A newly assigned vulnerability, CVE-2025-68746, exposes a race condition in the Linux kernel's Tegra QSPI driver (spi-tegra210-quad) that can leave the driver holding a stale transfer pointer after a timeout — a condition that may cause kernel instability and spurious transfer failures on systems using the Tegra210 QSPI controller.
The affected code lives in the spi-tegra210-quad driver, the Linux kernel component that implements support for the NVIDIA Tegra QSPI (Quad SPI) controller found on Tegra-class SoCs. This QSPI controller is responsible for handling quad-SPI flash operations (command/address/data phases) and is built into kernel trees as the CONFIG_SPI_TEGRA210_QUAD driver module. Systems that enable this driver — typically embedded Linux platforms running on Tegra210 and later Tegra SoCs — may be exposed when specific timing and CPU-load conditions align. The vulnerability was assigned CVE-2025-68746 and described in upstream advisories and vulnerability aggregators as a timeout handling bug that was fixed by a targeted patch series in the kernel SPI driver. The kernel-level fix clears an internal transfer pointer on timeout and hardens the IRQ-handling logic so that subsequent IRQ-thread work checks for a NULL transfer pointer before proceeding.
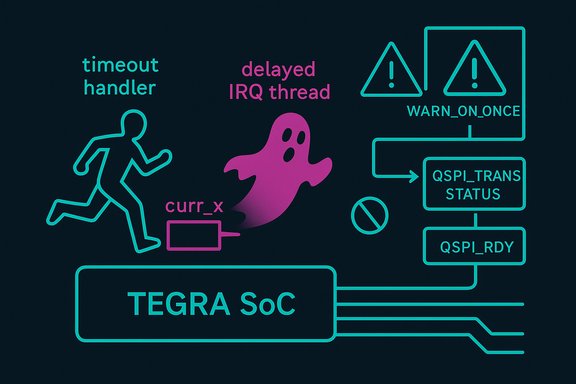
The bug arises when the CPU where the QSPI IRQ thread is supposed to run (commonly CPU 0 on many Tegra boards) becomes heavily loaded or otherwise preempted. In that rare scenario, the IRQ thread may not run before the wait_for_completion_timeout call expires. The driver's timeout path performs cleanup and marks the message as failed, but it did not clear the driver's pointer to the current transfer (commonly named curr_xfer or currxfer in different patches), leaving that pointer referencing memory that may already have been freed or otherwise invalidated. If the delayed IRQ thread later runs and attempts to act on that stale pointer, the result can be memory corruption, kernel warnings, or crash-like behavior depending on timing. To address the immediate issue, the patch clears curr_xfer on timeout and adds a check in the IRQ thread so it no longer dereferences a NULL/cleared transfer pointer. The patch also ensures interrupts are cleared on failure paths so new interrupts can be serviced. This sequence is a classic race between a timeout handler and a delayed IRQ thread: the timeout path assumes it owns the transfer cleanup, while the deferred IRQ path may still expect to find a valid transfer to finish. The fix removes the ambiguity by explicitly nulling out the transfer and guarding the IRQ thread against acting on a stale request.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
The affected code lives in the spi-tegra210-quad driver, the Linux kernel component that implements support for the NVIDIA Tegra QSPI (Quad SPI) controller found on Tegra-class SoCs. This QSPI controller is responsible for handling quad-SPI flash operations (command/address/data phases) and is built into kernel trees as the CONFIG_SPI_TEGRA210_QUAD driver module. Systems that enable this driver — typically embedded Linux platforms running on Tegra210 and later Tegra SoCs — may be exposed when specific timing and CPU-load conditions align. The vulnerability was assigned CVE-2025-68746 and described in upstream advisories and vulnerability aggregators as a timeout handling bug that was fixed by a targeted patch series in the kernel SPI driver. The kernel-level fix clears an internal transfer pointer on timeout and hardens the IRQ-handling logic so that subsequent IRQ-thread work checks for a NULL transfer pointer before proceeding. What happened: technical summary
