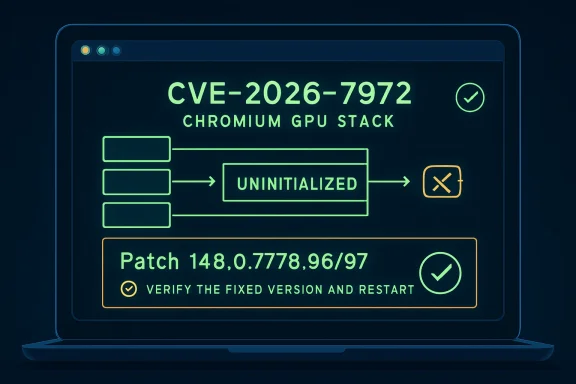
Google disclosed CVE-2026-7972 on May 6, 2026, as a medium-severity Chromium GPU vulnerability fixed in Chrome 148.0.7778.96 for Linux and 148.0.7778.96/97 for Windows and macOS, with Microsoft tracking the same Chromium flaw through its Security Update Guide. The bug is not the headline-grabbing remote-code-execution monster admins fear most, but it sits in a part of the browser stack that deserves more respect than the word “medium” usually gets. It is a reminder that modern browser compromise is rarely one clean break; it is a chain, and this flaw appears to live in the uncomfortable middle of that chain. For Windows users and IT teams running Chrome, Edge, or other Chromium-based browsers, the practical answer is simple: patch the browser, then verify that it actually moved.
CVE-2026-7972 is described as an uninitialized use issue in Chromium’s GPU component. In plainer terms, some piece of memory or state inside the graphics pipeline could be read before it was properly set to a known value. That can expose data the attacker should not be able to see.
The important qualifier is that the attacker first needed to have compromised the renderer process. That condition lowers the standalone severity because the bug is not advertised as a one-click, fresh-from-the-Internet takeover of Chrome by itself. But it also tells us exactly why defenders should pay attention: renderer compromise is one of the most common stepping stones in browser exploit chains.
The browser security model assumes hostile web content will be processed constantly. Sandboxing, site isolation, renderer separation, and GPU process boundaries exist because the browser is now the operating system’s most exposed application surface. A flaw that leaks cross-origin data after renderer compromise may not be the first domino, but it can be the domino that turns code execution into useful intelligence.
That matters because “cross-origin data” is the phrase doing much of the work here. The web’s same-origin rules are supposed to prevent one site from reading another site’s data. If a crafted HTML page can help leak data across that boundary after the attacker has already gained a foothold, the bug becomes a confidentiality tool inside a broader attack.
That framing is obsolete. The GPU process now sits close to complex web APIs, driver behavior, memory sharing, acceleration paths, and isolation boundaries. It is not merely drawing pixels; it is participating in a browser security architecture where performance shortcuts and memory lifetime bugs can become data exposure primitives.
Uninitialized-use bugs are especially awkward in this environment. They are not always dramatic crashes. Sometimes the program continues running while stale values, leftover memory, or undefined state become visible in ways the application never intended. In graphics workloads, where buffers are reused and timing-sensitive operations are routine, the difference between harmless residue and exploitable leakage can be thin.
This is why CVE-2026-7972 is more interesting than its score suggests. A CVSS 3.1 score of 4.3 says “medium,” and that is fair if the flaw requires user interaction and prior renderer compromise. But CVSS is a scoring language, not a threat model. It can tell you the shape of the vulnerability; it cannot tell you how attractive the bug is when paired with something else.
That is both reassuring and frustrating. Reassuring, because the fix is already in the stable release. Frustrating, because browser patching has become so frequent that many users and even some organizations treat updates as background noise. Chrome says it will update itself, Edge says the same, and everyone assumes the fleet is fine until an inventory report proves otherwise.
The release cadence also complicates messaging. A user who hears “Chrome 148 fixed critical bugs” may update once and move on. An administrator who sees “CVE-2026-7972, medium severity” may decide it can wait until the next maintenance window. Both reactions miss the operational reality: the browser is a constantly attacked endpoint platform, and version drift is the enemy.
There is also the Chromium multiplier. Chrome is the original disclosure point, but Microsoft Edge, Brave, Opera, Vivaldi, and countless embedded Chromium runtimes inherit much of the same security terrain. Microsoft tracking the CVE through MSRC is not a footnote for Windows shops; it is a reminder that Chromium vulnerabilities do not stop at Chrome’s icon.
That can create a dangerous kind of ambiguity. A vulnerability with “Chrome” in the source field may be mentally filed as “not our Microsoft problem,” while a vulnerability on the MSRC site may be assumed to arrive through Windows Update. Chromium-based Edge updates are their own channel. They can be managed well, but they must be managed deliberately.
This is where CPEs and affected-product records matter more than most people want to admit. The NVD change history indicates an affected Chrome configuration up to, but excluding, 148.0.7778.96 across Windows, Linux, and macOS. That is useful for scanners, but not enough for a Windows enterprise if the real asset question is “which Chromium runtimes are installed, which are actively used, and which are controlled by policy?”
The CPE question in the advisory is not academic. If vulnerability scanners lag behind vendor releases, mis-map Chromium forks, or miss unmanaged per-user browser installs, the dashboard can show green while exposed software remains on endpoints. This is one of the quiet failures of browser security: the patch exists, the version is known, and the fleet still contains ghosts.
The answer is that modern browser exploits are built in layers. A renderer bug may provide initial code execution inside a sandboxed process. A second bug may escape the sandbox or leak information needed to defeat address-space layout randomization, bypass site isolation, or steal data that should remain behind an origin boundary. CVE-2026-7972 appears to belong in that second category of useful follow-on capability.
This is why defenders should resist the comfort of single-CVE thinking. Attackers do not care whether one CVE tells the whole story. They care whether multiple imperfect bugs can be chained into a reliable exploit. A medium confidentiality bug in the GPU process can be far more useful in a chain than a higher-scored denial-of-service bug that only crashes a tab.
There is no public indication, at the time of disclosure, that CVE-2026-7972 is being actively exploited in the wild. That is good news. But browser attackers prize bugs that help cross boundaries, and the combination of renderer compromise, crafted HTML, GPU behavior, and cross-origin data leakage is precisely the kind of recipe that should keep this out of the “patch someday” pile.
That is especially true for Chromium. The project’s open-source nature is a security strength, but it also makes patch diffing part of the attacker workflow. When a stable release lands with dozens or hundreds of security fixes, defenders get broad protection; attackers get a menu of changed code to study.
CVE-2026-7972’s issue tracker entry requires permissions, which limits casual inspection. But the broader release still tells attackers where to look: GPU, uninitialized use, cross-origin data, renderer compromise, crafted HTML. That is not enough for easy exploitation, but it is enough to attract attention from researchers and offensive teams.
The practical implication is boring and unavoidable. Organizations should not wait for a weaponized exploit to care about the update. By the time exploit chatter becomes obvious, the easy patching window has already been wasted.
For Chrome, the target version is 148.0.7778.96 or later on Linux and 148.0.7778.96/97 or later on Windows and macOS. For Edge, admins should verify the corresponding Chromium-based Edge release from Microsoft’s channel rather than assuming the Chrome version number maps one-for-one. The core task is to confirm that every supported Chromium browser has consumed the fix.
On Windows, the visible version number is only part of the story. Admins should also confirm that update services are healthy, policies are not pinning old versions, and browser relaunch prompts are not being ignored indefinitely. A browser that downloaded an update but has not restarted is still running the old code.
This is also a good moment to inventory Chromium-based applications beyond the main browser. Electron apps, embedded WebView2 runtimes, remote support tools, kiosk shells, and vendor-packaged Chromium components can broaden exposure in ways ordinary browser patch reports do not capture. Not every Chromium CVE applies equally to every embedded runtime, but assuming “we patched Chrome” equals “we patched Chromium” is too optimistic.
CVE-2026-7972 does not say that any random page can do that unaided. The attacker first needs renderer compromise. But in a chained scenario, cross-origin leakage can turn a technical foothold into something more valuable: tokens, page contents, identifiers, fragments of sensitive workflows, or information that helps the next stage of compromise.
For WindowsForum readers, this lands squarely in the everyday threat model. The browser is where Microsoft 365 sessions live. It is where Entra ID sign-ins happen. It is where admins open cloud consoles, RMM dashboards, firewall interfaces, password vaults, and helpdesk systems. Cross-origin boundaries are not theoretical; they are the walls between a malicious tab and the rest of a working day.
That is also why ordinary advice like “don’t visit suspicious sites” is insufficient. The exploit path requires user interaction, but modern phishing does not need to look suspicious. A crafted HTML page can arrive through a compromised legitimate site, a malicious ad chain, a fake meeting link, a poisoned search result, or a message that looks routine.
A CPE can describe Google Chrome before a fixed version. It can describe the operating systems on which the application runs. But it may not represent every downstream Chromium consumer, every enterprise channel, every portable install, or every embedded runtime that security teams actually care about. Asset databases prefer neat product boxes; Chromium is an ecosystem.
This is where scanner output should be treated as evidence, not truth. If a scanner flags Chrome before 148.0.7778.96, believe it and patch. If a scanner does not flag a Chromium-based browser or runtime, do not automatically assume safety. Ask whether that product has shipped a Chromium update containing the fix.
The better enterprise posture is version-based and vendor-aware. Know which browsers are allowed, which update mechanisms are authoritative, which policies control relaunch, and which software bundles Chromium independently. CVE-2026-7972 is a medium-severity example of the same inventory problem that becomes urgent whenever Chromium ships a critical zero-day fix.
But the cost of that model is permanent operational churn. Users must relaunch. Admins must verify. Vendors downstream of Chromium must integrate. Security teams must triage a flood of CVEs whose individual severity scores do not always capture chainability. The machine works only if the last mile works.
CVE-2026-7972 illustrates this bargain well. The bug is not presented as an actively exploited emergency. It has a medium score. It has a prerequisite. It is fixed in a stable release. In a rational world, that would be low drama.
The web is not a rational world. It is the largest remote code parsing surface most users expose every minute of the day. A medium browser bug in a sensitive boundary can deserve faster action than a higher-scored flaw in software that is rarely installed, rarely exposed, or difficult to exploit in practice.
For administrators, the work is less about clicking update and more about proving coverage. Patch status should be checked across stable, extended stable, beta, developer, and unmanaged installs. Remote workers and lightly managed devices deserve special attention because they are often the endpoints that miss relaunch deadlines.
Browser relaunch policy is also a security control. A fleet that downloads patches quickly but lets users run vulnerable browser processes for days is not really patched. Forced relaunches are annoying, but so is explaining why a known browser flaw remained live after the fix was available.
The same goes for vulnerability exception processes. If an organization defers this update because CVE-2026-7972 is “only medium,” it should document that decision against the full Chrome 148 security release, not against this single CVE in isolation. The release contains more serious fixes, and browser patch bundles should be evaluated as bundles.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
 The “Medium” Label Hides a Chainable Browser Problem
The “Medium” Label Hides a Chainable Browser Problem
CVE-2026-7972 is described as an uninitialized use issue in Chromium’s GPU component. In plainer terms, some piece of memory or state inside the graphics pipeline could be read before it was properly set to a known value. That can expose data the attacker should not be able to see.The important qualifier is that the attacker first needed to have compromised the renderer process. That condition lowers the standalone severity because the bug is not advertised as a one-click, fresh-from-the-Internet takeover of Chrome by itself. But it also tells us exactly why defenders should pay attention: renderer compromise is one of the most common stepping stones in browser exploit chains.
The browser security model assumes hostile web content will be processed constantly. Sandboxing, site isolation, renderer separation, and GPU process boundaries exist because the browser is now the operating system’s most exposed application surface. A flaw that leaks cross-origin data after renderer compromise may not be the first domino, but it can be the domino that turns code execution into useful intelligence.
That matters because “cross-origin data” is the phrase doing much of the work here. The web’s same-origin rules are supposed to prevent one site from reading another site’s data. If a crafted HTML page can help leak data across that boundary after the attacker has already gained a foothold, the bug becomes a confidentiality tool inside a broader attack.
The GPU Is No Longer Just a Fast Paintbrush
For years, GPU bugs were easy for ordinary users to misunderstand. The graphics stack sounded like a performance feature: video playback, animations, WebGL, WebGPU, canvas rendering, compositing, and hardware acceleration. If the browser drew a page quickly, the GPU had done its job.That framing is obsolete. The GPU process now sits close to complex web APIs, driver behavior, memory sharing, acceleration paths, and isolation boundaries. It is not merely drawing pixels; it is participating in a browser security architecture where performance shortcuts and memory lifetime bugs can become data exposure primitives.
Uninitialized-use bugs are especially awkward in this environment. They are not always dramatic crashes. Sometimes the program continues running while stale values, leftover memory, or undefined state become visible in ways the application never intended. In graphics workloads, where buffers are reused and timing-sensitive operations are routine, the difference between harmless residue and exploitable leakage can be thin.
This is why CVE-2026-7972 is more interesting than its score suggests. A CVSS 3.1 score of 4.3 says “medium,” and that is fair if the flaw requires user interaction and prior renderer compromise. But CVSS is a scoring language, not a threat model. It can tell you the shape of the vulnerability; it cannot tell you how attractive the bug is when paired with something else.
Chrome 148 Was a Security Release Wearing a Feature-Release Jacket
Chrome 148’s stable-channel promotion began on May 5, 2026, with versions 148.0.7778.96 for Linux and 148.0.7778.96/97 for Windows and macOS rolling out over days and weeks. Reporting around the release indicates that it fixed well over 100 security issues, including several critical vulnerabilities elsewhere in the browser. CVE-2026-7972 is one entry in a much larger patch train.That is both reassuring and frustrating. Reassuring, because the fix is already in the stable release. Frustrating, because browser patching has become so frequent that many users and even some organizations treat updates as background noise. Chrome says it will update itself, Edge says the same, and everyone assumes the fleet is fine until an inventory report proves otherwise.
The release cadence also complicates messaging. A user who hears “Chrome 148 fixed critical bugs” may update once and move on. An administrator who sees “CVE-2026-7972, medium severity” may decide it can wait until the next maintenance window. Both reactions miss the operational reality: the browser is a constantly attacked endpoint platform, and version drift is the enemy.
There is also the Chromium multiplier. Chrome is the original disclosure point, but Microsoft Edge, Brave, Opera, Vivaldi, and countless embedded Chromium runtimes inherit much of the same security terrain. Microsoft tracking the CVE through MSRC is not a footnote for Windows shops; it is a reminder that Chromium vulnerabilities do not stop at Chrome’s icon.
Microsoft’s Role Is a Distribution Problem, Not a Discovery Problem
The MSRC entry for CVE-2026-7972 matters because many Windows environments standardize on Edge, manage browser updates through policy, and report vulnerabilities through Microsoft-centered tooling. The underlying vulnerability comes from Chromium, but the Windows admin experience often runs through Microsoft’s release notes, update guide, Intune, Configuration Manager, Defender Vulnerability Management, or third-party scanners reading Microsoft metadata.That can create a dangerous kind of ambiguity. A vulnerability with “Chrome” in the source field may be mentally filed as “not our Microsoft problem,” while a vulnerability on the MSRC site may be assumed to arrive through Windows Update. Chromium-based Edge updates are their own channel. They can be managed well, but they must be managed deliberately.
This is where CPEs and affected-product records matter more than most people want to admit. The NVD change history indicates an affected Chrome configuration up to, but excluding, 148.0.7778.96 across Windows, Linux, and macOS. That is useful for scanners, but not enough for a Windows enterprise if the real asset question is “which Chromium runtimes are installed, which are actively used, and which are controlled by policy?”
The CPE question in the advisory is not academic. If vulnerability scanners lag behind vendor releases, mis-map Chromium forks, or miss unmanaged per-user browser installs, the dashboard can show green while exposed software remains on endpoints. This is one of the quiet failures of browser security: the patch exists, the version is known, and the fleet still contains ghosts.
Renderer Compromise Is the Clause That Should Make Admins Lean In
The description says the attacker needed to have compromised the renderer process. For non-specialists, that can sound like a big mitigating factor. After all, if the attacker already compromised something, why panic about a data leak?The answer is that modern browser exploits are built in layers. A renderer bug may provide initial code execution inside a sandboxed process. A second bug may escape the sandbox or leak information needed to defeat address-space layout randomization, bypass site isolation, or steal data that should remain behind an origin boundary. CVE-2026-7972 appears to belong in that second category of useful follow-on capability.
This is why defenders should resist the comfort of single-CVE thinking. Attackers do not care whether one CVE tells the whole story. They care whether multiple imperfect bugs can be chained into a reliable exploit. A medium confidentiality bug in the GPU process can be far more useful in a chain than a higher-scored denial-of-service bug that only crashes a tab.
There is no public indication, at the time of disclosure, that CVE-2026-7972 is being actively exploited in the wild. That is good news. But browser attackers prize bugs that help cross boundaries, and the combination of renderer compromise, crafted HTML, GPU behavior, and cross-origin data leakage is precisely the kind of recipe that should keep this out of the “patch someday” pile.
The Patch Window Is Short Because the Diff Becomes a Map
Browser vendors often restrict access to bug details until most users have updated, and for good reason. Once a patch is available, attackers can compare old and new code, identify the changed area, and infer the vulnerability. The clock does not start when a proof-of-concept appears on a paste site. It starts when the fix ships.That is especially true for Chromium. The project’s open-source nature is a security strength, but it also makes patch diffing part of the attacker workflow. When a stable release lands with dozens or hundreds of security fixes, defenders get broad protection; attackers get a menu of changed code to study.
CVE-2026-7972’s issue tracker entry requires permissions, which limits casual inspection. But the broader release still tells attackers where to look: GPU, uninitialized use, cross-origin data, renderer compromise, crafted HTML. That is not enough for easy exploitation, but it is enough to attract attention from researchers and offensive teams.
The practical implication is boring and unavoidable. Organizations should not wait for a weaponized exploit to care about the update. By the time exploit chatter becomes obvious, the easy patching window has already been wasted.
Windows Fleets Need Browser Version Truth, Not Update Faith
Most consumer Chrome installations will eventually move because Chrome’s updater is good at its job. Enterprise environments are messier. Devices sleep, users defer restarts, virtual desktops are snapshotted, app control policies interfere, golden images age, and some browsers are installed per-user outside the neat lanes of central management.For Chrome, the target version is 148.0.7778.96 or later on Linux and 148.0.7778.96/97 or later on Windows and macOS. For Edge, admins should verify the corresponding Chromium-based Edge release from Microsoft’s channel rather than assuming the Chrome version number maps one-for-one. The core task is to confirm that every supported Chromium browser has consumed the fix.
On Windows, the visible version number is only part of the story. Admins should also confirm that update services are healthy, policies are not pinning old versions, and browser relaunch prompts are not being ignored indefinitely. A browser that downloaded an update but has not restarted is still running the old code.
This is also a good moment to inventory Chromium-based applications beyond the main browser. Electron apps, embedded WebView2 runtimes, remote support tools, kiosk shells, and vendor-packaged Chromium components can broaden exposure in ways ordinary browser patch reports do not capture. Not every Chromium CVE applies equally to every embedded runtime, but assuming “we patched Chrome” equals “we patched Chromium” is too optimistic.
The Cross-Origin Angle Is the Real User-Facing Risk
The phrase “leak cross-origin data” sounds abstract until you translate it into what the web is supposed to protect. Your banking site, webmail, admin console, SaaS dashboard, identity provider, ticketing system, and internal portal all rely on browser-enforced separation. A malicious page should not be able to peer sideways into another site’s data simply because both are open in the same browser session.CVE-2026-7972 does not say that any random page can do that unaided. The attacker first needs renderer compromise. But in a chained scenario, cross-origin leakage can turn a technical foothold into something more valuable: tokens, page contents, identifiers, fragments of sensitive workflows, or information that helps the next stage of compromise.
For WindowsForum readers, this lands squarely in the everyday threat model. The browser is where Microsoft 365 sessions live. It is where Entra ID sign-ins happen. It is where admins open cloud consoles, RMM dashboards, firewall interfaces, password vaults, and helpdesk systems. Cross-origin boundaries are not theoretical; they are the walls between a malicious tab and the rest of a working day.
That is also why ordinary advice like “don’t visit suspicious sites” is insufficient. The exploit path requires user interaction, but modern phishing does not need to look suspicious. A crafted HTML page can arrive through a compromised legitimate site, a malicious ad chain, a fake meeting link, a poisoned search result, or a message that looks routine.
The CPE Gap Shows Why Vulnerability Management Still Trips Over Browsers
The user-facing advisory asks whether a CPE is missing, and the change history shows NIST adding Chrome configurations tied to Windows, Linux, and macOS. That detail exposes a broader weakness in vulnerability management: browsers are easy to name but surprisingly hard to model.A CPE can describe Google Chrome before a fixed version. It can describe the operating systems on which the application runs. But it may not represent every downstream Chromium consumer, every enterprise channel, every portable install, or every embedded runtime that security teams actually care about. Asset databases prefer neat product boxes; Chromium is an ecosystem.
This is where scanner output should be treated as evidence, not truth. If a scanner flags Chrome before 148.0.7778.96, believe it and patch. If a scanner does not flag a Chromium-based browser or runtime, do not automatically assume safety. Ask whether that product has shipped a Chromium update containing the fix.
The better enterprise posture is version-based and vendor-aware. Know which browsers are allowed, which update mechanisms are authoritative, which policies control relaunch, and which software bundles Chromium independently. CVE-2026-7972 is a medium-severity example of the same inventory problem that becomes urgent whenever Chromium ships a critical zero-day fix.
The Chrome Security Model Is Working, But It Is Also Showing Its Cost
It is tempting to read a 127-fix browser release as evidence that something is broken. In a sense, the opposite is true. A large, mature, heavily fuzzed, widely attacked codebase will produce a constant stream of bugs because the ecosystem is looking hard. Chrome’s security machinery finds, rewards, fixes, and ships patches at enormous scale.But the cost of that model is permanent operational churn. Users must relaunch. Admins must verify. Vendors downstream of Chromium must integrate. Security teams must triage a flood of CVEs whose individual severity scores do not always capture chainability. The machine works only if the last mile works.
CVE-2026-7972 illustrates this bargain well. The bug is not presented as an actively exploited emergency. It has a medium score. It has a prerequisite. It is fixed in a stable release. In a rational world, that would be low drama.
The web is not a rational world. It is the largest remote code parsing surface most users expose every minute of the day. A medium browser bug in a sensitive boundary can deserve faster action than a higher-scored flaw in software that is rarely installed, rarely exposed, or difficult to exploit in practice.
The Fix Is Simple, the Assurance Work Is Not
For individual users, the job is straightforward: update Chrome to version 148.0.7778.96/97 or later, then restart the browser. On Windows, Chrome’s Help About page remains the quickest way to force the check and confirm the version. Edge users should do the same through Edge’s About page and verify that Microsoft’s Chromium-based build has advanced to a fixed release.For administrators, the work is less about clicking update and more about proving coverage. Patch status should be checked across stable, extended stable, beta, developer, and unmanaged installs. Remote workers and lightly managed devices deserve special attention because they are often the endpoints that miss relaunch deadlines.
Browser relaunch policy is also a security control. A fleet that downloads patches quickly but lets users run vulnerable browser processes for days is not really patched. Forced relaunches are annoying, but so is explaining why a known browser flaw remained live after the fix was available.
The same goes for vulnerability exception processes. If an organization defers this update because CVE-2026-7972 is “only medium,” it should document that decision against the full Chrome 148 security release, not against this single CVE in isolation. The release contains more serious fixes, and browser patch bundles should be evaluated as bundles.
The Practical Read for WindowsForum Readers
The lesson from CVE-2026-7972 is not that every medium Chromium CVE is a five-alarm fire. It is that browser severity needs context, and this context is a GPU flaw that can leak cross-origin data after renderer compromise. That is enough to justify prompt action, especially because the remedy is already available.- Chrome users should move to 148.0.7778.96/97 or later and restart the browser so the patched code is actually running.
- Edge users should verify Microsoft’s corresponding Chromium-based update rather than assuming Windows Update alone has handled the browser.
- Administrators should inventory Chrome, Edge, and other Chromium-based software instead of relying only on one browser’s update status.
- Vulnerability teams should treat CPE data as a starting point and validate whether scanners detect unmanaged, portable, or embedded Chromium instances.
- Security teams should evaluate CVE-2026-7972 as part of the larger Chrome 148 security release, not as an isolated medium-severity curiosity.
- Users who keep privileged SaaS, admin, identity, or finance sessions open in the browser should be especially disciplined about browser restarts after security updates.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center