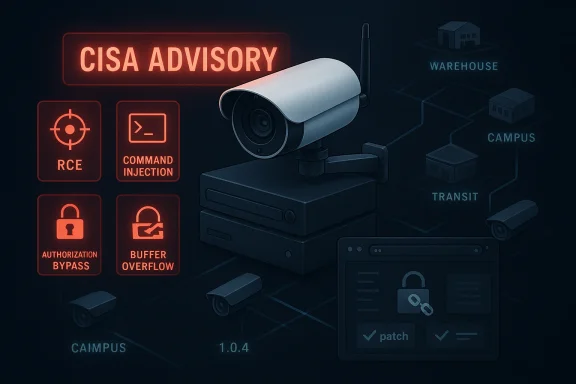
Milesight Cameras are back in the security spotlight with a sprawling CISA advisory that ties five CVE families to a wide range of AIoT, LPR, and network camera product lines, many of them still running firmware branches that can be exploited for device crashes or full remote code execution. CISA says successful exploitation could crash the device being accessed or allow remote code execution, and it also warns that the issue spans authorization bypass, hard-coded credentials, hard-coded cryptographic keys, OS command injection, and a heap-based buffer overflow. The advisory is especially notable because the affected fleet is broad, the severity is high, and the remediation path depends on careful version matching across many product families.
This disclosure matters because it is not a single bug in a single model line. It is a multi-CVE, multi-family security event affecting a large slice of Milesight’s camera and camera-adjacent portfolio, including models used in commercial facilities, public safety, transportation, and access-control-style deployments. CISA’s advisory lists products ranging from the MS-Cxx series to Nxxxx NVRs, TS series LPR devices, PMC/PM models, and smaller devices such as SC211 and SP111, with a common theme: firmware branches that need immediate attention if they sit at or below the vulnerable thresholds.
That breadth changes the operational picture. This is not the kind of issue an IT team can dismiss as “just a camera problem,” because modern cameras are often network endpoints with their own web interfaces, credentials, certificates, update logic, and sometimes analytics or access-control integrations. Once a device class like this becomes a management node, a recording endpoint, or a remote-visibility bridge, it stops being a passive sensor and becomes part of the trust boundary. That makes vulnerabilities in the firmware or embedded web server far more consequential than a simple image-quality bug or feature glitch.
The other reason this advisory stands out is the variety of weakness types. CISA’s summary groups the issues into categories that defenders dread in embedded products: user-controlled key handling, weak credential storage, default cryptographic material, unsafe command construction, and out-of-bounds memory access. In practical terms, that means attackers may have multiple paths to compromise, and defenders may need to close more than one failure mode before they can feel comfortable exposing the fleet to the network again.
For WindowsForum readers, the key takeaway is simple: if you manage Milesight gear anywhere in your environment, this is now a patch-and-verify moment, not a “wait for the next maintenance cycle” moment. CISA’s remediation guidance is explicit: update to the latest firmware versions published by the vendor, and confirm whether your exact model maps to the fixed build rather than assuming a nearby version is safe enough.
The affected product list in the advisory reflects that shift. The vulnerable families include multiple MS-C camera series, MS-N recorder/NVR lines, TS transport and license-plate recognition systems, PMC and PM products, and several niche hardware variants with firmware branches that are not obviously interchangeable. That matters because embedded fleets are rarely neat. They are usually a mixed population of models purchased over years, installed by different contractors, and updated on different schedules.
The practical challenge for defenders is inventory. A laptop or server fleet can often be enumerated by endpoint tooling, but surveillance and access-control devices are frequently scattered across buildings, closets, and remote sites with inconsistent documentation. If the organization does not know which exact Milesight model it has, it also cannot know whether the current firmware is safe, whether a vendor fix applies, or whether a device is running an older branch that needs a different remediation target. That is why advisories like this often expose a governance problem before they expose a code problem.
CISA’s advisory also underscores the role of firmware branch fragmentation. Some product lines are fixed at a specific revision increment, while others require a jump to a newer suffix, and a few families appear to have version ranges that are close enough to confuse rushed administrators. In the real world, that creates risk of partial patching, mistaken rollback, or the dangerous assumption that “updated this quarter” equals “secured.” The Milesight notice is a reminder that embedded software should be treated like any other critical infrastructure software: version precision matters.
There is also a broader historical lesson here. Camera and surveillance vendors have spent years adding smarter analytics, remote management, and cloud-adjacent functionality to products that were once far simpler. That convenience brings value, but it also imports all the usual risks of web applications, cryptography, and authenticated device management. When a single device family contains hard-coded credentials, default keys, and a command injection weakness, the problem is no longer just firmware maturity. It is a security architecture issue.
That mix tells a story. Weak key generation and default private keys are especially dangerous because they can undermine trust in the entire device identity model. Hard-coded credentials can survive long after a deployment changes hands, making them a long-tail exposure. Command injection and memory corruption, meanwhile, are the classic routes to active exploitation, persistence, or service disruption. Together, they create a layered risk profile that is much more serious than any one bug on its own.
For defenders, that means the risk is not limited to large enterprise camera installations. A small business or branch office with a handful of internet-reachable devices could be just as exposed if those devices are on an accessible VLAN, left on a public-facing management port, or integrated into a remote maintenance workflow. The absolute size of the deployment matters less than the quality of the exposure controls.
The advisory also includes CISA’s standard defensive recommendations for industrial and control-system devices: minimize network exposure, isolate systems behind firewalls, use VPNs only as part of broader defense-in-depth, and report suspicious activity through established channels. Those recommendations may sound routine, but they become urgent when the affected product line includes vulnerable web servers and hard-coded secrets.
The real significance here is that fleet owners cannot assume consistency across a brand family. Two cameras from the same vendor may require different remediation branches because they were built on different embedded platforms or product lines. That is why version mapping is such a critical part of incident response for surveillance hardware. A “Milesight camera” label is too broad to be operationally useful by itself.
That matters because downstream effects can include lost recordings, interrupted monitoring, or manipulated analytics. If a fleet includes plate-recognition devices or traffic-facing equipment, any downtime can disrupt both security coverage and operational reporting. In high-control environments, the camera is not a gadget. It is part of the evidence chain.
In practice, this is where many organizations get tripped up. The model might not look like a camera to the person responsible for patching, or it may be registered under a different internal naming convention than the vendor uses. That makes a clean asset inventory one of the most valuable response actions, even before firmware deployment begins.
Default private keys are equally troubling. They can allow attackers to impersonate the device or undermine encrypted connections if the same key material is reused broadly. Once certificate trust is weakened, the whole model of secure management, secure transport, and device authenticity becomes much harder to defend.
Weak key generation is more subtle but no less serious. If a device generates predictable or insufficiently random secrets, attackers may be able to reconstruct cryptographic state or derive trust material more easily than defenders expect. That kind of flaw is often invisible in everyday operation, which makes it dangerous precisely because it does not announce itself.
The heap-based buffer overflow and out-of-bounds memory access issues are also serious because they open the door to crashes, denial of service, or, depending on conditions, code execution. Even if exploitation is imperfect, repeated crashes on a security camera can blind a facility or create a denial-of-monitoring condition at the worst possible time. The operational effect can be just as painful as a full compromise.
The authorization-bypass issue, classified as CWE-639, is another reminder that broken access control can be just as dangerous as memory corruption. If an attacker can control a key parameter or identity value, they may be able to retrieve or act on resources they should never reach. That makes authorization flaws a force multiplier for the rest of the vulnerability set.
Another concern is reputation and evidentiary integrity. If an attacker can tamper with recordings, disable feeds, or inject instability into the device, the organization may lose confidence in footage that should have been trusted as evidence. That creates security, legal, and operational consequences at the same time, which is exactly why surveillance vulnerabilities often punch above their technical weight.
This is especially true when cameras are integrated into broader physical security ecosystems. If a monitoring platform trusts the camera identity or the management interface, a compromised device can become a way to poison the wider system. That is one reason why embedded security should be treated as part of enterprise risk management, not just facilities maintenance.
In distributed deployments, the challenge is often inconsistent ownership. One site may patch quickly, another may not know what model it has, and a third may depend on a contractor who is slow to respond. That operational fragmentation is a defender’s enemy, because attackers only need one unpatched device to matter.
The third priority is trust reset. Devices with hard-coded credentials or default private keys may need more than a software update. Administrators should check whether secrets must be rotated, whether certificates need replacement, and whether any management account assumptions were built on vendor-supplied defaults. That is the uncomfortable part of embedded remediation: the fix can be partly procedural, not just binary.
The other opportunity is organizational. A vulnerability wave like this can justify a broader cleanup of surveillance governance, especially around segmentation, ownership, and remote-access policy. If security teams use the incident to improve asset inventory and reduce unnecessary exposure, the long-term payoff will be larger than the immediate patch.
Another concern is that some of the vulnerabilities may leave lasting residue even after patching. Hard-coded credentials, default certificates, and weak key material can survive in backups, configurations, or operational habits unless someone actively resets them. In other words, a successful remediation can still leave behind a compromised trust model if teams only update the firmware and stop there.
The second thing to watch is whether Milesight’s firmware branches behave uniformly across the affected families. In embedded environments, a vendor may publish a fixed build for one line while another line requires a different packaging or suffix, and that can slow remediation. If new guidance appears, it will likely be about exact model-to-build matching rather than the existence of a fix itself.
The third thing to watch is whether additional device categories tied to the same platform or codebase surface with parallel issues. Broad embedded fleets often share cryptographic, web, or identity components across multiple product lines, so one advisory sometimes foreshadows more. That is why teams should treat this as a family-level trust event, not a one-off camera bug.
Source: CISA Milesight Cameras | CISA
 Overview
Overview
This disclosure matters because it is not a single bug in a single model line. It is a multi-CVE, multi-family security event affecting a large slice of Milesight’s camera and camera-adjacent portfolio, including models used in commercial facilities, public safety, transportation, and access-control-style deployments. CISA’s advisory lists products ranging from the MS-Cxx series to Nxxxx NVRs, TS series LPR devices, PMC/PM models, and smaller devices such as SC211 and SP111, with a common theme: firmware branches that need immediate attention if they sit at or below the vulnerable thresholds.That breadth changes the operational picture. This is not the kind of issue an IT team can dismiss as “just a camera problem,” because modern cameras are often network endpoints with their own web interfaces, credentials, certificates, update logic, and sometimes analytics or access-control integrations. Once a device class like this becomes a management node, a recording endpoint, or a remote-visibility bridge, it stops being a passive sensor and becomes part of the trust boundary. That makes vulnerabilities in the firmware or embedded web server far more consequential than a simple image-quality bug or feature glitch.
The other reason this advisory stands out is the variety of weakness types. CISA’s summary groups the issues into categories that defenders dread in embedded products: user-controlled key handling, weak credential storage, default cryptographic material, unsafe command construction, and out-of-bounds memory access. In practical terms, that means attackers may have multiple paths to compromise, and defenders may need to close more than one failure mode before they can feel comfortable exposing the fleet to the network again.
For WindowsForum readers, the key takeaway is simple: if you manage Milesight gear anywhere in your environment, this is now a patch-and-verify moment, not a “wait for the next maintenance cycle” moment. CISA’s remediation guidance is explicit: update to the latest firmware versions published by the vendor, and confirm whether your exact model maps to the fixed build rather than assuming a nearby version is safe enough.
Background
Milesight’s camera ecosystem is a good example of how embedded products evolve into enterprise infrastructure. Cameras once existed primarily as standalone surveillance devices, but in 2026 they are more often integrated into video management platforms, access-control systems, analytics pipelines, and operational technology networks. That means a camera firmware issue can affect not only security footage, but also authentication, perimeter monitoring, license-plate workflows, and incident response processes.The affected product list in the advisory reflects that shift. The vulnerable families include multiple MS-C camera series, MS-N recorder/NVR lines, TS transport and license-plate recognition systems, PMC and PM products, and several niche hardware variants with firmware branches that are not obviously interchangeable. That matters because embedded fleets are rarely neat. They are usually a mixed population of models purchased over years, installed by different contractors, and updated on different schedules.
The practical challenge for defenders is inventory. A laptop or server fleet can often be enumerated by endpoint tooling, but surveillance and access-control devices are frequently scattered across buildings, closets, and remote sites with inconsistent documentation. If the organization does not know which exact Milesight model it has, it also cannot know whether the current firmware is safe, whether a vendor fix applies, or whether a device is running an older branch that needs a different remediation target. That is why advisories like this often expose a governance problem before they expose a code problem.
CISA’s advisory also underscores the role of firmware branch fragmentation. Some product lines are fixed at a specific revision increment, while others require a jump to a newer suffix, and a few families appear to have version ranges that are close enough to confuse rushed administrators. In the real world, that creates risk of partial patching, mistaken rollback, or the dangerous assumption that “updated this quarter” equals “secured.” The Milesight notice is a reminder that embedded software should be treated like any other critical infrastructure software: version precision matters.
There is also a broader historical lesson here. Camera and surveillance vendors have spent years adding smarter analytics, remote management, and cloud-adjacent functionality to products that were once far simpler. That convenience brings value, but it also imports all the usual risks of web applications, cryptography, and authenticated device management. When a single device family contains hard-coded credentials, default keys, and a command injection weakness, the problem is no longer just firmware maturity. It is a security architecture issue.
What the advisory actually says
CISA says the Milesight camera issues could let an attacker crash the device or gain remote code execution, which is the kind of language defenders should read as “assume compromise potential, not just instability.” The advisory also marks the product status as known_affected, which removes any ambiguity about whether the issue is theoretical. These are not speculative weaknesses; they are recognized and tracked vulnerabilities with explicit remediation guidance.The CVE cluster
The five named CVEs are significant because they represent different failure classes, not one repeated mistake. CVE-2026-28747 is described as a weak key generation issue tied to specific firmware versions. CVE-2026-27785 involves hard-coded credentials. CVE-2026-32644 uses SSL certificates with default private keys. CVE-2026-32649 is a command injection flaw in the web server. CVE-2026-20766 is an out-of-bounds memory access issue.That mix tells a story. Weak key generation and default private keys are especially dangerous because they can undermine trust in the entire device identity model. Hard-coded credentials can survive long after a deployment changes hands, making them a long-tail exposure. Command injection and memory corruption, meanwhile, are the classic routes to active exploitation, persistence, or service disruption. Together, they create a layered risk profile that is much more serious than any one bug on its own.
Severity and exploitation implications
The severity mix in the advisory is also worth noting. CISA reports multiple high-severity entries, including CVSS 9.8 for the hard-coded credentials and command injection issues, while the authorization-bypass flaw is scored 7.1 HIGH and the out-of-bounds issue is scored 8.8 HIGH. In other words, the most dangerous bugs are not abstract hardening concerns; they are network-reachable and likely to matter quickly if exposed.For defenders, that means the risk is not limited to large enterprise camera installations. A small business or branch office with a handful of internet-reachable devices could be just as exposed if those devices are on an accessible VLAN, left on a public-facing management port, or integrated into a remote maintenance workflow. The absolute size of the deployment matters less than the quality of the exposure controls.
The advisory also includes CISA’s standard defensive recommendations for industrial and control-system devices: minimize network exposure, isolate systems behind firewalls, use VPNs only as part of broader defense-in-depth, and report suspicious activity through established channels. Those recommendations may sound routine, but they become urgent when the affected product line includes vulnerable web servers and hard-coded secrets.
Affected product families
One of the hardest parts of this advisory is simply reading the affected list carefully enough to know what is in scope. The list spans camera families, transport-focused devices, LPR systems, NVRs, and specialized hardware series with model-number patterns that can be easy to misclassify during inventory. The advisory names dozens of affected versions, and each one maps to a specific fixed build or later revision.Camera and imaging lines
The camera families include models such as MS-Cxx63-PD, MS-Cxx64-xPD, MS-Cxx73-xPD, MS-Cxx75-xxPD, MS-Cxx83-xPD, MS-C8477-HPG1, MS-C8477-PC, and several MS-Cxx and MS-CQxx series. For many of those, the vulnerable threshold sits at or below a firmware release in the 51.x, 61.x, 63.x, or 48.x branches. That means some sites may need multiple update paths, depending on which camera generation they deployed.The real significance here is that fleet owners cannot assume consistency across a brand family. Two cameras from the same vendor may require different remediation branches because they were built on different embedded platforms or product lines. That is why version mapping is such a critical part of incident response for surveillance hardware. A “Milesight camera” label is too broad to be operationally useful by itself.
NVR, LPR, and transport-oriented devices
The list also includes MS-Nxxxx recorder-style devices, TS transport and recognition systems, and LPR-focused models such as PMC8266-FPE, PMC8266-FGPE, and PM3322-E. These are not just passive video products; in many deployments they sit adjacent to physical security workflows, site access, or vehicle recognition systems. A compromise here can create a wider operational impact than the word “camera” suggests.That matters because downstream effects can include lost recordings, interrupted monitoring, or manipulated analytics. If a fleet includes plate-recognition devices or traffic-facing equipment, any downtime can disrupt both security coverage and operational reporting. In high-control environments, the camera is not a gadget. It is part of the evidence chain.
Smaller and specialized devices
CISA also lists smaller devices such as SC211 and SP111, along with RF and AIoT package variants like MS-Cxx66-RFIPKG1, MS-Cxx72-RFIPKG1, MS-Cxx66-FIPKG1, and MS-Cxx72-FIPKG1. These product identifiers are a clue that remediation may touch different packaging schemes, not just visible camera models. That increases the odds of overlooked assets sitting in storage, in remote offices, or in contractor-managed environments.In practice, this is where many organizations get tripped up. The model might not look like a camera to the person responsible for patching, or it may be registered under a different internal naming convention than the vendor uses. That makes a clean asset inventory one of the most valuable response actions, even before firmware deployment begins.
Why the flaws are dangerous
The combination of hard-coded credentials, default cryptographic keys, and weak key generation is the kind of thing that should make any security team slow down and re-evaluate trust assumptions. These issues can persist across resets, backups, or redeployments, which means patching alone may not be enough if secrets were already exposed. The device may be fixed in code while remaining compromised in practice.Identity and trust failure
Hard-coded credentials are especially risky because they often scale silently. If one attacker learns the credential, every device or instance that shares it may be vulnerable until it is replaced or rotated. That turns a single disclosure into a fleet-wide trust collapse, which is why credential hygiene is so central to embedded security.Default private keys are equally troubling. They can allow attackers to impersonate the device or undermine encrypted connections if the same key material is reused broadly. Once certificate trust is weakened, the whole model of secure management, secure transport, and device authenticity becomes much harder to defend.
Weak key generation is more subtle but no less serious. If a device generates predictable or insufficiently random secrets, attackers may be able to reconstruct cryptographic state or derive trust material more easily than defenders expect. That kind of flaw is often invisible in everyday operation, which makes it dangerous precisely because it does not announce itself.
Active exploitation paths
The OS command injection issue is the most obviously exploitable of the group because it can turn malformed input into execution on the device itself. When command injection exists in a web server, it often means the management interface can be abused without needing physical access or local compromise. That is a classic route from network interaction to device takeover.The heap-based buffer overflow and out-of-bounds memory access issues are also serious because they open the door to crashes, denial of service, or, depending on conditions, code execution. Even if exploitation is imperfect, repeated crashes on a security camera can blind a facility or create a denial-of-monitoring condition at the worst possible time. The operational effect can be just as painful as a full compromise.
The authorization-bypass issue, classified as CWE-639, is another reminder that broken access control can be just as dangerous as memory corruption. If an attacker can control a key parameter or identity value, they may be able to retrieve or act on resources they should never reach. That makes authorization flaws a force multiplier for the rest of the vulnerability set.
Enterprise and infrastructure impact
The Milesight advisory is clearly an enterprise and infrastructure problem, even if the affected devices are often purchased through ordinary commercial channels. CISA places the issue in the Commercial Facilities sector and notes worldwide deployment, which means the same model could be running in warehouses, campuses, retail sites, transportation nodes, and public buildings. That kind of distribution makes patch management far harder than in a conventional server environment.Enterprise risk
In enterprise settings, the biggest danger is often not the camera itself but the management path around it. Many organizations centralize surveillance administration through browser-based consoles, vendor tooling, or remote support channels, and those pathways can become a soft underbelly if hard-coded credentials or weak certificate handling exist underneath. A compromised camera may also provide a foothold into adjacent segments if the network is not tightly segmented.Another concern is reputation and evidentiary integrity. If an attacker can tamper with recordings, disable feeds, or inject instability into the device, the organization may lose confidence in footage that should have been trusted as evidence. That creates security, legal, and operational consequences at the same time, which is exactly why surveillance vulnerabilities often punch above their technical weight.
Industrial and commercial facility risk
In commercial facilities, the risk extends to safety and continuity. Cameras and LPR devices are often used for situational awareness, perimeter detection, vehicle tracking, and access control. A successful exploit can therefore do more than interrupt a feed; it can degrade the organization’s ability to understand what is happening on site in real time.This is especially true when cameras are integrated into broader physical security ecosystems. If a monitoring platform trusts the camera identity or the management interface, a compromised device can become a way to poison the wider system. That is one reason why embedded security should be treated as part of enterprise risk management, not just facilities maintenance.
Small and distributed deployments
Small deployments may feel the impact as reliability first and security second. A branch office may not think of one camera as critical infrastructure, but if that camera covers a loading dock, cash-handling area, or access point, the business effect is immediate. Smaller organizations also tend to have weaker segmentation, which can leave cameras more exposed than intended.In distributed deployments, the challenge is often inconsistent ownership. One site may patch quickly, another may not know what model it has, and a third may depend on a contractor who is slow to respond. That operational fragmentation is a defender’s enemy, because attackers only need one unpatched device to matter.
Response priorities
The first response priority is inventory. Before anyone can patch a Milesight environment, they have to know which models exist, where they are installed, and what firmware they are running. Without that, remediation becomes guesswork, and guesswork is a poor strategy for embedded devices that may be reachable from multiple internal or external networks.Immediate actions
- Identify every Milesight camera, recorder, transport device, and related appliance in the environment.
- Record the exact model and firmware version for each device.
- Compare each device against the affected version thresholds in the advisory.
- Remove or restrict internet exposure immediately.
- Apply vendor updates to the first fixed version or later build for the exact product line.
- Validate that credentials, certificates, and access controls were not already compromised.
- Review logs or monitoring data for abnormal requests, crashes, or unexpected management activity.
The third priority is trust reset. Devices with hard-coded credentials or default private keys may need more than a software update. Administrators should check whether secrets must be rotated, whether certificates need replacement, and whether any management account assumptions were built on vendor-supplied defaults. That is the uncomfortable part of embedded remediation: the fix can be partly procedural, not just binary.
Strengths and Opportunities
There is one helpful aspect to this disclosure: the advisory is specific enough to support real action. CISA gives version thresholds, affected product families, and vendor-recommended firmware targets, which means defenders can move from vague concern to a concrete patch plan. That clarity is valuable, especially in environments where camera fleets are usually under-inventoried and over-trusted.The other opportunity is organizational. A vulnerability wave like this can justify a broader cleanup of surveillance governance, especially around segmentation, ownership, and remote-access policy. If security teams use the incident to improve asset inventory and reduce unnecessary exposure, the long-term payoff will be larger than the immediate patch.
- Clear affected-version thresholds reduce ambiguity.
- Vendor firmware targets are already published.
- The issue can drive better camera inventory hygiene.
- Segmentation work will pay off beyond this advisory.
- Certificate and credential review can improve trust posture.
- Remote-access paths can be tightened while patching.
- Security teams can use the event to reset ownership of embedded assets.
Risks and Concerns
The biggest concern is that surveillance devices often live in plain sight while remaining poorly managed. Organizations know they have cameras, but they may not know which models are on which firmware branch or whether management interfaces are reachable from broader internal networks. That visibility gap is exactly what turns a public advisory into a real incident.Another concern is that some of the vulnerabilities may leave lasting residue even after patching. Hard-coded credentials, default certificates, and weak key material can survive in backups, configurations, or operational habits unless someone actively resets them. In other words, a successful remediation can still leave behind a compromised trust model if teams only update the firmware and stop there.
- Hidden or poorly labeled devices may be missed.
- Internal-only assumptions may be false.
- Credential reuse can outlive the firmware fix.
- Certificate trust may need to be rebuilt.
- Flat networks can spread the blast radius.
- Contractors may control devices the owner does not fully track.
- Logging may be too sparse to reconstruct abuse.
Looking Ahead
The next thing to watch is how quickly organizations can map the advisory’s version list to real-world fleets. If defenders have clean inventories, this becomes a manageable patching event. If they do not, the advisory will expose how much surveillance infrastructure has been left outside standard vulnerability management.The second thing to watch is whether Milesight’s firmware branches behave uniformly across the affected families. In embedded environments, a vendor may publish a fixed build for one line while another line requires a different packaging or suffix, and that can slow remediation. If new guidance appears, it will likely be about exact model-to-build matching rather than the existence of a fix itself.
The third thing to watch is whether additional device categories tied to the same platform or codebase surface with parallel issues. Broad embedded fleets often share cryptographic, web, or identity components across multiple product lines, so one advisory sometimes foreshadows more. That is why teams should treat this as a family-level trust event, not a one-off camera bug.
- Confirm exact model and firmware for every device.
- Compare each device against the vendor fix version.
- Remove unnecessary external or wide internal exposure.
- Rotate credentials and certificates where appropriate.
- Monitor for crashes, weird reboots, or admin anomalies.
- Watch for follow-on advisories affecting related product lines.
Source: CISA Milesight Cameras | CISA