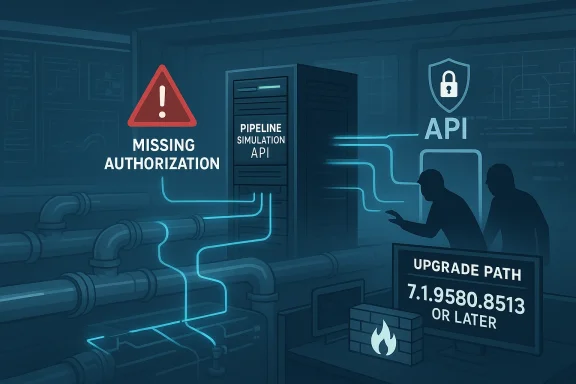
AVEVA’s Pipeline Simulation platform is facing a critical missing-authorization flaw that can let an unauthenticated attacker perform actions reserved for high-privilege users, including Simulator Instructor and Simulator Developer roles. CISA’s new industrial control systems advisory says the issue affects Pipeline Simulation 2025 SP1 build 7.1.9497.6351 and earlier, with a CVSS 3.1 score of 9.1 and a vendor fix already available. In practical terms, this is the kind of bug that can turn a training and simulation environment into a target for unauthorized manipulation, with potential downstream impact on operational readiness and process safety. (aveva.com)
AVEVA Pipeline Simulation sits in a sensitive corner of industrial software: it is not the plant floor itself, but it helps operators, engineers, and instructors rehearse pipeline behavior, validate scenarios, and preserve training records. That makes it both specialized and strategically important. A compromise here does not necessarily stop a compressor station or valve manifold directly, but it can corrupt the decision-support layer that underpins training, competence, and scenario planning.
The advisory describes the flaw as a missing authorization issue, which is a class of weakness that often looks deceptively simple but can have outsized consequences. If a server fails to check whether a caller truly has permission to perform a given action, the system can expose administrative functions to lower-privileged or even unauthenticated users. In an industrial training product, that means tampering with simulation parameters, training configuration, and historical records may become possible.
CISA says AVEVA reported the issue and that there is no known public exploitation at this time. That matters, but only partially. In ICS environments, even a newly disclosed flaw can be dangerous because patching is often slower, validation is heavier, and many deployments are deeply integrated into broader engineering workflows. The absence of known exploitation should be read as breathing room, not reassurance.
The remediation path is straightforward on paper: upgrade to AVEVA Pipeline Simulation 2025 SP1 P01 build 7.1.9580.8513 or later. AVEVA also recommends restricting network access to the Pipeline Simulation Server API and enabling TLS across API communications. Those are classic defense-in-depth steps, but they are especially relevant here because an authorization defect and a transport-level exposure can amplify each other. (aveva.com)
AVEVA has a long history in industrial software, and that history includes repeated security disclosures across its product families. The company’s cyber-security updates page shows a steady cadence of advisories in 2024 and 2025, spanning PI Server, PI Web API, PI Integrator, Edge, Application Server, and other products. The new Pipeline Simulation bulletin fits a familiar pattern: specialized ICS software, a remotely exploitable weakness, and a remediation path that depends on disciplined patch management. (aveva.com)
That broader context matters because industrial vendors often support long-lived systems. Customers do not simply install the latest build because a patch exists; they validate dependencies, regression-test projects, check integrations, and align changes with operations windows. For a simulation platform, there may also be archived scenarios and training records that need careful preservation. Security teams therefore have to balance urgency against operational continuity.
Historically, the ICS sector has treated simulation and training systems as lower-risk than live control systems, but that assumption is getting less defensible. If an attacker can alter training data or scenario parameters, they may not need to directly manipulate a process to cause harm. They can distort operator preparation, influence emergency response drills, or corrupt records used for compliance and competency tracking.
The affected product range is specific but not trivial: AVEVA Pipeline Simulation 2025 SP1 build 7.1.9497.6351 and all prior versions. AVEVA’s bulletin says the fix is available in 2025 SP1 P01 build 7.1.9580.8513 or higher, which gives administrators a concrete upgrade target. That specificity is helpful because industrial customers need exact build numbers, not vague “latest version” guidance. (aveva.com)
CISA rated the issue 9.1 critical, using the vector AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:N. The score tells the story: network reachable, low complexity, no privileges required, and no user interaction needed. Availability impact is marked as none, but confidentiality and integrity are both high, which is exactly the profile you would expect from a flaw aimed at unauthorized control rather than disruption.
The advisory also recommends network-level controls and TLS enforcement. That combination suggests CISA views the server API as part of the attack surface, not merely the application itself. In industrial environments, that is often where real-world exposure lives: API endpoints reachable from engineering workstations, jump hosts, remote maintenance paths, or segmented but still overly broad internal networks. (aveva.com)
A second abuse path is operational deception. If simulation parameters or training records are modified, administrators may later make decisions based on corrupted evidence. That can affect operator qualification, procedural reviews, after-action analysis, and even change management. The attack surface is informational as much as it is technical.
A third concern is trust erosion. Training platforms often serve as the “safe” environment where staff rehearse responses to abnormal situations. If that environment is compromised, the organization may start mistrusting its own records, which can slow remediation, complicate audits, and create uncertainty about what was actually practiced and approved.
Industrial operators use these systems to practice shutdowns, startup procedures, upset response, and abnormal event handling. If an attacker tampers with the simulator, they can distort the organization’s understanding of how a pipeline should behave under stress. That is a form of pre-incident sabotage that can be harder to measure than direct process interruption but just as damaging over time.
There is also a compliance angle. Training records are often retained for audits, certification, and internal governance. If those records are altered, an organization may be unable to prove competence or trace who approved a given configuration. In regulated environments, that can create legal exposure as well as security risk.
CISA’s mitigation guidance is not complicated, but it is important. Restrict network access to the Pipeline Simulation Server API so only trusted client systems can connect, and ensure TLS is enabled for API communications with managed certificates. Those steps will not fix the missing authorization bug, but they can reduce exposure and make interception or tampering harder. (aveva.com)
Security teams should also examine surrounding controls. If the server is reachable from broad internal segments, if certificate handling is weak, or if engineering workstations are over-permissioned, the effective risk grows quickly. In ICS, a vulnerability is rarely isolated; it lands inside an ecosystem of trust assumptions.
For operations teams, the immediate concern is the integrity of the model and the records tied to it. For IT and security teams, the concern is exposure of a network-reachable API with insufficient authorization checks. For management, the concern is whether training attestations, sign-off workflows, or change-control evidence can still be trusted.
There is also a segmentation lesson here. Many industrial environments are segmented in theory but connected in practice through remote access, admin jump servers, engineering VLANs, and vendor support paths. If the Pipeline Simulation API is reachable from any of those paths, the attack surface is larger than a diagram might suggest. That is why CISA’s firewall and trusted-client guidance deserves attention. (aveva.com)
That has competitive implications. Vendors that can demonstrate stronger identity controls, more robust API authorization, and faster patch turnarounds will have an advantage with risk-conscious customers. In a market where industrial buyers increasingly ask for security assurances during procurement, the quality of vulnerability response can influence buying decisions as much as feature sets do.
It also reinforces a broader trend in industrial software: the “edge” is no longer the only place attackers look. Simulation, analytics, reporting, and integration layers are now equally attractive because they hold secrets, workflows, and control logic in a more accessible form. That means vendors of all sizes need to assume that adjacent systems are part of the attack surface.
This advisory also points to a broader shift in industrial security. As more vendors publish issues affecting training, analytics, and engineering support tools, defenders will need to widen their mental model of what “critical infrastructure software” includes. The traditional boundary between control and preparation is getting thinner, and that boundary is now part of the target set.
What to watch next:
Source: CISA AVEVA Pipeline Simulation | CISA
 Overview
Overview
AVEVA Pipeline Simulation sits in a sensitive corner of industrial software: it is not the plant floor itself, but it helps operators, engineers, and instructors rehearse pipeline behavior, validate scenarios, and preserve training records. That makes it both specialized and strategically important. A compromise here does not necessarily stop a compressor station or valve manifold directly, but it can corrupt the decision-support layer that underpins training, competence, and scenario planning.The advisory describes the flaw as a missing authorization issue, which is a class of weakness that often looks deceptively simple but can have outsized consequences. If a server fails to check whether a caller truly has permission to perform a given action, the system can expose administrative functions to lower-privileged or even unauthenticated users. In an industrial training product, that means tampering with simulation parameters, training configuration, and historical records may become possible.
CISA says AVEVA reported the issue and that there is no known public exploitation at this time. That matters, but only partially. In ICS environments, even a newly disclosed flaw can be dangerous because patching is often slower, validation is heavier, and many deployments are deeply integrated into broader engineering workflows. The absence of known exploitation should be read as breathing room, not reassurance.
