Microsoft’s short public attestation — that “Azure Linux includes this open‑source library and is therefore potentially affected” — is accurate for the product Microsoft has inspected, but it is not a technical guarantee that Azure Linux is the only Microsoft product that could contain the vulnerable iperf3 code. Microsoft’s wording is a product‑scoped inventory statement: it confirms Azure Linux was found to ship the implicated component, and Microsoft has committed to publish machine‑readable CSAF/VEX attestations and update CVE mappings as they expand their inventory.
Iperf3 is a widely used open‑source network performance tool that runs a server and a client to measure throughput over TCP, UDP, and SCTP. The flaw tracked as CVE‑2023‑7250 stems from iperf3’s server code: a malicious or malfunctioning client can send less data than the server expects, causing the server to block waiting for the remainder and effectively hang — because a typical iperf3 server services one client at a time, that hang prevents other clients from connecting and produces a denial‑of‑service condition. The vulnerability has been assigned a Medium severity with a CVSS v3.1 base score of 5.3 in public databases. Upstream patches were merged in the project and distributors recommend upgrading to iperf 3.15 or later.
This vulnerability is practical and operational: it is exploitable over the network without privileges, and the mitigation path is straightforward (update the iperf3 package). Because iperf3 is packaged across many Linux distributions, container images, and marketplace appliances, exposure depends on whether a given product image or build actually includes the vulnerable iperf3 package and whether the vulnerable version is present at runtime. Distribution advisories such as Ubuntu, Red Hat, Amazon Linux, Debian and vendor‑specific trackers list iperf3 fixes and recommended package versions.
What the sentence does not say is: “No other Microsoft product contains this library” or “No other Microsoft product could ever be vulnerable.” That negative claim is technically imposssinventory statement. In short: the MSRC text is authoritative for Azure Linux, and deliberately conservative elsewhere. Several independent explainers and advisory analyses published around Microsoft advisories make the same point: the attestation is product‑scoped and phased, not exhaustive.
That approach has clear strengths: customers running Azure Linux have a direct signal to act on; automation tools that consume CSAF/VEX can triage or block vulnerable images; and Microsoft’s public commitment creates accountability. But the phased approach also creates a practical gap: until inventories for other Microsoft artifacts are completed and published, those artifacts remain un‑attested and therefore need independent verification by operators.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Iperf3 is a widely used open‑source network performance tool that runs a server and a client to measure throughput over TCP, UDP, and SCTP. The flaw tracked as CVE‑2023‑7250 stems from iperf3’s server code: a malicious or malfunctioning client can send less data than the server expects, causing the server to block waiting for the remainder and effectively hang — because a typical iperf3 server services one client at a time, that hang prevents other clients from connecting and produces a denial‑of‑service condition. The vulnerability has been assigned a Medium severity with a CVSS v3.1 base score of 5.3 in public databases. Upstream patches were merged in the project and distributors recommend upgrading to iperf 3.15 or later.This vulnerability is practical and operational: it is exploitable over the network without privileges, and the mitigation path is straightforward (update the iperf3 package). Because iperf3 is packaged across many Linux distributions, container images, and marketplace appliances, exposure depends on whether a given product image or build actually includes the vulnerable iperf3 package and whether the vulnerable version is present at runtime. Distribution advisories such as Ubuntu, Red Hat, Amazon Linux, Debian and vendor‑specific trackers list iperf3 fixes and recommended package versions.
What Microsoft’s wording actually says — and what it doesn’t
Microsoft’s Security Response Center (MSRC) entries for third‑party CVEs commonly include an FAQ line of the form you quoted: “Azure Linux includes this open‑source library and is therefore potentially affected by this vulnerability.” That sentence is an attestation — a factual statement about the inventory Microsoft has completed for a named product family. It means Microsoft has inspected the Azure Linux product artifacts and found the third‑party component in question. Microsoft also states that it began publishing machine‑readable CSAF/VEX attestations as part of a phased transparency rollout, and that it will update CVE product mappings if additional Microsoft products are found to ship the component.What the sentence does not say is: “No other Microsoft product contains this library” or “No other Microsoft product could ever be vulnerable.” That negative claim is technically imposssinventory statement. In short: the MSRC text is authoritative for Azure Linux, and deliberately conservative elsewhere. Several independent explainers and advisory analyses published around Microsoft advisories make the same point: the attestation is product‑scoped and phased, not exhaustive.
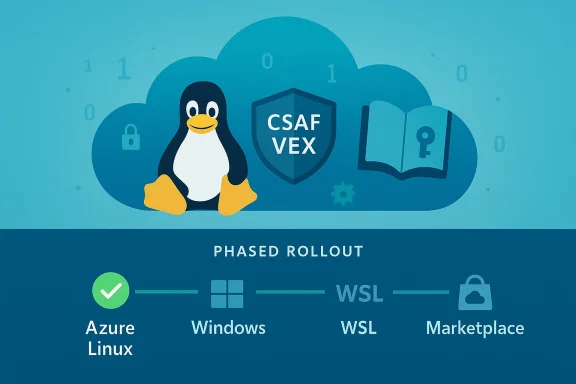
Why Azure Linux appears first in Microsoft’s inventory work
Microsoft’s transparency program for open‑source components and third‑party CVEs was phased. The company began publishing CSAF/VEX machine‑readable attestations with a focus on the Azure Linux distribution (the Microsoft‑maintained Linux distro used in many Azure images), because a single, well‑scoped product family is the practical starting point for deterministic SBOM and VEX output. Publishing a clear attestation for Azure Linux gives customers immediate, actionable guidance: if you run Microsoft’s Azure Linux images, treat that product as confirmed in‑scope and follow Microsoft’s remediation guidance. Microsoft’s public guidance explicitly promises to extend mappings to additional products over time as inventories complete.That approach has clear strengths: customers running Azure Linux have a direct signal to act on; automation tools that consume CSAF/VEX can triage or block vulnerable images; and Microsoft’s public commitment creates accountability. But the phased approach also creates a practical gap: until inventories for other Microsoft artifacts are completed and published, those artifacts remain un‑attested and therefore need independent verification by operators.
Where else the iperf3 component might appear inside Microsoft ecosystems
Even if Microsoft has only attested Azure Linux for a given CVE, there are several plausible places where the same open‑source library could appear elsewhere in Microsoft’s product and service portfolio. Understanding these carriers is key to answering the practical question “am I exposed?”:- WSL (Windows Subsystem for Linux) and the WSL2 kernel: Microsoft publishes and ships Linux kernel images for WSL2. Those kernels are built from upstream code and can include userland packages in vendor images or custom kernels used by customers. Because WSL allows custom kernels and Microsoft publishes kernel sources for WSL, kernel‑space exposure is possible wherever the vulnerable code is present in built artifacts.
- Microsoft‑maintained Azure VM images (including Marketplace): Azure Marketplace contains many VM images and appliances — both Microsoft‑published and third‑party offers — that package operating systems and tools such as iperf3. Third‑party Marketplace images explicitly offering iperf3 demonstrate that iperf3 is commonly included in VM appliance stacks on Azure. If a Marketplace image is maintained by Microsoft or rebuilt by Microsoft tooling, it may inherit the same vulnerable package unless upgraded.
- Containers and SDK/runtime images: Microsoft publishes container images and SDK/runtime images (for example, language runtime images and base images) used extensively across Azure App Services, Functions, and CI/CD pipelines. If those images include an iperf3 package or a base distribution that did not receive the fix, the vulnerability might exist in containerized workloads.
- Managed services with embedded Linux stacks: certain managed Azure services or appliances use Linux‑based images under the hood (for example, telemetry agents, VM host agents, or specialized service kernels). Those artifacts can include upstream packages and must be considered in scope until inventoryed.
- Third‑party software distributed through Microsoft channels: even when Microsoft does not ship iperf3 itself, partners and ISVs distribute prebuilt images and appliances through the Azure Marketplace that do include iperf3. Those images run on Azure infrastructure and could be exposed independently of Microsoft’s own product mappings.
Practical steps for defenders: verify whether any Microsoft product you run contains vulnerable iperf3
If you must determine exposure quickly, follow a focused verification checklist. These steps combine host‑level checks, image inspection, and vendor attestation consumption.- Inventory first
- List all Microsoft‑supplied artifacts in your estate: Azure Linux images, WSL instances, Azure Marketplace VM images, Microsoft container images (Acr, MCR), and any managed‑service agents deployed by Microsoft.
- Use your asset management or cloud inventory tools to enumerate images by name and tag.
- Check package lists inside images and running hosts
- For Debian/Ubuntu derivatives: run dpkg -l | grep iperf3 or apt list --installed iperf3.
- For RPM‑based images: run rpm -q iperf3 or dnf list installed iperf3.
- For containers: run docker run --rm <image> sh -c 'apk list --installed | grep iperf3' (adjust for distro), or inspect layers with container scanning tools.
- Verify package versions
- Confirm the installed iperf3 version. Upstream fixes for CVE‑2023‑7250 were merged in iperf 3.15; any earlier version is potentially vulnerable until the package is rebuilt and updated by the distributor. Where vendors backport security fixes into older package versions, consult the vendor advisory for the fixed package identifier.
- Consume MSRC / CSAF / VEX output
- Pull Microsoft’s CSAF/VEX attestations when available for the products you use. Microsoft pledged to publish machine‑readable attestations beginning in October 2025 and to update CVE mappings as inventories expand; these files can automate triage of attested product SKUs. However, do not treat absent attestations as proof of absence — treat them as “no data yet.”
- Apply mitigations where immediate updates are impractical
- If you cannot update iperf3 immediately:
- Disable or remove iperf3 on servers where it is not required.
- Restrict iperf3 server endpoints to management networks and apply firewall rules to limit client access.
- Run iperf3 under an unprivileged account (avoid running the server as root).
- Monitor iperf3 endpoints for unusual or long‑running sessions and implement connection timeouts at network or process supervision layers.
- Use automated binary and SBOM scanning
- Leverage image scanning tools and SBOM consumers to detect iperf3 presence across image registries, VM images, and containers. Many vulnerability scanners ingest CSAF/VEX and package indices to map CVEs to packages automatically.
Recommended remediation and mitigations
- Patch: Update iperf3 to a fixed distribution package (iperf 3.15 or the vendor’s patched build) wherever it is installed. Distribution advisories (Ubuntu, Red Hat, Amazon Linux, Debian) list fixed package versions — apply those updates via your normal patch management pipelines.
- Minimize attack surface: Stop and disable iperf3 servers when not required. Enforce network ACLs so the iperf3 server is not exposed to untrusted networks.
- Avoid privileged runs: Configure iperf3 to run as an unprivileged service account. This doesn’t eliminate the hang, but reduces collateral damage if combined with other weaknesses.
- Add operational controls: Use process supervisors with restart limits and process lifetime controls to ensure hung iperf3 instances do not block orchestration or service health checks indefinitely.
- Monitor and alert: Add instrumentation and alerts for long‑running iperf sessions or blocked processes, and correlate network connection states with process health.
Strengths and weak spots of Microsoft’s current disclosure approach
Strengths- Actionable attestation for Azure Linux. By explicitly stating that Azure Linux contains the implicated component, Microsoft gives Azure‑Linux users a clear actionable starting poinautomated triage systems that can immediately mark those images as in‑scope.
- Machine‑readable VEX/CSAF commitment. Publishing CSAF/VEX attestations enables downstream automation and machine processing of vulnerability and exploitation metadata, which scales better than narrative advisories.
- Clear promise to update mappings. Microsoft’s public pledge to update CVE records as product mappings expand reduces ambiguity for customers and creates an auditable trail.
- Phased rollout leaves interim gaps. Until inventories for every Microsoft artifact are finished and published, customers must assume that un‑attested components could still exist in other images, containers, or services. The absence of an attestation is not evidence of absence — and attackers understand this gap. Several community analysts have warned that product‑only attestations can be misread as exclusivity.
- Supply‑chain complexity increases audit burden. Microsoft hosts many distribution channels (Azure Marketplace, container registries, SDK images, managed services). Each requires separate inventory checks and may be maintained under different update cadences.
- Third‑party Marketplace images complicate responsibility. Many iPerf3‑containing images on Azure Marketplace are published by third parties; they may not be updated on Microsoft’s cadence, creating islands of exposure even in an otherwise patched estate.
A short, defensible answer to the original question
No — Azure Linux is not necessarily the only Microsoft product that could include the iperf3 library and therefore be potentially affected by CVE‑2023‑7250. What Microsoft’s advisory does say is that Azure Linux has been checked and found to include the implicated component, and Microsoft will expand VEX/CSAF product mappings if additional Microsoft products are found to ship the same library. Treat the MSRC mapping as an authoritative signal for Azure Linux, and as a starting point for broader, independent verification across any Microsoft images, WSL kernels, containers, Marketplace appliances, or managed agents that you run.How to communicate this to your stakeholders (recommended messaging)
- For Azure Linux hosts: Act now. The MSRC attestation means Azure Linux images have been inventory‑checked; prioritize updating iperf3 packages in those images or remove the package where unnecessary. Provide the package version and update ticket IDs to your ops team and schedule patch windows.
- For other Microsoft artifacts (WSL instances, Marketplace images, container images, managed services): Verify, don’t assume. Run the package checks and image scans described above. If iperf3 is present, treat the host as vulnerable until you confirm the installed package includes the upstream fix or the vendor has released a patched package.
- For auditors and risk owners: Document your process. Note that Microsoft’s CSAF/VEX rollout is a positive transparency step but remains phased; maintain evidence of host‑level checks and image scans to support your at--
Closing analysis: what to watch next
- Watch Microsoft’s CSAF/VEX feed for updates to the CVE mapping. Microsoft has publicly committed to updating product mappings as inventories expand; when that happens for products you use, it will materially reduce your manual verification burden.
- Monitor distribution advisories (Ubuntu, Red Hat, Debian, Amazon Linux) for the fixed package versions and backport notes. These vendor advisories also indicate whether a fix is a version upgrade or a backport into an existing package version — important for change control.
- Revisit Marketplace and third‑party images you consume: ensure your procurement and image‑approval pipelines include a vulnerability scan and a policy to replace or remediate images with unpatched iperf3 instances.
- Finally, treat MSRC product attestations as highly useful but not sufficient evidence. Use them to prioritize response, but keep doing the artifact‑level verification that confirms whether any particular host or image actually carries the vulnerable iperf3 package. Several public explainers and community analyses emphasize this distinction between attested products and the remaining, un‑attested surface area that still needs independent verification.
Source: MSRC Security Update Guide - Microsoft Security Response Center