endpoints), and advanced networking (ExpressRoute, NAT Gateway)?
- Confirm failback paths and whether Arpio handles hybrid scenarios where part of the app remains on‑prem.
- Data consistency and application semantics — Ask for evidence that replication maintains ACID semantics and application consistency for databases and stateful services during failover. Look for documented test cases and customer references.
- Security and isolation — Understand how the platform isolates recovery accounts and recovers sensitive identities and secrets (Key Vault, managed identities) without elevating risk. Ensure least‑privilege and service‑account hygiene are enforced.
- Cost and FinOps impact — Pilot‑light architectures reduce standby costs, but cross‑region replication, snapshot storage and test spin‑ups carry consumable costs. Demand transparent cost modeling and FinOps reporting during failure and test scenarios.
- Operational dependencies — Confirm that Arpio’s automation doesn’t implicitly create single points of failure (for example, central control plane outages) and that runbooks exist if the orchestrator itself is compromised.
- Vendor lock‑in and portability — Understand what artifacts Arpio leaves behind after failback. Are recovery configurations vendor‑agnostic, or will switching DR platforms require rework?
- Auditability and compliance — Request sample evidence of compliance support (audit trails, tamper‑evident logs) and test results that Arpio can generate for auditors.
Real‑world scenarios: when Arpio’s approach helps — and when it might not
Cases where Arpio’s model is a strong fit
- Enterprises running complex, distributed microservice applications across AWS and Azure that require coordinated recovery of multiple services, identities and networking settings.
- Organizations that need frequent, non‑disruptive DR testing for regulatory or cyber‑insurance requirements.
- Teams aiming to centralize DR governance for multi‑cloud estates to reduce runbook sprawl and audit friction.
Cases where caution is warranted
- Small shops whose recovery needs are limited to long‑term retention (archival) rather than application orchestration may be better served by simpler backup tools.
- Workloads dependent on very specific, narrowly supported Azure platform services should be validated for support before large‑scale rollouts.
- Highly regulated environments that require provider‑managed attestations and specific certifications should verify Arpio’s compliance posture in detail.
Scenario planning and testing — recommended steps for evaluation
- Define critical application boundaries and SLOs (RTO, RPO) for the top 10 most critical applications.
- Run a targeted proof‑of‑concept that includes:
- A full test failover (not just VM boot) that validates networking, identity, and external integrations.
- Consistency checks for databases and queues.
- Cost estimation for pilot‑light replication and test windows.
- Validate security posture:
- Confirm the recovery account model, secret/key handling, and least‑privilege roles.
- Audit the platform’s logging, retention, and tamper‑evidence controls.
- Produce a synthetic incident playbook:
- Simulate region failure, ransomware wipe, and configuration‑accident scenarios.
- Measure recovery times and identify manual steps.
- Review vendor SLAs, runbook portability, and exit strategies.
Broader market context and why multi‑cloud DR matters
Cloud outages are not hypothetical. Network disruptions — from submarine cable cuts to control plane failures — and platform incidents can cascade into large outages that affect customers globally. Community forums and incident threads have discussed Azure latency incidents due to infrastructure and subsea routing problems, which illustrate the real‑world need to design resilience across providers and regions. Using a consistent DR orchestration approach reduces the operational friction of invoking multi‑cloud failover under stress.Analyst and buyer‑guide material shows customers still rely on a mix of native and third‑party services to cover functional gaps: ASR for VM failover, Azure Backup for long‑term retention, and specialist vendors for orchestration or cyber recovery. Arpio’s bid is to be that orchestration layer for cloud‑native apps across AWS and Azure — an attractive proposition if the platform lives up to its coverage claims.
Final assessment: where Arpio’s Azure launch lands
Arpio’s Azure expansion is a logical and strategically sensible next step for a company that built credibility in AWS resilience and now faces customer demand for cross‑cloud uniformity. The core strengths — application‑aware orchestration, continuous replication and frequent, non‑disruptive testing — align tightly with what modern cloud applications need to be recoverable in practice, not just theoretically.However, the practical value for any specific organization will turn on the granular support matrix for Azure services, the platform’s behavior in complex hybrid scenarios, and transparent cost modeling for replication and testing. Buyers should treat the announcement as a strong reason to test Arpio in a proof‑of‑concept and to insist on documented coverage and runbooks rather than accepting marketing parity claims at face value.
Practical checklist for IT leaders considering Arpio for Azure
- Ask for a complete Azure service support matrix and sample test reports.
- Require a joint runbook and cost model for a pilot application, including test‑mode costs.
- Validate database and storage consistency guarantees with real application workloads.
- Inspect the recovery account model and secrets management during failover.
- Confirm evidence of independent validations or customer references for Azure recovery at scale.
- Plan a 30‑ to 90‑day phased POC: discovery, replication enablement, non‑disruptive tests, full failover and measured failback.
Arpio’s announcement that it now supports Azure completes an important piece of the company’s multi‑cloud story: it positions Arpio as a single orchestration layer for enterprises that can — in principle — validate, test and run application recoveries across AWS and Azure from the same control plane. The promise is compelling and technically aligned with modern best practices; the onus now shifts to rigorous, real‑world validation of service coverage, performance, security and cost before organizations commit to operationalizing Arpio as the foundation of their cloud resilience strategy.
Source: Morningstar https://www.morningstar.com/news/pr...re-delivering-best-in-class-cloud-resilience/