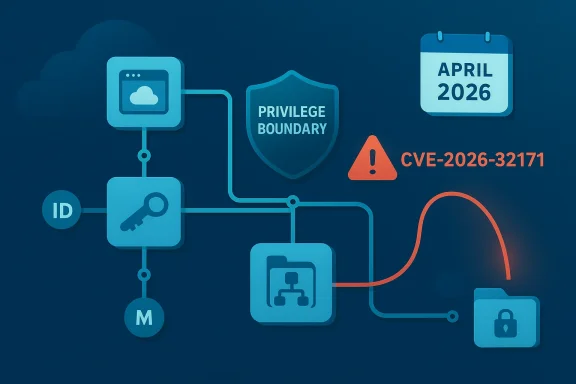
Microsoft’s April 2026 security update includes CVE-2026-32171, an Azure Logic Apps Elevation of Privilege vulnerability that Microsoft rates as Important. The entry is notable not just because it affects a managed cloud service, but because it sits in a product line where identity, connectors, and automation all intersect. Microsoft’s own advisory framing emphasizes the confidence dimension: the more certain the existence and technical shape of a vulnerability, the higher the urgency for defenders, and this case now appears to have enough corroboration to justify immediate attention. (bleepingcomputer.com)
Azure Logic Apps is Microsoft’s workflow automation platform for building integrations between services, APIs, and data sources without extensive custom code. It is available in both Consumption and Standard models, with different runtime and hosting characteristics, and it relies heavily on connectors that often authenticate through Microsoft Entra ID, managed identities, or service credentials. That architecture gives the platform enormous flexibility, but it also creates a security surface where a seemingly small authorization flaw can have outsized impact.
The specific CVE is described as an elevation of privilege issue, which in cloud services is usually more serious than the label first suggests. An EoP in Logic Apps can mean a low-privilege or otherwise unauthorized actor could cross a boundary that should have been enforced by the service, workflow runtime, or connector layer. In practice, that can turn a workflow platform from an integration engine into an access amplifier, especially when a workflow has been granted broad rights over Azure resources. (app.opencve.io)
Microsoft has a long history of shipping fixes for Azure-hosted services where the real issue is not just code correctness, but authorization correctness. Prior MSRC writeups on Azure Automation, Azure Machine Learning, and other cloud offerings show the same pattern: attackers often do not need to “break” encryption or defeat the whole service. They just need one path where the service trusts a request, token, callback, or connector too much, and then the attacker rides the platform’s own privileges to a higher level.
That context matters here because Logic Apps is built to do things on behalf of users and organizations. It can read data, trigger downstream automations, call third-party endpoints, and act through identity bindings that may be far more powerful than the user interface suggests. A weakness in that trust chain is not merely a bug; it is potentially a shortcut around the cloud control plane.
The timing is also important. The advisory is part of the April 2026 Patch Tuesday cycle, a release that BleepingComputer reported as covering 167 flaws overall, including two zero-days in other Microsoft products. Even though CVE-2026-32171 is not the headline zero-day, it appears in a release where Azure, Windows, and identity issues all share the same defensive spotlight. (bleepingcomputer.com)
Microsoft’s documentation ecosystem also shows that Logic Apps is designed around multiple security models, including managed identities and access keys. That means the blast radius of a privilege flaw depends heavily on how the service is configured, which connectors are in use, and whether the workflow is running in Consumption or Standard. In other words, the same CVE can have very different operational consequences from tenant to tenant.
If a flaw allows a user to break out of their intended scope, the next step is often identity theft, token abuse, or indirect access to resources the workflow can already reach. The practical risk is not limited to the Logic App itself; it extends to whatever the app can touch. That is why cloud EoPs can be more consequential than local privilege-escalation bugs on a single machine.
That plausibility matters because workflow engines often parse and persist user-defined content. If an attacker can control a path, a filename, or a location parameter anywhere in that chain, the consequences can range from configuration exposure to privilege escalation. In a managed cloud service, those mistakes are harder to spot precisely because the customer never sees the underlying filesystem or runtime directly. (app.opencve.io)
That is why server-side EoPs in cloud services are so disruptive. Customers are often told to prefer secure defaults, but secure defaults only help if the product enforces them consistently. When a bug undermines that enforcement, the customer’s trust in the platform’s boundary model is the first thing that breaks.
This distinction matters for containment. A multitenant service fix may be deployed centrally and immediately, while Standard deployments can add customer-managed layers such as virtual networks, private endpoints, and identity configuration. Those controls can reduce risk, but they also create more opportunities for misconfiguration. The more powerful the environment, the more carefully it must be governed.
The irony is that cloud issues can be harder to detect post-incident. Attackers who move through a service boundary may leave fewer host-based indicators than they would on a workstation or server. In a service like Logic Apps, the meaningful telemetry often lives in control-plane logs, identity logs, and connector audit trails, which many organizations do not monitor with the same intensity as endpoint events.
This also affects competitors in the automation and integration space. Any vendor offering low-code orchestration, managed connectors, or identity-based execution now has to defend against the same class of criticism: if a platform can act with elevated privileges, then any flaw in authorization becomes a strategic vulnerability. The market tends to reward feature velocity, but incidents like this remind buyers that security engineering is part of the product.
Security teams should also assess whether the Logic App is used as a bridge to Azure Monitor, Azure SQL, service buses, or line-of-business systems. Those connectors can be perfectly legitimate, but they turn a workflow into a multi-system control plane. In that setting, one privilege bug can become a lateral-movement platform.
This makes communication crucial. IT teams should explain in plain language that the issue is not “another Windows patch,” but a cloud-service trust boundary. That distinction helps nontechnical stakeholders understand why identity reviews and connector audits may matter more than endpoint scans.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Azure Logic Apps is Microsoft’s workflow automation platform for building integrations between services, APIs, and data sources without extensive custom code. It is available in both Consumption and Standard models, with different runtime and hosting characteristics, and it relies heavily on connectors that often authenticate through Microsoft Entra ID, managed identities, or service credentials. That architecture gives the platform enormous flexibility, but it also creates a security surface where a seemingly small authorization flaw can have outsized impact.The specific CVE is described as an elevation of privilege issue, which in cloud services is usually more serious than the label first suggests. An EoP in Logic Apps can mean a low-privilege or otherwise unauthorized actor could cross a boundary that should have been enforced by the service, workflow runtime, or connector layer. In practice, that can turn a workflow platform from an integration engine into an access amplifier, especially when a workflow has been granted broad rights over Azure resources. (app.opencve.io)
Microsoft has a long history of shipping fixes for Azure-hosted services where the real issue is not just code correctness, but authorization correctness. Prior MSRC writeups on Azure Automation, Azure Machine Learning, and other cloud offerings show the same pattern: attackers often do not need to “break” encryption or defeat the whole service. They just need one path where the service trusts a request, token, callback, or connector too much, and then the attacker rides the platform’s own privileges to a higher level.
That context matters here because Logic Apps is built to do things on behalf of users and organizations. It can read data, trigger downstream automations, call third-party endpoints, and act through identity bindings that may be far more powerful than the user interface suggests. A weakness in that trust chain is not merely a bug; it is potentially a shortcut around the cloud control plane.
What Microsoft Disclosed
Microsoft’s public classification for CVE-2026-32171 is terse, but it is enough to establish the broad shape of the issue. The advisory page names the vulnerability as an Azure Logic Apps Elevation of Privilege Vulnerability, and the associated vulnerability record indicates the affected product is Azure Logic Apps. OpenCVE’s normalized record also tags the issue as a path traversal-style flaw under CWE-22, describing it as an “improper limitation of a pathname to a restricted directory.” (app.opencve.io)The confidence metric matters
The user-supplied text points to a separate but important idea: Microsoft’s vulnerability confidence metric is about how certain the vendor is that the flaw exists and how much technical detail is known. That distinction matters because defenders often have to act before every exploit primitive is fully documented. Here, the fact that Microsoft has published a CVE, assigned a severity, and tied it to a named service suggests this is not speculative research or rumor. (app.opencve.io)The timing is also important. The advisory is part of the April 2026 Patch Tuesday cycle, a release that BleepingComputer reported as covering 167 flaws overall, including two zero-days in other Microsoft products. Even though CVE-2026-32171 is not the headline zero-day, it appears in a release where Azure, Windows, and identity issues all share the same defensive spotlight. (bleepingcomputer.com)
Microsoft’s documentation ecosystem also shows that Logic Apps is designed around multiple security models, including managed identities and access keys. That means the blast radius of a privilege flaw depends heavily on how the service is configured, which connectors are in use, and whether the workflow is running in Consumption or Standard. In other words, the same CVE can have very different operational consequences from tenant to tenant.
What the advisory does and does not say
The advisory does not, at least in the public metadata visible here, spell out the exploit chain, the vulnerable component, or whether abuse requires authentication. That silence is typical for cloud-service advisories, especially when the issue is being mitigated server-side or when Microsoft wants to limit attacker intelligence while customers apply the fix. The absence of detail should not be mistaken for lower severity. If anything, it often means the service team has already closed the most direct path. (app.opencve.io)- Microsoft has identified the bug as a Logic Apps EoP issue. (app.opencve.io)
- The normalized vulnerability data points to CWE-22 / path traversal. (app.opencve.io)
- The issue affects Azure Logic Apps across the service, not a single customer deployment artifact. (app.opencve.io)
- The issue appears in the same month as a broad Patch Tuesday release. (bleepingcomputer.com)
Why Elevation of Privilege in Logic Apps Is Serious
Logic Apps sits at a sensitive layer in the Azure stack because it can combine identity, networking, and business logic in one workflow. If an attacker can elevate privileges inside that environment, the result may be more than one compromised workflow. It can become a launch point for accessing storage accounts, APIs, message queues, monitoring data, or downstream enterprise systems that the workflow already trusts.Identity is the real asset
Azure Logic Apps increasingly encourages the use of managed identities rather than embedded secrets. Microsoft’s documentation says managed identities are the recommended approach because they let workflows authenticate to protected Azure resources without storing credentials directly. That is a strong design choice, but it also means privilege mistakes can be amplified when a workflow identity has broad rights.If a flaw allows a user to break out of their intended scope, the next step is often identity theft, token abuse, or indirect access to resources the workflow can already reach. The practical risk is not limited to the Logic App itself; it extends to whatever the app can touch. That is why cloud EoPs can be more consequential than local privilege-escalation bugs on a single machine.
Path traversal changes the threat model
The OpenCVE description’s reference to path traversal is especially important because path handling bugs often let an attacker escape a sandbox, read or overwrite files outside intended boundaries, or manipulate server-side resources through unexpected paths. In a service platform, that can translate into unauthorized access to configuration, workflow definitions, connector metadata, or internal runtime artifacts. We should be careful here: Microsoft has not publicly confirmed all of those mechanics in the advisory metadata, but the CWE mapping makes that class of failure plausible. (app.opencve.io)That plausibility matters because workflow engines often parse and persist user-defined content. If an attacker can control a path, a filename, or a location parameter anywhere in that chain, the consequences can range from configuration exposure to privilege escalation. In a managed cloud service, those mistakes are harder to spot precisely because the customer never sees the underlying filesystem or runtime directly. (app.opencve.io)
- Workflows can be privileged actors.
- Connectors often inherit access to critical systems.
- Identity mistakes can magnify a single bug into a tenant-level problem.
- A path traversal issue in a service boundary is rarely “just a file bug.”
- Service-side fixes can reduce exposure quickly, but they do not erase the need for least privilege.
Azure Logic Apps Security Model
Microsoft’s own guidance for Logic Apps security makes clear that the platform gives administrators several layers of control. You can use access keys, SAS URLs, OAuth 2.0, and managed identities depending on the trigger or connector. The documentation also stresses that inbound calls to request-based triggers can use only one authorization scheme at a time, which is a reminder that security boundaries in Logic Apps are explicit and operational, not abstract.Managed identity is safer, but not magic
The recommendation to use Microsoft Entra ID and managed identities whenever possible is sound, but it does not eliminate the risk of a service flaw. Managed identities are meant to lower credential exposure, not to make the workflow harmless. If the Logic App runtime itself is coerced into misusing its own identity or bypassing access checks, the attacker gains exactly the kind of privilege the service was supposed to keep safe.That is why server-side EoPs in cloud services are so disruptive. Customers are often told to prefer secure defaults, but secure defaults only help if the product enforces them consistently. When a bug undermines that enforcement, the customer’s trust in the platform’s boundary model is the first thing that breaks.
Consumption versus Standard
Logic Apps comes in Consumption and Standard flavors, and the security implications are not identical. The Consumption model runs in multitenant Azure Logic Apps, while Standard is single-tenant and can integrate more deeply with networking and hosting options. From a defender’s perspective, a vulnerability can therefore have a different blast radius depending on whether the workflow is shared infrastructure or isolated tenant infrastructure.This distinction matters for containment. A multitenant service fix may be deployed centrally and immediately, while Standard deployments can add customer-managed layers such as virtual networks, private endpoints, and identity configuration. Those controls can reduce risk, but they also create more opportunities for misconfiguration. The more powerful the environment, the more carefully it must be governed.
