Microsoft’s advisory — which calls out the nkeys “xkeys” issue as a vulnerability in open-source components used in Azure Linux — is accurate as far as Microsoft’s public inventory goes: Azure Linux is the only Microsoft product Microsoft has identified as containing the vulnerable library so far, and Microsoft says it will update the CVE entry if it finds the library in additional Microsoft products.
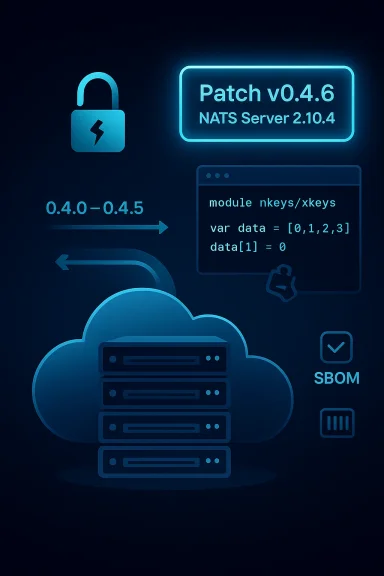
In late October 2023 a flaw in the NATS-related cryptographic library nkeys was disclosed as CVE-2023-46129. The bug sits in the library’s new xkeys (encryption) handling logic: an array was accidentally passed by value into an internal routine that mutates that buffer to produce the encryption key, and because of that programming mistake the effective key used for Seal operations ended up being an all-zero key. The practical result is that encryption performed with the affected code provided no confidentiality — everything encrypted with the broken path used a predictable, fixed key.
NATS (and related projects) adopted the xkeys extension to support encrypted payloads in certain callouts and workflows. The vulnerable nkeys versions were v0.4.0 through v0.4.5 (fixed in v0.4.6), and matching NATS Server versions implicated were 2.10.0 through 2.10.3 (fixed in 2.10.4). The problem affects encryption (Seal/Open) only, not the signing/authentication primitives that nkeys historically provided.
The vulnerability received a high severity score (CVSS v3.1 7.5) because the weakness undermines confidentiality and can be exploitable over the network in many deployments. Public vulnerability databases and distro security trackers (NVD, Ubuntu, Debian, Alpine, Red Hat summaries) catalog the issue and point to the same root cause and fixes.
Put plainly:
Notably:
Microsoft’s public position is transparent: Azure Linux is the Microsoft product it has identified as including the vulnerable library, and Microsoft will update its CVE product mapping if additional Microsoft products are found to be affected. That is the authoritative statement for Microsoft customers, but it should not be the endpoint of your response: teams must scan and verify their own environments, update vulnerable modules and binaries, and treat this as a supply-chain incident that calls for rebuilds and secret rotation where necessary.
If you maintain infrastructure that could touch NATS or nkeys — whether in Azure, on-premises, or in containers — prioritize the inventory, the rebuilds, and the key rotations now. The technical fix exists; the operational challenge is ensuring the fix reaches every image and binary that matters.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
In late October 2023 a flaw in the NATS-related cryptographic library nkeys was disclosed as CVE-2023-46129. The bug sits in the library’s new xkeys (encryption) handling logic: an array was accidentally passed by value into an internal routine that mutates that buffer to produce the encryption key, and because of that programming mistake the effective key used for Seal operations ended up being an all-zero key. The practical result is that encryption performed with the affected code provided no confidentiality — everything encrypted with the broken path used a predictable, fixed key.NATS (and related projects) adopted the xkeys extension to support encrypted payloads in certain callouts and workflows. The vulnerable nkeys versions were v0.4.0 through v0.4.5 (fixed in v0.4.6), and matching NATS Server versions implicated were 2.10.0 through 2.10.3 (fixed in 2.10.4). The problem affects encryption (Seal/Open) only, not the signing/authentication primitives that nkeys historically provided.
The vulnerability received a high severity score (CVSS v3.1 7.5) because the weakness undermines confidentiality and can be exploitable over the network in many deployments. Public vulnerability databases and distro security trackers (NVD, Ubuntu, Debian, Alpine, Red Hat summaries) catalog the issue and point to the same root cause and fixes.
What Microsoft has said — and what that means
Microsoft’s official FAQ language for Linux-related CVEs repeats one clear point: the Azure Linux distribution is maintained by Microsoft and the company tracks open-source components used in those images. For the CVE in question, Microsoft’s public guidance acknowledges that the Azure Linux distro includes the open-source library and therefore is potentially affected. Microsoft adds that it will update the CVE entry if impact to additional Microsoft products is identified.Put plainly:
- Microsoft has publicly confirmed one Microsoft product — Azure Linux — as including the component referenced by the CVE.
- Microsoft has not yet publicly identified other Microsoft products as containing the vulnerable nkeys/xkeys code.
- Microsoft commits to updating its CVE/Catalog entries if it finds the component in additional products.
Technical anatomy of the flaw — why it matters
How the bug happens
The problem is not an exotic cryptographic design flaw — it’s a programming error with cryptographic consequences. The library’s implementation passed an array (a buffer that should have been mutated by reference) by value to an internal helper. The helper then mutated the copy expecting to change the original buffer; because the mutation operated on a copy, the buffer actually used as the key remained in an uninitialized or default state which effectively produced an all-zero key for Seal operations. The encryption routine therefore always encrypted with the same known key (all zeros), breaking secrecy.Why using an all-zero key is catastrophic
- Confidentiality is nullified. Even if the encryption algorithm (e.g., NaCl box/seal) is theoretically strong, using a predictable key removes the secrecy requirement — an attacker can decrypt or recognize patterns.
- Downstream trust breaks. Systems relying on the nkeys xkeys Seal for protecting secrets in auth callouts, secret transports, or configuration exchanges can have their protections entirely bypassed.
- Silent failure. Because signing remained unaffected, many integrations that assumed encryption was working could continue functioning and never see an obvious operational failure — the failure is subtle but severe.
Where the vulnerable code shows up in the ecosystem
This vulnerability is primarily an issue if you are running code that depends on the nkeys library’s xkeys encryption paths — the most obvious examples are:- NATS Server: versions 2.10.0–2.10.3 used nkeys versions that expose the flaw; NATS Server 2.10.4 includes the fix and ships with nkeys v0.4.6. Upgrading NATS server to the fixed version resolves server-side exposure.
- Any Go application using nkeys v0.4.0–v0.4.5 (especially code that enables/uses xkeys for encryption) will be affected. If you vendor the module or statically link it into services, you must update and rebuild.
- Open-source projects and runtimes that use NATS + nkeys (for example, wasmCloud’s secret backends and other NATS-based secret transports) may have used xkeys for secret transport. Projects that adopted xkeys are listed in project docs and roadmaps; where the code path is in use, the vulnerability matters.
- Linux distribution packages: distribution packs of nats-server or nkeys (Debian, Ubuntu, Alpine, Fedora, Red Hat) mapped the issue and provided distro-specific updates or advisories; those are important if you deploy from distro packages rather than vendor binaries.
Is Azure Linux the only Microsoft product that includes the library?
Short answer: Yes — as far as Microsoft’s public advisory states. Microsoft’s published CVE entries and FAQ language identify Azure Linux as the Microsoft-maintained distro that includes the affected open-source library, and Microsoft has indicated it will update any product impact statements if additional Microsoft products are discovered to include the component. That means:- If you run Azure Linux images, treat them as potentially affected and follow remediation guidance.
- If you run other Microsoft products (Windows Server, Azure PaaS services, Azure-managed services), you should not assume a product is affected unless Microsoft lists it or the product’s component inventory shows nkeys/nats-server in the service image or dependency graph. Microsoft’s advisory explicitly commits to updating the CVE if more products are impacted.
Practical remediation steps for administrators and dev teams
If you maintain systems that could touch nkeys or nats-server, treat this as a supply-chain/cryptography patch that requires coordinated updates and verification.1. Inventory and detection (immediately)
- Search for nkeys in your codebases, go.mod files, container images, and vendor directories.
- Check whether you run nats-server versions 2.10.0–2.10.3 (or any downstream package that bundles nkeys v0.4.0–v0.4.5).
- Scan container registries and server images for the vulnerable binaries or module versions.
- Inspect logs and runtime configurations for xkeys usage — many projects document when they use xkeys for secrets in the service docs.
2. Patch and rebuild
- Upgrade the nkeys Go module to v0.4.6 or later, or upgrade nats-server to v2.10.4 or later. Rebuild binaries and images that include the dependency.
- For distro-managed packages, apply security updates supplied by your distribution vendor (Ubuntu, Debian, Alpine, Fedora, Red Hat, etc.). Those maintainers published advisories and updated packages after the fix.
- Redeploy updated services, ensuring that any auth callout integrations or secret backends are rebuilt with the patched module.
3. Rotate secrets and keys where appropriate
- If your deployment used xkeys to transport secrets or keys, assume that confidentiality may have been compromised during the exposure window and rotate the secrets, API keys, and tokens transported by that mechanism.
- For systems where audit or forensic evidence suggests possible exposure, escalate to incident response: collect logs, preserve images, and, if needed, take systems offline to rotate credentials.
4. Verify and test
- After updating, run functional tests that verify encryption paths are using correct keys and that the xkeys Seal/Open path behaves as expected.
- Use deterministic unit tests where possible to validate that keys are non-zero and generated as intended by the code. Re-run integration tests for auth callouts and secret transfer scenarios.
5. Apply broader supply-chain hygiene
- Apply SBOM and dependency scanning across CI pipelines. Ensure you can produce module-level inventories for all languages (including Go modules) and for container images.
- Where possible, enforce reproducible builds and pinned dependencies in production images to make future discovery and updates faster.
For Azure customers: what to check and what to expect from Microsoft
Microsoft’s public FAQ acknowledges Azure Linux images specifically. If you run Azure Linux images in Azure VMs or AKS nodepools, you should:- Check the image version and applied updates; Microsoft states a commitment to keep Azure Linux up to date with secure library versions. If your Azure Linux image is updated in the managed images, apply those image updates or patch the package inside the VM.
- For managed services (e.g., Azure Container Instances, Azure App Service on Linux, AKS): Microsoft’s advisory did not list additional affected managed services. However, you should still check your container images and application stacks — if you bring your own images (BYOI) that include nats-server or nkeys, you are responsible for patching them and rebuilding images.
- Keep an eye on Microsoft’s CVE page and CSAF/VEX publications (Microsoft has said it began publishing CSAF/VEX in October 2025) for any updates that expand product impact or provide machine-readable mitigation metadata.
Broader ecosystem and downstream impact
The nkeys/nats ecosystem is widespread: message brokers, microservice runtimes, wasmCloud host/actors, and other projects used xkeys to protect inter-component secrets. Several OS distributions, cloud vendors, and open-source projects published advisories and updates after CVE disclosure. This is a classic example of a small bug in a shared cryptographic primitive creating outsized risk when reused across many projects.Notably:
- wasmCloud documented xkeys usage in secrets backends and has since moved to deprecate or remove xkeys in newer roadmaps, highlighting how ecosystems change in response to cryptographic supply-chain risk.
- Many Linux distributions and package trackers mapped the affected versions and issued updates or flagged the packages; administrators that install nats/nkeys from distribution repositories should follow distro advisories.
Attribution, transparency, and vendor coordination
This CVE is a useful case study in coordinated disclosure and vendor transparency:- The NATS maintainers published the fix in the nkeys repo, and NATS Server release notes document the CVE and the fixed version.
- Public vulnerability databases (NVD, OSV, distro trackers) aggregated the technical details and severity.
- Microsoft’s approach — identifying Azure Linux as a Microsoft-managed product that includes the component and promising updates to the CVE if more products are affected — follows responsible disclosure practices for vendors with many product lines, where a cautious “known affectees only” statement is the correct first step while inventories are confirmed.
Critical analysis: strengths, gaps, and residual risks
Strengths
- The technical fix was straightforward and released promptly: increment the module version (nkeys v0.4.6) and the NATS Server patch (2.10.4) addressed the underlying code error.
- Distro vendors and upstream maintainers published advisories and coordinated updates across packaging ecosystems.
- Microsoft’s public statement and the CSAF/VEX commitment indicate improving machine-readable transparency for Linux component impacts within Microsoft-managed images.
Gaps and risks
- Inventory uncertainty. Public vendor statements are necessary but not sufficient to guarantee nothing else is affected. The presence of a library in one managed image does not preclude the library’s presence in other products or third-party bundles Microsoft ships or hosts. External teams must scan their environments rather than rely solely on vendor product lists.
- Silent exposure. Because signing paths were not broken, many installations may have continued to operate without alerting operators to broken confidentiality; detection is non-trivial unless teams audited the specific encryption path or rotated keys proactively.
- Dependency propagation. Go modules are often vendored into binaries and images; a vulnerable module can persist in an image even after the upstream package is updated, unless rebuilt. This means patching must include rebuild and redeploy, not just updating a system package.
Action checklist (concise)
- Inventory any use of nkeys or nats-server in your apps, images, and infrastructure.
- If you find nkeys in versions 0.4.0–0.4.5, update to 0.4.6+ and rebuild artifacts.
- If you run NATS Server 2.10.0–2.10.3, upgrade to 2.10.4+.
- For Azure Linux images: apply Microsoft’s updates or patch the package in your VM images according to Microsoft’s guidance. Monitor MSRC/CVEs for updates.
- Rotate any secrets that were transported using xkeys-enabled code paths where exposure is plausible.
- Add SBOM and dependency scanning to CI to prevent hidden transitive dependencies from persisting in images.
Final takeaways
CVE-2023-46129 is a reminder that small coding mistakes in cryptographic code can produce catastrophic effects. The fix was straightforward in code — but the operational work is not: inventorying, rebuilding, redeploying, and rotating secrets across distributed systems is work-intensive.Microsoft’s public position is transparent: Azure Linux is the Microsoft product it has identified as including the vulnerable library, and Microsoft will update its CVE product mapping if additional Microsoft products are found to be affected. That is the authoritative statement for Microsoft customers, but it should not be the endpoint of your response: teams must scan and verify their own environments, update vulnerable modules and binaries, and treat this as a supply-chain incident that calls for rebuilds and secret rotation where necessary.
If you maintain infrastructure that could touch NATS or nkeys — whether in Azure, on-premises, or in containers — prioritize the inventory, the rebuilds, and the key rotations now. The technical fix exists; the operational challenge is ensuring the fix reaches every image and binary that matters.
Source: MSRC Security Update Guide - Microsoft Security Response Center