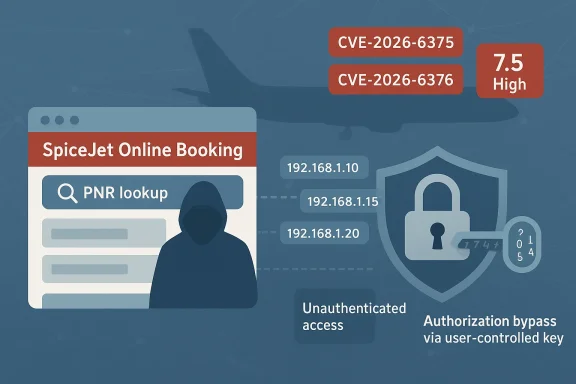
The latest CISA advisory on the SpiceJet Online Booking System is a straightforward but serious warning: two unauthenticated access-control flaws could let attackers disclose passenger data, including booking details and names, without needing an account or any special access. CISA says both vulnerabilities affect all versions of the online booking system and rates each one 7.5 High, with the core problems tied to authorization bypass through a user-controlled key and missing authentication for a critical function. The advisory also notes that SpiceJet did not respond to CISA’s coordination attempts, which raises the operational urgency for anyone relying on the booking platform.
The key thing to understand about this disclosure is that it is not a generic web bug report. CISA is treating the affected system as part of the transportation systems ecosystem, which means the stakes extend well beyond ordinary customer-service embarrassment. Passenger booking systems are high-value assets because they sit at the intersection of identity, travel itineraries, and customer contact data. Even when a flaw is “only” read-only, the volume and sensitivity of the data involved can make it highly exploitable from a privacy and intelligence-gathering standpoint.
The advisory names two CVEs: CVE-2026-6375 and CVE-2026-6376. The first allows unauthenticated querying of passenger name records, or PNRs, by exploiting predictable identifiers and weak access controls. The second lets an attacker retrieve full booking details with only a PNR and last name, again without authentication or verification. In practical terms, this means the application appears to trust data inputs that are not sufficient proof of identity, which is exactly the kind of mistake attackers love because it is simple to automate at scale.
CISA’s language is unusually direct about the mechanism. One issue is framed as authorization bypass through a user-controlled key, which is the classic pattern where the application uses an identifier supplied by the user as if it were a permission grant. The other is missing authentication for a critical function, meaning the booking retrieval path can be reached without first proving who the requester is. Those are distinct defects, but together they point to the same structural weakness: the system’s trust boundary is too loose around customer data.
This matters in a broader industry context because airlines and travel systems have long been attractive targets for scraping, fraud, and account abuse. Booking references are often reused in emails, SMS notifications, itineraries, and customer-service flows, which means a predictable PNR pattern can become a pivot point into larger data exposure. A system that was built for convenience can quickly become a data-mining interface if access control is not enforced at the server side. That is the real story here, not just the raw CVSS score.
For CVE-2026-6376, the public booking retrieval page permits access to full booking details using only a PNR and last name. CISA says there is no authentication or verification mechanism beyond those inputs, which means the page effectively treats knowledge of basic booking data as proof of identity. That is a weak trust model, especially when those inputs may be gleaned from emails, screenshots, leaked itineraries, or other low-effort sources.
The practical implication is that an attacker does not need to compromise SpiceJet systems in a dramatic way. They may simply need to guess, predict, or collect PNRs and then test them against a vulnerable endpoint. That is what makes the issue dangerous: the exploitation path is not necessarily sophisticated, but it is likely to be highly scalable. Low-friction data exposure is often the prelude to broader abuse because it lowers the cost of reconnaissance.
The advisory’s CWE mappings are revealing. CWE-639, authorization bypass through a user-controlled key, typically involves an attacker manipulating a parameter that the server incorrectly treats as authorization proof. CWE-306, missing authentication for critical function, means the system exposed a function that should have been gated behind a valid identity check. Together, those weaknesses suggest that the back-end trust model was not strict enough about who may ask for what.
The CVSS vector also matters. Both issues are scored with network attack vector, low attack complexity, no privileges required, and no user interaction. That combination signals that exploitation is likely to be straightforward and remote. In other words, this is the kind of flaw that can be discovered, automated, and scaled by a modest attacker rather than requiring a highly skilled intruder.
For the airline, the operational cost may be larger than the technical defect itself. When booking data can be queried without authentication, the company can face a surge in support tickets, forced credential resets, incident response work, and customer trust damage. Reputationally, passengers do not always distinguish between a “data disclosure” and a broader breach; they simply see that their travel information was exposed.
There is also a downstream fraud angle. Travel records can be used to validate personal details, construct social-engineering lures, or confirm whether someone has an upcoming trip. In the wrong hands, that information can be turned into targeted phishing, scam calls, or account takeover attempts. The issue is not just what data is shown on the page, but what that data enables next. That’s the multiplier effect.
The other notable point is CISA’s statement that SpiceJet did not respond to coordination requests. In coordinated disclosure, vendor engagement can often determine whether an issue is patched, acknowledged, or at least mitigated quickly. Here, the lack of response leaves defenders with less certainty and more reason to apply compensating controls immediately.
CISA also reminds organizations to minimize network exposure, use firewalls, segment systems, and avoid relying on internet reachability for sensitive operational functions. Those recommendations are broad because they work across many vulnerability classes, and they are especially relevant when a public-facing booking system is involved. The simplest defensive lesson is often the right one: if a function does not need to be exposed broadly, do not expose it broadly.
The second priority is server-side authorization review. Any endpoint that accepts a PNR, booking reference, last name, or similar token should be audited to ensure the token is never treated as proof of identity by itself. If a function returns customer records, it should verify not only that the data exists but that the requester is entitled to view it. That is basic access-control hygiene, but these advisories exist precisely because basic hygiene is often missing.
The third priority is monitoring for enumeration patterns. Even if the product cannot be immediately fixed, defenders may be able to identify suspicious request bursts, sequential lookups, or abnormal access patterns. Detection is not a substitute for remediation, but it can be the difference between a contained issue and a large-scale scrape. Visibility buys time.
There is also an opportunity here for the broader travel industry. Public booking portals are often designed for convenience first and security second, but this advisory is a reminder that access control has to be treated as a core product requirement. Organizations can use this moment to review customer-facing lookup flows, ticket-management portals, and support interfaces before similar flaws show up elsewhere.
A second concern is the possibility of follow-on abuse. Exposed passenger data is rarely the end of the story; it often becomes raw material for phishing, impersonation, or identity correlation. In a transportation context, even limited booking information can help an attacker time social engineering around real travel plans.
A third concern is the vendor-response gap. SpiceJet’s apparent lack of coordination with CISA means external parties cannot easily rely on a published fix or official mitigation path. That uncertainty can prolong exposure, especially if the organization has no direct channel to confirm remediation status or service configuration. Uncertainty is operationally expensive.
It will also be worth watching for signs that the problem is more systemic than the advisory suggests. When one public data-retrieval path lacks authentication, others often deserve scrutiny too. The travel sector has a long history of iterative portal expansion, which can leave old assumptions embedded in new features. That means today’s CVE may be a symptom of a larger application design problem.
Source: CISA SpiceJet Online Booking System | CISA
 Background
Background
The key thing to understand about this disclosure is that it is not a generic web bug report. CISA is treating the affected system as part of the transportation systems ecosystem, which means the stakes extend well beyond ordinary customer-service embarrassment. Passenger booking systems are high-value assets because they sit at the intersection of identity, travel itineraries, and customer contact data. Even when a flaw is “only” read-only, the volume and sensitivity of the data involved can make it highly exploitable from a privacy and intelligence-gathering standpoint.The advisory names two CVEs: CVE-2026-6375 and CVE-2026-6376. The first allows unauthenticated querying of passenger name records, or PNRs, by exploiting predictable identifiers and weak access controls. The second lets an attacker retrieve full booking details with only a PNR and last name, again without authentication or verification. In practical terms, this means the application appears to trust data inputs that are not sufficient proof of identity, which is exactly the kind of mistake attackers love because it is simple to automate at scale.
CISA’s language is unusually direct about the mechanism. One issue is framed as authorization bypass through a user-controlled key, which is the classic pattern where the application uses an identifier supplied by the user as if it were a permission grant. The other is missing authentication for a critical function, meaning the booking retrieval path can be reached without first proving who the requester is. Those are distinct defects, but together they point to the same structural weakness: the system’s trust boundary is too loose around customer data.
This matters in a broader industry context because airlines and travel systems have long been attractive targets for scraping, fraud, and account abuse. Booking references are often reused in emails, SMS notifications, itineraries, and customer-service flows, which means a predictable PNR pattern can become a pivot point into larger data exposure. A system that was built for convenience can quickly become a data-mining interface if access control is not enforced at the server side. That is the real story here, not just the raw CVSS score.
Why PNR access is especially sensitive
PNRs are not just reservation numbers. In airline workflows, they can be the shortcut that links a traveler to names, dates, routes, and booking metadata. If an attacker can enumerate valid records, they may be able to build a list of real passengers and correlate that with travel behavior or other personal data. The advisory’s wording suggests that this is not a theoretical privacy concern but an actual exposure path.Why the advisory is broader than a single bug
The two CVEs together indicate a pattern rather than an accident. One flaw exposes a query path that should have been permission-protected; the other exposes a retrieval function that should have required stronger verification. That combination often means the application’s data-access model was designed around assumptions about “friendly” inputs instead of hostile ones. In security terms, that is a fragile foundation.What CISA Says Happened
CISA’s summary is concise but enough to reconstruct the likely abuse path. For CVE-2026-6375, the booking API allegedly lets unauthenticated users query PNRs without access controls. Because PNR identifiers follow a predictable pattern, an attacker could enumerate values and harvest valid records, including passenger names. The vulnerability is described as an endpoint meant for authenticated profile access that simply fails to enforce that requirement.For CVE-2026-6376, the public booking retrieval page permits access to full booking details using only a PNR and last name. CISA says there is no authentication or verification mechanism beyond those inputs, which means the page effectively treats knowledge of basic booking data as proof of identity. That is a weak trust model, especially when those inputs may be gleaned from emails, screenshots, leaked itineraries, or other low-effort sources.
The practical implication is that an attacker does not need to compromise SpiceJet systems in a dramatic way. They may simply need to guess, predict, or collect PNRs and then test them against a vulnerable endpoint. That is what makes the issue dangerous: the exploitation path is not necessarily sophisticated, but it is likely to be highly scalable. Low-friction data exposure is often the prelude to broader abuse because it lowers the cost of reconnaissance.
The likely attacker workflow
A realistic attacker workflow would probably look like this:- Collect or infer PNR patterns.
- Probe the booking API for unauthenticated record lookup.
- Use the public retrieval page to fetch richer booking metadata.
- Aggregate results to identify passengers, travel routes, and booking behavior.
- Combine exposed data with phishing, fraud, or intelligence-gathering campaigns.
Why the lack of authentication matters more than the missing patch
CISA says SpiceJet did not respond to its attempts to coordinate. That detail is not just bureaucratic color; it tells defenders that no official vendor remediation path was available in the advisory. In situations like this, organizations and users have to assume the exposure remains live until proven otherwise, because silence is not a mitigation strategy.Technical Significance
The technical issue here is not really about API design alone. It is about authorization enforcement and identity verification, two controls that should be mandatory in any system returning sensitive customer data. When those controls are missing, the application becomes susceptible to abuse even if the transport layer is encrypted and the user interface looks legitimate. Security failures at the logic layer are often more dangerous than flashy bugs because they can be exploited quietly and repeatedly.The advisory’s CWE mappings are revealing. CWE-639, authorization bypass through a user-controlled key, typically involves an attacker manipulating a parameter that the server incorrectly treats as authorization proof. CWE-306, missing authentication for critical function, means the system exposed a function that should have been gated behind a valid identity check. Together, those weaknesses suggest that the back-end trust model was not strict enough about who may ask for what.
The CVSS vector also matters. Both issues are scored with network attack vector, low attack complexity, no privileges required, and no user interaction. That combination signals that exploitation is likely to be straightforward and remote. In other words, this is the kind of flaw that can be discovered, automated, and scaled by a modest attacker rather than requiring a highly skilled intruder.
Why predictable identifiers are a security smell
Predictable identifiers are not inherently bad, but they become dangerous when they control access to sensitive objects. If the PNR format is sequential, patterned, or otherwise guessable, attackers can move from single-record probing to bulk enumeration. The advisory strongly implies that the identifier itself became part of the trust model, which is a design mistake because identifiers should reference records, not authorize access to them.How this differs from ordinary privacy leakage
This is more serious than a page accidentally exposing a few fields. The flaw appears to affect the core retrieval path for reservations, which means the exposure could include a wide cross-section of passenger data rather than a small edge case. When the access check is missing at the application layer, the attacker can use the system as intended by the developers—just without the permission logic that should have stood in the way. That inversion is what makes these bugs so nasty.Passenger and Operational Impact
For passengers, the immediate concern is privacy. Exposed booking records can reveal names, itinerary details, and other travel metadata that users reasonably expect to remain confidential. Depending on what the booking pages expose beyond the summary text, the data could also help attackers craft convincing phishing messages or impersonate the airline in follow-on fraud campaigns.For the airline, the operational cost may be larger than the technical defect itself. When booking data can be queried without authentication, the company can face a surge in support tickets, forced credential resets, incident response work, and customer trust damage. Reputationally, passengers do not always distinguish between a “data disclosure” and a broader breach; they simply see that their travel information was exposed.
There is also a downstream fraud angle. Travel records can be used to validate personal details, construct social-engineering lures, or confirm whether someone has an upcoming trip. In the wrong hands, that information can be turned into targeted phishing, scam calls, or account takeover attempts. The issue is not just what data is shown on the page, but what that data enables next. That’s the multiplier effect.
Enterprise versus consumer impact
From a consumer perspective, the harm is mostly privacy loss and phishing risk. From an enterprise or operational perspective, the issue may also implicate legal reporting, customer-notification obligations, and internal process failures. Large-scale booking exposure can create an immediate need to review monitoring, logging, and customer communications strategy. Those are not trivial follow-on tasks, especially in a transport environment where customer service windows are tightly managed.Why “read-only” does not mean low impact
It is tempting to downplay flaws that do not directly alter records or disrupt availability. That would be a mistake. Read-only exposures often create the reconnaissance layer that supports later fraud, impersonation, or operational intelligence gathering. In this case, disclosure of PNR-linked booking metadata could allow attackers to map traveler behavior at scale.- Passengers may face privacy exposure.
- Attackers could use exposed data for phishing or fraud.
- Support teams may see a spike in account and booking inquiries.
- Trust in the booking process can erode quickly.
- Operational response may require customer notification and review.
- Reused booking references can widen the blast radius.
- Even limited disclosure can become a broader intelligence leak.
Why CISA’s Response Matters
CISA’s advisory is important because it confirms that the issue belongs in the category of high-priority exposure, not routine website cleanup. The agency explicitly frames the affected product in transportation infrastructure terms and lists both vulnerabilities as high severity. That gives airlines, security teams, and even individual travelers a concrete signal that the risk is real, not speculative.The other notable point is CISA’s statement that SpiceJet did not respond to coordination requests. In coordinated disclosure, vendor engagement can often determine whether an issue is patched, acknowledged, or at least mitigated quickly. Here, the lack of response leaves defenders with less certainty and more reason to apply compensating controls immediately.
CISA also reminds organizations to minimize network exposure, use firewalls, segment systems, and avoid relying on internet reachability for sensitive operational functions. Those recommendations are broad because they work across many vulnerability classes, and they are especially relevant when a public-facing booking system is involved. The simplest defensive lesson is often the right one: if a function does not need to be exposed broadly, do not expose it broadly.
What the lack of vendor response changes
When a vendor is silent, customers lose the ability to confirm whether a fix exists, whether a workaround is safe, or whether a patch is imminent. That uncertainty forces a more defensive posture. Organizations may need to treat the booking platform as vulnerable by default until they can independently verify otherwise. In security operations, uncertainty is a risk multiplier.Why advisory classification matters
The fact that CISA published this as an ICS advisory rather than burying it in a generic vulnerability feed gives the issue more weight. It signals that the problem is not only relevant to a single company’s website but also to the broader transport-sector cybersecurity conversation. That distinction matters because public booking systems often sit at the edge of much larger operational ecosystems.Defensive Priorities
For organizations and security teams, the first priority is exposure reduction. If the vulnerable booking interface is internet-reachable, that should be treated as an urgent condition. Even if immediate patching is not available, restricting access through network controls, gateway filtering, or temporary service isolation can reduce the chance of bulk enumeration.The second priority is server-side authorization review. Any endpoint that accepts a PNR, booking reference, last name, or similar token should be audited to ensure the token is never treated as proof of identity by itself. If a function returns customer records, it should verify not only that the data exists but that the requester is entitled to view it. That is basic access-control hygiene, but these advisories exist precisely because basic hygiene is often missing.
The third priority is monitoring for enumeration patterns. Even if the product cannot be immediately fixed, defenders may be able to identify suspicious request bursts, sequential lookups, or abnormal access patterns. Detection is not a substitute for remediation, but it can be the difference between a contained issue and a large-scale scrape. Visibility buys time.
Immediate action checklist
- Identify every externally reachable booking endpoint.
- Verify whether PNR-based retrieval requires true authentication.
- Check whether PNRs are sequential or otherwise guessable.
- Review logs for repetitive lookup patterns.
- Restrict access to the smallest viable set of users or networks.
- Engage the vendor or platform owner for remediation status.
- Prepare customer communications if exposure is confirmed.
What not to assume
Do not assume that HTTPS alone makes the system safe. Do not assume that a last name plus booking reference constitutes identity proof. Do not assume the issue is harmless because it is “only booking data.” And do not assume that the absence of public exploitation means the vulnerability is low risk. CISA’s advisory makes clear that the threat is already credible enough to justify action.- HTTPS does not replace authorization.
- A booking reference is not a password.
- Low-friction data leaks can scale quickly.
- Enumerated records are easy to automate.
- Public silence is not proof of safety.
- Transport-sector data has fraud value.
- Monitoring and segmentation both matter.
Strengths and Opportunities
The one encouraging aspect of this disclosure is that it is specific enough to support immediate triage. CISA identifies the affected product family, the exploit conditions, the likely impact, and the relevant weakness classes. That gives defenders a chance to move from general concern to concrete checks without guessing. Specificity is a gift in incident prevention.There is also an opportunity here for the broader travel industry. Public booking portals are often designed for convenience first and security second, but this advisory is a reminder that access control has to be treated as a core product requirement. Organizations can use this moment to review customer-facing lookup flows, ticket-management portals, and support interfaces before similar flaws show up elsewhere.
- Clear affected product identification.
- Two well-defined vulnerability classes.
- High-severity scoring for both issues.
- Strong motivation to audit booking workflows.
- Opportunity to tighten access control design.
- Chance to review logging and monitoring coverage.
- A useful reminder to reduce unnecessary exposure.
Risks and Concerns
The biggest concern is that the vulnerable system appears to be public-facing and exploitable without authentication. That is exactly the sort of condition that turns a narrow logic error into a broad data-exposure event. If the endpoint is reachable at scale, even a modest attacker could harvest a large volume of records quickly.A second concern is the possibility of follow-on abuse. Exposed passenger data is rarely the end of the story; it often becomes raw material for phishing, impersonation, or identity correlation. In a transportation context, even limited booking information can help an attacker time social engineering around real travel plans.
A third concern is the vendor-response gap. SpiceJet’s apparent lack of coordination with CISA means external parties cannot easily rely on a published fix or official mitigation path. That uncertainty can prolong exposure, especially if the organization has no direct channel to confirm remediation status or service configuration. Uncertainty is operationally expensive.
- Public reachability increases the attack surface.
- Enumeration makes bulk disclosure feasible.
- Passenger data can enable targeted fraud.
- Vendor silence complicates remediation.
- Weak access control may be repeated elsewhere.
- Support teams may be overwhelmed by inquiries.
- Trust damage can outlast the technical fix.
Looking Ahead
What happens next will depend on whether SpiceJet publishes a fix, whether the booking system can be temporarily hardened, and whether security teams can verify that the same design flaw does not exist in adjacent customer-service workflows. The most important near-term question is whether the exposed functions can be restricted fast enough to blunt enumeration before the issue spreads through the threat ecosystem.It will also be worth watching for signs that the problem is more systemic than the advisory suggests. When one public data-retrieval path lacks authentication, others often deserve scrutiny too. The travel sector has a long history of iterative portal expansion, which can leave old assumptions embedded in new features. That means today’s CVE may be a symptom of a larger application design problem.
Key things to watch
- Whether SpiceJet issues a public remediation statement.
- Whether PNR lookup endpoints are tightened or disabled.
- Whether additional travel-facing services share the same flaw pattern.
- Whether monitoring detects large-scale record enumeration.
- Whether customers are warned about booking-data exposure.
- Whether defensive controls are expanded beyond the affected pages.
Source: CISA SpiceJet Online Booking System | CISA