What administrators should internalize
- Authorization scheme choice matters.
- Managed identities reduce secret sprawl.
- Broad workflow permissions increase the payoff for any EoP.
- Single-tenant isolation helps, but does not replace patching.
- Connector trust should be reviewed as carefully as app code.
Patch Tuesday Context
CVE-2026-32171 landed in a particularly heavy Patch Tuesday. BleepingComputer’s roundup says Microsoft fixed 167 flaws in April 2026 and that the release also addressed two zero-days elsewhere in the Microsoft ecosystem. That makes the Logic Apps issue part of a broader defensive sprint rather than a standalone cloud bulletin, which can make it easier for organizations to overlook if they focus only on the headline zero-days. (bleepingcomputer.com)Why cloud issues get buried
Large patch cycles tend to emphasize the most obviously exploitable local vulnerabilities: kernel bugs, browser flaws, and publicly known zero-days. Cloud-service issues like this one can receive less attention because they may be auto-mitigated or because they do not require a reboot. That is a dangerous assumption, especially in enterprises that rely on workflow automation for finance, support, identity, and compliance tasks. (bleepingcomputer.com)The irony is that cloud issues can be harder to detect post-incident. Attackers who move through a service boundary may leave fewer host-based indicators than they would on a workstation or server. In a service like Logic Apps, the meaningful telemetry often lives in control-plane logs, identity logs, and connector audit trails, which many organizations do not monitor with the same intensity as endpoint events.
Enterprise response versus consumer response
Most consumer users will never interact directly with Azure Logic Apps, but enterprises almost certainly will. That means the priority is not individual user action, but platform governance: inventorying Logic Apps resources, reviewing identities and connector permissions, and verifying whether Microsoft’s service-side remediation has been applied. For organizations running business-critical automations, this is the kind of issue that deserves the same treatment as a directory or storage flaw.- Enterprise teams should inventory Logic Apps immediately.
- Security teams should review workflow identities and role assignments.
- Operations teams should verify whether service-side mitigation has reached every region.
- SOC teams should look in control-plane and Entra logs, not just endpoint tools.
- Governance teams should reassess least-privilege policies for connectors.
Competitive and Market Implications
This kind of vulnerability matters beyond Microsoft’s immediate patch cadence because it reinforces a broader market reality: workflow automation is now a core security boundary. Azure Logic Apps competes not just on productivity and integration breadth, but on the trustworthiness of its execution model. Every privilege flaw chips away at that trust and forces buyers to ask whether their automation platform is also an attack surface.Microsoft’s cloud advantage is also its burden
Microsoft benefits from the fact that it can sometimes mitigate service-side vulnerabilities centrally, which is a major advantage over on-premises products. But that same advantage creates a higher expectation: customers assume Microsoft’s hosted services will be hardened, isolated, and rapidly corrected. When a CVE like this appears, the company has to prove not just that it can patch quickly, but that its trust boundaries are resilient enough to withstand complex connector-driven workloads.This also affects competitors in the automation and integration space. Any vendor offering low-code orchestration, managed connectors, or identity-based execution now has to defend against the same class of criticism: if a platform can act with elevated privileges, then any flaw in authorization becomes a strategic vulnerability. The market tends to reward feature velocity, but incidents like this remind buyers that security engineering is part of the product.
Azure-specific lessons for rivals
Cloud platforms that rely on server-side orchestration should take one lesson very seriously: identity and path handling are not independent concerns. A workflow engine that resolves paths, loads metadata, or passes connector parameters across trust boundaries needs a defensive architecture that assumes inputs can be hostile. That is especially true when the engine can reach internal services unavailable to the outside world. (app.opencve.io)- Workflow platforms need stronger sandboxing.
- Connector privilege must be explicit and minimal.
- Central mitigation is helpful, but customers still need telemetry.
- Identity-bound services create high-value escalation targets.
- Managed cloud doesn’t mean managed risk is low.
Enterprise Impact
For enterprises, the question is not whether the CVE exists; it is what the vulnerability might have allowed inside their own automation estate before Microsoft closed the gap. Logic Apps often sits at the center of approvals, ticketing, monitoring, and data movement, which means a successful EoP can affect business continuity as much as confidentiality or integrity. That makes this a governance issue, not only a security issue.Where to look first
The first places to examine are workflows with broad managed identity permissions, high-value connectors, and request-based triggers exposed to a wide audience. Teams should also identify Standard workflows with custom networking, because those deployments often carry more privileges and more assumptions than simple consumption apps. If a Logic App controls anything resembling production access, it belongs in the top tier of review.Security teams should also assess whether the Logic App is used as a bridge to Azure Monitor, Azure SQL, service buses, or line-of-business systems. Those connectors can be perfectly legitimate, but they turn a workflow into a multi-system control plane. In that setting, one privilege bug can become a lateral-movement platform.
Practical enterprise priorities
- Map every Logic App to its identity and connector set.
- Validate least-privilege role assignments on managed identities.
- Review request-trigger exposure and callback URL handling.
- Check whether workflows can access secrets, queues, or admin APIs.
- Audit logs around late January and April 2026 for suspicious automation behavior.
Consumer and Small-Business Impact
Most home users will never deploy Azure Logic Apps, but small businesses increasingly consume Microsoft cloud services indirectly through automation, SaaS integrations, and managed IT. In that sense, a Logic Apps vulnerability can still matter even to organizations without a dedicated cloud team. If an MSP or internal admin uses Logic Apps to automate privileged tasks, a flaw in the platform becomes part of the organization’s operational risk.The hidden dependency problem
Small businesses often do not realize how many of their workflows depend on cloud orchestration engines. A help desk ticket may trigger a provisioning step, an accounting upload may call a storage API, and a sales process may notify internal systems through a Logic App chain. That hidden dependency is the risk: a flaw in the workflow platform can quietly affect core business functions without ever touching a desktop.This makes communication crucial. IT teams should explain in plain language that the issue is not “another Windows patch,” but a cloud-service trust boundary. That distinction helps nontechnical stakeholders understand why identity reviews and connector audits may matter more than endpoint scans.
- Do not assume “Azure” means low impact.
- Ask whether any business process depends on Logic Apps.
- Review vendors and MSPs that manage automations on your behalf.
- Treat workflow credentials like production secrets.
- Monitor for unusual rerouting or privilege changes in integrated systems.
Strengths and Opportunities
Microsoft’s response model has real strengths here. A hosted service can be fixed centrally, and the Logic Apps security documentation already pushes customers toward managed identities and Entra-backed authentication, which is the right architectural direction. If the remediation is complete, this CVE becomes a case study in how cloud vendors can reduce exposure without forcing every customer into an emergency upgrade cycle. That is not trivial.- Central mitigation can reach customers faster than manual patching.
- Managed identities reduce secret exposure when used correctly.
- Logic Apps security guidance already aligns with least privilege.
- This incident may accelerate better auditing of connector permissions.
- Security teams can use the advisory to justify workflow inventory projects.
- Microsoft can strengthen confidence by improving transparency around service-side fixes.
- The event reinforces the value of cloud-native telemetry and identity monitoring.
Risks and Concerns
The biggest concern is that a service-side EoP may hide in plain sight for customers who assume the cloud handled everything automatically. If the flaw was exploitable before remediation, then any workflow with elevated permissions could have become a stepping stone into adjacent Azure resources. The lack of public exploit detail is understandable, but it also means defenders must rely more on architecture review than on signatures. (app.opencve.io)- Privilege escalation can cascade into broader Azure access.
- Path traversal in a workflow service may expose more than files.
- Customers may not know which workflows were most exposed.
- Many organizations do not log Logic Apps activity with enough depth.
- Broad connector permissions can magnify a single vulnerability.
- Service-side fixes may not erase forensic uncertainty about prior abuse.
- Automation platforms are attractive targets because they already hold trust.
Looking Ahead
The next questions are operational, not theoretical. Customers need to know whether the mitigation is fully deployed across regions, whether any exploitation evidence exists, and whether Microsoft will provide further detail on root cause or impact scope. In the meantime, organizations should assume that any service running automation with privileged identity bindings deserves a fresh security review. (app.opencve.io)What defenders should watch
- Microsoft updates to the CVE record or advisory text.
- Any revised guidance on affected workflow types or regions.
- Signs of suspicious Logic Apps activity in audit logs.
- New best-practice guidance for connector and identity scoping.
- Follow-on research that explains the path traversal boundary more clearly.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: