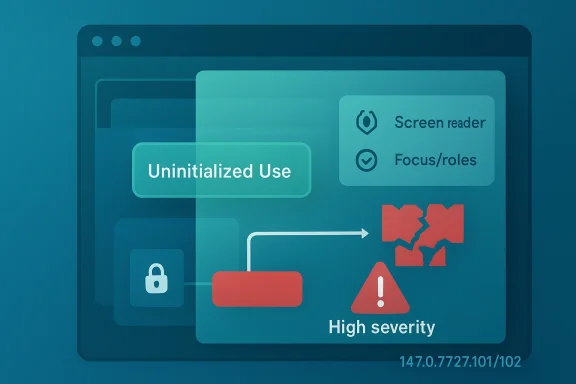
The latest Chrome security update closes a high-severity Chromium flaw, CVE-2026-6311, that lives in the browser’s accessibility code path and can be used as a sandbox escape on Windows if an attacker has already compromised the renderer process. Google’s April 15, 2026 Stable Channel release says the fixed desktop versions are 147.0.7727.101/102, with the Windows-specific advisory describing the issue as an uninitialized use in Accessibility. Microsoft’s Security Update Guide is tracking the same bug for downstream visibility, which is exactly what defenders should expect when a Chromium issue ripples into the broader browser ecosystem. gleblog.com]
CVE-2026-6311 is a reminder that browser security is often decided long before a malicious page reaches the open internet. The flaw is not described as a direct remote code execution bug from a normal browsing session; instead, it matters because it can be chained after a renderer compromise and then leveraged for sandbox escape. That distinction is important, because the sandbox is one of tnse separating a browser tab crash from a full system compromise.
Google’s classification of the issue as High severity fits the pattern we have seen repeatedly in Chromium security work through 2025 and 2026. The browser engine remains a massive attack surface, and memory-safety mistakes still dominate the most consequential flaws. The Accessibility subsystem is especially interesting because it is not usually the first place people think of when they picture browser exploitation, yet it touches complex object lifetimes, assistive technologies, and renderer-to-browser interactions that can become security-sensitive very quickly.
For Windows users, the practical answer is straightforward: if Chrome or a Chromium-based browser is still on a build before 147.0.7727.101, the browser should be updated immediately. Google says the update rolled o and Microsoft has already surfaced the CVE for administrators who rely on its security guidance to track upstream Chromium fixes. That downstream tracking matters because many enterprises treat browser updates as an operational workflow, not just a consumer click-through.
The larger storyurity model is increasingly a story about containment, not just prevention. If an attacker first gets renderer execution through another bug, then every weakness that helps them cross the process boundary becomes enormously valuable. In that sense, CVE-2026-6311 is not just a browser vulnerability; it is a potential pivot point in a multi-stage attack chain.
Accessibilitvely tricky in that model. It has to present information about page structure, focus, roles, and state to assistive technologies while also respecting the browser’s trust boundaries. That means it often sits at the edge of several subsystems at once, where lifetime management bugs, stale references, and incomplete initialization can all become security problems. A flaw categorized as CWE-457 Use of Uninitialized Variable is exactly the kind of defect that can produce unpredictable behavior when security-sensitive data is read before it has been properly set.
Google’s April 15 stable-channel update shows that this is not an isolated concern. The same release includes multiple high-severity Chromium fixes, which reflects a broader pattern: the browser update is less a single patch than a security bundle intended too bundling matters because defenders cannot treat browser hardening as a one-bug-at-a-time exercise anymore.
Microsoft’s Security Update Guide has become an important companion source for the Chromium ecosystem because Edge inherits Chromium fixes downstream. When Microsoft surfaces the advisory, it is not because Microsoft authored the bug; it is because organizations running Edge need a reliable way to know when the upstream Chromium fix has landed in their browser baseline. That is a subtle but critical distinction for enterprise patching.
Historically, browser security advisories have tended to cluster around memory corruption, type confusion, use-after-free, and policy-bypass bugs. CVE-2026-6311 fits that pattern by twhere object state can become inconsistent. The exploitability rating also hints that this is not a trivial one-step browser crash; it assumes an attacker who already has a foothold in the renderer process, which is exactly why the sandbox escape angle is so dangerous.
That does not automatically mean every accessibility bug becomes a full exploit chain. But it does mean that bugs in this area can sit closer to trust boundaries than many users assume. If a renderer compromise is already in play, then a security-sensitive logic flaw in accessibility may be enough to reach the browser process or bypass sandbox assumptions.
The reason defenders should care is that small-seeming defects can have outsized consequences in hardened architetialization may not sound dramatic, but in a browser it can become a primitive for reading or steering state that the attacker should never see. In security terms, that is exactly the kind of bug that turns a partial compromise into a much more serious incident.
The condition also explains why CVE-2026-6311 is rated high rather than automatically labeled catastrophic. It is a post-compromise vulnerability, not a universally reachable drive-by exploit in the advisory text. Still, post-compromise bugs are exactly what sophisticated attackers use to turn isolated code execution into durable access.
In practical terms, this means the issue belongs in the same mental bucket as privilege-escalation bugs inside an already-breached system. The first foothold may come from a malicious page, a malicious extension, or some other browser weakness; CVE-2026-6311 then becomes the mechanism that breaks the process boundary. That is why updates of this kind should be treated as urgent even when they are not zero-days.
The Microsoft tracking entry reinforces that point by mirroring the Chromium CVE for downstream consumers. Microsoft’s Security Update Guide is useful because it translates upstream Chrome and Chromium fixes into the terminology administrators already use when evaluating Edge. In enterprise environments, that can save hours of detective work during emergency patch windows.
Consumers usually experience this as a silent browser restart or a version bump in settings. Enterprises experience it as an asset-management exercise. The difference is not cosmetic; it determines whether the organization closes the exposure in hours or days. That gap is where a lot of real-world risk lives.
This creates a useful but sometimes confusing chain of responsibility. Google identifies and patches the defect, while Microsoft documents downstream impact for its browser customers. Enterprises that only watch one vendor’s advisories can easily miss the practical importance of the other’s release cadence.
The shared-engine model has major security advantages because it concentrates fixes and reduces duplicate patch work. But it also means that Chromium defects spread quickly across the ecosystem. A flaw in one browser can become a fleet-wide issue across multiple products, which onversation has to be ecosystem-wide rather than brand-specific.
That makes post-exploitation browser bugs strategically important even when they do not dominate headlines. They are the connective tissue of real intrusions. Once an attacker can escape the browser sandbox, they may be able to access local data, plant persistence, or pivot to other user context assets depending on the surroundeom]
The “crafted HTML page” detail also matters because it signals ordinary web content as the delivery mechanism. The page itself may not look exotic, which is precisely what makes browser exploitatefend by inspection alone. Security teams cannot rely on visual suspicion; they need patch discipline and layered detection.
This also explains why browser vendors treat process-boundary bugs with such seriousness. The sandbox is not a decorative security feature; it is the core containment model. Anything that weakens it should be handled with the same urgency as a privilege escalation in an operating system context. ([chromereleases.googleblog.com](https://chromereleases.googleblog.com/2026/04/stable-channel-update-for-desktop_15.htm
In practical incident-response terms, defenders should not ask only whether the flaw is exploitable from the internet. They should ask whether the organization has enough browser hardening, extension control, exploit mitigations, and patch velocity to make a renderer compromise unlikely in the firer is weak, then CVE-2026-6311 becomes far more relevant.
The MSRC mapping also helps security teams keep patch reporting consistent across departments. Compliance teams may think in terms of Microsoft advisories, while browser engineers think in terms of Chromium milestones. The guide acts as a translation layer between those operational languages.
That translation matters because browser vulnerabilities do not respect product branding. A flaw in Chrome can become a real issue for Edge, WebView-based apps, and any enterprise workflow that depends on Chromium internals. The more integrated the software stack, the more important this kind of cross-vendor documentation becomes.
This is where staged rollout becomes a double-edged sword. It reduces the odds of a bad update breaking the fleet, but it also means some systems remain vulnerable while the rollout progresses. If administrators do not watch actual installed versions, they can confuse “available” with “deployed.”
The lesson is simple but often ignored: patch orchestration must be measured in inventory coverage, not release notes. A browser fix only protects users who actually received it. That sounds obvious, yet it is one of the easiest places for organizations to lose time during urgent remediation.
Accessibility bugs are particularly illustrative because they often arise in code that must reconcile many states at once. A missing initialization may happen in a path that is less frequently exercised than core rendering, but exploitability does not require frequency to be dangerous. It only requires a path that an attacker can reliably force.
The industry’s answer so far has been layered mitigation: sandboxing, site isolation, process separation, and faster patch cycles. Those measures work, but only if they are kept current. A modern browser is secure not because it never ffails in ways that are increasingly difficult to convert into full compromise.
That is a healthy question. Security teams often focus on the most obvious exploit surfaces, but attackers do not. They look for the path with the best combination of reliability, reach, and stealth. Accessibility paths can be attractive precisely because defenders tend to think of them as low drama.
If nothing else, this CVE is a remidening must extend beyond the visible parts of the product. Any subsystem that touches renderer output, browser state, or cross-process communication can become part of the attack surface. That includes components the average user never sees.
For consumer users, the advice is simpler: update immediately and restart the browser if prompted. The exploit chain described by Google does not require the user to “do something obviously wrong” in order to matter. A malicious page is enough as the delivery foothold.
For defenders, the practical future-facing lesson is to treat browser patching like a continuous exposure-management exercise. That means faster version inventory, clearer restart enforcement, and a tighter understanding of how upstream Chromium fixes propagate into Edge and other derivatives. In 2026, browser security is less about waiting for the next monthly patch wave and more about closing the distance between disclosure and deployment.
What to watch next:
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
 Overview
Overview
CVE-2026-6311 is a reminder that browser security is often decided long before a malicious page reaches the open internet. The flaw is not described as a direct remote code execution bug from a normal browsing session; instead, it matters because it can be chained after a renderer compromise and then leveraged for sandbox escape. That distinction is important, because the sandbox is one of tnse separating a browser tab crash from a full system compromise.Google’s classification of the issue as High severity fits the pattern we have seen repeatedly in Chromium security work through 2025 and 2026. The browser engine remains a massive attack surface, and memory-safety mistakes still dominate the most consequential flaws. The Accessibility subsystem is especially interesting because it is not usually the first place people think of when they picture browser exploitation, yet it touches complex object lifetimes, assistive technologies, and renderer-to-browser interactions that can become security-sensitive very quickly.
For Windows users, the practical answer is straightforward: if Chrome or a Chromium-based browser is still on a build before 147.0.7727.101, the browser should be updated immediately. Google says the update rolled o and Microsoft has already surfaced the CVE for administrators who rely on its security guidance to track upstream Chromium fixes. That downstream tracking matters because many enterprises treat browser updates as an operational workflow, not just a consumer click-through.
The larger storyurity model is increasingly a story about containment, not just prevention. If an attacker first gets renderer execution through another bug, then every weakness that helps them cross the process boundary becomes enormously valuable. In that sense, CVE-2026-6311 is not just a browser vulnerability; it is a potential pivot point in a multi-stage attack chain.
Background
Chromium’s architecture isolates web content into a renderer process precisely because the web is hostile by default. The browser process is meant to be more trusted, while renderers are expected to absorb untrusted HTML, JavaScript, and media data. The sandbox is there to keep a compromised renderer from becoming a compromised machine, and any bug that weakens that barrier deserves serious attention.Accessibilitvely tricky in that model. It has to present information about page structure, focus, roles, and state to assistive technologies while also respecting the browser’s trust boundaries. That means it often sits at the edge of several subsystems at once, where lifetime management bugs, stale references, and incomplete initialization can all become security problems. A flaw categorized as CWE-457 Use of Uninitialized Variable is exactly the kind of defect that can produce unpredictable behavior when security-sensitive data is read before it has been properly set.
Google’s April 15 stable-channel update shows that this is not an isolated concern. The same release includes multiple high-severity Chromium fixes, which reflects a broader pattern: the browser update is less a single patch than a security bundle intended too bundling matters because defenders cannot treat browser hardening as a one-bug-at-a-time exercise anymore.
Microsoft’s Security Update Guide has become an important companion source for the Chromium ecosystem because Edge inherits Chromium fixes downstream. When Microsoft surfaces the advisory, it is not because Microsoft authored the bug; it is because organizations running Edge need a reliable way to know when the upstream Chromium fix has landed in their browser baseline. That is a subtle but critical distinction for enterprise patching.
Historically, browser security advisories have tended to cluster around memory corruption, type confusion, use-after-free, and policy-bypass bugs. CVE-2026-6311 fits that pattern by twhere object state can become inconsistent. The exploitability rating also hints that this is not a trivial one-step browser crash; it assumes an attacker who already has a foothold in the renderer process, which is exactly why the sandbox escape angle is so dangerous.
What the Vulnerability Actually Means
At a technical level, an uninitialized use means code reads memory or state before the program has given it a defined value. In secure code, that can yield garbage data, stale pointers, or inconsistent permission decisions. In the worst case, it can expose a control path the developer assumed would never be reachable.Why Accessibility Is a Sensitive Surface
Accessibility is not just a user-experience feature. It is a bridge between the page and external consumers of browser state, which means it is often handling structured data that has already been transformed once by the browser engine. When that bridge is imperfect, attackers can sometimes influence how the browser describes itself to higher-trust components.That does not automatically mean every accessibility bug becomes a full exploit chain. But it does mean that bugs in this area can sit closer to trust boundaries than many users assume. If a renderer compromise is already in play, then a security-sensitive logic flaw in accessibility may be enough to reach the browser process or bypass sandbox assumptions.
The reason defenders should care is that small-seeming defects can have outsized consequences in hardened architetialization may not sound dramatic, but in a browser it can become a primitive for reading or steering state that the attacker should never see. In security terms, that is exactly the kind of bug that turns a partial compromise into a much more serious incident.
The Renderer-Compromise Condition
Google’s wording is careful: the attacker must have compromised the renderer process first. That is a constraint, but it is not a comfort. Renderer compromises are common in browser exploitation chains, and once an attacker reaches that point, the value of a sandbox escape rises sharply.The condition also explains why CVE-2026-6311 is rated high rather than automatically labeled catastrophic. It is a post-compromise vulnerability, not a universally reachable drive-by exploit in the advisory text. Still, post-compromise bugs are exactly what sophisticated attackers use to turn isolated code execution into durable access.
In practical terms, this means the issue belongs in the same mental bucket as privilege-escalation bugs inside an already-breached system. The first foothold may come from a malicious page, a malicious extension, or some other browser weakness; CVE-2026-6311 then becomes the mechanism that breaks the process boundary. That is why updates of this kind should be treated as urgent even when they are not zero-days.
Release Timing and Version Exposure
The fixed build for Chrome desktop is 147.0.7727.101/102, with the split reflecting platform-specific packaging. Google’s release note indicates the update began rolling out over the following days and weeks, which is typical of Chrome’el. That rollout pattern is convenient for stability, but it also means defenders need to verify actual version adoption rather than assume availability equals protection.Why Version Numbers Matter
Version boundaries are the first srowser advisories often map cleanly to release-line cutoffs. If a fleet is still below 147.0.7727.101, then the vulnerable code is still present, regardless of whether the update has been announced. That makes inventory discipline as important as patch deployment itself.The Microsoft tracking entry reinforces that point by mirroring the Chromium CVE for downstream consumers. Microsoft’s Security Update Guide is useful because it translates upstream Chrome and Chromium fixes into the terminology administrators already use when evaluating Edge. In enterprise environments, that can save hours of detective work during emergency patch windows.
Consumers usually experience this as a silent browser restart or a version bump in settings. Enterprises experience it as an asset-management exercise. The difference is not cosmetic; it determines whether the organization closes the exposure in hours or days. That gap is where a lot of real-world risk lives.
Edge, Chrome, and the Shared Engine Problem
Because Microsoft Edge is Chromium-based, upstream Chrome fixes are not optional background noise. They become part of Edge’s security posture as soon as Microsoft absorbs them into its own release stream. That means a Chrome CVE is often also an Edge operational concern, even when Microsoft did not write the vulnerable code.This creates a useful but sometimes confusing chain of responsibility. Google identifies and patches the defect, while Microsoft documents downstream impact for its browser customers. Enterprises that only watch one vendor’s advisories can easily miss the practical importance of the other’s release cadence.
The shared-engine model has major security advantages because it concentrates fixes and reduces duplicate patch work. But it also means that Chromium defects spread quickly across the ecosystem. A flaw in one browser can become a fleet-wide issue across multiple products, which onversation has to be ecosystem-wide rather than brand-specific.
