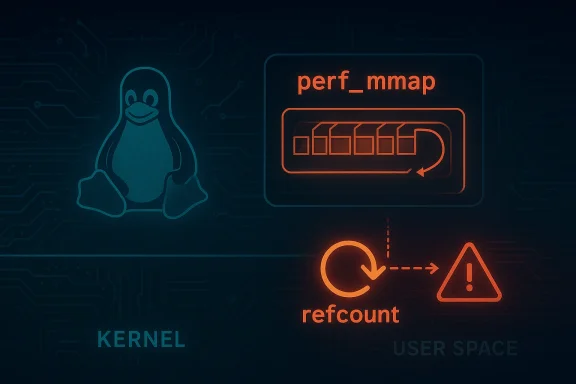
The Linux kernel’s perf subsystem has a new security-flavored bug fix on the table: CVE-2026-23248, described as a refcount bug and potential use-after-free in perf_mmap. The Microsoft Security Response Center entry currently returns a not-found page, but the title itself is enough to tell a familiar and important story: a bug in perf’s mmap path can create memory-safety risk in one of the kernel’s most performance-sensitive interfaces. In kernel terms, that is never just a bookkeeping issue. It is the kind of defect that can ripple from a niche profiling feature into a broader discussion about hardening, exploitability, and downstream patch uptake.
The perf subsystem is Linux’s built-in performance analysis framework, and its ring-buffer design is central to how it moves sampled data from kernel to user space. The user-space view is anchored by a shared control page,
That matters because a refcount bug in a structure like
Linux’s own CVE process also explains why issues like this are often treated conservatively. The kernel team notes that the CVE assignment process is deliberately cautious and that many bug fixes can receive CVEs even when exploitability is not immediately obvious. In other words, the mere fact that a bug fix exists in a security-sensitive subsystem can be enough to justify a CVE, even before the full exploitation story is nailed down. That is especially true for core kernel paths such as memory mapping, where lifetime mistakes can be subtle and architecture-dependent.
Microsoft’s update-guide page for this CVE is currently unavailable, but that does not make the issue less significant. If anything, the lack of a public advisory heightens the need to interpret the title carefully and in context. The bug is apparently in a core perf mmap path, which means it sits close to a kernel-user boundary that receives heavy scrutiny from attackers and defenders alike. Even when the immediate impact appears limited to a profiling feature, kernel memory bugs often have a way of becoming system-wide concerns once researchers start probing adjacent call chains.
The Linux perf documentation describes the mapping model as a control page followed by the ring buffer, with access patterns that depend on whether the mapping is writable or read-only. That means the kernel must manage not just event delivery but also page faults, mapping operations, and teardown in a way that is consistent across multiple modes of use. If a reference is dropped too early, a page fault or later cleanup step may dereference an object that has already been freed.
This kind of bug tends to sit in a gray area between reliability and security. A refcount bug might appear initially as a rare crash, but once a freed object can be reallocated with attacker-controlled data, the issue becomes more serious. In a kernel setting, that can turn into arbitrary code execution, privilege escalation, or at minimum denial of service. The exact impact depends on the surrounding hardening features and the reachable control flow, but potential UAF is a phrase no kernel maintainer likes to see.
There is also a reason such issues often attract distribution and vendor attention beyond the original subsystem. Kernel bugs in shared infrastructure can affect container hosts, developer workstations, CI runners, monitoring nodes, and even desktop systems where perf is used for troubleshooting. That broad reach means a bug that begins as a perf housekeeping issue can matter to both enterprise and consumer Linux deployments. The risk is not universal in every environment, but the blast radius is wider than the feature name implies.
From a kernel-design perspective, that contract is delicate. The kernel must allocate, populate, fault in, and eventually tear down mapped pages while also respecting per-thread, per-CPU, and system-wide modes. It has to do so under races from scheduling, page faults, and concurrent reads. If the object lifetime is not managed by the refcount precisely, the mapping can outlast the object or the object can disappear while still in use. That is exactly the kind of bug that turns a cleanup path into an attack surface.
In perf-related code, that fragility is amplified by the interaction with memory mappings. A userspace mapping can stay alive independently of the original file descriptor, and the kernel needs to know whether the object can still be touched after the caller thinks it is done. If the refcount says “free me now” while a mapping still exists, the next access can hit freed memory. That is the essence of a use-after-free.
Enterprise environments may be especially interested in whether this flaw can be triggered in environments where perf is enabled for observability or debugging. Containers, multi-tenant Linux hosts, build systems, and shared developer workstations are all places where local privilege boundaries matter. If a low-privilege account can trigger the bug, the operational concern jumps immediately from “patch eventually” to “patch urgently.” If it requires elevated capabilities, the issue may still matter, but its exposure profile changes considerably.
The more conservative reading is that any kernel UAF deserves timely remediation, regardless of whether a proof of concept exists. That is particularly true when the bug lives in core infrastructure rather than a niche driver. The kernel’s own CVE process emphasizes that applicability depends heavily on the user’s configuration and use case, which is why administrators should avoid assuming a bug is harmless simply because their current workload does not use perf heavily.
Over time, the kernel community has become more explicit about treating many bug fixes as potentially security-relevant. That does not mean every bug is remotely exploitable. It does mean the community understands that the boundary between correctness and security is porous in low-level code. A lifecycle bug in a shared-memory mapping path may look like an internal maintenance issue, but it can become an attack primitive if the surrounding conditions line up just right.
A flaw in this area can be especially troublesome because mapping lifetime often survives far beyond the call that created it. A process can fork, clone, or hand off work to another thread; descriptors can be duplicated; and cleanup can occur from different execution contexts. If the reference model does not account for every live path, the kernel may free the
Microsoft’s inclusion of a Linux kernel perf issue in its update guide, even though the page is currently unavailable, signals the broader reality of cross-platform security management. Cloud and enterprise environments routinely mix Microsoft tooling, Linux workloads, and kernel-level observability. A Linux kernel memory bug can therefore land in a Microsoft-adjacent security workflow because the affected systems are part of the same operational estate. That is a reminder that modern patch management no longer stops at operating-system branding.
It is also worth watching whether the fix lands alongside additional hardening in related perf mapping code. Kernel maintainers often use one bug as a chance to tighten invariants across nearby paths, especially when the root cause suggests a pattern rather than a one-off mistake. That could mean better refcount assertions, stricter teardown sequencing, or documentation changes that make future mistakes less likely. That would be the best possible outcome: not just a patched bug, but a less fragile subsystem.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
The perf subsystem is Linux’s built-in performance analysis framework, and its ring-buffer design is central to how it moves sampled data from kernel to user space. The user-space view is anchored by a shared control page, perf_event_mmap_page, and the kernel streams records into a mapped buffer behind it. That architecture is efficient, but it also means that lifetime management must be exact, because the kernel and user space are both touching structures that can outlive assumptions if reference counts are mishandled. Linux documentation on the perf ring buffer describes this shared-memory design and the control-page mechanism in detail.That matters because a refcount bug in a structure like
perf_mmap is not a garden-variety logic error. Refcounts are the kernel’s way of deciding when an object can be safely reused or freed, and a bad decrement or missing increment can lead to a stale pointer being accessed after the object’s lifetime ends. In security language, that is the classic setup for a UAF, or use-after-free. Once a freed object is reachable again, the bug may be exploitable in ways that range from a crash to privilege escalation, depending on what occupies the freed memory and what code paths remain reachable.Linux’s own CVE process also explains why issues like this are often treated conservatively. The kernel team notes that the CVE assignment process is deliberately cautious and that many bug fixes can receive CVEs even when exploitability is not immediately obvious. In other words, the mere fact that a bug fix exists in a security-sensitive subsystem can be enough to justify a CVE, even before the full exploitation story is nailed down. That is especially true for core kernel paths such as memory mapping, where lifetime mistakes can be subtle and architecture-dependent.
Microsoft’s update-guide page for this CVE is currently unavailable, but that does not make the issue less significant. If anything, the lack of a public advisory heightens the need to interpret the title carefully and in context. The bug is apparently in a core perf mmap path, which means it sits close to a kernel-user boundary that receives heavy scrutiny from attackers and defenders alike. Even when the immediate impact appears limited to a profiling feature, kernel memory bugs often have a way of becoming system-wide concerns once researchers start probing adjacent call chains.
Why perf bugs attract attention
Perf is not a casual subsystem. It is widely used by developers, SREs, and security teams for profiling, tracing, and diagnosing performance regressions. The ring-buffer machinery exists to move high-volume event streams with low overhead, which means performance optimizations are deeply intertwined with object lifetimes and concurrency. That combination makes for excellent engineering and occasionally dangerous bug surfaces.- The data path is hot and highly concurrent.
- The kernel and user space share state across an mmap boundary.
- Refcount mistakes can become dangling-pointer bugs.
- Debugging can be difficult because symptoms may look nondeterministic.
- Even “only local” bugs are often serious in multi-user systems.
Overview
The title of CVE-2026-23248 suggests a narrow but consequential flaw: a refcount bug in perf_mmap that can lead to a potential UAF. Theperf_mmap object typically represents the userspace mapping context for perf ring buffers, so a lifetime mistake there could affect how mappings are created, retained, or destroyed. The important detail is not just that the structure is involved, but that the bug touches mapping lifetime, which is a classic place where reference ownership goes wrong.The Linux perf documentation describes the mapping model as a control page followed by the ring buffer, with access patterns that depend on whether the mapping is writable or read-only. That means the kernel must manage not just event delivery but also page faults, mapping operations, and teardown in a way that is consistent across multiple modes of use. If a reference is dropped too early, a page fault or later cleanup step may dereference an object that has already been freed.
This kind of bug tends to sit in a gray area between reliability and security. A refcount bug might appear initially as a rare crash, but once a freed object can be reallocated with attacker-controlled data, the issue becomes more serious. In a kernel setting, that can turn into arbitrary code execution, privilege escalation, or at minimum denial of service. The exact impact depends on the surrounding hardening features and the reachable control flow, but potential UAF is a phrase no kernel maintainer likes to see.
There is also a reason such issues often attract distribution and vendor attention beyond the original subsystem. Kernel bugs in shared infrastructure can affect container hosts, developer workstations, CI runners, monitoring nodes, and even desktop systems where perf is used for troubleshooting. That broad reach means a bug that begins as a perf housekeeping issue can matter to both enterprise and consumer Linux deployments. The risk is not universal in every environment, but the blast radius is wider than the feature name implies.
What the title implies, and what it does not
The published title gives us useful clues, but it does not by itself tell us the full exploit chain. We know the defect is about refcounting and memory lifetime. We do not yet know whether the issue is reachable by unprivileged users, whether a particular perf configuration is required, or whether exploitation is practical on hardened systems. Those are critical distinctions, and they usually determine whether a kernel bug is merely theoretically dangerous or truly high risk. Still, a UAF in a mapping path is serious enough to take seriously even before those details are public.How perf_mmap Fits Into the Kernel
perf_mmap is part of the glue between the perf event subsystem and the mapped ring buffer that user space reads. The documentation shows that perf uses a shared-memory protocol with a user page, data_head, data_tail, and an mmap-backed record stream. That means perf_mmap is not an isolated helper; it is part of a live contract between the kernel and a userspace consumer.From a kernel-design perspective, that contract is delicate. The kernel must allocate, populate, fault in, and eventually tear down mapped pages while also respecting per-thread, per-CPU, and system-wide modes. It has to do so under races from scheduling, page faults, and concurrent reads. If the object lifetime is not managed by the refcount precisely, the mapping can outlast the object or the object can disappear while still in use. That is exactly the kind of bug that turns a cleanup path into an attack surface.
The mapping lifecycle
The lifecycle typically looks simple on paper: create the event, mmap the buffer, use it, then unmap and destroy it. In reality, there are several transitions that can happen in parallel, especially when multiple threads interact with the same perf event or when a process exits while another thread is still handling the mapping. Each transition is a chance to either acquire or drop a reference incorrectly.- Allocation and setup must establish the first valid ownership.
- Page-fault handling may temporarily need the object to remain alive.
- Concurrent reads and writes can delay teardown.
- Process exit and fd release can race with active mappings.
- Error paths are often where refcount mistakes hide.
Why Reference Counts Matter So Much
A reference count is supposed to answer a simple question: “How many live users still need this object?” In practice, the answer is encoded across multiple functions, with ownership passing implicitly through file descriptors, VMAs, event contexts, and helper routines. That makes the system robust when implemented correctly, but fragile when one code path forgets to increment, decrements twice, or assumes another path will hold the object longer than it actually does.In perf-related code, that fragility is amplified by the interaction with memory mappings. A userspace mapping can stay alive independently of the original file descriptor, and the kernel needs to know whether the object can still be touched after the caller thinks it is done. If the refcount says “free me now” while a mapping still exists, the next access can hit freed memory. That is the essence of a use-after-free.
Refcount bugs and UAFs in kernel practice
Kernel UAFs are rarely trivial. They often begin as accounting mistakes and become security issues because the freed object sits in a cache that can be repopulated with something else. That “something else” may contain function pointers, list pointers, or other metadata that turns a stale access into a controlled write or read. Even when exploitation is not straightforward, the possibility is enough to merit fast patching and careful backporting.- The bug may be silent until a precise race occurs.
- Symptoms can vary from kernel oopses to hung processes.
- Exploitability depends on memory layout and hardening.
- The affected code path may be reachable from unprivileged tooling.
- Fixes often require coordinated stable-tree updates.
Potential Impact on Systems
The most important practical question is not whether a CVE exists, but how it might affect real systems. For CVE-2026-23248, the impact likely depends on how perf is used, which kernel versions carry the bug, and whether the vulnerable mapping path is reachable by the relevant user. Because the public advisory is missing, we should be careful not to overstate the exploit story. Still, a kernel UAF is never something to dismiss as an academic defect.Enterprise environments may be especially interested in whether this flaw can be triggered in environments where perf is enabled for observability or debugging. Containers, multi-tenant Linux hosts, build systems, and shared developer workstations are all places where local privilege boundaries matter. If a low-privilege account can trigger the bug, the operational concern jumps immediately from “patch eventually” to “patch urgently.” If it requires elevated capabilities, the issue may still matter, but its exposure profile changes considerably.
Consumer and workstation relevance
Consumer Linux systems are less likely than servers to run intensive perf workflows all the time, but that does not eliminate exposure. Desktop users, performance engineers, and developers regularly invoke perf for troubleshooting. Systems used for software development also often run with debugging tools installed and with elevated permissions granted to trusted accounts. In that environment, a local kernel memory bug can still matter even if it is not broadly exploitable from a web browser or remote service.The more conservative reading is that any kernel UAF deserves timely remediation, regardless of whether a proof of concept exists. That is particularly true when the bug lives in core infrastructure rather than a niche driver. The kernel’s own CVE process emphasizes that applicability depends heavily on the user’s configuration and use case, which is why administrators should avoid assuming a bug is harmless simply because their current workload does not use perf heavily.
Why the missing advisory matters
When a public advisory is unavailable, defenders lose three things at once: scope, severity, and exact remediation guidance. That is inconvenient for patch management because teams cannot easily determine whether the bug affects their deployment, whether workarounds exist, or which kernel branches contain the fix. In practice, that usually means relying on the eventual stable-tree backport and release notes from the kernel ecosystem. Until then, the prudent assumption is that the issue is worthy of attention.Historical Context: Perf Security Bugs and Kernel Hardening
Perf has been around long enough that its interfaces are mature, but maturity does not eliminate security risk. The subsystem’s complexity stems from the same qualities that make it powerful: high-throughput data paths, multiple modes, and aggressive optimization. Linux documentation shows that the ring-buffer mechanism is designed for performance and relies on careful synchronization, which is exactly the kind of environment where subtle refcounting mistakes can hide.Over time, the kernel community has become more explicit about treating many bug fixes as potentially security-relevant. That does not mean every bug is remotely exploitable. It does mean the community understands that the boundary between correctness and security is porous in low-level code. A lifecycle bug in a shared-memory mapping path may look like an internal maintenance issue, but it can become an attack primitive if the surrounding conditions line up just right.
Why this class of bug keeps recurring
Refcount bugs keep recurring because ownership in the kernel is distributed across many layers. File descriptors, VMAs, event contexts, and helper structures all participate in lifetime control, and each layer may have its own teardown path. If one layer assumes another will keep the object alive, the assumption can break during abnormal exit, error unwinding, or concurrent close. That is why UAFs often emerge in code that is otherwise considered stable.- Shared ownership is hard to reason about.
- Error paths are easy to under-test.
- Concurrency multiplies possible race windows.
- Readability and performance often trade off against simplicity.
- Small accounting mistakes can have large downstream effects.
What Makes the perf_mmap Path Sensitive
The mmap path is sensitive because it governs the bridge between kernel-managed ring buffers and user-visible memory mappings. The perf documentation shows that the control page and buffer are laid out contiguously and accessed according to specific synchronization rules. That means teardown must respect both memory ordering and object ownership, not just one or the other.A flaw in this area can be especially troublesome because mapping lifetime often survives far beyond the call that created it. A process can fork, clone, or hand off work to another thread; descriptors can be duplicated; and cleanup can occur from different execution contexts. If the reference model does not account for every live path, the kernel may free the
perf_mmap backing state too early. That is exactly the sort of condition that produces a crash in development and a potential exploit in the wild.Kernel memory safety in one sentence
The kernel must always know whether an object is still reachable. When it guesses wrong, a free becomes a dangling pointer, and a dangling pointer can become a security incident.Why Vendors Track These Issues Closely
Vendors care about bugs like CVE-2026-23248 because kernel issues are expensive to triage after the fact. Once a UAF is public, downstream patching has to balance stability against urgency, and the fix may need to be backported across multiple supported kernel streams. The Linux CVE process notes that stable/LTS support boundaries matter, and that not every version will receive the same treatment.Microsoft’s inclusion of a Linux kernel perf issue in its update guide, even though the page is currently unavailable, signals the broader reality of cross-platform security management. Cloud and enterprise environments routinely mix Microsoft tooling, Linux workloads, and kernel-level observability. A Linux kernel memory bug can therefore land in a Microsoft-adjacent security workflow because the affected systems are part of the same operational estate. That is a reminder that modern patch management no longer stops at operating-system branding.
Enterprise implications
Enterprises may want to review whether any hosts expose perf to untrusted users, whether developer machines are protected by kernel hardening defaults, and whether container hosts permit local profiling capabilities. The answer to those questions can determine whether this vulnerability is theoretical or operationally meaningful. If perf is already restricted, the bug might be a lower priority. If not, it belongs on the short list.Consumer implications
For consumers, the immediate concern is simpler: apply kernel updates promptly once the fix is available. Desktop distributions often carry their own backports, and users may never see the CVE name, only the patched kernel package. The lesson is the same regardless of platform: memory-safety bugs in core kernel paths are not the kind of issue to defer indefinitely.Strengths and Opportunities
The upside of a disclosure like this is that it reinforces the value of the kernel community’s increasingly conservative approach to bug classification and patching. A problem labeled as a refcount bug and potential UAF in perf_mmap is exactly the sort of issue that benefits from rapid containment, stable backports, and careful review of adjacent code. It is also a chance for operators to reassess whether perf access is more open than it needs to be.- It highlights a core memory-safety issue rather than a cosmetic bug.
- It gives maintainers a reason to audit nearby reference ownership paths.
- It may lead to stronger teardown and fault-path testing.
- It encourages operators to tighten perf access controls where possible.
- It reinforces the value of stable/LTS backports for kernel security.
- It may surface related bugs in other mmap-backed subsystems.
- It improves awareness that profiling tools can still be attack surfaces.
Risks and Concerns
The main concern is that the public record is incomplete right now, which makes it harder for defenders to determine exposure and urgency. A missing advisory page means no official scope statement, no exact affected versions, and no public mitigation guidance yet. That uncertainty is risky because teams may underestimate the issue or postpone remediation while waiting for more detail.- The affected kernel versions are not clearly documented in the public page.
- The exploitability threshold is not yet visible to defenders.
- The bug may be reachable from local unprivileged code or may require elevated access.
- The issue could be present in downstream kernels with different backport histories.
- Administrators may assume perf is too niche to matter, which could be a mistake.
- UAF bugs can produce outcomes ranging from crashes to privilege escalation.
- The absence of a public advisory can slow incident-response planning.
Looking Ahead
The next important milestone is the publication of a usable advisory trail: an official MSRC page, a kernel stable commit reference, or a downstream vendor bulletin that spells out the scope. Once that exists, defenders can compare affected versions, determine whether the issue touches their deployments, and prioritize updates accordingly. Until then, the best reading is cautious but not alarmist: this is a serious kernel memory bug, but the real-world risk hinges on the missing details.It is also worth watching whether the fix lands alongside additional hardening in related perf mapping code. Kernel maintainers often use one bug as a chance to tighten invariants across nearby paths, especially when the root cause suggests a pattern rather than a one-off mistake. That could mean better refcount assertions, stricter teardown sequencing, or documentation changes that make future mistakes less likely. That would be the best possible outcome: not just a patched bug, but a less fragile subsystem.
- Watch for the official advisory and any linked kernel commit.
- Check whether Linux distributions issue backported fixes.
- Verify whether the bug requires local access or special capabilities.
- Monitor whether related perf or mmap code receives additional hardening.
- Compare vendor bulletins for differences in severity language and scope.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: