The latest CISA industrial control systems advisory puts a sharp spotlight on Contemporary Controls BASC-20T and, more specifically, on an old building automation controller that should probably never have been left to age quietly on live networks. According to the advisory, successful exploitation could let an attacker enumerate device functionality, reconfigure components, rename and delete objects, transfer files, and issue remote procedure calls. The affected product is BASControl20 3.1, and CISA says the BASC-20T is now obsolete, which makes the warning feel less like a routine patch notice and more like a late-stage wake-up call for operators running legacy building systems.
This is a familiar story in industrial and building automation, but it is still an uncomfortable one. A device that once solved a practical control problem is now carrying a modern cybersecurity burden that its original design never anticipated. CISA’s advisory frames the issue as CWE-807, Reliance on Untrusted Inputs in a Security Decision, a classification that usually means an attacker can influence security-relevant logic with data the system should not trust. In plain English, if the controller believes network traffic too readily, the attacker may be able to impersonate legitimate activity.
The product at the center of this advisory sits in an important, but often overlooked, category: building automation and control. Contemporary Controls’ BASautomation line is used in environments where HVAC, energy management, and other facility functions are increasingly connected to IP networks. That connectivity has obvious operational benefits, but it also means the old assumption that “this box lives safely behind a panel door” no longer holds. Once a controller is reachable on a network, it becomes part of the broader attack surface, whether the operator intended that or not.
CISA’s notice is also notable for what it does not say. It does not describe active public exploitation, and it does not point to a vendor-issued patch for the affected product line. Instead, the remediation guidance says Contemporary Controls considers the BASC-20T obsolete and advises users to contact the company for additional information. That is not much comfort to a facility manager who may still depend on the controller to keep air handling, zone control, or other building systems operational.
The advisory lands in a broader context that has become increasingly hard to ignore: critical infrastructure operators are being forced to balance uptime against security on systems that are often older than the cybersecurity controls protecting them. CISA’s recommended practices for control systems read like a checklist for surviving legacy exposure: isolate control networks, minimize internet exposure, use firewalls and segmented architecture, and approach remote access with caution. Those are not new ideas, but they remain essential because the underlying device base is still full of old hardware, long lifecycles, and thin margins for downtime.
The severity is equally plain: CVSS 3.1 base score 9.8, Critical. That score reflects a network-exploitable flaw with no privileges required, no user interaction, and high impact to confidentiality, integrity, and availability. For an ICS or building-management asset, that combination is especially concerning because operators rarely want to discover that a device can be remotely manipulated only after it has been integrated into a live building network.
In a building automation controller, the practical consequence can be worse than just unauthorized viewing. If the attacker can persuade the controller to act on forged traffic, they may be able to alter device state, rename objects, delete entries, or trigger functions meant for legitimate administrators. That makes the issue more than a confidentiality problem; it is an integrity and availability problem in a control environment where wrong state can become physical consequence.
Obsolete controllers also linger because they are operationally “good enough.” If the device controls a stable building subsystem, it may run for years without obvious issues. The problem is that security weaknesses accumulate invisibly while the system appears to work normally. That is how quiet exposure becomes a major risk: an administrator may not notice the danger until the network changes around the controller, not the controller itself.
The BASautomation catalog still positions Contemporary Controls’ building automation line as a practical product family with support materials and replacement information, which shows that the vendor ecosystem still exists even if one specific controller model is obsolete. That creates a common transition pattern: the product family remains current enough to support migration, but the original deployed unit is now a liability. This is often how legacy OT exposure ends up persisting longer than it should.
The hidden cost is that legacy controllers often sit close to business networks, especially in buildings where facilities and IT have grown together over time. That overlap means an attacker who reaches a flat network or exposed port may not need a sophisticated foothold to start probing. In that sense, the BASC-20T advisory is also a warning about network design debt.
This is one reason the advisory’s recommended protections emphasize isolation. If the controller is not reachable from broad business networks, and if remote access is tightly constrained, the attacker’s path becomes much narrower. A fragile packet trust model is much less dangerous when the device is not sitting on a large, permissive flat subnet.
The practical risk here is not limited to one kind of malicious action. An adversary might use unauthorized requests to map the device, then selectively disrupt configurations to cause subtle operational effects. That could be more damaging than an obvious outage because misconfiguration in a building system may show up as comfort complaints, energy anomalies, or intermittent failures rather than a clean alarm.
The practical consequence is that a flaw in one controller can ripple outward. If one building management device is compromised, the attacker may use it as an anchor point for persistence, reconnaissance, or pivoting to adjacent systems. That’s why CISA’s guidance does not frame the issue as merely a product bug; it treats it as a network exposure problem that must be managed through architecture.
The more connected these systems become, the more they inherit familiar IT threats: unauthorized discovery, spoofing, packet manipulation, and privilege abuse. But they also bring unique constraints: long replacement cycles, specialized service dependencies, and limited maintenance windows. In practice, that makes vulnerability response slower and more complicated than in standard enterprise environments.
From a procurement standpoint, this also reinforces the idea that building controls should be bought with a support lifecycle in mind. A controller that looks inexpensive at installation can become expensive the moment it crosses into unsupported territory. That is the real lesson of obsolete OT: the upfront savings often become future remediation debt.
Remote access is the other major concern. CISA recommends using more secure methods such as VPNs, while also warning that VPNs can have vulnerabilities and are only as secure as the connected devices. That last caveat is critical: remote access can be a force multiplier for maintenance, but it can also become the easiest path to compromise when the endpoint and controller trust model is weak.
CISA also reminds organizations to perform proper impact analysis and risk assessment before deploying defensive measures. That is a subtle but important point. Overcorrecting in a building environment can create physical inconvenience or operational outages, so security teams need to validate changes carefully rather than treat isolation as a one-click fix.
At the same time, “obsolete” should not be confused with “ignored.” In industrial environments, vendors often still support migration paths, replacement families, or service advice for retired products. Contemporary Controls’ BASautomation materials still reference BAScontrol20 and related products in its catalog ecosystem, reinforcing the idea that users may need to move rather than simply patch.
For operators, the real question is whether the device is sufficiently isolated to buy time for replacement. If it is not, then the organization is carrying a risk that will only get harder to manage. Legacy plus exposure is the worst combination in building automation, and that is exactly what this advisory highlights.
That said, the vulnerability is serious enough that it should not be triaged as “theoretical.” CISA explicitly says exploitation could permit a wide range of administrative or manipulative actions. When the impact includes reconfiguration, deletion, file transfer, and RPC-style access, the burden shifts to the defender to prove the system is not exposed.
The second step is exposure review. If the device is reachable outside a tightly controlled management path, the risk rises sharply. If the network is already segmented and the controller is being phased out, the organization still has work to do, but the response can be more measured. Visibility first, then containment is the right sequence here.
The third step is replacement planning. If the controller is truly obsolete, then mitigation is not the endgame; it is the bridge. Security teams that stop at firewall rules often end up revisiting the same risk later, under more pressure and with fewer options.
CISA’s advisory may also prompt a wider conversation about how many legacy controllers remain in service across commercial and industrial properties. That is the uncomfortable question every building operator eventually faces: if one obsolete controller is exposed, how many similar devices are waiting in adjacent closets, panels, and mechanical rooms? The answer is usually more than one.
Source: CISA Contemporary Controls BASC 20T | CISA
 Overview
Overview
This is a familiar story in industrial and building automation, but it is still an uncomfortable one. A device that once solved a practical control problem is now carrying a modern cybersecurity burden that its original design never anticipated. CISA’s advisory frames the issue as CWE-807, Reliance on Untrusted Inputs in a Security Decision, a classification that usually means an attacker can influence security-relevant logic with data the system should not trust. In plain English, if the controller believes network traffic too readily, the attacker may be able to impersonate legitimate activity.The product at the center of this advisory sits in an important, but often overlooked, category: building automation and control. Contemporary Controls’ BASautomation line is used in environments where HVAC, energy management, and other facility functions are increasingly connected to IP networks. That connectivity has obvious operational benefits, but it also means the old assumption that “this box lives safely behind a panel door” no longer holds. Once a controller is reachable on a network, it becomes part of the broader attack surface, whether the operator intended that or not.