The remediation path is straightforward on paper: upgrade to AVEVA Pipeline Simulation 2025 SP1 P01 build 7.1.9580.8513 or later. AVEVA also recommends restricting network access to the Pipeline Simulation Server API and enabling TLS across API communications. Those are classic defense-in-depth steps, but they are especially relevant here because an authorization defect and a transport-level exposure can amplify each other. (aveva.com)
Background
Industrial simulation software rarely gets the same public attention as PLC firmware or HMI platforms, yet it plays a crucial role in how organizations prepare for outages, incidents, and operational changes. Pipeline simulation tools let teams model flow, pressure, control logic, and operational responses before making changes in the real world. In sectors like critical manufacturing and energy-adjacent operations, that training layer is not a luxury; it is part of the risk management stack.AVEVA has a long history in industrial software, and that history includes repeated security disclosures across its product families. The company’s cyber-security updates page shows a steady cadence of advisories in 2024 and 2025, spanning PI Server, PI Web API, PI Integrator, Edge, Application Server, and other products. The new Pipeline Simulation bulletin fits a familiar pattern: specialized ICS software, a remotely exploitable weakness, and a remediation path that depends on disciplined patch management. (aveva.com)
That broader context matters because industrial vendors often support long-lived systems. Customers do not simply install the latest build because a patch exists; they validate dependencies, regression-test projects, check integrations, and align changes with operations windows. For a simulation platform, there may also be archived scenarios and training records that need careful preservation. Security teams therefore have to balance urgency against operational continuity.
Historically, the ICS sector has treated simulation and training systems as lower-risk than live control systems, but that assumption is getting less defensible. If an attacker can alter training data or scenario parameters, they may not need to directly manipulate a process to cause harm. They can distort operator preparation, influence emergency response drills, or corrupt records used for compliance and competency tracking.
Why this class of bug matters
Missing authorization flaws are especially dangerous in environments where the software exposes an API or service endpoint. If the application trusts the caller too much, a network-facing server can become a universal control point. That is what makes this advisory more than a routine bug report; it is a reminder that identity checks are security checks.- It can enable privilege escalation without credential theft.
- It can allow unauthorized changes to training records.
- It can undermine the integrity of simulation scenarios.
- It may be abused in a low-noise attack that is harder to spot.
- It is particularly concerning in shared engineering networks.
What CISA and AVEVA disclosed
CISA’s advisory identifies the flaw as CVE-2026-5387, and the vendor impact statement is blunt: exploitation could allow an unauthenticated attacker to carry out operations intended only for Simulator Instructor or Simulator Developer roles. The result is potential modification of simulation parameters, training configuration, and training records. In other words, the issue is not just about viewing data; it is about rewriting the operational narrative inside the simulator.The affected product range is specific but not trivial: AVEVA Pipeline Simulation 2025 SP1 build 7.1.9497.6351 and all prior versions. AVEVA’s bulletin says the fix is available in 2025 SP1 P01 build 7.1.9580.8513 or higher, which gives administrators a concrete upgrade target. That specificity is helpful because industrial customers need exact build numbers, not vague “latest version” guidance. (aveva.com)
CISA rated the issue 9.1 critical, using the vector AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:N. The score tells the story: network reachable, low complexity, no privileges required, and no user interaction needed. Availability impact is marked as none, but confidentiality and integrity are both high, which is exactly the profile you would expect from a flaw aimed at unauthorized control rather than disruption.
The advisory also recommends network-level controls and TLS enforcement. That combination suggests CISA views the server API as part of the attack surface, not merely the application itself. In industrial environments, that is often where real-world exposure lives: API endpoints reachable from engineering workstations, jump hosts, remote maintenance paths, or segmented but still overly broad internal networks. (aveva.com)
What the severity score implies
A 9.1 rating is not just a label; it is a policy signal for defenders. It implies the vulnerability can be exploited with minimal friction and potentially at scale, especially if the service is reachable on a flat or weakly segmented network. That is the sort of issue that should move directly into emergency patch planning.- No credentials appear to be required.
- No local access appears to be required.
- No user click appears to be required.
- Integrity impact is the main concern.
- Confidentiality impact is also significant.
How attackers could abuse the flaw
The most obvious abuse path is straightforward: connect to the exposed service, invoke functions reserved for privileged roles, and alter simulation assets or records. Because the flaw is about authorization rather than code execution, an attacker may not need to crash the system or drop malware to achieve a meaningful result. That makes this kind of vulnerability especially dangerous in environments that monitor for noisy exploitation rather than subtle data tampering.A second abuse path is operational deception. If simulation parameters or training records are modified, administrators may later make decisions based on corrupted evidence. That can affect operator qualification, procedural reviews, after-action analysis, and even change management. The attack surface is informational as much as it is technical.
A third concern is trust erosion. Training platforms often serve as the “safe” environment where staff rehearse responses to abnormal situations. If that environment is compromised, the organization may start mistrusting its own records, which can slow remediation, complicate audits, and create uncertainty about what was actually practiced and approved.
Attack chain possibilities
This vulnerability may also be used as a stepping stone in a broader intrusion. An attacker who gains access to an engineering network through another path could use the flaw to hide traces, manipulate records, or prepare follow-on activity. Even if the simulator is not directly connected to live control, it can still provide intelligence about procedures, assets, and operator workflows.- Reconnaissance against exposed APIs.
- Unauthorized role-function access.
- Modification of training scenarios.
- Alteration of user or session records.
- Use as a staging point for broader ICS mapping.
Why training systems are high-value targets
It is tempting to assume that training systems are less attractive than production control systems, but that assumption is increasingly outdated. Training and simulation environments often contain detailed process logic, real operational workflows, and sometimes near-production data. That makes them rich sources of intelligence for attackers and valuable tools for defenders.Industrial operators use these systems to practice shutdowns, startup procedures, upset response, and abnormal event handling. If an attacker tampers with the simulator, they can distort the organization’s understanding of how a pipeline should behave under stress. That is a form of pre-incident sabotage that can be harder to measure than direct process interruption but just as damaging over time.
There is also a compliance angle. Training records are often retained for audits, certification, and internal governance. If those records are altered, an organization may be unable to prove competence or trace who approved a given configuration. In regulated environments, that can create legal exposure as well as security risk.
Integrity over availability
This advisory is a good example of why integrity attacks can be as serious as classic outages. The CVSS vector shows no availability impact, but in industrial contexts, corrupted data can lead to flawed decisions, and flawed decisions can lead to outages later. That chain is indirect, but it is very real.- Training data can shape operator behavior.
- Scenario corruption can change response expectations.
- Record tampering can undermine audit confidence.
- Configuration changes can distort drill outcomes.
- Deception can delay incident response.
Patch guidance and hardening steps
The primary fix is to move affected systems to 2025 SP1 P01 build 7.1.9580.8513 or higher. In an enterprise environment, that means identifying every instance of AVEVA Pipeline Simulation, confirming the exact build number, and checking whether the software is embedded in a larger engineering workstation image or centrally hosted service. It also means treating the patch as a controlled change, not an isolated installer run.CISA’s mitigation guidance is not complicated, but it is important. Restrict network access to the Pipeline Simulation Server API so only trusted client systems can connect, and ensure TLS is enabled for API communications with managed certificates. Those steps will not fix the missing authorization bug, but they can reduce exposure and make interception or tampering harder. (aveva.com)
Security teams should also examine surrounding controls. If the server is reachable from broad internal segments, if certificate handling is weak, or if engineering workstations are over-permissioned, the effective risk grows quickly. In ICS, a vulnerability is rarely isolated; it lands inside an ecosystem of trust assumptions.
A practical response sequence
- Inventory all AVEVA Pipeline Simulation installations.
- Confirm whether any instance is on build 7.1.9497.6351 or earlier.
- Prioritize upgrade to 7.1.9580.8513 or later.
- Restrict API access to approved client systems only.
- Enable and validate TLS for all communications.
- Review logs for unusual parameter or record changes.
Operational and enterprise impact
The enterprise impact is broader than the simulator alone. In many industrial organizations, simulation platforms are used by engineering, operations, training, and compliance teams simultaneously. A compromise can therefore ripple across multiple business functions, especially if the affected instance serves as a shared service. That shared-service nature is what makes the bug consequential.For operations teams, the immediate concern is the integrity of the model and the records tied to it. For IT and security teams, the concern is exposure of a network-reachable API with insufficient authorization checks. For management, the concern is whether training attestations, sign-off workflows, or change-control evidence can still be trusted.
There is also a segmentation lesson here. Many industrial environments are segmented in theory but connected in practice through remote access, admin jump servers, engineering VLANs, and vendor support paths. If the Pipeline Simulation API is reachable from any of those paths, the attack surface is larger than a diagram might suggest. That is why CISA’s firewall and trusted-client guidance deserves attention. (aveva.com)
Consumer versus enterprise impact
This is not a consumer vulnerability, but the distinction matters because enterprise risk is magnified by scale and persistence. A home user can patch a desktop; an industrial operator may need to coordinate change windows, validate safety consequences, and preserve certifications. The patch burden is heavier, but so is the downstream exposure.- Enterprise systems have shared credentials and workflows.
- Changes may require formal validation.
- Training records may be auditable artifacts.
- Downtime can have costly coordination effects.
- Remote access controls may be inherited or inconsistent.
Industry and competitive implications
AVEVA is not alone in seeing industrial simulation tools become security targets. CISA has repeatedly published advisories for simulation and engineering products across the ICS ecosystem, including prior advisories involving Siemens Tecnomatix Plant Simulation. The pattern suggests that simulation platforms are now firmly in the crosshairs because they straddle operational data, engineering logic, and user trust.That has competitive implications. Vendors that can demonstrate stronger identity controls, more robust API authorization, and faster patch turnarounds will have an advantage with risk-conscious customers. In a market where industrial buyers increasingly ask for security assurances during procurement, the quality of vulnerability response can influence buying decisions as much as feature sets do.
It also reinforces a broader trend in industrial software: the “edge” is no longer the only place attackers look. Simulation, analytics, reporting, and integration layers are now equally attractive because they hold secrets, workflows, and control logic in a more accessible form. That means vendors of all sizes need to assume that adjacent systems are part of the attack surface.
Market signals to watch
The most important competitive signal is whether vendors start shipping tighter authorization defaults, more granular role models, and clearer hardening guidance. Customers increasingly want not just a fix, but a framework for understanding what the fix means in a real deployment. That is especially true when software is used for safety-critical or compliance-sensitive training.- Stronger role-based access controls.
- Better secure-by-default networking.
- Clearer hardening guides.
- Faster security bulletin cadence.
- More transparent patch build numbers.
Strengths and Opportunities
Despite the seriousness of the bug, there are positives in how the issue has been handled. AVEVA has a published fix, CISA has issued a clear advisory, and the recommended mitigations are concrete rather than vague. That combination gives defenders a workable path forward, which is not always the case in ICS disclosures. It also creates an opportunity for organizations to improve their broader simulation-security posture rather than treating this as a one-off patch event.- A specific fixed build is available, reducing ambiguity.
- AVEVA and CISA both provided clear remediation guidance.
- The flaw is well categorized as missing authorization, aiding triage.
- The advisory helps organizations prioritize network segmentation.
- The issue highlights the value of defense in depth.
- The disclosure can drive better asset inventory discipline.
- It may prompt stronger API governance across ICS tools.
Risks and Concerns
The major risk is that organizations will underestimate the impact because the software is “just” a simulator. That mindset would be a mistake. Simulation integrity is operational integrity, especially when training records and configuration histories are used to validate competence and readiness. Another concern is delayed patching due to change-control friction, which is common in industrial settings and can leave vulnerable versions exposed for longer than intended.- Unauthenticated abuse may be possible if the API is exposed.
- Training data could be quietly altered without obvious disruption.
- Corrupted records can create audit and compliance problems.
- Patch delays are likely in carefully managed ICS environments.
- Weak segmentation can turn a local flaw into a network-wide issue.
- Certificate mismanagement could undermine TLS-based protections.
- Attackers may prefer this flaw because it is low-noise and high-impact.
Looking Ahead
The immediate next step is clear: operators should verify their build numbers, identify exposure paths, and move to the fixed release as quickly as operationally possible. After that, the more important question is whether simulation platforms are being treated with the same rigor as production systems. The answer in many organizations is still no, and that gap is exactly where attackers thrive.This advisory also points to a broader shift in industrial security. As more vendors publish issues affecting training, analytics, and engineering support tools, defenders will need to widen their mental model of what “critical infrastructure software” includes. The traditional boundary between control and preparation is getting thinner, and that boundary is now part of the target set.
What to watch next:
- Whether CISA or AVEVA release any follow-up clarifications.
- Whether defenders report exposure in flat internal networks.
- Whether the bug appears in threat actor tooling or scanning.
- Whether additional hardening guidance is published.
- Whether similar authorization issues emerge in related AVEVA products.
Source: CISA AVEVA Pipeline Simulation | CISA