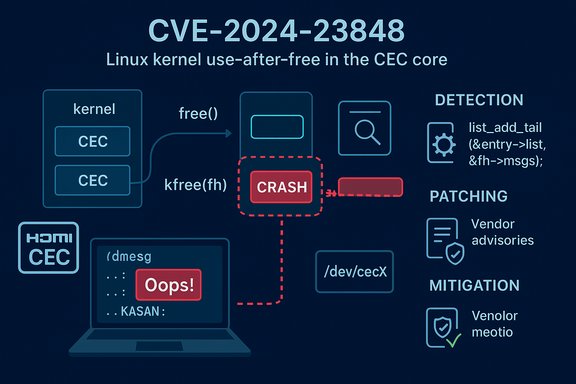
A newly documented Linux-kernel vulnerability, tracked as CVE-2024-23848, is a use‑after‑free in the kernel's Consumer Electronics Control (CEC) stack that can be triggered locally to produce a kernel oops or crash. The bug sits in the cec_queue_msg_fh path — code that handles file-handle messaging in the CEC core — and affects kernels through 6.7.1. Impact is availability-first: attackers with local access can cause sustained or persistent denial-of-service (service crash or host instability) on affected systems unless a patched kernel is installed. Practical exposure depends on whether a given kernel image contains the CEC driver and whether untrusted processes can reach the CEC device nodes. This article explains what went wrong, who is affected, how to detect it, and concrete steps for remediation and mitigation — with a critical appraisal of vendor response and operational risk.
The Linux CEC (Consumer Electronics Control) framework provides a kernel API for HDMI CEC hardware and creates device nodes (typically /dev/cecX) to let userspace read and write CEC messages. The interface is used by HDMI controllers, USB CEC adapters, media boxes and set‑top devices to implement coordinated remote-control and device control behaviors across HDMI chains. The kernel CEC core exports APIs such as cec_allocate_adapter, cec_register_adapter and creates /dev/cecX device nodes for userspace tools (cec-client, cec-ctl) to interact with the bus. CVE-2024-23848 was publicly recorded on 2024-01-23; NVD and multiple vendor advisories describe the defect as a use-after-free in cec_queue_msg_fh and list the affected files as drivers/media/cec/core/cec-adap.c and drivers/media/cec/core/cec-api.c. The canonical vulnerability entries and distribution advisories classify this as an availability‑focused issue with an overall Medium severity when scored (CVSS around 5.5 in many trackers).
A note on broader context: kernel-level availability flaws like CVE‑2024‑23848 highlight the operational fragility introduced when device driver teardown and concurrency interact incorrectly. The upstream response was timely and conservative, and distributions moved quickly to package fixes; the remaining risk is mainly operational (inventory, long-tail embedded images and appliance kernels). Administrators should treat this one as another instance where proactive inventory and standard kernel maintenance (apply vendor kernel updates, reboot, validate) eliminate the exposure with minimal system-level disruption. For practical detection and hunting guidance, review kernel logs for the cec function signatures mentioned above and prioritize remediation for any exposed, multi-tenant, or CI-facing hosts.
Concluding checklist (one-page summary)
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The Linux CEC (Consumer Electronics Control) framework provides a kernel API for HDMI CEC hardware and creates device nodes (typically /dev/cecX) to let userspace read and write CEC messages. The interface is used by HDMI controllers, USB CEC adapters, media boxes and set‑top devices to implement coordinated remote-control and device control behaviors across HDMI chains. The kernel CEC core exports APIs such as cec_allocate_adapter, cec_register_adapter and creates /dev/cecX device nodes for userspace tools (cec-client, cec-ctl) to interact with the bus. CVE-2024-23848 was publicly recorded on 2024-01-23; NVD and multiple vendor advisories describe the defect as a use-after-free in cec_queue_msg_fh and list the affected files as drivers/media/cec/core/cec-adap.c and drivers/media/cec/core/cec-api.c. The canonical vulnerability entries and distribution advisories classify this as an availability‑focused issue with an overall Medium severity when scored (CVSS around 5.5 in many trackers). Technical anatomy: what exactly went wrong
The root bug (brief, technical)
At a code level, the defect is a classic use‑after‑free. A kernel path that queues a CEC message into a file-handle's message list (cec_queue_msg_fh) may attempt to access fields of the file-handle structure after the structure has already been freed by another path. The result — in instrumentation builds or under kernel address sanitizers (KASAN) — is a "slab‑use‑after‑free" diagnostic; in production kernels that lack KASAN the behavior is typically a kernel oops, driver crash, or unpredictable host instability. Public kernel mailing‑list discussion and patches describe the failing list_add_tail(&entry->list, &fh->msgs) and a corresponding kfree(fh) from a different code path that frees the file-handle too early. The immediate symptoms observed by researchers include reproducible KASAN reports and Syzkaller reproducer programs that exercise cec_ioctl paths and trigger the faulty sequence. Kernel developers (notably maintainers and contributors on the LKML thread) proposed surgical fixes that add appropriate synchronization and ordering to prevent use-after-free and to guard interactions with file-handle lifetimes. Those patches are small and defensive in nature.Why this becomes an availability problem
A kernel-level use-after-free is dangerous because the kernel runs with full privileges and a NULL or dangling pointer dereference typically produces an oops or panic that stops normal execution. For this CVE the primary realistic outcome is denial-of-service: affected hosts can crash, enter an oops loop, or otherwise lose the impacted subsystem until reboot or a driver reload. Public trackers and distribution advisories therefore emphasize availability impact while noting no credible public evidence of privilege escalation at the time of disclosure. Nevertheless, kernel memory-safety bugs demand prompt remediation because heap corruption, if it occurs in particular allocator states, can sometimes be escalated to worse outcomes on some architectures.Who is affected — mapping scope and exposure
- Affected upstream kernels: the canonical public descriptions list Linux kernels through 6.7.1 as vulnerable (i.e., kernels at or before v6.7.1). Vendor and distribution advisories map that upstream range into their package trees.
- Which systems actually expose risk: Only kernels that include the CEC core and relevant drivers (drivers/media/cec/**) and where userspace or untrusted processes can interact with /dev/cecX are meaningfully exposed. On many desktops and embedded devices the CEC stack is present (for HDMI controllers, USB CEC adaptors, and SoC platforms). On servers and generic x86 cloud images the CEC driver is commonly absent or unused — risk is therefore lower for those systems unless the kernel image was built with CEC support.
- Long-tail exposures: Embedded devices, SoC vendor images, Android/embedded kernels, OEM firmware and appliance images commonly lag upstream. Those unmaintained or slowly updated kernels present the largest, practical exposure. Distribution kernels typically receive backports quickly but device vendors and appliance builders must be verified individually.
- Attack vector and privileges: The attack is local (AV:L); an attacker needs local code execution or an unprivileged process with access to CEC device nodes to trigger the faulty ioctl sequences. In some desktop or embedded setups that allow unprivileged access to /dev/cecX, the privileges required can be low. CVSS vectors commonly reflect AV:L/AC:L/PR:L/UI:N with Availability impact high.
How to detect and hunt for CVE-2024-23848
Detection in practice relies on kernel logs and host inventory:- Kernel oops / KASAN traces: Watch dmesg and journalctl for KASAN slab-use-after-free or OOPS traces that reference cec_queue_msg_fh, cec_transmit_msg_fh, or cec_api functions. The LKML reproducer discussion published explicit KASAN traces that identify the failing frames, which makes signature-based log detection practical for many environments.
- Device presence: Identify hosts with CEC device nodes: ls /dev/cec or use v4l-utils (cec-ctl) to enumerate adapters. The kernel CEC documentation documents that drivers register /dev/cecX device nodes via cec_register_adapter. If /dev/cec exists, the kernel CEC core is active on that host and should be assessed.
- Module / build-time checks: Check whether the kernel includes CEC support (CONFIG_CEC_CORE) or whether the cec module is loaded:
- uname -r
- grep -i CEC /boot/config-$(uname -r) (or zcat /proc/config.gz | grep CONFIG_CEC_CORE)
- lsmod | grep cec
These quick checks let you triage whether a host can ever load the vulnerable paths. - Reproducers: Security researchers used Syzkaller testers to reproduce the issue during disclosure. If you have a test host that you can sacrifice, a KASAN-enabled test build and the public reproducer can confirm presence and remediation — but do not run reproducer tests on production hosts.
Confirmed fixes and vendor advisories
Upstream kernel maintainers discussed and proposed fixes on the kernel mailing list; patches were focused, defensive changes to prevent the use-after-free by changing ordering, adding guard checks and ensuring proper cancellation/cleanup ordering. Distribution and vendor advisories (Ubuntu, Oracle/Oracle Linux, SUSE, AlmaLinux and others) subsequently published kernel security updates that map to the upstream stable fixes. The NVD entry and major distro advisories list the affected range as up to 6.7.1 and show status entries for vendor-supplied kernels. What to verify in vendor advisories:- Confirm your distribution’s kernel package includes the upstream stable commit IDs or an advisory referencing CVE-2024-23848.
- Prefer vendor-supplied kernel packages rather than hand-applying patches unless you maintain your own kernels and test rigorously.
- For embedded/OEM images ask the vendor for an explicit kernel/firmware image ID that includes the fix. Many vendor kernels need backporting; do not assume a cloud or appliance image is patched until the vendor says so.
Remediation: step-by-step actions
- Inventory and prioritize
- Run uname -r and identify kernels across your estate.
- Identify systems with CEC device nodes: ls /dev/cec* — devices present imply exposure. Use configuration management to find devices and images that include CEC drivers.
- Patch promptly (recommended)
- Install the vendor- or distribution-supplied kernel packages that include the upstream stable fix and schedule reboots. Most distributions issued security updates that include the fix. Confirm patch presence by checking the package changelog for CVE-2024-23848 or the upstream commit ID.
- If you cannot immediately patch, apply compensating controls
- Restrict access to CEC device nodes:
- Create a udev rule to set /dev/cec* ownership and permissions so that only a trusted group (e.g., cecadmin) may open them:
- Example udev rule (place in /etc/udev/rules.d/99-cec.rules):
- ACTION=="add|change", KERNEL=="cec[0-9]*", OWNER="root", GROUP="cecadmin", MODE="0660"
- Add only trusted users to the cecadmin group.
- Remove device passthrough from untrusted containers and CI runners (avoid --device=/dev/cecX).
- Unload or blacklist the CEC module (only where safe):
- modprobe -r cec (or the specific vendor module, if modular)
- Add blacklist entry in /etc/modprobe.d/ if you must prevent loading permanently.
- Warning: unloading or blacklisting the module will disable CEC behavior (remote-control integration, HDMI device control).
- Isolate hosts that must keep CEC: move them out of multi-tenant pools until patched.
- Test and validate
- After kernel updates, reboot hosts into the patched kernel.
- Validate CEC functionality on representative hardware (if CEC is required) and confirm no kernel oopses occur during typical CEC operations such as cec-ctl examinination or HDDMI hotplug sequences. If you maintain a test ring, run the earlier reproducers only in KASAN/test environments to confirm the vulnerability no longer triggers.
- Monitor and hunt
- Add SIEM/alerting rules that scan for kernel oops signatures:
- "KASAN: slab-use-after-free" with "cec_queue_msg_fh"
- "BUG: unable to handle kernel NULL pointer dereference" lines referencing cec functions
- Retain kernel logs and crash dumps for forensic triage during upgrades.
Practical mitigation examples (commands and udev sample)
- Check kernel and CEC device presence:
- uname -a
- zcat /proc/config.gz | grep CONFIG_CEC_CORE || grep -i CEC /boot/config-$(uname -r)
- lsmod | grep cec
- ls /dev/cec*
- Example udev rule (drop-in):
- /etc/udev/rules.d/99-cec.rules
- ACTION=="add|change", KERNEL=="cec[0-9]*", OWNER="root", GROUP="cecadmin", MODE="0660"
- Example module unload:
- sudo modprobe -r cec
- (Note: only possible if module is not built‑in and no dependent modules hold it.
Critical analysis — strengths, limits, and operational risks
Strengths in upstream response
- The upstream patching approach was surgical and defensive: developers proposed minimal changes to ordering and cleanup logic rather than large rewrites, which both minimizes regression risk and facilitates backports to stable branches. Kernel maintainers favor this style for small correctness fixes; that typically speeds distribution rollouts. LKML threads show maintainers iterating on small changes to cancel-delayed-work ordering and guard conditions.
- Distribution advisories and trackers (Ubuntu, Oracle Linux, SUSE, AlmaLinux and others) rapidly published kernel updates or mapped the CVE to their kernel packages, which provides a clear path for administrators to remediate via standard package channels.
Risks and blind spots
- Vendor / embedded lag remains the biggest operational problem. Devices with vendor-supplied kernels — set-top boxes, SoC-based media appliances, and some cloud marketplace/firmware images — may take much longer to receive fixes. The long tail of unpatched embedded kernels often represents the most likely place for lingering vulnerability. Operational teams should treat vendor kernels as distinct from distribution kernels and require explicit vendor confirmation when devices are in scope.
- Detection can be noisy. Kernel oops traces are clear when they occur, but not every vulnerable host will immediately show symptoms in logs: exploitation requires triggering the specific message-queue/file-handle sequences. Relying only on observed oopses undercounts exposure. Inventory and proactive patching remain primary controls.
- The initial public signal was availability-focused, and no reliable public proof-of-exploit for privilege escalation was available at disclosure; however, kernel memory-safety defects can evolve — and sophisticated attackers can sometimes chain allocator corruption into more serious primitives on specific platforms. Prioritize remediation in multi‑tenant and CI environments where local attacks are realistic and the blast radius is high.
Operational prioritization (recommended)
- Patch servers and appliances that expose /dev/cec* or that explicitly load CEC modules, especially multi‑tenant hosts and devices used in media/AV pipeline appliances.
- For hosts where firmware/vendor fixes are absent, implement the udev/module mitigation and isolate devices from untrusted workloads.
- Maintain a short lifecycle for reboots after kernel updates; kernel fixes require a reboot to take effect.
Detection, telemetry and incident‑response checklist
- Add SIEM rules for kernel traces that include:
- "cec_queue_msg_fh"
- "KASAN: slab-use-after-free" and "cec"
- "BUG: spinlock recursion", "NULL pointer dereference" lines referencing cec functions (if present in your environment)
- If you find an oops matching the cec stack trace:
- Capture dmesg and /var/log/kern.log immediately.
- Reproduce in a test environment (if safe) to confirm before and after applying suspected patches.
- Identify the process that invoked the ioctl from the oops call trace (often present in usermode info in the trace).
- Schedule remediation (patch and reboot) as high priority for the host.
- After patching:
- Reboot hosts and rerun the workload that previously triggered the oops to confirm the issue is resolved.
- Validate with representative hardware if CEC functionality is required in production.
Final verdict — what administrators should do now (practical checklist)
- Inventory: Identify systems with CEC support (ls /dev/cec*, check kernel config, lsmod | grep cec).
- Patch: Apply vendor or distribution kernel updates that include the CVE-2024-23848 fix and reboot at your earliest maintenance window.
- Mitigate: If you cannot patch quickly:
- Restrict /dev/cec* access via udev.
- Remove CEC device passthrough from containers/CI.
- Unload/blacklist modules where safe and acceptable.
- Monitor: Add SIEM alerts for cec-related kernel oops or KASAN traces and collect kernel logs for any incidents.
- Vendor follow-up: For embedded/OEM images, request explicit firmware/kernel image identifiers that include the fix and schedule upgrades for long-tail devices.
A note on broader context: kernel-level availability flaws like CVE‑2024‑23848 highlight the operational fragility introduced when device driver teardown and concurrency interact incorrectly. The upstream response was timely and conservative, and distributions moved quickly to package fixes; the remaining risk is mainly operational (inventory, long-tail embedded images and appliance kernels). Administrators should treat this one as another instance where proactive inventory and standard kernel maintenance (apply vendor kernel updates, reboot, validate) eliminate the exposure with minimal system-level disruption. For practical detection and hunting guidance, review kernel logs for the cec function signatures mentioned above and prioritize remediation for any exposed, multi-tenant, or CI-facing hosts.
Concluding checklist (one-page summary)
- Confirm whether your kernels are at or below 6.7.1 and whether CEC is present.
- If CEC is present, apply vendor kernel updates that reference CVE‑2024‑23848 or the corresponding stable commit IDs.
- If you cannot patch immediately, restrict access to /dev/cec*, avoid device passthrough to untrusted containers, and, where safe, unload/blacklist the CEC module.
- Monitor dmesg and kernel logs for cec oops/KASAN traces and confirm remediation with a controlled repro in a test environment.
Source: MSRC Security Update Guide - Microsoft Security Response Center