Threat Modeling and Exploit Chains
CVE-2026-6311 is best understood as a chaining vulnerability. On its own, the bug is not described as a one-click remote compromise in Google’s release note. In a larger exploit chain, however, it can be the step that turns a renderer foothold into a process escape and then into a more serious system-level incident.How Attackers Think About It
Attackers often care less about the first bug than about the second and third. A renderer exploit grants code execution in a constrained environment, but the sandbox is designed to limit what happens next. If a second bug weakens that barrier, then the attacker’s return on investment rises dramatically.That makes post-exploitation browser bugs strategically important even when they do not dominate headlines. They are the connective tissue of real intrusions. Once an attacker can escape the browser sandbox, they may be able to access local data, plant persistence, or pivot to other user context assets depending on the surroundeom]
The “crafted HTML page” detail also matters because it signals ordinary web content as the delivery mechanism. The page itself may not look exotic, which is precisely what makes browser exploitatefend by inspection alone. Security teams cannot rely on visual suspicion; they need patch discipline and layered detection.
Why “Renderer Compromised First” Is Not a Small Caveat
Some readers may see the precondition and think the risk is less urgent. In practice, the opposite is often tad any renderer execution route, a sandbox escape becomes the sort of capability that separates a noisy intrusion attempt from a successful compromise.This also explains why browser vendors treat process-boundary bugs with such seriousness. The sandbox is not a decorative security feature; it is the core containment model. Anything that weakens it should be handled with the same urgency as a privilege escalation in an operating system context. ([chromereleases.googleblog.com](https://chromereleases.googleblog.com/2026/04/stable-channel-update-for-desktop_15.htm
In practical incident-response terms, defenders should not ask only whether the flaw is exploitable from the internet. They should ask whether the organization has enough browser hardening, extension control, exploit mitigations, and patch velocity to make a renderer compromise unlikely in the firer is weak, then CVE-2026-6311 becomes far more relevant.
Microsoft’s Role in Downstream Tracking
Microsoft’s Security Update Guide is increasingly important for organizations that run Edge at scale. Its value is not in duplicating Google’s work, but in helping administrators map Chromium-originated vulnerabilities to Microsoft-managed browser deployments. That downstream visibility is often the difference between a clean patch run and a missed exposure.Why the MSRC Entry Matters
Microsoft’s entry does two things at once. First, it confirms that the Chromium issue is relevant to Edge users. Second, it gives security teams a place to monitor whether their Edge build has absorbed the fix. In a mixed-browser environment, that saves a lot of guesswork.The MSRC mapping also helps security teams keep patch reporting consistent across departments. Compliance teams may think in terms of Microsoft advisories, while browser engineers think in terms of Chromium milestones. The guide acts as a translation layer between those operational languages.
That translation matters because browser vulnerabilities do not respect product branding. A flaw in Chrome can become a real issue for Edge, WebView-based apps, and any enterprise workflow that depends on Chromium internals. The more integrated the software stack, the more important this kind of cross-vendor documentation becomes.
Enterprise Patching Realities
Enterprises rarely patch browsers with the same speed they patch a zero-day in a perimeter appliance. Browser updates have to coexist with compatibility testing, user disruption, and software distribution controls. That is rational, but it also makes browser CVEs a frequent source of residual exposure.This is where staged rollout becomes a double-edged sword. It reduces the odds of a bad update breaking the fleet, but it also means some systems remain vulnerable while the rollout progresses. If administrators do not watch actual installed versions, they can confuse “available” with “deployed.”
The lesson is simple but often ignored: patch orchestration must be measured in inventory coverage, not release notes. A browser fix only protects users who actually received it. That sounds obvious, yet it is one of the easiest places for organizations to lose time during urgent remediation.
What This Says About Browser Security in 2026
CVE-2026-6311 reinforces a broader reality: browser security is increasingly about controlling complex internal trust boundaries. The web content itself may be untrusted, but the browser contains many auxiliary pathways that must still make security decisions. Accessibility is one of those pathways, and it is only getting more important as browsers grow more integrated with operating-system features.Memory Safety Is Still the Core Problem
The persistence of uninitialized use, use-after-free, and out-of-bounds issues in Chromium underlines a painful truth. Even as browser sandboxes improve, the underlying code still contains memory-safety defects that can be turned into exploitation primitives. That is why Chromium security releases keep arriving in batches rather than as rare exceptions.Accessibility bugs are particularly illustrative because they often arise in code that must reconcile many states at once. A missing initialization may happen in a path that is less frequently exercised than core rendering, but exploitability does not require frequency to be dangerous. It only requires a path that an attacker can reliably force.
The industry’s answer so far has been layered mitigation: sandboxing, site isolation, process separation, and faster patch cycles. Those measures work, but only if they are kept current. A modern browser is secure not because it never ffails in ways that are increasingly difficult to convert into full compromise.
The Accessibility Angle Should Not Be Ignored
Assistive technology support is an essential feature, not an optional add-on. But any feature that exposes rich internal state needs a strong security engineering posture. CVE-2026-6311 may lead some teams to scrutinize whether auxiliary subsystems receive enough hardening attention compared with headline components likchromereleases.googleblog.com]That is a healthy question. Security teams often focus on the most obvious exploit surfaces, but attackers do not. They look for the path with the best combination of reliability, reach, and stealth. Accessibility paths can be attractive precisely because defenders tend to think of them as low drama.
If nothing else, this CVE is a remidening must extend beyond the visible parts of the product. Any subsystem that touches renderer output, browser state, or cross-process communication can become part of the attack surface. That includes components the average user never sees.
Practical Guidance for Windows Users and Admins
The immediate action is to confirm that Chrome on Windows is at least 147.0.7727.101/102, depending on platform packaging. If it is not, the uptized alongside other high-severity browser fixes in the same release cycle. Waiting for a maintenance window is a reasonable enterprise instinct, but in this case the exposure window is not where you want to save time.gleblog.com]What to Check First
- Verify the installed browser version on endpoints.
- Confirm the update has reached every managed channel, not just pilot devices.
- Check whether Edge is also aligned with the Chromium fix path.
- Review browser restart behavior so users are not left on stale builds.
- Validate that remote or offline devices eventually receive the patched package.
For consumer users, the advice is simpler: update immediately and restart the browser if prompted. The exploit chain described by Google does not require the user to “do something obviously wrong” in order to matter. A malicious page is enough as the delivery foothold.
Strengths and Opportunities
The good news is that the browser ecosystem is becoming better at responding quickly once a vulnerability is identified. Google’s stable-channel cadence is fast, Microsoft’s downstream tracking adds visibility, and the release-line boundary gives defenders a clear target for remediation. The following strengths stand out in this case, even if the underlying bug itself is serious.- Clear fixed version guidance makes patch verification practical.
- Downstream Microsoft tracking helps Edge administrators align their response.
- High-severity classification gives security teams a defensible prioritization signal.
- Sandbox design still limits direct reachability, which reduces ambient exposure compared with a fully remote bug.
- Browser auto-update mechanisms can close gaps faster than traditional enterprise software patching.
- Version-based remediation lets admins confirm compliance without waiting for intrusive forensics.
- The advisory language is specific enough to support SIEM and vulnerability-management workflows.
Risks and Concerns
The bad news is that the conditions around CVE-2026-6311 are exactly the sort that matter in real attacks. Renderer compromise is a realistic precursor in browser exploitation, and sandbox escapes can transform a constrained foothold into a much more damaging incident. The bigger concern is not just the bug itself, but what it enables in a chained attack.- Renderer compromise is a plausible first stage in browser exploitation campaigns.
- Sandbox escape potential raises the operational impact far beyond a normal crash bug.
- Staged rollout can leave some endpoints unpatched even after release day.
- Edge and other Chromium-based products inherit risk downstream, broadening the exposure footprint.
- Uninitialized-use bugs can be hard to reason about and may behave differently across builds or mitigations.
- Users often defer browser restarts, delaying practical protection.
- Enterprises may underestimate auxiliary subsystems like Accessibility when prioritizing fixes.
Looking Ahead
The next few days will tell us whether this CVE remains a routine high-severity patch or becomes part of a broader exploit narrative. The key question is not whether the flaw exists — that is already clear — but whether attackers can pair it with another renderer-side issue in the wild. If that happens, the advisory will look a lot more important in hindsight than it does in a simple version-check list.For defenders, the practical future-facing lesson is to treat browser patching like a continuous exposure-management exercise. That means faster version inventory, clearer restart enforcement, and a tighter understanding of how upstream Chromium fixes propagate into Edge and other derivatives. In 2026, browser security is less about waiting for the next monthly patch wave and more about closing the distance between disclosure and deployment.
What to watch next:
- Whether security researchers publish exploit details that clarify the Accessibility code path.
- How quickly Edge ingests the Chromium fix across stable and enterprise channels.
- Whether more Chromium CVEs appear in the same release batch, signaling a broader hardening push.
- How enterprise endpoint telemetry reflects real version adoption after rollout begins.
- Whether attackers chain CVE-2026-6311 with other renderer bugs in proof-of-concept or active exploit reporting.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
Last edited: