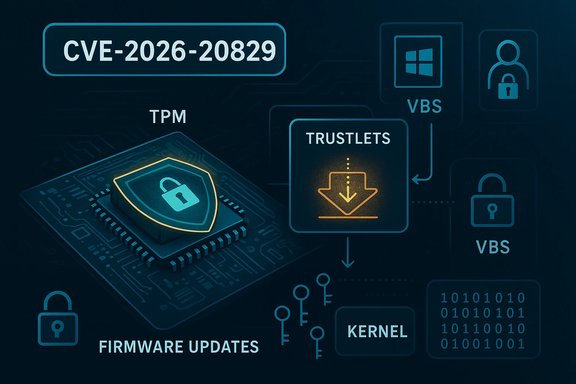
A terse entry in Microsoft’s Security Update Guide has drawn renewed attention to the fragile boundary between the Trusted Platform Module (TPM) ecosystem and the isolated “trustlet” processes that help Windows implement Virtualization‑Based Security. The item—tracked as CVE‑2026‑20829—was surfaced with an explanatory paragraph about the vendor’s confidence metric (how certain the vulnerability is and how credible the technical details are). That metric matters: it tells defenders whether they’re reacting to rumour, preliminary researcher conjecture, or a confirmed, vendor‑acknowledged flaw with firm technical guidance. The advisory’s summary points to an information disclosure pathway affecting a TPM trustlet, and while Microsoft’s page is intentionally brief, the broader TPM literature and contemporaneous vendor advisories allow a concrete, evidence‑backed assessment of what this class of bug means for Windows environments and virtualized workloads.
TPM (Trusted Platform Module) is the hardware or firmware component that provides a hardware root of trust for keys, measurements and attestation. On modern Windows systems TPMs anchor features like BitLocker, Secure Boot attestation and Virtualization‑Based Security (VBS). The TPM can be a discrete chip, firmware on the CPU (fTPM), or a virtualized instance (vTPM) supplied by the hypervisor. Windows implements several layers of isolation to protect secrets: Virtualization‑Based Security (VBS) creates an isolated execution environment (VTL1) for small, signed processes called trustlets (also called IUM processes). Trustlets run with strong isolation from the main OS kernel, and some trustlets host high‑value services—one notable example is the virtual TPM service which mediates TPM requests for virtual machines. Compromising a trustlet or causing it to leak memory undermines the very protections VBS and TPM are supposed to provide. The practical implication is straightforward: information disclosure from a trustlet is rarely a benign bug. Even small leaks—uninitialized buffers, out‑of‑bounds reads, or permissive fallback behaviors—can reveal kernel pointers, ephemeral keys, or measurement values that let attackers defeat mitigations such as KASLR or automate local privilege escalation. In virtualization contexts, the stakes rise: tenant code inside a VM can sometimes interact with vTPM endpoints; a local leak there becomes a multi‑tenant threat.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background: TPM, trustlets, and why small leaks matter
Background: TPM, trustlets, and why small leaks matter
TPM (Trusted Platform Module) is the hardware or firmware component that provides a hardware root of trust for keys, measurements and attestation. On modern Windows systems TPMs anchor features like BitLocker, Secure Boot attestation and Virtualization‑Based Security (VBS). The TPM can be a discrete chip, firmware on the CPU (fTPM), or a virtualized instance (vTPM) supplied by the hypervisor. Windows implements several layers of isolation to protect secrets: Virtualization‑Based Security (VBS) creates an isolated execution environment (VTL1) for small, signed processes called trustlets (also called IUM processes). Trustlets run with strong isolation from the main OS kernel, and some trustlets host high‑value services—one notable example is the virtual TPM service which mediates TPM requests for virtual machines. Compromising a trustlet or causing it to leak memory undermines the very protections VBS and TPM are supposed to provide. The practical implication is straightforward: information disclosure from a trustlet is rarely a benign bug. Even small leaks—uninitialized buffers, out‑of‑bounds reads, or permissive fallback behaviors—can reveal kernel pointers, ephemeral keys, or measurement values that let attackers defeat mitigations such as KASLR or automate local privilege escalation. In virtualization contexts, the stakes rise: tenant code inside a VM can sometimes interact with vTPM endpoints; a local leak there becomes a multi‑tenant threat.What Microsoft’s “confidence” metric means (and why it matters)
Microsoft’s Update Guide includes an explicit metric that rates the degree of confidence in the existence and technical quality of a reported vulnerability. That scale separates:- cases where only the existence of a vulnerability is suspected (low confidence),
- cases where independent research points to likely root causes but lacks full proof (medium confidence),
- and cases where the vendor or author confirms both existence and technical details (high confidence).
- Low confidence: Treat as investigate, not emergency. Monitor vendor updates and do targeted inventory to see whether the component exists in deployed images.
- Medium confidence: Raise to prepare: prioritize inventory and mitigations, and accelerate patch testing if vendor fixes arrive.
- High confidence: Move to immediate remediation: deploy vendor patches, rotate keys if advised, and hunt for exploitation activity.
Technical anatomy: the typical failure modes behind TPM/trustlet leaks
While CVE numbers and vendor summaries vary, multiple independent advisories published over 2024–2025 reveal recurring technical root causes that apply directly to trustlet/TPM information‑disclosure findings:- Uninitialized resources: Code returns or transmits structure fields that were never zeroed. These may contain stale pointers or leftover stack/heap data—classic reconnaissance primitives for follow‑on exploits. This is the class Microsoft calls “use of uninitialized resource.”
- Bounds‑checking failures / out‑of‑bounds reads: Functions that process TPM command payloads or helper routines (for example, CryptHmacSign in the TCG reference code) sometimes fail to pair signature schemes and keys correctly, enabling a crafted command to read memory past intended buffers. TCG and vendor advisories show this class enables leakage of up to tens of kilobytes in some reference implementations.
- Permissive fallback logic: In some firmware or microservice code, an error path intended to preserve compatibility accidentally invokes a less‑secure routine rather than failing safe—this can convert a verification failure into a data leak or a bypass. Historical firmware bugs of this type (in UEFI/EDK2) illustrate the danger when logic, not memory safety, is at fault.
- TEE / fTPM attack surface: Firmware TPMs (fTPMs) often run inside a CPU’s Trusted Execution Environment (TEE). Compromises against the TEE or incorrect parameter validation between TEE trustlets can fully expose TPM internal state. Academic work and vendor incident responses have shown these paths result in worst‑case outcomes—full key extraction—if exploited with physical or privileged access.
How the current CVE fits the pattern (what is known and what is not)
The MSRC entry for CVE‑2026‑20829 lists the issue as a TPM trustlet information disclosure and includes the explanatory language about the confidence metric that the user quoted. Microsoft’s entry is deliberately concise and does not release full exploit mechanics in the public text. That is consistent with prior MSRC behavior for sensitive, local‑vector defects where disclosure could enable immediate weaponization. Administrators should therefore treat Microsoft’s advisory as authoritative for remediation mapping while relying on cross‑vendor advisories for technical context. Independent sources show exactly how similar TPM issues have behaved in the wild:- TCG’s advisory family (VRT0009) disclosed an out‑of‑bounds read in the TPM 2.0 reference code (CryptHmacSign), which vendors mapped to real‑world fTPM and vTPM implementations. That advisory documented that a crafted request could cause a memory read that the TPM would send back—enabling information disclosure and potentially DoS of the TPM. Several vendors (AMD, Intel, Infineon) issued firmware/BIOS updates after TCG’s notice.
- Open‑source projects (libtpms, swtpm) and distributor advisories demonstrate that virtual TPMs built on the affected reference code will also respond to malformed commands, sometimes aborting or exposing memory. That means virtualization stacks and cloud providers must treat these bugs as relevant even when the physical TPM chip is not the culprit.
Cross‑verification: independent corroboration and consensus
To avoid undue alarm, key claims should be cross‑checked against at least two independent authorities:- The Trusted Computing Group (TCG) advisory series (VRT0009) documents the class of TPM reference‑implementation issues and is the canonical technical anchor for many downstream vendor advisories. Vendor bulletins quoting VRT0009 provide the first independent cross‑check.
- Vendor advisories from major silicon vendors (AMD, Intel) confirm that a reference‑implementation defect affects firmware TPMs and can cause either data leakage or TPM availability failures; these advisories include mappings to specific firmware updates and provide the recommended remediation route (apply firmware/BIOS updates via OEM channels).
- Open‑source project advisories (libtpms, swtpm) and security trackers show how the bug class appears in virtual TPM stacks and in QEMU/OVMF contexts—an independent confirmation that the attack surface is larger than discrete chips alone.
Practical risk matrix for Windows admins and security teams
- Attack vector: Local (authenticated) or local within a VM context (tenant code). Not typically remotely exploitable without pre‑existing access.
- Preconditions: Ability to issue TPM commands (in a VM, that may be achieved by a process inside the guest that can reach the vTPM device); in host contexts, the attacker must be able to interact with DRTM/vTPM APIs.
- Immediate impact: Confidentiality loss (leaked memory, potential exposure of keys or platform measurements); availability impact (TPM or vTPM service DoS).
- Likelihood of follow‑on escalation: High if leaked data contains kernel pointers or attestation materials. Even a small leak is a potent reconnaissance primitive that accelerates local privilege escalation exploitation.
- Operational urgency: Elevated for hosts used as virtualization platforms, shielded VM hosts, Azure/Hyper‑V clusters, and administrative workstations that handle attestation or encryption keys.
Recommended remediation and incident steps (operational checklist)
- Identify affected assets:
- Inventory systems that provide or consume vTPM (Hyper‑V hosts, Azure Stack, virtualization hosts). Use patch management and firmware inventory tools to map vendor updates to deployed SKUs.
- Apply vendor fixes:
- Install Microsoft’s security updates mapped to CVE‑2026‑20829 as published in the Update Guide and use the Microsoft Update Catalog or OEM firmware channels for BIOS/firmware updates where vendor advisories indicate fTPM/TPM firmware is affected.
- Short‑term mitigations if immediate patching is not possible:
- Restrict access to management interfaces that can issue TPM/DRTM commands.
- For multi‑tenant hosts, tighten tenant isolation and restrict untrusted code from directly interacting with vTPM interfaces.
- Monitor and hunt:
- Increase telemetry for calls to TPM APIs and DRTM/attestation endpoints. Search logs for unusual TPM command sequences and repeated malformed requests. Centralize event logs from Hyper‑V and host management subsystems.
- Rotate and validate:
- If there is evidence of prior anomalous access, rotate keys and re‑issue attestation material where feasible. Validate measured boot values and attestation flows post‑patch.
- Test and validate updates:
- Apply patches in a staging environment first—firmware changes to TPM implementations can impact boot and attestation behavior; validate BitLocker and shielded VM workflows before rolling to production.
Critical analysis: vendor response, disclosure tradeoffs, and residual risk
Strengths:- The coordinated response model—TCG advisories feeding vendor bulletins, plus Microsoft’s Update Guide mapping—shows the ecosystem functioning: standard body → silicon vendors → OS vendor. This coordination reduces the chance of unpatched vendor islands and helps operators get prioritized fixes.
- Microsoft’s confidence metric and conservative public advisory style limit the immediate disclosure of exploit recipes while still signalling operators to act. That measured approach reduces short‑term weaponization risk in widely distributed ecosystems where PoCs can be abused quickly.
- Inventory blind spots remain a perennial problem. Microsoft can attest to a subset of artifacts (e.g., Azure images), but absence of an attestation for other Microsoft artifacts is not proof of absence; organizations must actively inventory both physical firmware and virtual stacks (WSL, Marketplace images, custom appliances). The MSRC wording and machine‑readable VEX outputs help but do not eliminate the work.
- Virtualization stacks multiply attack surface. Virtual TPM implementations built on shared reference code mean a single reference bug (TCG code) can appear across many vendors—hypervisor vendors, cloud images and OEM firmware—multiplying remediation effort.
- Disclosure tradeoffs. Vendors balancing public disclosure against enabling defenders versus enabling attackers is not a technical issue but an operational one: terse advisories protect customers in the short term but increase operational friction for defenders who need IOCs and indicators to hunt. The confidence metric softens this by indicating how much the short advisory should be trusted; still, defenders often need more telemetry and patch mapping than a short entry supplies.
Final takeaways and practical guidance
- Treat CVE‑2026‑20829 as a high‑value local information disclosure that demands product‑level inventory and timely patching. Microsoft’s confidence metric is a useful signal: use it to prioritize remediation windows without over‑reacting to unverified claims.
- Apply vendor firmware/BIOS updates and Microsoft security updates as they are released; for virtual environments, patch both the host hypervisor and any virtual TPM implementation (swtpm, libtpms, or vendor vTPM) used by guest images.
- Harden and monitor access to TPM and DRTM APIs, especially in multi‑tenant or cloud hosting environments. Increase telemetry for TPM command sequences and hunt for malformed or repeated requests that could indicate exploitation attempts.
- Maintain an aggressive inventory program: confirm which Microsoft and third‑party artifacts include vulnerable code, and map each CVE to the exact KB or firmware version before rolling updates. Absence of public detail does not mean absence of risk—assume unknown until verified.
Source: MSRC Security Update Guide - Microsoft Security Response Center