 Background
Background
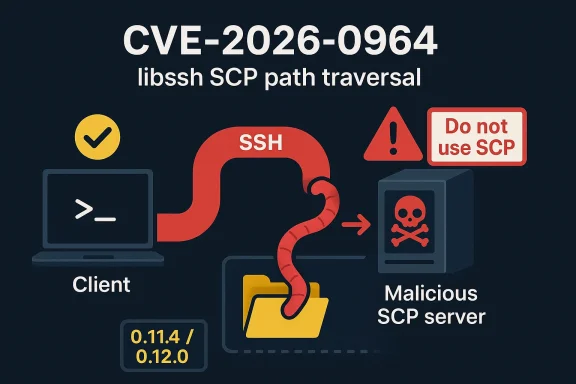
CVE-2026-0964 is a path traversal vulnerability in libssh’s SCP client API, specifically in ssh_scp_pull_request(). In practical terms, a malicious SCP server can feed a client an unexpected path and trick the application into writing a file somewhere other than the intended working directory. The libssh advisory describes the flaw as improper sanitation of paths received from SCP servers, and notes that the issue can be used to plant malicious executables or configuration files that may later be run or loaded by the victim system. (libssh.org)The important detail is that this is not a server-side file write bug in libssh itself. The library does not directly perform the unsafe write; rather, it returns metadata to the application, and the application may then create or overwrite a local file based on that metadata. That distinction matters because it shifts the security boundary toward the caller, while still leaving libssh responsible for passing along attacker-controlled path data in a dangerous way. (libssh.org)
The advisory also makes an explicit historical comparison: it says the issue is the same class of problem as OpenSSH CVE-2019-6111. That older issue became a reference point for SCP hardening because it exposed the longstanding tension between SCP’s simple protocol design and the assumptions client software makes about filenames returned by remote servers. In other words, this is not a novel bug pattern so much as a familiar one resurfacing in a widely used SSH stack. (libssh.org)
The CVSS vector published by libssh is 5.0 medium, with network attack vector but high attack complexity and user interaction required. That tells us the issue is serious, but not effortless to exploit at scale. An attacker needs a victim to speak SCP to a malicious or compromised server, and the victim must then act on the returned path in a vulnerable way. (libssh.org)
What makes CVE-2026-0964 especially relevant to WindowsForum readers is that it lands at the intersection of legacy file transfer behavior, enterprise automation, and supply-chain-style trust assumptions. SCP is old, familiar, and often embedded in scripts, appliances, or administrative tooling. That combination tends to keep bugs like this alive long after the broader industry has moved on to safer alternatives. (libssh.org)
What the Vulnerability Actually Does
At its core, the flaw allows a malicious SCP server to influence where a client-side application believes a file should be written. If the application trusts the filename or path returned by libssh without validating it, the server can steer the write outside the intended directory. That can lead to overwriting sensitive files, dropping malicious code, or corrupting application configuration. (libssh.org)The danger is magnified by the way SCP is often used in automation. Many deployment scripts assume the remote side is trustworthy, and they may pass paths straight into file-handling logic without performing strict checks. In a well-behaved environment, that shortcut is fine; in a hostile environment, it creates a clean opening for path traversal. (libssh.org)
Why path traversal matters here
Path traversal is not only about escaping../ segments. It is about any mechanism that causes the receiving software to honor a location outside the intended sandbox. In this case, the malicious server can send unexpected path data that persuades the client to override files elsewhere on disk. That can have consequences far beyond the transfer itself because a single overwritten file can become a persistence mechanism or a launch point for later execution. (libssh.org)A subtle but important point is that the attacker does not need to win a race condition or break encryption. The issue sits at the protocol/application boundary, where a legitimate encrypted session still carries attacker-controlled data. That is one reason SSH-related bugs can be deceptive: the transport is secure, but the semantics of the data inside the tunnel are still risky. (libssh.org)
- The attack is server-driven, not client-driven.
- The payload is path metadata, not a malformed binary blob.
- The impact depends heavily on how the calling application handles the returned filename.
- The issue becomes more dangerous when scripts run with elevated privileges.
- The bug is amplified when applications assume SCP replies are inherently trustworthy. (libssh.org)
Why CVE-2026-0964 Is a Real-World Risk
The advisory makes clear that a malicious SCP server can cause the client application to overwrite local files outside the working directory. That is a direct route to malicious file placement, and in many environments, malicious file placement is enough to gain a foothold. A compromised configuration file can redirect services, a planted script can be executed later, and an overwritten binary can alter behavior in ways that are hard to trace. (libssh.org)This is why the issue is not just theoretical. Administrative workflows often rely on trust chains that are difficult to audit end-to-end. If a backup job, transfer agent, or orchestration script fetches a file via SCP and then writes it to disk, a hostile server can turn a routine operation into a delivery vehicle for persistence. (libssh.org)
Enterprise impact versus consumer impact
For consumers, the most likely risk is limited and situational. A user would need to connect to a malicious SCP server and then act on the transferred file or a file it overwrote. That is annoying and potentially dangerous, but it is still constrained by user behavior and by how much the affected software trusts the transfer result. (libssh.org)For enterprises, the exposure is broader because SCP is often used in scripted, unattended, or semi-automated flows. A single vulnerable integration can affect many endpoints, especially if it runs with service privileges or writes into shared locations. In that setting, a medium CVSS score can still represent a substantial operational risk. (libssh.org)
- Scheduled transfer jobs may run without direct supervision.
- Service accounts often have more filesystem access than end users.
- Overwritten configuration files can alter downstream services.
- Malicious files can be staged for later execution.
- Shared scripts can propagate the problem across many machines. (libssh.org)
How the Attack Works in Practice
In a typical SCP flow, the client requests a file and receives metadata that includes a target name. If the client application assumes that the returned name is safe, it may create or overwrite a local file using that path. With CVE-2026-0964, the malicious server can manipulate that metadata so the client writes somewhere unexpected. (libssh.org)The simplest exploitation scenario is a user downloading a file from a malicious server that returns a crafted path. A more dangerous scenario involves an administrative script that performs unattended transfers and then saves the file into a privileged or shared location. The difference is not just convenience; it is the difference between a nuisance and a reliable foothold. (libssh.org)
The role of user interaction
Libssh rates the issue as requiring UI:R, which means some form of user action is needed. That does not mean the victim must explicitly approve a dangerous prompt; in practice, it can mean the user initiates the transfer or runs a script that does it. That is a common pattern in file-transfer vulnerabilities, because the protocol itself is only one step in a longer workflow. (libssh.org)Another important wrinkle is that the library’s own wording emphasizes the application’s responsibility to validate the filename returned by
ssh_scp_request_get_filename(). That implies the secure path is not simply “upgrade libssh and forget it,” but “upgrade libssh and also audit every caller that trusts SCP path metadata.” (libssh.org)- A malicious server controls the returned pathname.
- The client may write outside its intended directory.
- The issue becomes worse when the caller runs with elevated privileges.
- Validation in the application remains essential.
- Legacy SCP assumptions are the root of the risk. (libssh.org)
Libssh’s Response and Security Release
Libssh fixed CVE-2026-0964 in the 0.11.4 and 0.12.0 security releases, both published on February 10, 2026. The advisory says patches were posted and urges administrators to upgrade or apply the patch as soon as possible. That is the standard and correct response to a client-side path traversal bug: reduce exposure quickly, then make sure the software path that consumes the data is hardened too.The release page places CVE-2026-0964 in the security section alongside another issue, reinforcing the point that libssh’s security releases were part of a broader hardening effort. In security terms, this is useful because it means maintainers were not only reacting to one bug in isolation, but also cleaning up adjacent attack surface.
The workaround guidance is blunt for a reason
Libssh’s advisory says, in plain language, “Do not use SCP!” It also says SCP is deprecated and will be removed in future releases. That language is unusually direct for a project advisory, but it reflects a broader industry view: SCP’s design has a long history of edge cases, protocol ambiguity, and filename trust problems that make it a poor choice for modern secure transfer workflows. (libssh.org)The workaround continues with an application-level warning: if SCP must be used, the application must validate that the path returned from
ssh_scp_request_get_filename() is the path it originally requested. That is a crucial clue for developers. The fix is not just to treat remote metadata as tainted; it is to compare it against the expected value and reject anything that drifts. (libssh.org)Why that warning matters
This advice tells us the library authors expect misuse in the wild. In other words, the problem is not only malicious servers but also legitimate clients that failed to constrain their own behavior. That is often how these bugs become exploitable at scale: a protocol quirk becomes an application bug because someone assumed the transport layer would sanitize for them. (libssh.org)- Upgrade to libssh 0.11.4 or 0.12.0.
- Treat SCP path metadata as untrusted input.
- Compare returned filenames against the expected request.
- Remove SCP dependencies where possible.
- Prefer safer transfer mechanisms in new development. (libssh.org)
Compatibility and Ecosystem Implications
The advisory’s warning that SCP is deprecated is more than a housekeeping note. It is a signal that ecosystems depending on SCP need to start planning for migration, because future libssh releases may remove support altogether. That matters for appliance vendors, internal platforms, and embedded tools that still rely on the classic SCP workflow. (libssh.org)In enterprise environments, legacy protocols often survive because they are embedded in scripts written years ago and never revisited. The cost of upgrading can seem invisible until security breaks the illusion. CVE-2026-0964 is a good example of how a small protocol assumption can force a broader modernization conversation across operations, security, and development teams. (libssh.org)
The migration problem
The real challenge is not replacing one command with another. It is unwinding the automation and trust models built around SCP and ensuring that newer mechanisms preserve the exact operational behavior administrators depend on. That is why migration projects often stall: they are not hard because the replacement is unavailable, but because the old process has accumulated dependencies and exceptions. (libssh.org)There is also a compatibility tension between security and convenience. SCP is popular precisely because it is simple to invoke and widely understood. But that simplicity hides an ugly truth: the protocol gives attackers too much opportunity to shape filenames in ways the client may not expect. The safer the replacement, the more likely it is to look slightly less convenient to the person writing the script. (libssh.org)
- Legacy scripts may depend on SCP semantics.
- Appliance vendors may need firmware updates.
- CI/CD pipelines may require transfer logic changes.
- Training and documentation must reflect the new workflow.
- Security teams should inventory SCP usage before removal deadlines. (libssh.org)
Comparison to Prior SCP and SSH Issues
The advisory’s comparison to OpenSSH CVE-2019-6111 is highly significant because it shows that the root issue is not a single vendor’s bug, but a recurrent design problem in SCP-style workflows. The pattern is familiar: a remote server gets to influence file naming, and the client trusts that naming too much. That is enough to create a path traversal condition even when the underlying SSH transport is sound. (libssh.org)Libssh’s broader security history also underscores how often SSH ecosystems inherit old assumptions. The project has published multiple advisories over time, and its security process page shows a recurring emphasis on coordinated release, patching, and CVSS scoring. That tells us the maintainers treat vulnerabilities as a routine part of the support lifecycle, not as isolated anomalies.
What makes this issue different
CVE-2026-0964 is different from memory corruption bugs because it is easier to understand and easier to trigger, but still dependent on deployment context. The attacker does not need to smash memory or race the parser; they need only to shape the path returned by the server and get the client to use it. That can make the bug feel less dramatic than a crash, while arguably making it more practical. (libssh.org)The issue also highlights how “secure by default” claims can fail at the seams. SSH is secure, encryption is secure, authentication may be secure, and yet the data field inside the tunnel can still be used to subvert the application. That is a classic boundary failure, and it is one reason seasoned defenders look beyond transport-layer assurances. (libssh.org)
- SCP filename handling has a documented history of path issues.
- Client-side trust is the weakest link in this class of bug.
- Transport security does not equal application safety.
- Similar bugs recur because legacy protocols are sticky.
- Vendor advisories often point to the same operational fix: stop using SCP. (libssh.org)
Mitigation Guidance for Administrators
The first and most obvious mitigation is to upgrade libssh to a fixed release. That should be the default step for any software stack embedding the affected library, whether it is a standalone client, a packaged admin tool, or a vendor appliance. If the product has not yet shipped a firmware or software update, administrators should assume exposure until proven otherwise. (libssh.org)The second mitigation is to eliminate SCP wherever practical. This is not just a matter of preference; it is a security hardening step backed by the advisory itself. If a team still needs to move files over SSH, it should consider transfer methods that do not rely on server-supplied path semantics in the same brittle way. (libssh.org)
Practical steps for defenders
Security teams should start by inventorying where SCP is used, especially in scripts and scheduled jobs. Many organizations know they use SSH, but few have a complete map of where SCP still lives. That inventory becomes the basis for deciding whether the risk is isolated to a few endpoints or spread across the estate. (libssh.org)Then comes validation. Any application using
ssh_scp_request_get_filename() should compare the returned name against the path it requested, and it should refuse to write outside the expected directory. That may sound obvious, but bugs like this persist because developers assume a remote server will never lie about a filename. (libssh.org)Finally, teams should review privilege levels. A low-privilege process that writes into a private directory is one thing; a privileged service writing into system locations is another. The same bug can have very different outcomes depending on where the transferred file ends up. (libssh.org)
- Patch all libssh-based clients promptly.
- Audit scripts for SCP usage.
- Compare requested and returned filenames.
- Restrict write permissions wherever possible.
- Replace SCP in long-lived automation. (libssh.org)
Strengths and Opportunities
The main strength of the libssh response is that it is clear, direct, and operationally useful. The advisory does not bury the issue in abstractions; it tells administrators exactly what the bug does, what versions are fixed, and why SCP should be reconsidered entirely. That kind of candor is valuable because it turns a vulnerability bulletin into a migration signal. (libssh.org)This situation also creates an opportunity for enterprises to clean up old file-transfer logic. Many organizations have been postponing the SCP-to-something-safer transition for years, and a concrete CVE is often the catalyst they need. Sometimes the best security project is the one that removes an entire class of risk, rather than merely patching around it. (libssh.org)
- The advisory is explicit about the risk and the fix.
- Fixed versions are already available.
- The issue is easy to explain to non-specialists.
- Migration away from SCP improves long-term security.
- The bug offers a clean trigger for auditing automation.
- Application developers can add simple filename validation.
- Security teams can prioritize exposed scripts and services.
Risks and Concerns
The most obvious concern is that many organizations will treat this as a low-priority advisory because the CVSS score is only 5.0. That would be a mistake. Path traversal bugs often look modest on paper but become much more serious when they land in automation, privileged workflows, or systems that ingest files into trusted locations. (libssh.org)Another concern is incomplete remediation. Patching libssh is necessary, but it may not be sufficient if surrounding applications still assume that SCP output is trustworthy. In other words, a fixed library inside an unsafe workflow can still leave users exposed to bad operational decisions. (libssh.org)
The hidden risk surface
The most vulnerable deployments are often the least visible ones: embedded appliances, vendor tools, custom scripts, and scheduled jobs that no one has reviewed in years. Those are precisely the places where SCP tends to linger. They are also the places where changing behavior is slow, because no one wants to touch a script that has been “working fine” for a decade. (libssh.org)A third concern is that the advisory’s deprecation language may be ignored by organizations that only react to immediate break-fix pressure. If SCP remains in use until a vulnerability forces a change, defenders may end up with a long tail of residual risk long after the fix is installed. Security wins are often lost in the operational cleanup phase. (libssh.org)
- Low CVSS scores can lull teams into delay.
- Legacy scripts may remain unreviewed.
- Privileged transfers can amplify the impact.
- Vendor appliances may patch slowly.
- SCP deprecation will create migration churn.
- Application-level validation may still be missing.
- Security ownership may be split across teams, delaying action.
Looking Ahead
The most likely next step is that more vendors embedding libssh will issue their own advisories or firmware updates if they have not already done so. That is typical for library vulnerabilities: the upstream fix is only the first move, and downstream products can lag behind. Enterprises should assume that their real exposure depends on the slowest vendor in the chain. (libssh.org)We should also expect the industry to keep nudging users away from SCP altogether. Libssh’s own advisory practically says as much, and projects rarely talk that bluntly unless they have reached a conclusion about the protocol’s future. The longer SCP survives in automation, the more likely more path-related security defects will keep appearing around it. (libssh.org)
What security teams should watch next
- Vendor patch cadence for libssh-based products.
- Internal inventories of SCP usage in scripts and jobs.
- Whether applications validate returned filenames explicitly.
- Announcements about SCP removal in future libssh releases.
- Migration guidance toward safer SSH-based file transfer approaches. (libssh.org)
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: