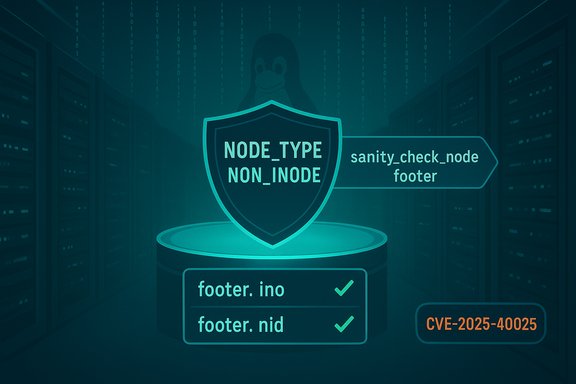
A targeted kernel fix for F2FS that guards against malformed node footers has been landed upstream and assigned CVE‑2025‑40025, closing a small but potentially disruptive path to kernel panics when specially crafted F2FS images are processed. The change introduces a new node type and tightens the sanity_check_node_footer logic so that a non‑inode dnode cannot be misinterpreted as an inode — a condition that, under fuzzing, could drive the filesystem into an assertion and kernel oops.
F2FS (Flash-Friendly File System) is a flash‑optimized Linux filesystem commonly used on embedded devices, Android phones, and other systems that rely on NAND/flash storage semantics. Recent automated testing (syzbot / syzkaller) surfaced a scenario where a dnode that is not an inode nevertheless contains footer fields that match inode identifiers. When that mistaken identity is treated as an inode, subsequent computations of block address counts become incorrect and can reduce an expected non‑zero count to zero, triggering an internal kernel assertion and a panic during truncation operations. The NVD summary of CVE‑2025‑40025 captures the failure trace and the high‑level remediation approach. The upstream patch, authored and submitted to f2fs maintainers, takes a surgical approach: introduce a dedicated node type (NODE_TYPE_NON_INODE) and pass the node type into the existing footer sanity check so that the code will detect and reject a non‑inode dnode that happens to carry inode‑like footer fields. That patch and its review thread are visible in upstream kernel mailings and stable commit streams.
count = min(end_offset - dn.ofs_in_node, pg_end - pg_start);
can evaluate to zero. Later code explicitly asserts that count must be non‑zero; hitting that assertion causes the kernel to OOPS. This is an availability impact (panic/host crash) rather than a direct information‑disclosure or remote code‑execution primitive, but a denial‑of‑service on a multi‑tenant host is still high impact.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
F2FS (Flash-Friendly File System) is a flash‑optimized Linux filesystem commonly used on embedded devices, Android phones, and other systems that rely on NAND/flash storage semantics. Recent automated testing (syzbot / syzkaller) surfaced a scenario where a dnode that is not an inode nevertheless contains footer fields that match inode identifiers. When that mistaken identity is treated as an inode, subsequent computations of block address counts become incorrect and can reduce an expected non‑zero count to zero, triggering an internal kernel assertion and a panic during truncation operations. The NVD summary of CVE‑2025‑40025 captures the failure trace and the high‑level remediation approach. The upstream patch, authored and submitted to f2fs maintainers, takes a surgical approach: introduce a dedicated node type (NODE_TYPE_NON_INODE) and pass the node type into the existing footer sanity check so that the code will detect and reject a non‑inode dnode that happens to carry inode‑like footer fields. That patch and its review thread are visible in upstream kernel mailings and stable commit streams. What went wrong: technical anatomy
How the failure manifests
Under a fuzzed or intentionally corrupted image, F2FS can encounter an inconsistent truncation range in direct node during the truncation/hole‑punching path. The kernel oops trace recorded by syzbot shows the failure starts in f2fs_truncate_hole and bubbles up through f2fs_punch_hole and f2fs_fallocate before provoking a kernel BUG. The core root cause is a mis‑parsing of a dnode as an inode when the footer fields (footer.ino and footer.nid) coincide by chance or are maliciously set.Why parsing as an inode is dangerous here
When a dnode is misinterpreted as an inode, helper macros/functions that compute the number of block addresses per page (ADDRS_PER_PAGE or similar) return counts that do not reflect the actual dnode layout. Combined with an ofs_in_node value that by chance mirrors a computed count (the report cites 923 as an example), an arithmetic expression:count = min(end_offset - dn.ofs_in_node, pg_end - pg_start);
can evaluate to zero. Later code explicitly asserts that count must be non‑zero; hitting that assertion causes the kernel to OOPS. This is an availability impact (panic/host crash) rather than a direct information‑disclosure or remote code‑execution primitive, but a denial‑of‑service on a multi‑tenant host is still high impact.
Reproducer notes
Upstream and vulnerability feeds include a concrete reproducer sequence that demonstrates how to construct an image and provoke the condition. The repro blends normal F2FS creation and writes with an image injection tool that mutates node metadata, then mounts and issues a punch‑hole operation to trigger truncation logic. The presence of concrete reproduce steps increases confidence in the diagnosis while also reinforcing the need to treat vulnerable hosts as exposed until patched.The fix: what changed upstream
The upstream contribution introduces:- A new enumerated node type: NODE_TYPE_NON_INODE.
- Modifications to the node parsing path so f2fs_get_node_folio passes the node type into sanity_check_node_footer.
- Additional logic inside the sanity checker to detect when a node that is not an inode nonetheless carries inode‑like footer identifiers and to reject that node as corrupted.
Timeline, propagation, and vendor tracking
- The patch was posted to the Linux kernel mailing lists and f2fs development flow in August 2025 and flagged for stable backporting.
- The CVE entry (CVE‑2025‑40025) and NVD record appeared in public trackers in late October 2025, documenting the vulnerability and mapping it to the upstream commit(s) that fix the issue.
- Distribution trackers (Debian vulnerability tracker) and open‑source vulnerability databases imported the CVE and enumerated package versions that remain vulnerable until the stable fixes are merged into those distribution kernels. Administrators must verify their distro changelogs for the upstream commit or CVE references before claiming a host is patched.
Impact assessment: who should care and why
- Systems that mount F2FS partitions: desktop/server hosts, Android devices, embedded appliances that mount F2FS images — especially those that accept untrusted images — are potentially exposed until patched.
- Multi‑tenant hosts and shared infrastructure: cloud hosts or virtualization nodes where one workload can influence a host filesystem or supply images to be mounted have elevated risk because a local kernel panic affects all tenants.
- Vendor/OEM kernels: devices running vendor‑supplied kernels (e.g., many Android devices and appliance images) are the longest tail; vendors may lag upstream backports, leaving devices vulnerable for extended periods.
Detection, telemetry, and incident response
Practical detection should focus on operational artifacts rather than signatures:- Look for kernel oops/panic entries referencing f2fs_truncate_hole, f2fs_punch_hole, fs/f2fs/file.c or any stack frames that include compress/truncate helpers. Repeated or recent oops traces in these code paths are a strong indicator.
- In fuzzing and test environments, KASAN/KMSAN traces that point to node footer parsing are clear reproducer artifacts; sanitize‑enabled builds are helpful in R&D but not typical in production.
- If you suspect an attempt to trigger the condition in production, preserve crash logs and memory snapshots before rebooting. Forensic captures (vmcore, dmesg, journalctl) are necessary to determine whether a crash was accidental or deliberately provoked.
Recommended remediation and mitigation (practical playbook)
Immediate priorities:- Inventory — Identify hosts that mount F2FS or may process F2FS images:
- Commands: uname -r; findmnt -t f2fs; grep f2fs /proc/filesystems; lsmod | grep f2fs.
- Patch — Apply vendor/distribution kernel updates that include the upstream fix and reboot into the patched kernel. This is the only complete remediation. Confirm changelog or package notes reference CVE‑2025‑40025 or the upstream commit.
- Short‑term mitigations if immediate patching is impossible:
- Restrict who can mount filesystems or create loop devices; remove or disable F2FS mounts on hosts that process untrusted images.
- Move image ingestion or image‑processing workloads to isolated hosts that can be patched rapidly or that do not include F2FS support.
- Increase monitoring for repeated kernel oops traces and set alerts on F2FS related call stacks. Preserve logs for forensic analysis.
- Test the patched kernel in a representative pilot group that exercises filesystem operations, including truncation/punch hole operations.
- Validate that the kernel changelog includes the upstream commit or CVE mapping before broad rollout.
- Roll out using a phased approach with rollback plans and increase telemetry retention during the window.
Why the upstream fix is reassuring — and where residual risk remains
Strengths of the upstream patch:- Surgical change: the fix is narrowly focused — adding a node type and passing it into an existing validation helper — which reduces regression risk. Kernel maintainers favor such small, well‑defined edits for correctness bugs because they are easier to review and backport.
- Fast to backport: small diffs are straightforward to apply across stable branches; the patch was flagged to stable lists and referenced in vendor trackers.
- Vendor lag: embedded vendors and OEMs may delay shipping backports. Organizations using vendor images must coordinate with vendors or plan local patching.
- Local attack surface: because the exploit model requires the ability to supply or mount crafted images (or run code on the host), systems that operate on untrusted images remain at risk until patched. Prioritize those hosts.
- Unverified weaponization claims: absent a public PoC, treat claims of remote exploitation as speculative. If a PoC emerges, re‑evaluate urgency and mitigation posture accordingly.
Broader lessons for operators and kernel reviewers
- Small arithmetic and parsing mistakes in kernel filesystem code can produce high‑impact availability faults; defensive validation of on‑disk structures is essential.
- Automated fuzzing and sanitizer tooling (syzbot/KMSAN/KASAN) continue to be highly effective at surfacing corner cases that human review can miss; the community workflow of fuzz → patch → stable backport remains critical to system hardening.
- Operators must maintain an inventory of vendor kernels in their fleet and require transparent patch timetables from OEMs for devices that ship with kernel‑level filesystems like F2FS. The long tail of embedded devices is the predictable weak link.
What we verified and what is still uncertain
Verified facts:- The technical root cause — misinterpreting certain non‑inode dnodes as inodes due to matching footer.ino and footer.nid — is described in the upstream patch and CVE metadata.
- The upstream patch was submitted, reviewed, and queued for stable backport, and the CVE record maps to the upstream commits.
- Distribution trackers (Debian) list versions that remain vulnerable until they absorb the stable patch; operators should confirm vendor changelogs before assuming remediation.
- There is no authoritative, public proof‑of‑concept demonstrating remote exploitation or privilege escalation using this specific bug as of the public records consulted. Treat statements to the contrary with caution until independent researchers publish reproducible PoCs.
Recommended checklist for WindowsForum readers responsible for mixed fleets
- Inventory: run findmnt -t f2fs and grep /proc/filesystems to locate F2FS usage. Confirm kernel package versions (uname -r) and consult vendor trackers for CVE‑2025‑40025 mappings.
- Patch: apply distribution or vendor kernel updates that explicitly reference CVE‑2025‑40025 or the upstream commit ID and reboot. Test in a pilot group before broad rollout.
- Mitigate: isolate untrusted image processing and restrict mount capabilities until patches are available. Increase logging and alerting for F2FS‑related oops messages.
- Validate: after patching, confirm that kernel logs no longer include the old traces, and that the kernel changelog or package release notes mention the CVE or upstream commit.
Conclusion
CVE‑2025‑40025 is a focused, upstream‑addressed Linux kernel vulnerability in the F2FS node parsing path that exposes hosts to kernel oopses when malformed or fuzzed images are processed. The upstream remedy is small, low‑risk, and designed to be backportable across stable kernels: introduce a non‑inode node type and use it to strengthen footer sanity checks so a non‑inode dnode cannot masquerade as an inode. Operators should treat this as a patch‑and‑reboot item for hosts that mount F2FS volumes or consume third‑party F2FS images, with priority given to multi‑tenant and image‑processing infrastructure. Verify vendor and distribution advisories for the exact package mappings, apply updates in a staged rollout, and tighten mount privileges and logging until remediation is confirmed.Source: MSRC Security Update Guide - Microsoft Security Response Center