Under normal operation, the Tegra QSPI driver schedules memory transfers (DMA or PIO) and waits for a completion event signaled by the IRQ thread that services the QSPI interrupt. The driver uses wait_for_completion_timeout to bound how long it will wait for that IRQ-driven completion.The bug arises when the CPU where the QSPI IRQ thread is supposed to run (commonly CPU 0 on many Tegra boards) becomes heavily loaded or otherwise preempted. In that rare scenario, the IRQ thread may not run before the wait_for_completion_timeout call expires. The driver's timeout path performs cleanup and marks the message as failed, but it did not clear the driver's pointer to the current transfer (commonly named curr_xfer or currxfer in different patches), leaving that pointer referencing memory that may already have been freed or otherwise invalidated. If the delayed IRQ thread later runs and attempts to act on that stale pointer, the result can be memory corruption, kernel warnings, or crash-like behavior depending on timing. To address the immediate issue, the patch clears curr_xfer on timeout and adds a check in the IRQ thread so it no longer dereferences a NULL/cleared transfer pointer. The patch also ensures interrupts are cleared on failure paths so new interrupts can be serviced. This sequence is a classic race between a timeout handler and a delayed IRQ thread: the timeout path assumes it owns the transfer cleanup, while the deferred IRQ path may still expect to find a valid transfer to finish. The fix removes the ambiguity by explicitly nulling out the transfer and guarding the IRQ thread against acting on a stale request.
Evidence and upstream patches
The Tegra QSPI timeout fixes were developed and discussed openly on kernel mailing lists and patch trackers. The patch series submitted by driver maintainers and contributors includes:- A minimal fix that clears the transfer pointer on timeout and ensures interrupts are cleared on failure paths. This change prevents the IRQ thread from accessing freed memory after a timed-out transfer.
- A refinement to limit excessive kernel warnings by replacing WARN_ON with WARN_ON_ONCE for repeated timeout conditions, reducing log spam while retaining diagnostic messages.
- A broader set of changes that refactor error/cleanup routines into helper functions and add logic to inspect hardware status on timeout. The latter checks the QSPI controller status register to determine whether a timeout represented a genuine hardware failure or simply a delayed interrupt; if the hardware reports completion, the driver invokes the completion path instead of treating the transfer as failed. That change reduces false negatives for transfer completion under heavy CPU load.
Who and what is affected
- The vulnerability is a Linux kernel issue in the drivers/spi/spi-tegra210-quad.c code path. Any Linux kernel build that enables the spi-tegra210-quad driver (built-in or as a module) is conceptually affected. Distribution kernels that include the driver in their builds and devices that rely on Tegra QSPI hardware are the practical exposure surface.
- Specific product-level impact depends on whether a vendor/distribution maintains a kernel version that contains the vulnerable code and whether that kernel includes the Tegra QSPI driver. The public advisories list the vulnerability as affecting Linux kernels broadly, but the real-world affected set is smaller — embedded Tegra platforms that use the QSPI controller in production (for flash accesses, firmware updates, TPM-like interfaces, etc.. The vulnerability record does not enumerate OEM products by name, so administrators must rely on distribution security notices and vendor kernel changelogs to determine whether their devices have received the fix.
Severity and exploitability
Official aggregators and vulnerability scanning vendors currently classify the issue as medium severity. One widely referenced scoring (published by Tenable) lists CVSS v3 at 5.5 (Medium) with vector AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H — reflecting a local attack vector and primarily availability impact (denial-of-service or instability). In practical terms, the bug is not a remote network wormhole; it requires code or actions that cause QSPI transfers to be started and the target machine to allow the specific race conditions to occur (e.g., CPU saturation or delayed IRQ handling). The public descriptions emphasize memory-pointer staleness (curr_xfer pointing at stale memory), which raises the theoretical risk that delayed code paths could dereference freed memory. That pattern can sometimes lead to use-after-free style memory corruption with more serious consequences (kernel oops, arbitrary code execution) in other contexts. However, neither the upstream advisory nor the published patches assert that remote code execution is possible, and the published scoring and commentary focus on spurious failures and availability impact rather than guaranteed code execution. Treat claims of privilege escalation or RCE as speculative unless a concrete exploit or proof-of-concept is published.Why this bug matters in the wild
- Embedded and industrial systems often rely on QSPI flash stacks for boot, firmware updates, and runtime storage; spurious failures or corruption in the QSPI path can translate to boot failures, failed firmware updates, or inability to access critical peripherals.
- The condition is timing-dependent and occurs under heavy CPU load or when IRQ threads are delayed. That makes the vulnerability non-deterministic — hard to trigger predictably, but observed in production under RAS firmware activity, error-injection testing, and CPU saturation scenarios used by the developer community when diagnosing the problem.
- Linux is commonly used on Tegra SoC platforms across robotics, embedded AI appliances, and edge servers. Any production fleet using Tegra-based hardware and relying on the QSPI path needs to evaluate whether their deployments use the affected driver.
Patch and remediation guidance
Upstream developers produced a multi-part patch series to address both the immediate flaw and edge-case behaviors that lead to it. Recommended actions for administrators and system maintainers are:- Apply upstream kernel fixes or update to a distribution kernel that includes the patched code. The patch series is available in the public kernel mailing lists and patch trackers; distributions are expected to backport or include the changes in their kernel updates.
- For systems with vendor-managed kernels (e.g., SoC vendors or appliance vendors), monitor vendor security advisories and pull vendor-supplied kernel updates as they become available. Many vendors will backport the fix rather than upgrading the entire kernel.
- If immediate updating is not possible, mitigate risk by minimizing workloads that can saturate the CPU core running the QSPI IRQ thread. While this is operationally blunt and not a secure long-term solution, it can reduce the incidence of the timing window that triggers the race. Note that this is a stopgap; the driver fix must be applied for true remediation.
- If performing kernel maintenance, audit whether CONFIG_SPI_TEGRA210_QUAD is enabled in your kernel build. If the driver is not required for your platform, consider disabling it in custom kernel builds to remove the attack surface. This must be balanced against functional needs (e.g., boot-from-QSPI or in-field update features).
- Check your kernel version and whether spi-tegra210-quad is present (lsmod, zgrep in /proc/config.gz, or check your distribution's kernel config).
- Search your distribution's security tracker and change log for CVE-2025-68746; apply any vendor- or distro-supplied packages that reference the CVE.
- If using upstream kernels, pull the set of patches submitted by the Tegra maintainers or cherry-pick the commits into your stable kernel branch, test in staging, then roll to production.
What the patches change in code (concise)
- Clear the driver’s internal transfer pointer (curr_xfer) when a transfer times out, preventing later IRQ-thread code from dereferencing freed data.
- Add defensive checks in the IRQ thread to guard against null/cleared curr_xfer before acting.
- Ensure interrupts are cleared on failure paths so that the controller can generate new interrupts and the IRQ-thread remains functional.
- Reduce logging spam by replacing repeated WARN_ON invocations with WARN_ON_ONCE in timeout code paths so that only the first occurrence prints a full stack backtrace. This balances visibility for debugging with operational log hygiene.
- Add a hardware-status probe in timeouts (reading QSPI_TRANS_STATUS QSPI_RDY bit) to distinguish a true hardware timeout from an interrupt that was delayed; if the hardware completed the transfer, the driver will manually run the completion handler rather than incorrectly failing the transfer.
Analysis: strengths of the fix
- The patch series is pragmatic and layered: it addresses the immediate pointer-staleness bug while also improving diagnostics and reducing false failures. That reduces both crash risk and operational noise.
- The hardware-status check is a strong engineering move: instead of relying purely on software timeout semantics, the driver now consults the controller's own status to validate whether the transfer actually failed. That makes the driver resilient against transient scheduling delays — a real-world problem for busy embedded platforms.
- The code hygiene changes (refactoring cleanup into helper functions; replacing WARN_ON with WARN_ON_ONCE) increase maintainability and reduce the cost of triaging related bugs. These are defensive programming wins that will reduce the chance of a similar regression in the future.
Analysis: remaining risks and limitations
- The fixes are targeted; they reduce the race and handle the most critical failure modes, but maintainers note that a more thorough fix would move the interrupt clearing into a hard IRQ handler and rework the IRQ thread signaling so the IRQ thread is not scheduled when a transfer has already timed out. Those changes are more invasive and were explicitly deferred in favor of smaller, reviewable patches. This means a latent class of race conditions could remain if further architectural changes are not made.
- The patch series depends on upstream review and distribution backports. For devices on vendor kernels (long-term support kernels maintained by boards or OEMs), tracking whether the patch was backported is non-trivial. Some vendors may delay inclusion, leaving devices exposed despite upstream fixes. Administrators must verify vendor release notes and kernel changelogs rather than assuming consumers or appliances are automatically protected.
- While the public advisories emphasize availability impact, the code pattern (stale pointer + delayed IRQ handling) can in theory be escalated to more serious memory corruption in some contexts. There’s no verified exploit in the public record at the time of writing; treating the possibility as speculative is prudent until reproducible exploit code or deeper analysis surfaces. Maintain vigilance in systems where kernel memory integrity is critical.
Practical checklist for engineers and integrators
- Inventory: Identify all devices and kernels that run on Tegra SoCs and list whether the spi-tegra210-quad driver is compiled in or loaded. Use kernel config inspection and boot logs to locate driver presence.
- Patch: Prioritize applying vendor-provided kernel updates that reference CVE-2025-68746, or backport the minimal fixes from the upstream patch series into your maintenance branch. Test aggressively in a staging environment that recreates heavy-load conditions.
- Monitor: Watch for kernel OOPS, repeated QSPI WARN messages, or failed firmware updates that correlate with heavy CPU usage — these symptoms are consistent with the pre-fix failure modes. Replace repeated WARN_ON spam with fix-backed kernels to reduce noise that hides real issues.
- Operational mitigations: Where patching is temporarily impossible, minimize synthetic CPU saturation on the target CPU, avoid heavy background tasks that can delay IRQ-thread scheduling, and schedule firmware updates when devices are under low load. This is a short-term mitigation and not an acceptable long-term substitute for patching.
Conclusion
CVE-2025-68746 is a meaningful but managed kernel flaw: a race in the Tegra QSPI driver that could leave the driver referencing stale memory after a transfer timeout. The engineering response in the upstream patch series is practical — nulling stale pointers, defending IRQ-thread behavior, reducing log spam, and adding hardware-status checks to distinguish real timeouts from delayed IRQs — and addresses both the immediate stability risk and the operational noise that made diagnosis difficult. The vulnerability underscores the fragility of interrupt-driven, timing-sensitive kernel code on systems that face heavy load or unusual firmware activity. For operators of Tegra-based Linux devices, the concrete actions are clear: confirm whether the spi-tegra210-quad driver is in use, apply vendor or distribution kernel updates that reference CVE-2025-68746 (or the upstream patch series), and, while patches are staged, avoid operational profiles that increase the likelihood of the IRQ-thread delays that created the window for this bug. Administrators should treat vendor kernel advisories as authoritative for shipped devices and track backport status closely — a patched upstream kernel does not automatically mean every production device is protected. Administrators and kernel integrators with Tegra deployments should prioritize remediation and testing over workaround reliance; the fix is available upstream and the patch discussion provides clear guidance for maintainers and integrators seeking to close the window on this timing-sensitive flaw.Source: MSRC Security Update Guide - Microsoft Security Response Center