CISA’s notice is also notable for what it does not say. It does not describe active public exploitation, and it does not point to a vendor-issued patch for the affected product line. Instead, the remediation guidance says Contemporary Controls considers the BASC-20T obsolete and advises users to contact the company for additional information. That is not much comfort to a facility manager who may still depend on the controller to keep air handling, zone control, or other building systems operational.
The advisory lands in a broader context that has become increasingly hard to ignore: critical infrastructure operators are being forced to balance uptime against security on systems that are often older than the cybersecurity controls protecting them. CISA’s recommended practices for control systems read like a checklist for surviving legacy exposure: isolate control networks, minimize internet exposure, use firewalls and segmented architecture, and approach remote access with caution. Those are not new ideas, but they remain essential because the underlying device base is still full of old hardware, long lifecycles, and thin margins for downtime.
What the advisory says
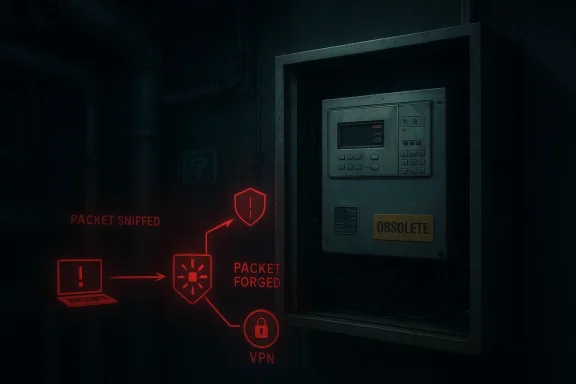
CISA’s advisory is unusually direct about the impact of exploitation. The issue is described as an attacker being able to use sniffed network traffic to forge packets and make arbitrary requests to the BASC-20T. That matters because it suggests the vulnerability is not simply about a malformed request crashing a service; it is about a broader trust failure in how the controller interprets traffic. In operational terms, that can translate into unauthorized configuration changes and data manipulation.The severity is equally plain: CVSS 3.1 base score 9.8, Critical. That score reflects a network-exploitable flaw with no privileges required, no user interaction, and high impact to confidentiality, integrity, and availability. For an ICS or building-management asset, that combination is especially concerning because operators rarely want to discover that a device can be remotely manipulated only after it has been integrated into a live building network.
Key advisory details
The most important facts are straightforward, but they tell a larger story when viewed together.- Affected product: Contemporary Controls BASC-20T / BASControl20 3.1.
- CVE: CVE-2025-13926.
- CWE: CWE-807, reliance on untrusted inputs in a security decision.
- Severity: CVSS 9.8 Critical.
- Operational effect: unauthorized requests, file operations, reconfiguration, and RPC-style actions.
Why CWE-807 matters
CWE-807 is one of those weakness categories that sounds abstract until you translate it into operational risk. It describes a product that relies on input values or signals from a source it should not fully trust. MITRE’s definition is concise: the security mechanism can be bypassed because the input can be modified by an untrusted actor. That is precisely the kind of defect that becomes dangerous on an ICS network, where packets often carry administrative intent and authenticity assumptions are baked deep into device behavior.In a building automation controller, the practical consequence can be worse than just unauthorized viewing. If the attacker can persuade the controller to act on forged traffic, they may be able to alter device state, rename objects, delete entries, or trigger functions meant for legitimate administrators. That makes the issue more than a confidentiality problem; it is an integrity and availability problem in a control environment where wrong state can become physical consequence.
Why obsolete controllers are so risky
The word obsolete changes the tone of this advisory. When a product is no longer actively maintained, security teams lose the most important response option: a patch. That pushes mitigation toward compensating controls, segmentation, and replacement planning, all of which are harder to execute quickly in a live facility. It is one thing to patch a workstation fleet; it is another to replace a controller embedded in building operations.Obsolete controllers also linger because they are operationally “good enough.” If the device controls a stable building subsystem, it may run for years without obvious issues. The problem is that security weaknesses accumulate invisibly while the system appears to work normally. That is how quiet exposure becomes a major risk: an administrator may not notice the danger until the network changes around the controller, not the controller itself.
Legacy technology and real-world inertia
Industrial and building automation teams often inherit systems rather than design them from scratch. The controller may be tied to a vendor-specific configuration workflow, paired with older engineering software, or dependent on spare parts that are already difficult to source. In that environment, “replace it immediately” sounds like a security recommendation but behaves like a capital project.The BASautomation catalog still positions Contemporary Controls’ building automation line as a practical product family with support materials and replacement information, which shows that the vendor ecosystem still exists even if one specific controller model is obsolete. That creates a common transition pattern: the product family remains current enough to support migration, but the original deployed unit is now a liability. This is often how legacy OT exposure ends up persisting longer than it should.
Operational implications
For operators, the difficult part is not understanding the risk in theory. It is deciding how to tolerate it while keeping the lights on, the air conditioning running, and maintenance crews from being called in at the worst possible time. That means controls need to be introduced carefully, ideally during maintenance windows and with a clear rollback plan. The security fix may be architectural, not software-based.The hidden cost is that legacy controllers often sit close to business networks, especially in buildings where facilities and IT have grown together over time. That overlap means an attacker who reaches a flat network or exposed port may not need a sophisticated foothold to start probing. In that sense, the BASC-20T advisory is also a warning about network design debt.
The attack path CISA is warning about
The advisory’s description suggests a classic trust breakdown: an attacker can sniff network traffic, then forge packets that the device accepts as legitimate. That is not the same as blind remote exploitation over the internet; it implies some ability to observe or position traffic, which often points to local network access, lateral movement, or a compromised adjacent system. Even so, once that foothold exists, the impact could be severe.This is one reason the advisory’s recommended protections emphasize isolation. If the controller is not reachable from broad business networks, and if remote access is tightly constrained, the attacker’s path becomes much narrower. A fragile packet trust model is much less dangerous when the device is not sitting on a large, permissive flat subnet.
From sniffing to control
The exploit chain described by CISA reads like a sequence that control-system defenders know well:- Observe or intercept relevant traffic.
- Reconstruct enough of the protocol or session state to look legitimate.
- Forge requests accepted by the controller.
- Use those requests to enumerate, alter, or delete functions and data.
The practical risk here is not limited to one kind of malicious action. An adversary might use unauthorized requests to map the device, then selectively disrupt configurations to cause subtle operational effects. That could be more damaging than an obvious outage because misconfiguration in a building system may show up as comfort complaints, energy anomalies, or intermittent failures rather than a clean alarm.
Possible attacker outcomes
- Enumerating controller functionality.
- Reconfiguring points or components.
- Renaming or deleting objects.
- Transferring files.
- Issuing remote procedure calls.
Why this matters for building automation
Building automation systems occupy a strange middle ground between IT and OT. They do not get the same security attention as enterprise servers, but they increasingly sit on the same network fabric and often use the same supporting infrastructure. Contemporary Controls has long marketed BASautomation as a family for BACnet and Sedona environments, and that makes the BASC-20T representative of a whole class of embedded building devices that were designed for utility first and hardening second.The practical consequence is that a flaw in one controller can ripple outward. If one building management device is compromised, the attacker may use it as an anchor point for persistence, reconnaissance, or pivoting to adjacent systems. That’s why CISA’s guidance does not frame the issue as merely a product bug; it treats it as a network exposure problem that must be managed through architecture.
Building systems are not just “facilities”
In modern facilities, the line between comfort control and business continuity has become thinner. HVAC failures can affect tenant productivity, server room cooling, clean-room tolerances, and energy costs. So even if a compromised BAS controller does not directly endanger public safety, it can still have a serious operational footprint. That is especially true in Critical Manufacturing and Energy contexts, where process stability matters.The more connected these systems become, the more they inherit familiar IT threats: unauthorized discovery, spoofing, packet manipulation, and privilege abuse. But they also bring unique constraints: long replacement cycles, specialized service dependencies, and limited maintenance windows. In practice, that makes vulnerability response slower and more complicated than in standard enterprise environments.
Enterprise versus consumer impact
This advisory is clearly aimed at organizations, not consumers, but the distinction is worth emphasizing. Enterprises and facility operators face the cost of downtime, contractor coordination, and compliance pressure, while consumers mostly feel the consequences indirectly through building availability and service quality. The risk is institutional, not personal, but it can still affect everyone inside the building.From a procurement standpoint, this also reinforces the idea that building controls should be bought with a support lifecycle in mind. A controller that looks inexpensive at installation can become expensive the moment it crosses into unsupported territory. That is the real lesson of obsolete OT: the upfront savings often become future remediation debt.
CISA’s mitigation playbook
CISA does not offer a patch for this issue in the advisory text provided, which means mitigation is mainly about reducing exposure. The agency recommends minimizing network exposure for all control system devices so they are not accessible from the internet, placing control networks behind firewalls, and isolating them from business networks. Those recommendations sound generic until you remember how many building networks remain flatter than anyone would like to admit.Remote access is the other major concern. CISA recommends using more secure methods such as VPNs, while also warning that VPNs can have vulnerabilities and are only as secure as the connected devices. That last caveat is critical: remote access can be a force multiplier for maintenance, but it can also become the easiest path to compromise when the endpoint and controller trust model is weak.
Defensive priorities
The advisory’s guidance can be translated into a practical response order:- Remove direct internet exposure.
- Segment the controller from business IT.
- Audit remote-access paths and tighten them.
- Identify whether the obsolete device can be replaced.
- If replacement is delayed, document compensating controls and maintenance ownership.
CISA also reminds organizations to perform proper impact analysis and risk assessment before deploying defensive measures. That is a subtle but important point. Overcorrecting in a building environment can create physical inconvenience or operational outages, so security teams need to validate changes carefully rather than treat isolation as a one-click fix.
What good hygiene looks like
- Keep the controller off the public internet.
- Restrict management traffic to known addresses.
- Separate facilities networks from office networks.
- Review any VPN or jump-host dependency.
- Inventory every BAS device that still depends on legacy trust assumptions.
Vendor context and support reality
Contemporary Controls still maintains a visible BASautomation support and contact structure, including regional offices and a dedicated technical support page. That matters because one of the first questions operators ask after reading an advisory like this is, “Who do we call, and what can they do for us?” The company’s support page asks customers to provide the model, serial number, and problem description, which suggests the vendor is still an active point of contact even if the BASC-20T itself is obsolete. (basautomation.ccontrols.com)At the same time, “obsolete” should not be confused with “ignored.” In industrial environments, vendors often still support migration paths, replacement families, or service advice for retired products. Contemporary Controls’ BASautomation materials still reference BAScontrol20 and related products in its catalog ecosystem, reinforcing the idea that users may need to move rather than simply patch.
What obsolescence usually means in practice
Obsolescence does not always mean the controller instantly fails. It usually means that spare parts, firmware work, and engineering attention are no longer guaranteed in the way buyers expect from a current product. That creates a kind of security asymmetry: the attack surface remains alive, but the maintenance path gets weaker every year.For operators, the real question is whether the device is sufficiently isolated to buy time for replacement. If it is not, then the organization is carrying a risk that will only get harder to manage. Legacy plus exposure is the worst combination in building automation, and that is exactly what this advisory highlights.
How operators should interpret the risk
The temptation with a high CVSS score is to treat the problem as universally urgent in the same way on every network. In reality, exposure varies. A BASC-20T sitting behind strong segmentation, with no direct management path and limited trust relationships, is not the same as one reachable from a broad flat internal network or a vendor-maintained remote-access tunnel. The score is a warning, but the architecture determines how fast the warning becomes a crisis.That said, the vulnerability is serious enough that it should not be triaged as “theoretical.” CISA explicitly says exploitation could permit a wide range of administrative or manipulative actions. When the impact includes reconfiguration, deletion, file transfer, and RPC-style access, the burden shifts to the defender to prove the system is not exposed.
Decision points for security teams
The first step is discovery. Organizations need to know whether they have BASControl20 3.1 or a BASC-20T in service, where it is deployed, and how it is connected. Without that inventory, every other decision becomes guesswork, and guesswork is a bad operating model for control systems.The second step is exposure review. If the device is reachable outside a tightly controlled management path, the risk rises sharply. If the network is already segmented and the controller is being phased out, the organization still has work to do, but the response can be more measured. Visibility first, then containment is the right sequence here.
The third step is replacement planning. If the controller is truly obsolete, then mitigation is not the endgame; it is the bridge. Security teams that stop at firewall rules often end up revisiting the same risk later, under more pressure and with fewer options.
Strengths and Opportunities
This advisory is disruptive, but it also gives operators a chance to correct a class of hidden debt before a real incident forces the issue. The strong point is not the vulnerability itself; it is the clarity of the warning and the chance to use it as a catalyst for a broader legacy review.- It provides a clear product identification and version scope.
- It names a specific CVE-2025-13926 issue rather than a vague product concern.
- It gives a concrete CWE-807 framing that helps security teams map the flaw to known weaknesses.
- It reinforces network segmentation as the primary defense for legacy OT.
- It creates an opportunity to inventory other obsolete controllers that may be hiding nearby.
- It nudges organizations toward better remote-access hygiene.
- It can justify budget for replacement planning rather than another short-term workaround.
Risks and Concerns
The most obvious concern is the lack of a simple vendor patch in the advisory text. When a product is obsolete, the defender’s choices narrow fast, and that can leave organizations leaning on controls that were never designed as final answers. The situation is especially difficult if the controller is operationally embedded and replacement requires downtime.- The controller may still be reachable from too many internal networks.
- The vulnerability could be abused for reconnaissance before impact.
- Obsolete devices may be protected by inconsistent documentation or stale diagrams.
- Security teams may underestimate building systems because they seem non-critical.
- Remote maintenance paths may already be too permissive.
- Replacement projects may be delayed by budget, scheduling, or vendor dependencies.
- Compensating controls may become permanent if no migration plan is set.
Looking Ahead
The near-term story here is likely to be less about public exploitation and more about remediation prioritization. Organizations that already know where their BASC-20T devices are and how they are segmented will be in a much better position than those discovering them during an audit or incident response. The long-term story is bigger: building automation vendors and operators need to treat obsolescence as a cybersecurity event, not just a procurement milestone.CISA’s advisory may also prompt a wider conversation about how many legacy controllers remain in service across commercial and industrial properties. That is the uncomfortable question every building operator eventually faces: if one obsolete controller is exposed, how many similar devices are waiting in adjacent closets, panels, and mechanical rooms? The answer is usually more than one.
What to watch next
- Whether Contemporary Controls issues any further technical guidance or migration advice.
- Whether additional BASautomation or Sedona-related products receive scrutiny.
- Whether defenders begin treating obsolete building controllers as a formal inventory class.
- Whether the advisory triggers more segmentation and remote-access reviews in facilities networks.
- Whether similar trust-boundary flaws surface in other legacy building automation controllers.
Source: CISA Contemporary Controls BASC 20T | CISA
Last edited: