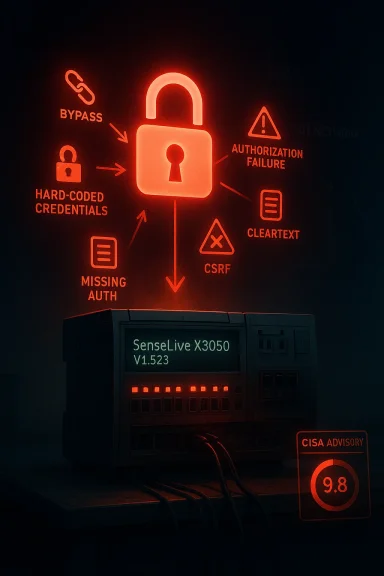
SenseLive X3050 has just been pulled into the spotlight for all the wrong reasons, and the headline is hard to soften: CISA says successful exploitation of the newly disclosed vulnerabilities could allow an attacker to take complete control of the device. The advisory covers SenseLive X3050 V1.523 and assigns a cluster of critical issues, including authentication bypass, hard-coded credentials, insufficient authorization, cleartext transmission, CSRF, and missing authentication for critical functions. CISA also notes there is no known public exploitation at this time, but the combination of a 9.8 CVSS score and an industrial-control footprint makes this the kind of alert operators should treat as immediate business risk, not routine patch noise.
The SenseLive X3050 advisory fits a pattern that security teams in industrial environments know too well: one vendor device can contain multiple weak links in the same trust chain, and once they line up, the result is often full device compromise. CISA’s summary is blunt about the possible outcome, and that bluntness matters because industrial products are rarely isolated gadgets. They are embedded in workflows, monitoring loops, and operational processes where a single compromised component can have ripple effects well beyond the box itself.
What makes this case stand out is not just the vulnerability count, but the breadth of the weakness classes. The advisory lists authentication bypass using an alternate path or channel, insufficient session expiration, use of hard-coded credentials, insufficiently protected credentials, missing authentication for critical function, cleartext transmission of sensitive information, missing authorization, and CSRF. In other words, this is not one bug with one fix path; it is a systemic security failure across identity, transport, and access-control layers.
That matters for defenders because industrial devices are often protected by perimeter assumptions that no longer hold. A box that was once considered “internal only” may now be reachable through remote support, segmented-but-flat OT networks, cloud management gateways, or contractor access paths. Once an attacker can find one weak trust boundary, a set of secondary flaws can turn a limited foothold into persistent administrative control.
The advisory also places the device squarely in sectors where downtime and manipulation are expensive: Critical Manufacturing, Water and Wastewater, Energy, and Information Technology. That is a reminder that industrial cybersecurity is no longer just about classic factories. It now spans the digital plumbing that supports modern services, utilities, and production systems, which is why even a single vulnerable controller or management appliance can become a high-value target.
At a broader level, the SenseLive case is another example of why CISA’s ICS advisories remain so influential. They are not just notices for government buyers; they are operational signals for any organization that runs industrial or semi-industrial infrastructure. The value of the advisory is that it narrows the question from “Is this product risky?” to “Which assets are exposed, and how fast can we take them out of the attacker’s reach?”
The vendor and product details in the advisory show that SenseLive is headquartered in India and that the affected device is deployed worldwide. Those two facts matter because they imply both a global support footprint and a broad downstream customer base. In industrial security, wide deployment plus weak access controls is a dangerous combination, especially when the affected asset is something operators may not inventory as carefully as servers or laptops.
The advisory also credits Jithin Nambiar J with reporting the vulnerabilities to CISA. That acknowledgment is worth noting because industrial disclosures often depend on responsible reporting by researchers who can see beyond a single exploit path and identify the deeper architectural problem. When a report surfaces a broad collection of issues at once, it usually means the product’s security model was fragile from the start.
CISA’s recommended practices are familiar, but they remain the backbone of practical mitigation. The agency urges organizations to minimize network exposure, isolate control system networks behind firewalls, and use VPNs carefully when remote access is required. That guidance is repeated often for a reason: the fastest way to reduce risk from a device with severe flaws is to make it hard to reach, hard to abuse, and hard to pivot through.
The important historical lesson is that industrial software often fails not because one vulnerability is unusually clever, but because security was bolted on too late or too narrowly. Hard-coded credentials, missing session expiration, and weak authorization controls all point to a product model that may have prioritized convenience, deployment speed, or supportability over defensive depth. That is precisely the tradeoff attackers love to inherit.
The advisory’s 9.8 vendor equipment CVSS score also frames the issue in a way that boards and operations managers can understand quickly. While CVSS is not the whole story, a score that high usually means the bug set is likely unauthenticated, remotely reachable, and capable of severe impact. In plain English, this is the kind of finding that can justify emergency change control.
Several of the disclosed issues are especially dangerous because they undermine the first line of defense: authentication. Authentication bypass, hard-coded credentials, and insufficient session expiration each reduce the attacker’s cost of entry, while missing authorization and missing authentication for critical function reduce the attacker’s cost of escalation. That combination is what turns a vulnerability from a nuisance into a takeover path.
The presence of hard-coded or insufficiently protected credentials is particularly troubling in industrial gear because those values often survive deployment, documentation, or support practice long after the original developer assumed they were harmless. If the credential is shared, reused, or recoverable, it becomes a built-in skeleton key. And if session expiration is weak, a stolen or hijacked session can remain valid long enough for persistence or lateral movement.
That is especially dangerous in an industrial context because critical functions often map directly to operational outcomes. A configuration change that looks minor in a web console can have physical consequences downstream, from lost telemetry to altered control behavior. The key point is that these are not abstract web-app bugs; they can become process-impacting events.
CSRF is a different class of risk, but it is no less relevant. If a device exposes browser-based administrative pages without strong anti-forgery protections, a legitimate user can be tricked into issuing state-changing commands simply by visiting a malicious page. That makes trust in the operator’s browser part of the attack surface, which is the opposite of what industrial systems need.
In manufacturing, a compromised management device can interrupt process visibility, alter settings, or become a pivot into engineering systems. In water and wastewater, integrity and availability matter as much as confidentiality because changes to control devices can affect service continuity. In energy, even a limited administrative compromise can cascade into maintenance overhead, safety concerns, or further segmentation failures.
The practical consequence is that the same vulnerability can be managed very differently depending on where the X3050 sits. If it is internet-exposed or reachable from business networks, the urgency rises sharply. If it is inside a carefully isolated OT enclave, defenders still need action, but they may have more room to stage compensating controls while arranging a vendor fix.
The best-run environments will already know the answer to four questions: which X3050 systems exist, where they are located, whether they are externally reachable, and whether they run V1.523. If any of those answers is unknown, the exposure should be treated as potentially present until proven otherwise. That is the kind of disciplined assumption that prevents a vulnerability from becoming an incident.
The agency also recommends using VPNs when remote access is required, while warning that VPNs themselves can be vulnerable and should be updated regularly. That caveat is important because too many organizations treat VPN as a magic word. In reality, a VPN is only one layer of trust, and it is only as secure as the devices and credentials behind it.
For defenders, the most important immediate actions are straightforward:
The advisory’s social engineering reminder is broader than the device itself, but still relevant. Industrial compromises often begin with deceptive email, support requests, or bogus links that steer an operator toward an attacker-controlled page. Keeping users skeptical of unsolicited messages is not a substitute for patching, but it reduces the odds that a vulnerable device gets targeted through a human shortcut first.
At the same time, operators should collect logs, admin access records, and configuration baselines. If the vulnerabilities are later found to have been used offensively, those records will help establish whether there was compromise, attempted compromise, or simply exposure. In industrial response work, the absence of evidence is not evidence of safety.
If the device supports it, disable unused features, rotate any exposed credentials, and review whether any saved or embedded secrets could have been harvested previously. Hard-coded credentials are especially important to investigate because they can persist across resets or maintenance cycles. If attackers have already learned those values, patching alone may not be enough.
That assessment should also extend to architecture. If a management device can be isolated more effectively, it should be. If remote administration can be replaced with a more tightly controlled workflow, it should be. And if the answer is that the device is so deeply embedded it cannot be moved quickly, that is a sign the organization needs a better strategy for resilience next time.
Another opportunity is that the mitigation path is conceptually straightforward even if the operational work is not. Limiting exposure, hardening remote access, and isolating control networks are all proven measures. The challenge is executing them quickly and safely, which is exactly where disciplined industrial security programs can show their value.
A second concern is remediation friction. Industrial environments often require testing, scheduling, and operational approval before updates can be applied. That delay creates a window in which defenders know the risk exists but cannot yet eliminate it. That window is exactly what attackers count on.
CISA’s note that there is no known public exploitation does not change the urgency; it just defines the countdown. In the ICS world, the most dangerous period is often the one between discovery and active abuse, when defenders still have a chance to close the door quietly. Once the first real incident lands, the cost of catching up tends to rise fast.
Source: CISA SenseLive X3050 | CISA
 Overview
Overview
The SenseLive X3050 advisory fits a pattern that security teams in industrial environments know too well: one vendor device can contain multiple weak links in the same trust chain, and once they line up, the result is often full device compromise. CISA’s summary is blunt about the possible outcome, and that bluntness matters because industrial products are rarely isolated gadgets. They are embedded in workflows, monitoring loops, and operational processes where a single compromised component can have ripple effects well beyond the box itself.What makes this case stand out is not just the vulnerability count, but the breadth of the weakness classes. The advisory lists authentication bypass using an alternate path or channel, insufficient session expiration, use of hard-coded credentials, insufficiently protected credentials, missing authentication for critical function, cleartext transmission of sensitive information, missing authorization, and CSRF. In other words, this is not one bug with one fix path; it is a systemic security failure across identity, transport, and access-control layers.
That matters for defenders because industrial devices are often protected by perimeter assumptions that no longer hold. A box that was once considered “internal only” may now be reachable through remote support, segmented-but-flat OT networks, cloud management gateways, or contractor access paths. Once an attacker can find one weak trust boundary, a set of secondary flaws can turn a limited foothold into persistent administrative control.
The advisory also places the device squarely in sectors where downtime and manipulation are expensive: Critical Manufacturing, Water and Wastewater, Energy, and Information Technology. That is a reminder that industrial cybersecurity is no longer just about classic factories. It now spans the digital plumbing that supports modern services, utilities, and production systems, which is why even a single vulnerable controller or management appliance can become a high-value target.
At a broader level, the SenseLive case is another example of why CISA’s ICS advisories remain so influential. They are not just notices for government buyers; they are operational signals for any organization that runs industrial or semi-industrial infrastructure. The value of the advisory is that it narrows the question from “Is this product risky?” to “Which assets are exposed, and how fast can we take them out of the attacker’s reach?”
Background
Industrial control system advisories tend to become more urgent when several exploitation paths converge on the same target. A single authentication flaw can sometimes be contained with network controls, but a product that also leaks credentials, skips authorization checks, and transmits sensitive data in cleartext creates a much broader attack surface. That is what makes this release especially concerning: it suggests a design and implementation stack that failed in multiple places, not a lone oversight.The vendor and product details in the advisory show that SenseLive is headquartered in India and that the affected device is deployed worldwide. Those two facts matter because they imply both a global support footprint and a broad downstream customer base. In industrial security, wide deployment plus weak access controls is a dangerous combination, especially when the affected asset is something operators may not inventory as carefully as servers or laptops.
The advisory also credits Jithin Nambiar J with reporting the vulnerabilities to CISA. That acknowledgment is worth noting because industrial disclosures often depend on responsible reporting by researchers who can see beyond a single exploit path and identify the deeper architectural problem. When a report surfaces a broad collection of issues at once, it usually means the product’s security model was fragile from the start.
CISA’s recommended practices are familiar, but they remain the backbone of practical mitigation. The agency urges organizations to minimize network exposure, isolate control system networks behind firewalls, and use VPNs carefully when remote access is required. That guidance is repeated often for a reason: the fastest way to reduce risk from a device with severe flaws is to make it hard to reach, hard to abuse, and hard to pivot through.
The important historical lesson is that industrial software often fails not because one vulnerability is unusually clever, but because security was bolted on too late or too narrowly. Hard-coded credentials, missing session expiration, and weak authorization controls all point to a product model that may have prioritized convenience, deployment speed, or supportability over defensive depth. That is precisely the tradeoff attackers love to inherit.
Why the advisory matters now
CISA notes that no known public exploitation has been reported at this time, but that should not be read as reassurance. In ICS security, “not yet observed” can still mean “widely exploitable if exposed,” especially when the device is reachable from segments that were never designed to withstand active probing. The absence of public exploitation simply means defenders have a narrow window to fix the exposure before the attack ecosystem catches up.The advisory’s 9.8 vendor equipment CVSS score also frames the issue in a way that boards and operations managers can understand quickly. While CVSS is not the whole story, a score that high usually means the bug set is likely unauthenticated, remotely reachable, and capable of severe impact. In plain English, this is the kind of finding that can justify emergency change control.
Vulnerability Cluster
The most alarming detail in the SenseLive X3050 notice is the number of distinct failure modes bundled into one affected version. CISA lists eleven CVEs affecting V1.523, and the titles read like a checklist of what not to do in a device that manages operational infrastructure. When a single release contains multiple critical control failures, patching becomes only part of the story; operators also need to ask how the product got shipped in that state.Several of the disclosed issues are especially dangerous because they undermine the first line of defense: authentication. Authentication bypass, hard-coded credentials, and insufficient session expiration each reduce the attacker’s cost of entry, while missing authorization and missing authentication for critical function reduce the attacker’s cost of escalation. That combination is what turns a vulnerability from a nuisance into a takeover path.
Identity and session flaws
Identity weaknesses are often the most exploit-friendly because they are easy to chain. If an attacker can get past login checks through an alternate path, reuse credentials embedded in the product, or ride a stale session longer than intended, the rest of the interface becomes fair game. Once management access is established, the attacker may not need anything more sophisticated than the device’s own administrative features.The presence of hard-coded or insufficiently protected credentials is particularly troubling in industrial gear because those values often survive deployment, documentation, or support practice long after the original developer assumed they were harmless. If the credential is shared, reused, or recoverable, it becomes a built-in skeleton key. And if session expiration is weak, a stolen or hijacked session can remain valid long enough for persistence or lateral movement.
Authorization and function-control failures
Missing authorization is the kind of flaw that can make an otherwise authenticated interface collapse into privilege confusion. A user who should be able to view status may end up able to invoke commands, reconfigure a device, or access administrative functions. When combined with missing authentication for critical function, the result is a control surface that does not reliably distinguish between observers and operators.That is especially dangerous in an industrial context because critical functions often map directly to operational outcomes. A configuration change that looks minor in a web console can have physical consequences downstream, from lost telemetry to altered control behavior. The key point is that these are not abstract web-app bugs; they can become process-impacting events.
- Authentication bypass lowers the bar for initial access.
- Missing authorization makes privilege escalation easier.
- Hard-coded credentials create hidden universal keys.
- Insufficient session expiration extends attacker dwell time.
- Missing authentication for critical function can expose control actions directly.
- CSRF can let a logged-in user’s browser be weaponized against the device.
Transport and browser-mediated weaknesses
Cleartext transmission of sensitive information is another red flag because it suggests the product may expose management traffic, secrets, or operational data to anyone able to observe the network path. In an industrial environment, that can include attackers on adjacent segments, compromised jump hosts, or malicious insiders. Even when the cleartext issue does not directly yield control, it can hand over the breadcrumbs needed for follow-on exploitation.CSRF is a different class of risk, but it is no less relevant. If a device exposes browser-based administrative pages without strong anti-forgery protections, a legitimate user can be tricked into issuing state-changing commands simply by visiting a malicious page. That makes trust in the operator’s browser part of the attack surface, which is the opposite of what industrial systems need.
What the bundle suggests
Taken together, these flaws suggest a product that may have accumulated security debt across multiple releases. That is not the same as saying the device is beyond repair, but it does mean defenders should assume the attack surface is larger than the advisory’s short summary alone conveys. When access control, secret handling, and transport security all show cracks, the safest response is to reduce exposure first and investigate the vendor’s remediation path second.- The advisory points to a multi-layered security failure rather than one isolated bug.
- Attackers could combine low-friction access with weak session and authorization logic.
- Browser-mediated attacks may matter if administrative sessions are reachable over web interfaces.
- Cleartext exposure could help adversaries harvest credentials or operational intelligence.
- The overall pattern raises questions about release engineering and security validation.
Sector Impact
The sectors named in the advisory are not accidental. Critical Manufacturing, Water and Wastewater, Energy, and Information Technology all rely on operational devices that must be reachable, manageable, and reliable, which is exactly why insecure management interfaces are so dangerous. A product that sits in the control path but lacks robust access control can become both a cyber foothold and an operational failure point.In manufacturing, a compromised management device can interrupt process visibility, alter settings, or become a pivot into engineering systems. In water and wastewater, integrity and availability matter as much as confidentiality because changes to control devices can affect service continuity. In energy, even a limited administrative compromise can cascade into maintenance overhead, safety concerns, or further segmentation failures.
Enterprise versus operational exposure
Enterprise IT teams may look at this advisory and see another critical patch item. Operational teams, by contrast, will see a device that may need maintenance windows, validation, vendor coordination, and rollback planning. That difference matters because OT environments cannot always absorb emergency reboots or configuration resets the way a conventional server fleet can.The practical consequence is that the same vulnerability can be managed very differently depending on where the X3050 sits. If it is internet-exposed or reachable from business networks, the urgency rises sharply. If it is inside a carefully isolated OT enclave, defenders still need action, but they may have more room to stage compensating controls while arranging a vendor fix.
Why asset visibility is everything
This is where many organizations get caught out. They know they own “industrial devices,” but they do not always know exactly which firmware revisions are deployed, which units are reachable from remote access tools, or which sites inherited older configurations. In that sense, the SenseLive advisory is as much an inventory test as it is a vulnerability test.The best-run environments will already know the answer to four questions: which X3050 systems exist, where they are located, whether they are externally reachable, and whether they run V1.523. If any of those answers is unknown, the exposure should be treated as potentially present until proven otherwise. That is the kind of disciplined assumption that prevents a vulnerability from becoming an incident.
- Manufacturing plants should check for vendor portals and engineering workstations tied to the device.
- Water operators should verify remote maintenance paths and monitoring links.
- Energy organizations should examine segmentation between business and control networks.
- IT teams should look for management exposure through shared infrastructure.
- All sectors should inventory firmware versions before they inventory blame.
CISA Guidance
CISA’s mitigation guidance is broad, but it is also practical. The agency recommends minimizing network exposure, keeping control system networks behind firewalls, and isolating remote devices from business networks. Those suggestions are not glamorous, but they are the fastest path to shrinking attack surface when a product has severe flaws and uncertain exploitation status.The agency also recommends using VPNs when remote access is required, while warning that VPNs themselves can be vulnerable and should be updated regularly. That caveat is important because too many organizations treat VPN as a magic word. In reality, a VPN is only one layer of trust, and it is only as secure as the devices and credentials behind it.
Defensive priorities
CISA’s guidance also encourages proper impact analysis and risk assessment before deploying defensive measures. That is sound advice in an ICS setting because a rushed change can be nearly as harmful as the vulnerability itself. The goal is to reduce exposure without causing unintended process disruption.For defenders, the most important immediate actions are straightforward:
- Confirm whether any SenseLive X3050 devices are deployed.
- Identify whether those devices run V1.523.
- Remove unnecessary exposure from internet-facing or business-facing networks.
- Restrict remote access to the smallest possible set of users and systems.
- Apply vendor guidance or compensating controls as soon as they are available.
Detection and response hygiene
CISA also reminds organizations to report suspected malicious activity through established internal procedures and to contact CISA for correlation when appropriate. That is an important signal because early reporting helps defenders see whether the advisory is beginning to show up in the wild. In security operations, the sooner suspicious activity is logged and shared, the faster patterns emerge.The advisory’s social engineering reminder is broader than the device itself, but still relevant. Industrial compromises often begin with deceptive email, support requests, or bogus links that steer an operator toward an attacker-controlled page. Keeping users skeptical of unsolicited messages is not a substitute for patching, but it reduces the odds that a vulnerable device gets targeted through a human shortcut first.
- Minimize network exposure wherever possible.
- Segment control networks from business networks.
- Use remote access only when absolutely necessary.
- Keep VPN and remote access tools fully updated.
- Maintain incident-reporting procedures that actually get used.
- Treat social engineering as part of the industrial attack surface.
Operational Response
The right way to respond to a critical ICS advisory is to combine asset discovery, exposure reduction, and vendor coordination. That is especially true here because the advisory does not just warn about one type of bug; it describes a product-level weakness set that could let an attacker take complete control. Organizations need to assume that every exposed interface is a candidate for misuse until proven otherwise.First 24 hours
The first day should be about visibility and containment, not heroics. Teams should locate every SenseLive X3050 instance, identify the firmware version, and determine whether any device is reachable from external networks or broader internal segments than necessary. If a device is exposed, shrinking that exposure should happen immediately, even before the permanent fix is installed.At the same time, operators should collect logs, admin access records, and configuration baselines. If the vulnerabilities are later found to have been used offensively, those records will help establish whether there was compromise, attempted compromise, or simply exposure. In industrial response work, the absence of evidence is not evidence of safety.
- Inventory every X3050 deployment.
- Record firmware versions and management paths.
- Identify remote access and browser-based admin exposure.
- Preserve logs before they roll over.
- Restrict access while remediation is staged.
- Coordinate with operations before making disruptive changes.
Short-term remediation
Short-term remediation should focus on eliminating easy attacker pathways. That means reducing reachability, tightening authentication boundaries, and removing any unnecessary reliance on browser-mediated admin workflows if the device exposes them. Even when a firmware update becomes available, compensating controls remain valuable because industrial patching can take time to validate safely.If the device supports it, disable unused features, rotate any exposed credentials, and review whether any saved or embedded secrets could have been harvested previously. Hard-coded credentials are especially important to investigate because they can persist across resets or maintenance cycles. If attackers have already learned those values, patching alone may not be enough.
Longer-term posture
Longer term, this advisory should be treated as an opportunity to reassess procurement and validation practices. A product that ships with this many critical categories of flaw raises questions about secure development, third-party review, and acceptance testing. Organizations may not be able to influence the vendor’s past, but they can influence what they buy, deploy, and trust in the future.That assessment should also extend to architecture. If a management device can be isolated more effectively, it should be. If remote administration can be replaced with a more tightly controlled workflow, it should be. And if the answer is that the device is so deeply embedded it cannot be moved quickly, that is a sign the organization needs a better strategy for resilience next time.
- Reduce management-plane exposure.
- Revoke or rotate any credential paths that may be embedded.
- Validate whether session timeouts are enforced.
- Check whether cleartext traffic can be intercepted on any segment.
- Review browser-based admin use for CSRF and privilege abuse risks.
- Build remediation lessons into future vendor evaluations.
Strengths and Opportunities
The good news, if there is any, is that CISA has already done the hard part of prioritization. By issuing a detailed advisory with a critical score, the agency has given defenders a clear signal that this device deserves urgent attention. That clarity can help teams move faster than they typically would on a generic vulnerability notice, and it can also improve executive buy-in for emergency work.Another opportunity is that the mitigation path is conceptually straightforward even if the operational work is not. Limiting exposure, hardening remote access, and isolating control networks are all proven measures. The challenge is executing them quickly and safely, which is exactly where disciplined industrial security programs can show their value.
- CISA has provided a strong, actionable warning.
- The advisory makes the likely impact easy to explain to leadership.
- Network isolation can reduce risk even before a vendor fix lands.
- Asset inventories can be improved while responding.
- Existing OT segmentation efforts can be validated.
- Credential hygiene can be strengthened across affected sites.
- The incident can sharpen vendor risk management going forward.
Risks and Concerns
The biggest concern is simple: if exploitation begins before exposure is reduced, the consequences could be severe. A product that can be taken over through multiple weaknesses is dangerous even when it is not internet-facing, because internal attackers and lateral movement paths are very common in real environments. And if the device is already poorly segmented, the blast radius may be larger than the asset owner expects.A second concern is remediation friction. Industrial environments often require testing, scheduling, and operational approval before updates can be applied. That delay creates a window in which defenders know the risk exists but cannot yet eliminate it. That window is exactly what attackers count on.
- Exposure may be greater than the owner realizes.
- Patching can be delayed by production constraints.
- Hard-coded credentials may survive ordinary fixes.
- Cleartext traffic could have already leaked sensitive data.
- CSRF or session flaws may enable abuse by authenticated users.
- Segmentation gaps can turn a local weakness into a wider incident.
- Asset ownership confusion can leave systems unpatched.
Looking Ahead
The next few weeks will tell us a lot about how quickly industrial organizations can move from disclosure to containment. If operators know their device inventory well, the response should be manageable: identify the affected firmware, reduce exposure, and apply vendor guidance as soon as it is safe to do so. If inventory is weak, though, the advisory will expose a more fundamental problem than a single vulnerable product.CISA’s note that there is no known public exploitation does not change the urgency; it just defines the countdown. In the ICS world, the most dangerous period is often the one between discovery and active abuse, when defenders still have a chance to close the door quietly. Once the first real incident lands, the cost of catching up tends to rise fast.
- Confirm whether any X3050 units are deployed.
- Verify the exact firmware version in every site.
- Segment or isolate remote management immediately.
- Track vendor remediation instructions and release notes.
- Preserve logs and access records for possible investigation.
Source: CISA SenseLive X3050 | CISA