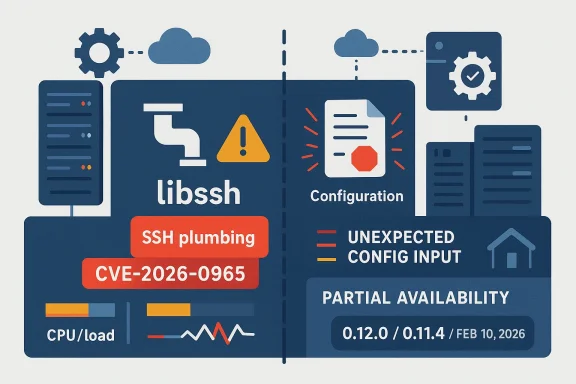
Microsoft’s listing for CVE-2026-0965 highlights a denial-of-service condition in libssh tied to improper configuration file handling, and the upstream libssh project confirms that the issue was among the security fixes shipped in its 0.12.0 and 0.11.4 releases on February 10, 2026. The practical takeaway is that this is not a headline-grabbing remote code execution bug, but it is still a meaningful reliability problem in a library that sits inside real network stacks and enterprise software. In other words, the attack surface is small enough to dismiss at your peril and broad enough to matter in production, especially where SSH-based automation and embedded clients are common.
libssh occupies an important niche in the open-source security ecosystem. It is a C library that implements SSHv2 for both client and server use, and the project has long treated security releases as part of its normal maintenance rhythm rather than as extraordinary events. The upstream security-release process explicitly states that only supported versions are eligible and that advisories are published alongside patches, a sign that the maintainers expect downstream consumers to move quickly once an issue is disclosed.
That matters because SSH libraries are often treated as plumbing. They are embedded in management tools, automation systems, network appliances, backup products, and embedded devices, so a flaw in the parser or configuration layer can ripple outward into many different products. When the weakness is in a network-facing code path, even a “mere” denial of service can become operationally expensive if it affects shared infrastructure or a fleet of devices that rely on the same library build.
The CVE’s phrasing also fits a familiar pattern in protocol and configuration handling bugs: the issue is not necessarily a single catastrophic crash primitive, but a bad assumption about what input should look like. In libssh’s case, the upstream release note groups CVE-2026-0965 with several other defects in the same security batch, suggesting a concentrated hardening effort around parsing and boundary conditions rather than a one-off emergency fix. That is often how mature libraries evolve after enough fuzzing and field exposure reveal the sharp edges.
Microsoft’s Security Update Guide has become more transparent about third-party and partner-assigned CVEs over time, including vulnerabilities in open-source libraries that show up inside Microsoft products or services. Microsoft has also emphasized that the guide can be used to sort, filter, and track security issues across CVE, product, and release dimensions, which makes it the right place to watch when a dependency like libssh is involved.
The upstream release note does not frame the issue as a memory-safety catastrophe; instead, it labels CVE-2026-0965 as a possible denial of service when parsing unexpected configuration files. That points to the configuration parser, file discovery logic, or an error-handling path reacting badly to malformed or unexpected input. Bugs like that often look small in code review and big in production, which is exactly why they keep getting CVEs.
In that sense, CVE-2026-0965 is less a shock and more a reminder. Configuration parsing is one of those places where a project can be technically correct for years and still be one odd file away from a reliability bug. The difference between “works on my machine” and “survives hostile environments” is often one corrupted config, one unexpected path, or one malformed file away.
The attack may also depend on the surrounding deployment. If libssh is only used in a local client or a narrowly scoped service, the operational impact may be limited. But if it is embedded in infrastructure software, orchestration tools, or a fleet of appliances, then even intermittent parser stalls can create a noisy support burden, repeated retries, and “ghost” performance problems that are hard to trace back to the root cause.
That is especially relevant in SSH-adjacent workflows, because these components often underpin automation. If a configuration parser slows down or hiccups at the wrong moment, the downstream effect may not look like a security incident; it may look like a flaky deployment, a backup window overrun, or an unreliable maintenance task. That ambiguity is dangerous because it can delay remediation.
That makes the phrase “improper configuration file handling” more important than it first appears. It hints at input validation, path handling, or parser robustness rather than a simple protocol mistake on the wire. Those bugs are often harder for defenders to recognize because they look like local hygiene issues until they are studied as security problems.
The pattern is familiar across mature C libraries: the code grows feature by feature, platforms expand, and edge cases accumulate. Then a security cycle sweeps in and hardens the pieces that turned out to be more brittle than expected. libssh’s release notes show exactly that evolution, with security items alongside new features such as post-quantum key exchanges and FIDO2/U2F support, which means the project is balancing modernization with maintenance.
In practice, configuration bugs are often exploited indirectly. They may be triggered by a malformed file placed in a location the software scans automatically, by a surprising default, or by a dependency that inherits a file-handling quirk from another layer. Even when the impact is only partial denial of service, the reliability penalty can be enough to justify urgent patching.
The same point applies to Microsoft’s inclusion of the CVE. Microsoft’s Security Update Guide has become a useful aggregation point for vulnerabilities that affect Microsoft products directly or indirectly, and Microsoft has emphasized that its guide now supports machine-readable formats and broader CVE transparency. That means third-party library issues can surface quickly when they matter to Microsoft customers, even if Microsoft is not the upstream author.
That is especially plausible in libraries that support automatic configuration loading. Microsoft’s and libssh’s ecosystem context both matter here: if a dependency silently processes user or system configuration in the background, then an attacker who can influence that input may be able to force the library into a bad loop without needing privileged access to the network path itself. That is the sort of issue that tends to be environment-specific but still widespread.
That is why denial-of-service issues in file-handling code should not be treated as low-value findings. In a networked environment, repeated faults can be amplified by watchdogs, orchestration, or service restarts, turning a limited bug into a persistent operational nuisance. Even if the attacker cannot completely deny service, they may still create enough friction to matter.
The safest interpretation is therefore conservative: if you rely on libssh and your package line includes a version older than the February 2026 security release, assume you need to check the specific vendor build. Version numbers alone are not enough when backports and distro patches are in play.
The more integrated the library, the more expensive the bug becomes. A shared platform service that uses libssh can amplify a minor parsing issue into repeated support tickets, and if several products share the same dependency, patch coordination becomes part of the incident response process. That is why enterprise security teams should think in terms of dependency blast radius, not just package names.
That makes patching this class of issue a governance problem as much as a technical one. Teams need inventory, ownership, and change windows aligned so that a dependency update does not get buried under more glamorous security priorities. The boring bugs are often the ones that clog the most workstreams.
In those cases, the immediate question is not whether the attacker can achieve full denial of service. It is whether the bug can make the system inconsistent enough to delay recovery, complicate logins, or force manual intervention. Those are real business impacts, and they justify prioritization even when the CVE text sounds restrained.
The edge-device story is similar. When libssh is included in routers, storage appliances, industrial equipment, or network appliances, a reliability bug can become a field support problem long before it becomes a textbook security event. Users may see connection failures, slower administration, or intermittent unavailability, while vendors struggle to reproduce the exact trigger.
This is also where attack visibility gets tricky. A partial denial-of-service event may look like a transient bug or a bad network, not a security issue. That makes incident classification harder and increases the chance that the vulnerable build stays in circulation longer than it should. Visibility is often the real casualty.
That is why defenders should resist the temptation to treat parser bugs as “only local.” In modern systems, local file state is often generated by remote orchestration, synchronization, or automation, which means even a file-handling weakness can end up being operationally remote in effect if not in direct trigger path.
That is particularly relevant in open-source infrastructure libraries, where the blast radius is multiplied by reuse. A single parser bug in libssh can affect multiple products, and multiple products may ship their fixes on different schedules. That staggered remediation pattern is one reason these bugs stay important long after the first upstream patch lands.
The practical lesson is simple: keep a close eye on dependencies that are usually invisible until they fail. By the time a parser bug makes itself known, it may already have affected more systems than the original ticket implies. That is why fast patch uptake matters so much in infrastructure software.
That is not the same as saying Microsoft is the only source you need. Upstream release notes remain crucial, particularly for details like fixed versions, because vendor advisories may lag or abstract the technical nuance. But when both sources point in the same direction, the signal is usually strong enough to act on quickly.
It is also worth watching whether Microsoft or other vendors expand their own advisories with more precise product mappings. Microsoft has been steadily improving the Security Update Guide and machine-readable formats for vulnerability data, which should help defenders connect a third-party CVE like this to the products they actually run. That trend is good for triage, but only if organizations are ready to consume the data intelligently.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
libssh occupies an important niche in the open-source security ecosystem. It is a C library that implements SSHv2 for both client and server use, and the project has long treated security releases as part of its normal maintenance rhythm rather than as extraordinary events. The upstream security-release process explicitly states that only supported versions are eligible and that advisories are published alongside patches, a sign that the maintainers expect downstream consumers to move quickly once an issue is disclosed.That matters because SSH libraries are often treated as plumbing. They are embedded in management tools, automation systems, network appliances, backup products, and embedded devices, so a flaw in the parser or configuration layer can ripple outward into many different products. When the weakness is in a network-facing code path, even a “mere” denial of service can become operationally expensive if it affects shared infrastructure or a fleet of devices that rely on the same library build.
The CVE’s phrasing also fits a familiar pattern in protocol and configuration handling bugs: the issue is not necessarily a single catastrophic crash primitive, but a bad assumption about what input should look like. In libssh’s case, the upstream release note groups CVE-2026-0965 with several other defects in the same security batch, suggesting a concentrated hardening effort around parsing and boundary conditions rather than a one-off emergency fix. That is often how mature libraries evolve after enough fuzzing and field exposure reveal the sharp edges.
Microsoft’s Security Update Guide has become more transparent about third-party and partner-assigned CVEs over time, including vulnerabilities in open-source libraries that show up inside Microsoft products or services. Microsoft has also emphasized that the guide can be used to sort, filter, and track security issues across CVE, product, and release dimensions, which makes it the right place to watch when a dependency like libssh is involved.
Why this CVE matters even without a dramatic exploit claim
The description supplied by Microsoft is measured: performance may be reduced, resources may become intermittently unavailable, and the attacker cannot fully deny service to legitimate users. That sounds modest, but the wording is actually important. It implies a flaw that may not flatten a service in one clean strike, yet can still produce enough degradation, interruption, or instability to matter in real deployments.The upstream release note does not frame the issue as a memory-safety catastrophe; instead, it labels CVE-2026-0965 as a possible denial of service when parsing unexpected configuration files. That points to the configuration parser, file discovery logic, or an error-handling path reacting badly to malformed or unexpected input. Bugs like that often look small in code review and big in production, which is exactly why they keep getting CVEs.
The broader libssh security backdrop
libssh has seen repeated security releases over the years, including prior denial-of-service and parsing issues. That history does not mean the project is unusually insecure; it means it is doing what mature infrastructure libraries do when they sit near adversarial input and get used across a wide range of environments. A protocol library that lives in client software, servers, and embedded products will inevitably spend part of its life defending against malformed inputs, bad assumptions, and edge cases.In that sense, CVE-2026-0965 is less a shock and more a reminder. Configuration parsing is one of those places where a project can be technically correct for years and still be one odd file away from a reliability bug. The difference between “works on my machine” and “survives hostile environments” is often one corrupted config, one unexpected path, or one malformed file away.
What Microsoft’s description really implies
Microsoft’s wording suggests a partial denial-of-service model rather than a full stop. That distinction matters because it frames the vulnerability as one that can reduce capacity, stall workflows, or intermittently interrupt operations without necessarily taking down every affected instance at once. For enterprise defenders, that is still a real security and availability issue, even if it lacks the drama of a total outage.The attack may also depend on the surrounding deployment. If libssh is only used in a local client or a narrowly scoped service, the operational impact may be limited. But if it is embedded in infrastructure software, orchestration tools, or a fleet of appliances, then even intermittent parser stalls can create a noisy support burden, repeated retries, and “ghost” performance problems that are hard to trace back to the root cause.
Partial availability is still a security problem
A lot of teams mentally bucket vulnerabilities into binary categories: either the service is down or it is fine. Real systems are messier than that. A parser that sporadically fails, consumes extra CPU, or delays critical sessions can still trigger timeouts, failovers, queue buildup, and operator intervention, which is precisely why Microsoft’s description emphasizes reduced performance and interruptions in resource availability.That is especially relevant in SSH-adjacent workflows, because these components often underpin automation. If a configuration parser slows down or hiccups at the wrong moment, the downstream effect may not look like a security incident; it may look like a flaky deployment, a backup window overrun, or an unreliable maintenance task. That ambiguity is dangerous because it can delay remediation.
Why configuration file handling is a high-value target
Configuration code is deceptively sensitive. It often runs early, touches the filesystem, and makes assumptions about trusted local state. If a library accepts unexpected configuration files or interprets them in a surprising way, attackers may be able to force slow-path behavior, trigger exception-heavy code paths, or repeatedly exercise a bug that never fully resolves into a clean crash.That makes the phrase “improper configuration file handling” more important than it first appears. It hints at input validation, path handling, or parser robustness rather than a simple protocol mistake on the wire. Those bugs are often harder for defenders to recognize because they look like local hygiene issues until they are studied as security problems.
- The issue is availability-focused, not confidentiality-focused.
- The likely trigger is unexpected configuration input.
- The effect can be intermittent degradation rather than a total outage.
- The operational pain may show up as latency, retries, or service instability.
- The real blast radius depends on where libssh is embedded.
Historical context: why libssh keeps showing up in security advisories
libssh’s security-release page shows a project that actively tracks and backports fixes into supported branches. In February 2026, the maintainers released 0.12.0 and 0.11.4 with multiple security fixes at once, including CVE-2026-0965. That is a sign of healthy disclosure hygiene, but it also underscores how many separate parsing and logic surfaces a library like this exposes.The pattern is familiar across mature C libraries: the code grows feature by feature, platforms expand, and edge cases accumulate. Then a security cycle sweeps in and hardens the pieces that turned out to be more brittle than expected. libssh’s release notes show exactly that evolution, with security items alongside new features such as post-quantum key exchanges and FIDO2/U2F support, which means the project is balancing modernization with maintenance.
What makes this different from older libssh issues
Some libssh issues have been about authentication logic, packet parsing, or data handling on the wire. CVE-2026-0965 is notable because it points to the configuration path, which tends to get less attention than obvious network parsing. That makes it a useful reminder that attack surfaces are not limited to socket input; they also include the files software reads in the normal course of startup or operation.In practice, configuration bugs are often exploited indirectly. They may be triggered by a malformed file placed in a location the software scans automatically, by a surprising default, or by a dependency that inherits a file-handling quirk from another layer. Even when the impact is only partial denial of service, the reliability penalty can be enough to justify urgent patching.
Upstream release cadence matters
Upstream project cadence is one of the best clues defenders have. The fact that libssh bundled this issue into a security release with multiple other fixes tells operators two things: the issue was serious enough to land in a coordinated patch, and the maintainers considered the stable branch important enough to receive backports. That is the kind of signal enterprise teams should watch for when deciding patch priority.The same point applies to Microsoft’s inclusion of the CVE. Microsoft’s Security Update Guide has become a useful aggregation point for vulnerabilities that affect Microsoft products directly or indirectly, and Microsoft has emphasized that its guide now supports machine-readable formats and broader CVE transparency. That means third-party library issues can surface quickly when they matter to Microsoft customers, even if Microsoft is not the upstream author.
- Upstream security releases help establish fix availability.
- Microsoft inclusion helps establish ecosystem relevance.
- Multiple fixes in one release often indicate active hardening.
- Configuration-handling bugs are frequently underestimated at first glance.
- The combination of two vendor signals raises the patching priority.
Technical significance of “unexpected configuration files”
The phrase unexpected configuration files is doing a lot of work here. It suggests the parser may encounter files it did not anticipate, perhaps because of location, format, contents, or timing. Any of those can become a denial-of-service vector if the library spends too much time recovering, repeatedly errors out, or enters a degraded state when the file is not what it expected.That is especially plausible in libraries that support automatic configuration loading. Microsoft’s and libssh’s ecosystem context both matter here: if a dependency silently processes user or system configuration in the background, then an attacker who can influence that input may be able to force the library into a bad loop without needing privileged access to the network path itself. That is the sort of issue that tends to be environment-specific but still widespread.
Parser robustness is a security feature
A robust parser does not merely accept valid files; it rejects invalid ones cleanly and cheaply. If failure handling becomes expensive, the attacker does not need a memory corruption primitive to cause trouble. They only need a way to feed the parser enough edge cases to create sustained overhead or recurring interruptions.That is why denial-of-service issues in file-handling code should not be treated as low-value findings. In a networked environment, repeated faults can be amplified by watchdogs, orchestration, or service restarts, turning a limited bug into a persistent operational nuisance. Even if the attacker cannot completely deny service, they may still create enough friction to matter.
Why the issue may vary by platform
Library behavior around configuration files can differ across operating systems, packaging styles, and downstream integration. A bug that is easy to trigger in one Linux distribution’s package layout may be hard to reproduce in a minimal embedded image or a Windows deployment with different file conventions. That variability makes this kind of flaw particularly annoying for defenders because affected status may depend on build options and packaging details, not just the library version number.The safest interpretation is therefore conservative: if you rely on libssh and your package line includes a version older than the February 2026 security release, assume you need to check the specific vendor build. Version numbers alone are not enough when backports and distro patches are in play.
- Configuration files are often implicitly trusted.
- Unexpected file formats can trigger expensive error paths.
- Automatic file loading expands the attack surface.
- Packaging differences can change real-world exposure.
- Downstream backports may make simple version checks misleading.
Enterprise impact: where the pain is likely to show up
For enterprise teams, the biggest concern is not a single crashed daemon; it is the way a partial denial-of-service can interfere with fleet-wide workflows. SSH libraries are used in remote administration, automated deployment, inventory tools, backup systems, and appliance management interfaces. If one of those paths becomes flaky, the result can be delayed change windows, retry storms, or a chain of small failures that eats operational time.The more integrated the library, the more expensive the bug becomes. A shared platform service that uses libssh can amplify a minor parsing issue into repeated support tickets, and if several products share the same dependency, patch coordination becomes part of the incident response process. That is why enterprise security teams should think in terms of dependency blast radius, not just package names.
Identity and automation depend on stable SSH behavior
SSH is often treated as the quiet backbone of operational trust. When it misbehaves, the impact is not just that one connection fails; it is that scripts, schedulers, and operators can no longer rely on the transport behaving consistently. In those environments, a vulnerability that produces intermittent resource interruption can undermine confidence across the whole automation chain.That makes patching this class of issue a governance problem as much as a technical one. Teams need inventory, ownership, and change windows aligned so that a dependency update does not get buried under more glamorous security priorities. The boring bugs are often the ones that clog the most workstreams.
Appliances and embedded systems are especially exposed
Embedded vendors often move slowly on library upgrades, and SSH libraries frequently live in maintenance interfaces, remote access tools, or update mechanisms. If the vulnerable code path is part of a device management plane, then even a partial service degradation can interfere with support, remediation, or recovery. That is a nasty combination in environments that already depend on tight operational windows.In those cases, the immediate question is not whether the attacker can achieve full denial of service. It is whether the bug can make the system inconsistent enough to delay recovery, complicate logins, or force manual intervention. Those are real business impacts, and they justify prioritization even when the CVE text sounds restrained.
- Shared libraries create many-to-one risk.
- Automation failures can be more costly than visible outages.
- Embedded systems often patch more slowly.
- Device management planes can magnify the impact.
- Partial degradation can still interrupt business operations.
Consumer and edge-device impact
Consumers are less likely to notice libssh by name, but they absolutely feel the effects of the software that embeds it. A desktop app that fails to connect reliably, a backup tool that stalls, or a network utility that hesitates on malformed configuration input can all translate into bad user experience without exposing the underlying dependency. That is part of the reason dependency CVEs deserve attention beyond the enterprise world.The edge-device story is similar. When libssh is included in routers, storage appliances, industrial equipment, or network appliances, a reliability bug can become a field support problem long before it becomes a textbook security event. Users may see connection failures, slower administration, or intermittent unavailability, while vendors struggle to reproduce the exact trigger.
Why “not a full DoS” still matters to users
A lot of consumer-facing security communications focus on whether an attacker can fully take over a device or service. But for the user, a repeated failure to connect or a slowdown in a critical utility can feel almost as bad. If the affected code is in a tool used for updates, remote access, or maintenance, reliability loss can have knock-on effects that are hard to see from the outside.This is also where attack visibility gets tricky. A partial denial-of-service event may look like a transient bug or a bad network, not a security issue. That makes incident classification harder and increases the chance that the vulnerable build stays in circulation longer than it should. Visibility is often the real casualty.
Why the path to exploitation may be narrow but still relevant
Not every CVE needs to be easy to exploit to matter. If a bug can be triggered by an unusual but reachable configuration file state, that may be enough in environments where the attacker can influence packaging, deployment, or local inputs. The result can be a narrow but valuable target, especially when the same library exists in many products with slightly different behavior.That is why defenders should resist the temptation to treat parser bugs as “only local.” In modern systems, local file state is often generated by remote orchestration, synchronization, or automation, which means even a file-handling weakness can end up being operationally remote in effect if not in direct trigger path.
- Consumer impact may appear as flaky connectivity.
- Edge devices may show intermittent management failures.
- Update and backup utilities are especially sensitive.
- Support teams may misdiagnose the issue as networking noise.
- Long-lived devices often remain exposed longer than servers.
How this compares with other modern library CVEs
CVE-2026-0965 is part of a broader trend: modern security disclosures are increasingly about reliability, validation, and resource exhaustion rather than only classic memory corruption. Microsoft’s own Security Update Guide has highlighted that not every vulnerability is a catastrophic code-execution flaw; many are about the operational consequences of a weakness in a shared component.That is particularly relevant in open-source infrastructure libraries, where the blast radius is multiplied by reuse. A single parser bug in libssh can affect multiple products, and multiple products may ship their fixes on different schedules. That staggered remediation pattern is one reason these bugs stay important long after the first upstream patch lands.
The ecosystem lesson
Security teams should read this CVE as a reminder that the narrowness of a bug description does not equal narrowness of impact. A denial-of-service rooted in configuration handling can be operationally serious if it lands in the wrong place, even if the attacker never gets a dramatic primitive like code execution or data theft. That is especially true for libraries that are foundational to administration and orchestration.The practical lesson is simple: keep a close eye on dependencies that are usually invisible until they fail. By the time a parser bug makes itself known, it may already have affected more systems than the original ticket implies. That is why fast patch uptake matters so much in infrastructure software.
Why Microsoft’s inclusion should not be ignored
When Microsoft lists an open-source dependency CVE, it is often because that dependency has relevance somewhere in Microsoft’s product ecosystem or in the broader customer base. Microsoft has also been explicit about improving the transparency and machine-readability of CVE data, which makes its guide a useful signal rather than just a passive catalog. For defenders, that means the appearance of a library issue in the guide should be treated as a strong prioritization cue.That is not the same as saying Microsoft is the only source you need. Upstream release notes remain crucial, particularly for details like fixed versions, because vendor advisories may lag or abstract the technical nuance. But when both sources point in the same direction, the signal is usually strong enough to act on quickly.
- Library CVEs often have ecosystem-wide reach.
- Vendor listings can reveal downstream relevance.
- Upstream notes give the most precise fix data.
- Staggered patching increases residual exposure.
- Reliability bugs can be just as operationally disruptive as classic exploits.
Strengths and Opportunities
The good news is that CVE-2026-0965 appears to be the kind of bug that can usually be addressed with a targeted update rather than a major architectural rewrite. libssh’s upstream maintainers already shipped fixes in the February 2026 security releases, and Microsoft’s classification makes it clear that the issue is worth attention even though it is not a catastrophic compromise scenario. That combination gives defenders a relatively clean remediation path if they can identify their exposure quickly.- The fix appears to be part of an already published security release.
- The issue is framed as availability-related, which often simplifies communication with stakeholders.
- The upstream project has an established security-release process.
- Microsoft’s listing improves visibility for downstream consumers.
- Teams can treat this as a dependency hygiene exercise, not a major product redesign.
- The bug is a good candidate for inventory-driven remediation across fleets.
- It offers an opportunity to review other file-handling paths for similar weaknesses.
Risks and Concerns
The biggest risk is underestimation. Because the issue is not described as a full denial-of-service or a remote code execution flaw, some teams may relegate it to a low-priority maintenance bucket. That would be a mistake if the affected build sits in a management path, embedded product, or automation workflow where intermittent failure can create outsized operational pain.- Partial availability loss can still disrupt critical workflows.
- Configuration-file bugs are easy to misclassify as ordinary stability issues.
- Downstream backports may obscure whether a build is actually fixed.
- Embedded devices may remain vulnerable for a long time.
- Retry loops and watchdogs can amplify the resource cost.
- Support teams may struggle to reproduce the trigger.
- Patch deferral can leave a small bug in place long enough to matter.
Looking Ahead
The next thing to watch is downstream uptake. Upstream fixed the issue in libssh’s February 2026 security releases, but real-world exposure will depend on how quickly distributions, appliance vendors, and software integrators absorb those changes. In practice, the long tail of a dependency CVE is often measured not in days but in vendor release cycles.It is also worth watching whether Microsoft or other vendors expand their own advisories with more precise product mappings. Microsoft has been steadily improving the Security Update Guide and machine-readable formats for vulnerability data, which should help defenders connect a third-party CVE like this to the products they actually run. That trend is good for triage, but only if organizations are ready to consume the data intelligently.
What to watch next
- Vendor advisories confirming fixed package versions.
- Backports into long-term support and appliance branches.
- Any clarification on the exact configuration-file trigger.
- Reports of downstream products carrying the vulnerable libssh build.
- Whether additional libssh configuration-related issues surface in the same maintenance cycle.
Source: MSRC Security Update Guide - Microsoft Security Response Center