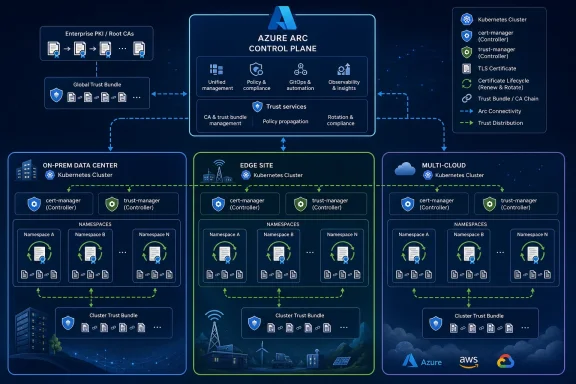
Microsoft put cert-manager support for Azure Arc-enabled Kubernetes into public preview in April 2026, packaging Microsoft-supported cert-manager and trust-manager components as an Arc extension for clusters running on-premises, at the edge, and across other clouds. The move is not glamorous, but it is strategically tidy: Microsoft is trying to turn certificate hygiene from a cluster-by-cluster chore into a control-plane service. For WindowsForum readers who live with hybrid estates, the interesting part is not that Kubernetes can automate TLS certificates. The interesting part is that Microsoft now wants Azure Arc to be the place where that automation is standardized, supported, and monitored.
There are few technologies more capable of ruining a quiet weekend than an expired certificate. The failure mode is embarrassing precisely because it is so avoidable: a perfectly healthy service suddenly looks dead, clients refuse to connect, dashboards light up, and the eventual root cause is a date that nobody owned.
That is the practical problem behind Microsoft’s new public preview of cert-manager for Azure Arc-enabled Kubernetes. The feature automates certificate issuance, renewal, and trust bundle distribution for Kubernetes clusters connected through Azure Arc. It is aimed squarely at the messiest environments: not the clean single-cloud demo cluster, but the on-premises platform next to a plant floor system, the edge cluster in a retail site, the OpenShift estate inherited from one team, and the AKS environment run by another.
The announcement matters because TLS is no longer just a perimeter concern. In Kubernetes, certificates sit under ingress, service-to-service communication, webhooks, internal APIs, observability pipelines, and platform extensions. If those certificates are manually issued and renewed, the security model is only as good as the spreadsheet, calendar reminder, or shell script nobody has touched since the last migration.
Microsoft’s bet is that Azure Arc can make that problem less artisanal. By offering cert-manager and trust-manager as a Microsoft-maintained extension, it is not inventing a new certificate system so much as productizing an already familiar cloud-native pattern for enterprises that want support boundaries and repeatable deployment.
The more interesting version of Arc is not the dashboard story. It is the extension story. Microsoft has steadily used Arc-enabled Kubernetes as a vehicle for pushing Azure-flavored capabilities into clusters that Azure does not actually host.
That includes GitOps, monitoring, policy, security, secret integration, storage, and now certificate lifecycle management. Each extension moves Arc from inventory into operations. The control plane stops being a passive catalog and becomes the method by which Microsoft deploys managed functionality into heterogeneous infrastructure.
Cert-manager support fits that arc perfectly. Kubernetes already has mechanisms for custom resources and controllers. Azure already has an enterprise management plane. The extension model binds the two: Azure deploys and manages a set of controllers inside the cluster, and those controllers operate on Kubernetes-native objects.
That distinction is important. Microsoft is not asking every team to abandon Kubernetes conventions and manage certificates through an Azure-only abstraction. The extension installs cert-manager and trust-manager into the cluster, where they watch resources such as Issuers, ClusterIssuers, Certificates, and Bundles. The workflow remains recognizable to platform engineers, while the packaging and support model become more Microsoft-shaped.
In a single cluster, that is convenient. Across dozens or hundreds of clusters, it becomes governance. Who installed cert-manager? Which version? Who patches it? Which issuers are approved? Are trust bundles consistent across namespaces? Are edge sites using the same CA chain as datacenter clusters? Are application teams copy-pasting YAML from a three-year-old wiki page?
Microsoft’s preview tries to answer those questions with a familiar enterprise move: take the open-source component everyone is already using, package it as a supported distribution, and attach it to the broader platform lifecycle. The value is not that Microsoft discovered certificate automation. The value is that it is offering a supported way to deploy it through Arc.
That may sound like a small distinction until you are the person responsible for production. Open-source cert-manager is widely used, but self-managing it means owning its upgrades, compatibility testing, installation manifests, security posture, and troubleshooting path. In regulated or conservative environments, “we installed the upstream controller ourselves” can be a harder sell than “we deployed the Microsoft-supported Arc extension.”
This is the same enterprise pattern that has played out repeatedly in Kubernetes. Organizations adopt open-source primitives because they solve real problems, then look for vendors to reduce the operational ambiguity. Microsoft’s move does not replace the community project; it wraps it in a procurement-, support-, and governance-friendly shape.
But the inclusion of trust-manager is arguably the more consequential part of Microsoft’s package. Issuing a certificate is only half of TLS. The other half is deciding what the workload should trust.
In hybrid environments, trust is where elegant diagrams go to die. One cluster might trust an internal enterprise CA. Another might use a local cluster CA. A third might need to trust a partner chain or an intermediate authority used by a particular appliance. Teams often distribute CA bundles through ConfigMaps, base images, init containers, Helm charts, or manual namespace setup. Every one of those paths can drift.
Trust-manager exists to distribute trusted CA bundles across namespaces in a controlled way. In Microsoft’s Arc extension, that means the same package handling certificate lifecycle can also propagate trust material to the workloads that need it. That is critical for service-to-service communication, private PKI, and zero-trust-style architectures where internal TLS is no longer optional.
For Windows administrators, this should feel familiar. Enterprise Windows environments have long depended on centralized certificate trust through Active Directory, Group Policy, and enterprise PKI. Kubernetes does not automatically give you that same clean trust distribution model. It gives you primitives. Cert-manager and trust-manager bring those primitives closer to something an enterprise can standardize.
This is where Arc’s hybrid ambition becomes more concrete. Microsoft knows many customers are not running everything in AKS and will not be any time soon. If it can make trust distribution consistent across AKS Edge Essentials, OpenShift, Rancher RKE2, Tanzu, K3s, and other Arc-connected clusters, it gives IT departments a reason to view Arc as more than an asset registry.
The validated distribution list is also worth reading closely. Microsoft says the current preview has been validated on several Arc-enabled Kubernetes distributions, including AKS enabled by Azure Arc, VMware Tanzu TKGm, K3s, Red Hat OpenShift, SUSE Rancher RKE2, and AKS Edge Essentials, with specific version numbers attached. The feature may deploy to other Arc-connected clusters, but validation is not the same thing as theoretical compatibility.
That is the first operational caveat. The second is regional availability. Microsoft lists a broad set of supported Azure regions for the preview, including major US, European, Asian, Middle Eastern, African, and Australian regions, but it is not universal by default. Organizations with strict residency or disconnected requirements will need to check whether their chosen Arc region and cluster topology align.
The third caveat is that certificate automation does not eliminate PKI design. It accelerates whatever design you give it. A bad issuer policy, weak private key handling, sloppy namespace permissions, or unclear ownership model can be automated just as effectively as a good one.
That is the uncomfortable truth about platform automation. It reduces manual error, but it raises the cost of architectural error. Once a certificate pattern is baked into an extension-backed fleet deployment, it becomes easier to replicate and harder to unwind.
A datacenter cluster usually has better connectivity, better staffing, and more mature operational tooling. An edge cluster may sit in a branch office, factory, hospital, retail store, or remote facility where connectivity is intermittent and hands-on maintenance is expensive. If a certificate expires there, the fix may not be a quick Slack message to the platform team. It may require a dispatch, a maintenance window, or a workaround nobody wants to explain later.
Microsoft says the Arc cert-manager extension is designed with edge scenarios in mind, including periods where the cluster is temporarily disconnected from Azure or public networks. That does not mean certificates magically renew forever in isolation. Expiration periods, renewal windows, issuer availability, and local trust design still matter. But it does mean Microsoft is thinking about certificate infrastructure as something that must continue operating when the cloud control plane is not immediately reachable.
That is a pragmatic acknowledgment of how hybrid systems behave. Cloud vendors often talk as if hybrid means a neat line between cloud and on-premises. In reality, hybrid is latency, firewalls, legacy dependencies, overlapping teams, sovereign requirements, unreliable circuits, and maintenance schedules driven by physical operations. Certificate automation in that world has to survive imperfect connectivity.
This is also why the ability to integrate with enterprise PKI is important. Many organizations cannot simply shift internal trust to a public ACME provider or a cloud-only CA. They have existing roots, intermediates, audit controls, hardware-backed key policies, and compliance processes. Microsoft’s extension supports self-signed cluster-local CAs and external enterprise CA certificates, which gives customers a path to automate without abandoning their established PKI hierarchy.
Some customers run OpenShift because they standardized there before AKS matured. Some use Rancher because they wanted distribution flexibility. Some run lightweight K3s at the edge. Some have VMware Tanzu footprints tied to existing virtualization investments. Some will keep workloads on-premises because of latency, sovereignty, licensing, or plain old organizational inertia.
Arc is Microsoft’s answer to that pluralism. It lets Microsoft participate in environments where it does not own the underlying cluster lifecycle. Cert-manager support deepens that participation by touching one of the most sensitive parts of the stack: trust.
This is a subtle competitive move. If Azure Arc becomes the place where organizations manage policy, monitoring, security, secrets, storage, networking, and certificates across Kubernetes distributions, Microsoft does not need every cluster to be AKS to maintain influence. The customer may be running OpenShift or RKE2, but the operational overlay can still be Azure.
That is not necessarily bad for customers. A consistent management plane across messy infrastructure is genuinely valuable. But it also means Arc adoption should be understood as strategic platform adoption, not just a convenience feature. Once certificate management, trust distribution, and compliance workflows are routed through Arc, Azure becomes part of the operational dependency chain for clusters that may otherwise appear cloud-neutral.
Automating issuance and renewal reduces one class of failure. Centralizing trust bundle distribution reduces another. Supporting enterprise PKI gives security teams a way to maintain authority without forcing application teams into slow ticket-driven certificate requests.
But automation can also create false confidence. Cert-manager can renew certificates, but it cannot decide whether a workload should be allowed to request one. Trust-manager can distribute CA bundles, but it cannot guarantee that every trusted CA should be trusted by every namespace. Azure Arc can deploy an extension, but it cannot replace a threat model.
The cert-manager ecosystem also inherits Kubernetes’ usual security concerns. Certificates and private keys often land in Kubernetes Secrets, and those Secrets depend on cluster RBAC, etcd protection, backup handling, and namespace boundaries. If a cluster’s identity and secret storage practices are weak, automating certificate issuance does not fix the underlying exposure.
The correct way to view Microsoft’s extension is as a control that needs surrounding controls. Organizations should pair it with least-privilege RBAC, clear issuer separation, monitored renewal status, alerting on failed certificate requests, defined trust bundle ownership, and secure handling of private keys. The extension gives teams a better mechanism. It does not absolve them from designing the PKI model.
Cert-manager for Arc-enabled Kubernetes is aimed at that translation layer. It gives developers a declarative Kubernetes-native way to request certificates. It gives security teams a way to align issuance with enterprise PKI and trust policy. It gives operations teams a supported extension model instead of a snowflake deployment.
That makes the feature more important than its modest surface area suggests. Certificate lifecycle management is not a headline cloud service, but it is one of those platform capabilities that determines whether higher-level security ambitions are realistic. Mutual TLS, internal service encryption, secure ingress, webhook reliability, private endpoints, and compliance evidence all depend on certificate hygiene.
The timing also fits the industry’s broader direction. Certificate lifetimes are getting shorter, internal service identities are becoming more important, and zero-trust architectures demand more TLS in more places. Manual renewal processes do not scale into that world. Neither do cluster-specific trust hacks.
Microsoft is therefore positioning Arc as a place where Kubernetes security plumbing can be made fleet-aware. That is the key phrase. A single cluster can be managed with patience. A fleet needs policy, packaging, reporting, and repeatability.
Day-two operations will decide whether this preview becomes a serious enterprise feature or just another useful-but-niche Arc add-on. Customers will want to know how updates are handled, how quickly Microsoft tracks upstream cert-manager security releases, how version pinning works, how extension failures surface in Azure, and how troubleshooting splits between Azure support and Kubernetes-native diagnostics.
The monitoring documentation already points administrators toward checking extension status in Azure and inspecting pods in the cert-manager namespace with kubectl. That duality is unavoidable. Arc may provide the management plane, but the controllers still live inside Kubernetes. When something breaks, teams will need both Azure fluency and cluster fluency.
There is also the question of migration. Many organizations already run cert-manager. Microsoft says the Arc extension can serve as a replacement for open-source cert-manager and trust-manager, but replacement is not the same as a no-risk migration. Existing issuers, certificates, webhooks, CRDs, Helm releases, namespace assumptions, and GitOps pipelines all need to be inventoried before a platform team swaps in a supported extension.
That migration path may be one of the most important adoption blockers. Greenfield clusters are easy. Brownfield clusters are where enterprise features prove themselves. Microsoft will need clear guidance for customers who already have cert-manager deeply embedded in their platform stack.
Kubernetes made infrastructure programmable, but it also pushed more security responsibility into YAML, controllers, and cluster-local conventions. A team can spin up an ingress, request a certificate, mount a Secret, and ship an application with remarkable speed. Across an enterprise, that speed can turn into fragmentation.
Certificate handling exposes the fragmentation because it crosses so many boundaries. It involves application teams, platform teams, security teams, network teams, compliance teams, and sometimes desktop or identity teams when internal trust roots are involved. It also crosses environments: cloud, datacenter, branch, edge, lab, and disaster recovery.
Azure Arc gives Microsoft a way to impose some order without forcing full infrastructure consolidation. That is the point. Enterprises rarely get to simplify by replacing everything. They simplify by putting a management layer over what they already have and slowly standardizing the pieces that create the most operational drag.
Cert-manager and trust-manager are exactly those kinds of pieces. Nobody buys a cloud platform because of certificate renewal. But people lose confidence in platforms when certificate renewal fails. Reliability is often built from unglamorous controls that work every time.
The Arc extension is a chance to bring those worlds closer together. If Kubernetes clusters can request and renew certificates through a standardized pattern that chains back to enterprise-approved authorities, the platform becomes easier to audit and defend. If trust bundles can be distributed consistently, developers have fewer reasons to ship custom CA files or bypass verification.
That does not mean every certificate should come from the same root or every namespace should trust the same bundle. In fact, mature environments will likely need separation: different issuers for ingress and internal services, different trust bundles for production and non-production, and different policies for edge clusters that must operate offline.
The important shift is ownership. Instead of each application team inventing its own certificate story, the platform team can define a small set of supported patterns. Instead of security teams approving one-off exceptions, they can review the issuer and trust model. Instead of operations teams chasing expiration dates, they can monitor controllers and renewal status.
This is the difference between automation and platform engineering. Automation removes repetitive work. Platform engineering turns the removal of repetitive work into a supported product for internal users.
That is not trivial. Cert-manager sits close to sensitive workloads. A bug in certificate issuance can break applications. A misconfiguration in trust distribution can create subtle security failures. A failed webhook can block resource creation. A botched upgrade can become a platform incident.
Microsoft’s advantage is that it already has the cloud control plane and support machinery. Its challenge is that Kubernetes operators are skeptical for good reason. They have lived through vendor abstractions that are helpful until something breaks, at which point the abstraction leaks and the customer is told to debug the underlying open-source component anyway.
For this feature to succeed, Microsoft must make the support boundary real. If an Arc extension fails, administrators should not have to reverse-engineer a Helm chart and compare it with upstream manifests. If a supported distribution version changes, the compatibility story should be obvious. If an enterprise PKI integration fails, the logs and documentation should point to the right layer.
Trust management is a sensitive domain in both the technical and institutional sense. Microsoft is asking customers to let Arc help manage who their workloads trust. That requires more than a preview badge and a deployment command.
For organizations already experimenting with Arc-enabled Kubernetes, this preview belongs in a lab or pilot environment, especially where expired certificates or inconsistent trust bundles have caused pain. For organizations with mature cert-manager deployments, the question is whether Microsoft’s extension meaningfully reduces support burden without disrupting existing workflows. For organizations still managing Kubernetes certificates by hand, the preview should be a warning that the industry has moved on.
The feature also gives IT leaders a useful forcing function. If nobody can explain how certificates are issued, renewed, monitored, and trusted across Kubernetes clusters, that is not a Kubernetes problem. That is an operational risk hiding in plain sight.
Source: Petri IT Knowledgebase Azure Arc-Enabled Kubernetes Adds Cert-Manager for TLS Certificate Automation
 Microsoft Is Selling Boring Infrastructure as the New Security Boundary
Microsoft Is Selling Boring Infrastructure as the New Security Boundary
There are few technologies more capable of ruining a quiet weekend than an expired certificate. The failure mode is embarrassing precisely because it is so avoidable: a perfectly healthy service suddenly looks dead, clients refuse to connect, dashboards light up, and the eventual root cause is a date that nobody owned.That is the practical problem behind Microsoft’s new public preview of cert-manager for Azure Arc-enabled Kubernetes. The feature automates certificate issuance, renewal, and trust bundle distribution for Kubernetes clusters connected through Azure Arc. It is aimed squarely at the messiest environments: not the clean single-cloud demo cluster, but the on-premises platform next to a plant floor system, the edge cluster in a retail site, the OpenShift estate inherited from one team, and the AKS environment run by another.
The announcement matters because TLS is no longer just a perimeter concern. In Kubernetes, certificates sit under ingress, service-to-service communication, webhooks, internal APIs, observability pipelines, and platform extensions. If those certificates are manually issued and renewed, the security model is only as good as the spreadsheet, calendar reminder, or shell script nobody has touched since the last migration.
Microsoft’s bet is that Azure Arc can make that problem less artisanal. By offering cert-manager and trust-manager as a Microsoft-maintained extension, it is not inventing a new certificate system so much as productizing an already familiar cloud-native pattern for enterprises that want support boundaries and repeatable deployment.
Arc Keeps Becoming Microsoft’s Hybrid Operating Layer
Azure Arc began life as a way to project non-Azure resources into Azure management. Servers, Kubernetes clusters, databases, and other resources could show up in Azure Resource Manager even when they physically lived somewhere else. That framing was useful, but also abstract. “Single pane of glass” has been promised so many times in enterprise IT that it now lands somewhere between aspiration and punchline.The more interesting version of Arc is not the dashboard story. It is the extension story. Microsoft has steadily used Arc-enabled Kubernetes as a vehicle for pushing Azure-flavored capabilities into clusters that Azure does not actually host.
That includes GitOps, monitoring, policy, security, secret integration, storage, and now certificate lifecycle management. Each extension moves Arc from inventory into operations. The control plane stops being a passive catalog and becomes the method by which Microsoft deploys managed functionality into heterogeneous infrastructure.
Cert-manager support fits that arc perfectly. Kubernetes already has mechanisms for custom resources and controllers. Azure already has an enterprise management plane. The extension model binds the two: Azure deploys and manages a set of controllers inside the cluster, and those controllers operate on Kubernetes-native objects.
That distinction is important. Microsoft is not asking every team to abandon Kubernetes conventions and manage certificates through an Azure-only abstraction. The extension installs cert-manager and trust-manager into the cluster, where they watch resources such as Issuers, ClusterIssuers, Certificates, and Bundles. The workflow remains recognizable to platform engineers, while the packaging and support model become more Microsoft-shaped.
Cert-Manager Was Already the Standard; Microsoft Is Standardizing the Standard
Cert-manager has been one of the more successful examples of Kubernetes plumbing becoming de facto infrastructure. It gives cluster operators a way to request certificates declaratively, store the result in Kubernetes Secrets, and renew certificates before they expire. It can work with ACME providers, internal CAs, self-signed issuers, and other PKI integrations depending on configuration.In a single cluster, that is convenient. Across dozens or hundreds of clusters, it becomes governance. Who installed cert-manager? Which version? Who patches it? Which issuers are approved? Are trust bundles consistent across namespaces? Are edge sites using the same CA chain as datacenter clusters? Are application teams copy-pasting YAML from a three-year-old wiki page?
Microsoft’s preview tries to answer those questions with a familiar enterprise move: take the open-source component everyone is already using, package it as a supported distribution, and attach it to the broader platform lifecycle. The value is not that Microsoft discovered certificate automation. The value is that it is offering a supported way to deploy it through Arc.
That may sound like a small distinction until you are the person responsible for production. Open-source cert-manager is widely used, but self-managing it means owning its upgrades, compatibility testing, installation manifests, security posture, and troubleshooting path. In regulated or conservative environments, “we installed the upstream controller ourselves” can be a harder sell than “we deployed the Microsoft-supported Arc extension.”
This is the same enterprise pattern that has played out repeatedly in Kubernetes. Organizations adopt open-source primitives because they solve real problems, then look for vendors to reduce the operational ambiguity. Microsoft’s move does not replace the community project; it wraps it in a procurement-, support-, and governance-friendly shape.
The Trust-Manager Piece Is the Part Sysadmins Should Not Skip
Most attention naturally goes to certificate issuance and renewal. That is the visible pain. Expired certificates break things loudly, and automatic renewal is an easy benefit to understand.But the inclusion of trust-manager is arguably the more consequential part of Microsoft’s package. Issuing a certificate is only half of TLS. The other half is deciding what the workload should trust.
In hybrid environments, trust is where elegant diagrams go to die. One cluster might trust an internal enterprise CA. Another might use a local cluster CA. A third might need to trust a partner chain or an intermediate authority used by a particular appliance. Teams often distribute CA bundles through ConfigMaps, base images, init containers, Helm charts, or manual namespace setup. Every one of those paths can drift.
Trust-manager exists to distribute trusted CA bundles across namespaces in a controlled way. In Microsoft’s Arc extension, that means the same package handling certificate lifecycle can also propagate trust material to the workloads that need it. That is critical for service-to-service communication, private PKI, and zero-trust-style architectures where internal TLS is no longer optional.
For Windows administrators, this should feel familiar. Enterprise Windows environments have long depended on centralized certificate trust through Active Directory, Group Policy, and enterprise PKI. Kubernetes does not automatically give you that same clean trust distribution model. It gives you primitives. Cert-manager and trust-manager bring those primitives closer to something an enterprise can standardize.
This is where Arc’s hybrid ambition becomes more concrete. Microsoft knows many customers are not running everything in AKS and will not be any time soon. If it can make trust distribution consistent across AKS Edge Essentials, OpenShift, Rancher RKE2, Tanzu, K3s, and other Arc-connected clusters, it gives IT departments a reason to view Arc as more than an asset registry.
Preview Means “Use It,” Not “Forget the Risk Register”
Microsoft’s documentation is clear that cert-manager for Azure Arc-enabled Kubernetes is in public preview. That matters. Preview features can change, may have support limitations, and should not be treated as boring production infrastructure without careful evaluation.The validated distribution list is also worth reading closely. Microsoft says the current preview has been validated on several Arc-enabled Kubernetes distributions, including AKS enabled by Azure Arc, VMware Tanzu TKGm, K3s, Red Hat OpenShift, SUSE Rancher RKE2, and AKS Edge Essentials, with specific version numbers attached. The feature may deploy to other Arc-connected clusters, but validation is not the same thing as theoretical compatibility.
That is the first operational caveat. The second is regional availability. Microsoft lists a broad set of supported Azure regions for the preview, including major US, European, Asian, Middle Eastern, African, and Australian regions, but it is not universal by default. Organizations with strict residency or disconnected requirements will need to check whether their chosen Arc region and cluster topology align.
The third caveat is that certificate automation does not eliminate PKI design. It accelerates whatever design you give it. A bad issuer policy, weak private key handling, sloppy namespace permissions, or unclear ownership model can be automated just as effectively as a good one.
That is the uncomfortable truth about platform automation. It reduces manual error, but it raises the cost of architectural error. Once a certificate pattern is baked into an extension-backed fleet deployment, it becomes easier to replicate and harder to unwind.
Edge Clusters Make Certificate Automation Less Optional
The edge angle in Microsoft’s announcement is not decorative. Edge Kubernetes clusters are exactly where manual certificate operations become least tolerable.A datacenter cluster usually has better connectivity, better staffing, and more mature operational tooling. An edge cluster may sit in a branch office, factory, hospital, retail store, or remote facility where connectivity is intermittent and hands-on maintenance is expensive. If a certificate expires there, the fix may not be a quick Slack message to the platform team. It may require a dispatch, a maintenance window, or a workaround nobody wants to explain later.
Microsoft says the Arc cert-manager extension is designed with edge scenarios in mind, including periods where the cluster is temporarily disconnected from Azure or public networks. That does not mean certificates magically renew forever in isolation. Expiration periods, renewal windows, issuer availability, and local trust design still matter. But it does mean Microsoft is thinking about certificate infrastructure as something that must continue operating when the cloud control plane is not immediately reachable.
That is a pragmatic acknowledgment of how hybrid systems behave. Cloud vendors often talk as if hybrid means a neat line between cloud and on-premises. In reality, hybrid is latency, firewalls, legacy dependencies, overlapping teams, sovereign requirements, unreliable circuits, and maintenance schedules driven by physical operations. Certificate automation in that world has to survive imperfect connectivity.
This is also why the ability to integrate with enterprise PKI is important. Many organizations cannot simply shift internal trust to a public ACME provider or a cloud-only CA. They have existing roots, intermediates, audit controls, hardware-backed key policies, and compliance processes. Microsoft’s extension supports self-signed cluster-local CAs and external enterprise CA certificates, which gives customers a path to automate without abandoning their established PKI hierarchy.
Microsoft’s Kubernetes Strategy Is Becoming Less About AKS Alone
For years, Kubernetes strategy from the major cloud providers had a predictable center of gravity: use our managed Kubernetes service. For Microsoft, that meant AKS. AKS remains central, but Arc shows Microsoft has accepted a broader reality. Enterprise Kubernetes is plural.Some customers run OpenShift because they standardized there before AKS matured. Some use Rancher because they wanted distribution flexibility. Some run lightweight K3s at the edge. Some have VMware Tanzu footprints tied to existing virtualization investments. Some will keep workloads on-premises because of latency, sovereignty, licensing, or plain old organizational inertia.
Arc is Microsoft’s answer to that pluralism. It lets Microsoft participate in environments where it does not own the underlying cluster lifecycle. Cert-manager support deepens that participation by touching one of the most sensitive parts of the stack: trust.
This is a subtle competitive move. If Azure Arc becomes the place where organizations manage policy, monitoring, security, secrets, storage, networking, and certificates across Kubernetes distributions, Microsoft does not need every cluster to be AKS to maintain influence. The customer may be running OpenShift or RKE2, but the operational overlay can still be Azure.
That is not necessarily bad for customers. A consistent management plane across messy infrastructure is genuinely valuable. But it also means Arc adoption should be understood as strategic platform adoption, not just a convenience feature. Once certificate management, trust distribution, and compliance workflows are routed through Arc, Azure becomes part of the operational dependency chain for clusters that may otherwise appear cloud-neutral.
The Security Win Is Real, but It Is Not Automatic
The strongest case for Microsoft’s preview is straightforward: manual certificate management is a security and reliability liability. Expired certificates cause outages. Inconsistent trust stores create brittle services. Untracked private keys increase risk. Ad hoc renewal scripts become institutional folklore.Automating issuance and renewal reduces one class of failure. Centralizing trust bundle distribution reduces another. Supporting enterprise PKI gives security teams a way to maintain authority without forcing application teams into slow ticket-driven certificate requests.
But automation can also create false confidence. Cert-manager can renew certificates, but it cannot decide whether a workload should be allowed to request one. Trust-manager can distribute CA bundles, but it cannot guarantee that every trusted CA should be trusted by every namespace. Azure Arc can deploy an extension, but it cannot replace a threat model.
The cert-manager ecosystem also inherits Kubernetes’ usual security concerns. Certificates and private keys often land in Kubernetes Secrets, and those Secrets depend on cluster RBAC, etcd protection, backup handling, and namespace boundaries. If a cluster’s identity and secret storage practices are weak, automating certificate issuance does not fix the underlying exposure.
The correct way to view Microsoft’s extension is as a control that needs surrounding controls. Organizations should pair it with least-privilege RBAC, clear issuer separation, monitored renewal status, alerting on failed certificate requests, defined trust bundle ownership, and secure handling of private keys. The extension gives teams a better mechanism. It does not absolve them from designing the PKI model.
The Real Audience Is the Platform Team Caught Between Developers and Security
Developers want TLS to be invisible. Security teams want it to be governed. Operations teams want it to stop breaking at 2 a.m. Platform teams are the unlucky translators between those desires.Cert-manager for Arc-enabled Kubernetes is aimed at that translation layer. It gives developers a declarative Kubernetes-native way to request certificates. It gives security teams a way to align issuance with enterprise PKI and trust policy. It gives operations teams a supported extension model instead of a snowflake deployment.
That makes the feature more important than its modest surface area suggests. Certificate lifecycle management is not a headline cloud service, but it is one of those platform capabilities that determines whether higher-level security ambitions are realistic. Mutual TLS, internal service encryption, secure ingress, webhook reliability, private endpoints, and compliance evidence all depend on certificate hygiene.
The timing also fits the industry’s broader direction. Certificate lifetimes are getting shorter, internal service identities are becoming more important, and zero-trust architectures demand more TLS in more places. Manual renewal processes do not scale into that world. Neither do cluster-specific trust hacks.
Microsoft is therefore positioning Arc as a place where Kubernetes security plumbing can be made fleet-aware. That is the key phrase. A single cluster can be managed with patience. A fleet needs policy, packaging, reporting, and repeatability.
The Preview’s Biggest Test Will Be Day-Two Operations
Installing an extension is the easy part. The harder test is what happens six months later.Day-two operations will decide whether this preview becomes a serious enterprise feature or just another useful-but-niche Arc add-on. Customers will want to know how updates are handled, how quickly Microsoft tracks upstream cert-manager security releases, how version pinning works, how extension failures surface in Azure, and how troubleshooting splits between Azure support and Kubernetes-native diagnostics.
The monitoring documentation already points administrators toward checking extension status in Azure and inspecting pods in the cert-manager namespace with kubectl. That duality is unavoidable. Arc may provide the management plane, but the controllers still live inside Kubernetes. When something breaks, teams will need both Azure fluency and cluster fluency.
There is also the question of migration. Many organizations already run cert-manager. Microsoft says the Arc extension can serve as a replacement for open-source cert-manager and trust-manager, but replacement is not the same as a no-risk migration. Existing issuers, certificates, webhooks, CRDs, Helm releases, namespace assumptions, and GitOps pipelines all need to be inventoried before a platform team swaps in a supported extension.
That migration path may be one of the most important adoption blockers. Greenfield clusters are easy. Brownfield clusters are where enterprise features prove themselves. Microsoft will need clear guidance for customers who already have cert-manager deeply embedded in their platform stack.
The Kubernetes Certificate Problem Was Always a Governance Problem
It is tempting to frame this feature as a convenience layer for TLS. That undersells it. The deeper problem is governance.Kubernetes made infrastructure programmable, but it also pushed more security responsibility into YAML, controllers, and cluster-local conventions. A team can spin up an ingress, request a certificate, mount a Secret, and ship an application with remarkable speed. Across an enterprise, that speed can turn into fragmentation.
Certificate handling exposes the fragmentation because it crosses so many boundaries. It involves application teams, platform teams, security teams, network teams, compliance teams, and sometimes desktop or identity teams when internal trust roots are involved. It also crosses environments: cloud, datacenter, branch, edge, lab, and disaster recovery.
Azure Arc gives Microsoft a way to impose some order without forcing full infrastructure consolidation. That is the point. Enterprises rarely get to simplify by replacing everything. They simplify by putting a management layer over what they already have and slowly standardizing the pieces that create the most operational drag.
Cert-manager and trust-manager are exactly those kinds of pieces. Nobody buys a cloud platform because of certificate renewal. But people lose confidence in platforms when certificate renewal fails. Reliability is often built from unglamorous controls that work every time.
The Cert-Manager Extension Turns Arc Into a PKI Conversation
For Windows-heavy organizations, this preview should trigger an internal conversation that goes beyond Kubernetes. Many enterprises already have Microsoft Certificate Services, hardware security modules, documented root hierarchies, device trust policies, and application certificate processes. Kubernetes often arrives as a parallel universe with its own practices.The Arc extension is a chance to bring those worlds closer together. If Kubernetes clusters can request and renew certificates through a standardized pattern that chains back to enterprise-approved authorities, the platform becomes easier to audit and defend. If trust bundles can be distributed consistently, developers have fewer reasons to ship custom CA files or bypass verification.
That does not mean every certificate should come from the same root or every namespace should trust the same bundle. In fact, mature environments will likely need separation: different issuers for ingress and internal services, different trust bundles for production and non-production, and different policies for edge clusters that must operate offline.
The important shift is ownership. Instead of each application team inventing its own certificate story, the platform team can define a small set of supported patterns. Instead of security teams approving one-off exceptions, they can review the issuer and trust model. Instead of operations teams chasing expiration dates, they can monitor controllers and renewal status.
This is the difference between automation and platform engineering. Automation removes repetitive work. Platform engineering turns the removal of repetitive work into a supported product for internal users.
Microsoft Still Has to Earn Trust in the Trust Layer
The phrase “Microsoft-supported distribution” will be attractive to enterprises, but it also raises expectations. If Microsoft puts its name on cert-manager and trust-manager inside Arc, customers will expect timely security updates, clear lifecycle policy, useful diagnostics, and coherent documentation.That is not trivial. Cert-manager sits close to sensitive workloads. A bug in certificate issuance can break applications. A misconfiguration in trust distribution can create subtle security failures. A failed webhook can block resource creation. A botched upgrade can become a platform incident.
Microsoft’s advantage is that it already has the cloud control plane and support machinery. Its challenge is that Kubernetes operators are skeptical for good reason. They have lived through vendor abstractions that are helpful until something breaks, at which point the abstraction leaks and the customer is told to debug the underlying open-source component anyway.
For this feature to succeed, Microsoft must make the support boundary real. If an Arc extension fails, administrators should not have to reverse-engineer a Helm chart and compare it with upstream manifests. If a supported distribution version changes, the compatibility story should be obvious. If an enterprise PKI integration fails, the logs and documentation should point to the right layer.
Trust management is a sensitive domain in both the technical and institutional sense. Microsoft is asking customers to let Arc help manage who their workloads trust. That requires more than a preview badge and a deployment command.
The Practical Read for WindowsForum’s Hybrid Crowd
The immediate lesson is not that every Arc-connected cluster should install the preview tomorrow. The lesson is that Microsoft is steadily moving Arc into the operational core of hybrid Kubernetes, and certificate management is one of the clearest examples yet.For organizations already experimenting with Arc-enabled Kubernetes, this preview belongs in a lab or pilot environment, especially where expired certificates or inconsistent trust bundles have caused pain. For organizations with mature cert-manager deployments, the question is whether Microsoft’s extension meaningfully reduces support burden without disrupting existing workflows. For organizations still managing Kubernetes certificates by hand, the preview should be a warning that the industry has moved on.
The feature also gives IT leaders a useful forcing function. If nobody can explain how certificates are issued, renewed, monitored, and trusted across Kubernetes clusters, that is not a Kubernetes problem. That is an operational risk hiding in plain sight.
- Microsoft’s cert-manager for Azure Arc-enabled Kubernetes is a public preview feature, not a general-availability service, so production adoption should start with controlled pilots.
- The extension packages Microsoft-supported cert-manager and trust-manager components for Arc-connected Kubernetes clusters across hybrid, multicloud, and edge environments.
- The most important operational benefit is not only automated renewal, but consistent trust bundle distribution across namespaces and workloads.
- Existing cert-manager users should treat migration as a platform project because issuers, CRDs, Secrets, GitOps flows, and application assumptions may already depend on the current deployment.
- Edge and intermittently connected clusters are among the strongest use cases because certificate failures in those locations are harder to remediate manually.
- The feature strengthens Azure Arc’s role as Microsoft’s hybrid Kubernetes control plane, even for clusters Microsoft does not host.
Source: Petri IT Knowledgebase Azure Arc-Enabled Kubernetes Adds Cert-Manager for TLS Certificate Automation