The Linux kernel’s CVE-2026-23392 is a narrow but serious use-after-free issue in the nf_tables flowtable error path, and its significance comes from the kind of bug it is rather than the drama of its description. According to the kernel.org-stamped NVD text, the bug can expose a flowtable to both the packet path and the
The CVE description says the flaw shows up in an error path, not the normal happy path, which is an important distinction. In practice, that means the vulnerability is likely to be hit only when the kernel is already in the middle of a failed flowtable setup or a failed offload transition, such as when the number of hooks has reached a limit or hardware offload setup fails. Those are the kinds of paths that receive less real-world testing than ordinary packet forwarding, yet they still must obey the same lifetime rules as the rest of the subsystem. The kernel’s description also notes that the parser could be improved to catch duplicate device-hook usage earlier, reducing how often this late-stage cleanup path is exercised. That suggests maintainers see the bug as partly a control-flow ht a single bad
This is also a reminder that Linux kernel security increasingly lives in the space between performance optimizations and memory safety guarantees. Flowtables exist precisely because the networking stack wants to be fast; RCU exists because readers should not stall on every teardown; error handling exists because not every offload attempt succeeds. When those three things collide, a bug can be rare, hard to reproduce, and still security-relevant. The fact that KASAN surfaced a use-after-free from the
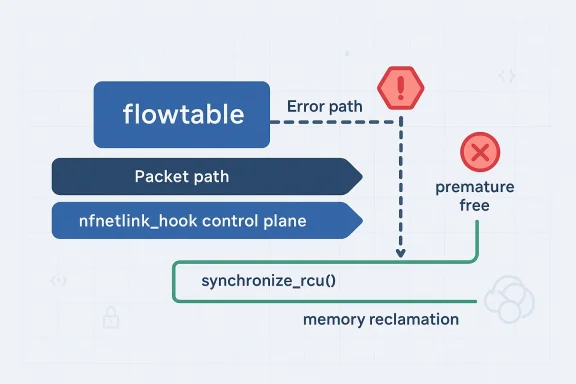
Finally, Microsoft’s Security Update Guide entry matters because it shows how Linux kernel CVEs now move through a broader enterprise remediation ecosystem, not just upstream kernel mailing lists. That has practical consequences for hybrid fleets, cloud appliances, WSL-adjacent environments, and any organization that tracks Linux packages through vendor advisories rather than mainline Git history. In other words, even a rare kernel bug becomes operationally important once it enters a patch-management pipelt a technical level, the bug centers on the lifetime of a flowtable object after a failed setup sequence. The kernel description says a hook that already refers to the flowtable may already be registered, which means the flowtable can still be reachable through runtime paths even after the error code has been triggered. If the code unregisters hooks and then immediately releases the object without waiting for in-flight RCU readers to drain, a stale reference can survive long enough to be dereferenced. That is the classic shape of a use-after-free: the object is gone from the allocator’s perspective, but not gone from the readers’ perspective.
The kernel APIthe meaning of
The vulnerability is also interesting because it sits in a rarely exercised path. The kernel text says the error path should only happen when reaching the maximum number of hooks or when hardware offload setup fails. That rarity matters for two reasons. First, it explains how the bug could survive long enough to reach CVE status despite being in a mature subsystem. Second, it suggests that the exploitable surface may be narrower than the headline implies, even though the memory-safety issue is real. Rare bugs can still be serious if they occur in the wrong context or are reachable through user-contflows.
What makes this CVE especially instructive is that it reflects a common kernel pattern: a fix that is locally simple but globally meaningful. The patch does not appear to redesign flowtables, alter the packet path, or remove the error path entirely. Instead, it aligns teardown with the lifetime model already implied by RCU. That is often the cleanest type of kernel fix, because it preserves behavior while restoring correctness. And in a networking subsystem, preserving behavior matters as much as fixing memory safety, because administrators need stability at scale, not just security in the abstract.
The core issue is a stale pointer window created during cleanup. The CVE description says that after unregistering hooks from the error path, the code should call
The error path’s rarity actually makes the RCU mistake more understandable, not less serious. When code is expected to fail only under unusual conditions, it is easy for developers to focus on the success path and assume the teardown path is “obviously” safe. But in kernel networking, hooks, control-plane objects, and packet-path readers can all overlap in ways that are hard to reason about informally. That is why the bug was uncovered by KASAN rather than by routine testing. Sanitizers are esping these narrow lifetime mistakes because they catch the exact moment a freed object is touched.
The practical effect is that the vulnerability is less about a direct packet payload issue and more about lifetime confusion in shared infrastructure. That distinction matters. It means the bug is not likely to be exploitable by tricking the kernel into parsing a malformed packet; instead, it depends on a configuration and teardown sequence that leaves a flowtable reachable after an error. That is a narrower attack shape, but one that still deserves iause use-after-free bugs are among the most dangerous classes in the kernel.
This also explains why the bug was observed when dumping hooks. A dump operation sounds passive, but in kernel terms it often walks live data structures and assumes those structures still obey their lifetime guarantees. If teardown races with introspection, the result can be a UAF that appears only during administrative actions. That creates a subtle operational risk: even if ordinareems stable, a management operation could trip the bug at exactly the wrong time.
That also helps explain why the stable patch probably exists in several Linux branches already. When a concurrency bug is found in a core networking subsystem, maintainers generally prefer a minimal, backportable fix that restores ordering without reworking the design. Here, that means waiting for an RCU grace period aoks. The fact that multiple stable references are attached to the CVE strongly suggests the fix moved quickly through the upstream-to-stable pipeline.
From an operational perspective, the source of discovery matters because it tells defenders how to interpret the risk. A KASAN-found use-after-free is usually not a speculative issue or a mere theoretical cleanup task. It is a concrete memory-safety defeve already reasoned about enough to write a fix. That makes patch adoption the correct response, even before NVD assigns a score.
The description also hints at a possible future improvement: the hook parser could validate duplicate device-hook usage earlier, before the error path becomes reachable. That would be a quality-of-life enhancement for the code, but it is not required to eliminate the UAF. From a security standpoint, it is useful because it reduces the odds of reaching the problematic path at all. From a maintenance standpoint, it also makes the subsysteout. That is the kind of preventive cleanup kernel maintainers like, even when they have already closed the vulnerability itself.
That said, enterprises should not dismiss the bug because NVD had not yet published a score. The absence of a score at publication time is not the same thing as low severity. It vulnerability is still moving through enrichment. For patch management, that is a reason to watch the upstream fix and vendor backports closely, not a reason to defer action.
This is also a reminder that security operations should not overfit to numeric severity alone. Kernel bugs often sit in a gray area where the exploitability is highly context-dependent. A score later in the lifecycle may help triage, but the first sign class itself. A UAF in networking code is not something to casually postpone.
The third thing to watch is whether enterprise security teams use this as a reminder to audit advares more aggressively. Flowtables, hardware offload, and hook management are exactly the sort of capabilities that make servers faster while also enlarging the concurrency surface. A bug like CVE-2026-23392 is a good argument for pairing performance features with stronger validation and better observability.
CVE-2026-23392 is not a flashy exploit story, but it is a very real example of why kernel security work remains so unforgiving: a tiny teardown mistake, hidden in an uncommon path, can still undermine the integrity of a high-speed networking subsystem. The best response is also the most kernel-native one—respect the RCU model, patch the error path, and treat rare lifetime bugs as first-class security issues before they become practical ones.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
nfnetlink_hook control plane after an error occurs, because teardown happened before an RCU grace period had elapsed. The fix is conceptually simple—wait with synchronize_rcu() after unregistering hooks on the failing path—but that simplicity hides a common kernel lesson: in concurrency-sensitive code, when you free matters as much as what you free. The vulnerability was received from kernel.org on March 25, 2026, and NVD had not yet assigned a CVSS score at publication time, which leaves defenders with a patch-first problem rather than a neat numeric severity label. affected subsystem sits in one of Linux networking’s most performance-sensitive areas: Netfilter, specifically the nf_tables framework and its flowtable fast path. Netfilter flowtables are designed to let established traffic bypass parts of the classic forwarding path, improving throughput and reducing overhead on packets that are already known-good. That optimization is valuable, but it also means the subsystem relies heavily on carefully managed object lifetimes and RCU discipline, because packets may continue to observe objects long after the control plane thinks it has cleaned them up. Linux kernel documentation describes flowtables as a fast path that can offload forwarding decisions and even support hardware offload, which means the structure is not just a bookkeeping object but part of the live packet-processing path.The CVE description says the flaw shows up in an error path, not the normal happy path, which is an important distinction. In practice, that means the vulnerability is likely to be hit only when the kernel is already in the middle of a failed flowtable setup or a failed offload transition, such as when the number of hooks has reached a limit or hardware offload setup fails. Those are the kinds of paths that receive less real-world testing than ordinary packet forwarding, yet they still must obey the same lifetime rules as the rest of the subsystem. The kernel’s description also notes that the parser could be improved to catch duplicate device-hook usage earlier, reducing how often this late-stage cleanup path is exercised. That suggests maintainers see the bug as partly a control-flow ht a single bad
kfree().This is also a reminder that Linux kernel security increasingly lives in the space between performance optimizations and memory safety guarantees. Flowtables exist precisely because the networking stack wants to be fast; RCU exists because readers should not stall on every teardown; error handling exists because not every offload attempt succeeds. When those three things collide, a bug can be rare, hard to reproduce, and still security-relevant. The fact that KASAN surfaced a use-after-free from the
nfnetlink_hook path while dumping hooks shows the issue was not theoretical. It was observed in tooling, which is exactly how many kernel lifetime bugsown.Finally, Microsoft’s Security Update Guide entry matters because it shows how Linux kernel CVEs now move through a broader enterprise remediation ecosystem, not just upstream kernel mailing lists. That has practical consequences for hybrid fleets, cloud appliances, WSL-adjacent environments, and any organization that tracks Linux packages through vendor advisories rather than mainline Git history. In other words, even a rare kernel bug becomes operationally important once it enters a patch-management pipelt a technical level, the bug centers on the lifetime of a flowtable object after a failed setup sequence. The kernel description says a hook that already refers to the flowtable may already be registered, which means the flowtable can still be reachable through runtime paths even after the error code has been triggered. If the code unregisters hooks and then immediately releases the object without waiting for in-flight RCU readers to drain, a stale reference can survive long enough to be dereferenced. That is the classic shape of a use-after-free: the object is gone from the allocator’s perspective, but not gone from the readers’ perspective.
The kernel APIthe meaning of
synchronize_rcu() very clear: it waits until a full grace period has elapsed, meaning all pre-existing RCU read-side critical sections have completed. That is precisely why the fix in this CVE makes sense. If teardown is occurring after unregistering hooks but before the data structure is actually safe to reclaim, the correct response is to delay the free until readers can no longer hold valid references. In kernel terms, this is a conservative, well-understood safety barrier rather than a workaround.The vulnerability is also interesting because it sits in a rarely exercised path. The kernel text says the error path should only happen when reaching the maximum number of hooks or when hardware offload setup fails. That rarity matters for two reasons. First, it explains how the bug could survive long enough to reach CVE status despite being in a mature subsystem. Second, it suggests that the exploitable surface may be narrower than the headline implies, even though the memory-safety issue is real. Rare bugs can still be serious if they occur in the wrong context or are reachable through user-contflows.
What makes this CVE especially instructive is that it reflects a common kernel pattern: a fix that is locally simple but globally meaningful. The patch does not appear to redesign flowtables, alter the packet path, or remove the error path entirely. Instead, it aligns teardown with the lifetime model already implied by RCU. That is often the cleanest type of kernel fix, because it preserves behavior while restoring correctness. And in a networking subsystem, preserving behavior matters as much as fixing memory safety, because administrators need stability at scale, not just security in the abstract.
 What the bug actually does
What the bug actually does
The core issue is a stale pointer window created during cleanup. The CVE description says that after unregistering hooks from the error path, the code should call synchronize_rcu() because a hook that refers to the flowtable may already have been registered. That means the flowtable can still be visible to packet processing and to the nfnetlink_hook control plane while the error path is trying to tear it down. If the object is released too early, any re or discovers a reference can encounter freed memory.Why RCU matters here
RCU is not just a synchronization primitive; it is a contract between writers and readers. Readers are allowed to proceed quickly, but writers must account for those readers before reclaiming memory. The Linux documentation emphasizes that a grace period is the moment when all readers that started before the wait have completed. That contract is why RCU is so useful in networking, where read performance matters, but it also means a writer that skips the wait can create a latent memory-safety bug.The error path’s rarity actually makes the RCU mistake more understandable, not less serious. When code is expected to fail only under unusual conditions, it is easy for developers to focus on the success path and assume the teardown path is “obviously” safe. But in kernel networking, hooks, control-plane objects, and packet-path readers can all overlap in ways that are hard to reason about informally. That is why the bug was uncovered by KASAN rather than by routine testing. Sanitizers are esping these narrow lifetime mistakes because they catch the exact moment a freed object is touched.
The practical effect is that the vulnerability is less about a direct packet payload issue and more about lifetime confusion in shared infrastructure. That distinction matters. It means the bug is not likely to be exploitable by tricking the kernel into parsing a malformed packet; instead, it depends on a configuration and teardown sequence that leaves a flowtable reachable after an error. That is a narrower attack shape, but one that still deserves iause use-after-free bugs are among the most dangerous classes in the kernel.
- The object is freed too early after an error.
- Readers may still access it through packet or control paths.
- The fix is to wait for an RCU grace period before reclaiming memory.
- The bug is rare, but rarity does not eliminate exploitabed the problem as a use-after-free during hook dumping.
Why this belongs to netfilter and flowtable design
Netfilter has always balanced policy enforcement, packet classification, and fast-path acceleration. Flowtables are an explicit acknowledgment that not every packet needs to traverse the full rule evaluation path once a flow is established. That architectural choice boosts throughput, but it also creates a second set of lifecycle rules for objects that may be shared between control plane state and dataplane readers. Linux’s own flowtable documentation describes packets hitting the flowtable as bypassing classic forwarding, which is exactly why stale object exposure is dangerous: the fast path is designed to be low friction, not heavily synchronized.The control plane and the packet path are both relevant
The CVE text explicitly says the flowtable becomes visible to the packet path and to the nfnetlink_hook control plane. That is a big deal because it means the object is not only used in forwarding decisions but also inspected or enumerated by management interfaces. A use-after-free in a dataplane object is already serious; a use-after-free that can cross into intros is even more troubling because it broadens the set of code paths that might dereference stale memory.This also explains why the bug was observed when dumping hooks. A dump operation sounds passive, but in kernel terms it often walks live data structures and assumes those structures still obey their lifetime guarantees. If teardown races with introspection, the result can be a UAF that appears only during administrative actions. That creates a subtle operational risk: even if ordinareems stable, a management operation could trip the bug at exactly the wrong time.
- Flowtables accelerate established traffic.
- Fast paths reduce synchronization opportunities.
- Control-plane inspection widens the set of readers.
- Hook dumps are not “safe” just because they are read-only.
- Rare teardown races can still be reachable through normal administration.
How the bug surfaced
The kernel description says the issue was uncovered by KASAN, which is one of the most important clues in the entire advisory. KASAN, the Kernel Address Sanitizer, is built to catch invalid memory accesses such as use-after-free conditions. That means the bug was likely not discovered through exploitation or a production crash but through instrumentation that m violation visible. In modern kernel security, that is a good sign: it means the codebase is being systematically checked for problems before attackers can turn them into real-world incidents.Why rare bugs are still found
Rare paths are exactly where sanitizers and fuzzing are most valuable. Human testers tend to exercise common paths repeatedly, while tools can generate unusual combinations that hit error handling, teardown, and introspection all at once. The CVE text says the erroen the kernel hits the maximum number of hooks or when hardware offload fails, which are the kinds of states that automated testing is better at provoking than humans are.That also helps explain why the stable patch probably exists in several Linux branches already. When a concurrency bug is found in a core networking subsystem, maintainers generally prefer a minimal, backportable fix that restores ordering without reworking the design. Here, that means waiting for an RCU grace period aoks. The fact that multiple stable references are attached to the CVE strongly suggests the fix moved quickly through the upstream-to-stable pipeline.
From an operational perspective, the source of discovery matters because it tells defenders how to interpret the risk. A KASAN-found use-after-free is usually not a speculative issue or a mere theoretical cleanup task. It is a concrete memory-safety defeve already reasoned about enough to write a fix. That makes patch adoption the correct response, even before NVD assigns a score.
- KASAN found the issue as an actual UAF.
- The bug was in an error path, not the common path.
- The condition depends on hook exhaustion or offload failure.
- ences indicate real downstream patchability.
- Instrumentation found the bug before public exploitation did.
What the fix means technically
The fix is straightforward: callsynchronize_rcu() after unregistering hooks on the error path. That wait ensures any reader that could still see the flowtable has completed before the memory is released. In a high-performance kernel subsystem, that kind of wait is not free, but it is acceptable when the code is already on an exceptional path. The advisory notes that this path is y the kind of situation where correctness should take priority over micro-optimization.Why the patch is the right tradeoff
If the flowtable is only being torn down because setup failed, the system is already not on the performance-critical fast path. That makes a grace-period wait a sensible cost. It is better to pay a one-time synchronization penalty during error handling than to risk freeing memory that a packet or control reader might still access. Linux’s RCU model exists precisely to make this kind of delayed reclamation practical, so the patch is not unusual—it is the canonical fix.The description also hints at a possible future improvement: the hook parser could validate duplicate device-hook usage earlier, before the error path becomes reachable. That would be a quality-of-life enhancement for the code, but it is not required to eliminate the UAF. From a security standpoint, it is useful because it reduces the odds of reaching the problematic path at all. From a maintenance standpoint, it also makes the subsysteout. That is the kind of preventive cleanup kernel maintainers like, even when they have already closed the vulnerability itself.
synchronize_rcu()prevents premature reclamation.- The error path can tolerate extra latency.
- Earlier validation would make the bug path less reachable.
- The fix preserves existing behavior instead of redesigning flowtables.
- This is a lifecycle bug, not a parser bug.
Enterprise impact
For enterprises, the immediate question is not whether this is a headline-grabbing remote exploit; it is whether the bug can affect fleet reliability, appliance behavior, or network-management workflows. In many environments, the answer is yes, because nftables and flowtables are not niche lab features. They are used in routers, gateways, container hosts, firewalls, and Linux appliances where control-plane stability matters as much as raw throughput. A use-after-free in those contexts can crash a daemon, destabilize packet processing, or complicate troubleshooting even if exploitation is difficult.Consumer vs enterprise exposure
On consumer desktops, the practical risk may be low unless the user is running custom firewalling, advanced networking, or a kernel build that exercises flowtables. On servers and appliances, the exposure is more plausible because administrators are more likely to use nftables aggressively and to rely on hardware offload or high-voluThe error path described in the CVE also suggests a configuration-sensitive trigger, which is exactly the sort of thing that crops up more often in managed infrastructure than in typical home use.That said, enterprises should not dismiss the bug because NVD had not yet published a score. The absence of a score at publication time is not the same thing as low severity. It vulnerability is still moving through enrichment. For patch management, that is a reason to watch the upstream fix and vendor backports closely, not a reason to defer action.
- Firewalls and routers may exercise flowtables heavily.
- Managed Linux servers are more likely than desktops to hit the relevant code.
- Hardware offload failures can move the bug from theory to reality.
- Control-plane tooling may surface the issue during inspection or dumps.
- Patch timing will vary across vendor kernels and LTS branches.
Why the absence of a CVSS score should not calm anyone
A missing CVSS score can create false comfort. In reality, it often means the vulnerability is still awaiting formal scoring, not that the risk has been assessed as trivial. Here, the description already tells defenders enough: a use-after-free exists, it is in a networking subsystem, and it h an error path involving hooks and offload setup. That combination is sufficient to treat the CVE as a real patch item.How to think about severity before scoring
In practice, teams should prioritize by exposure and reachability. If you run nftables flowtables, especially with hardware offload or advanced hook configurations, this is more urgent. If your kernels do not enable or use the feature, the practical risk is lower, but the update still belongs in your normal kernel main is the right way to handle a CVE whose technical severity is obvious but whose scoring is delayed.This is also a reminder that security operations should not overfit to numeric severity alone. Kernel bugs often sit in a gray area where the exploitability is highly context-dependent. A score later in the lifecycle may help triage, but the first sign class itself. A UAF in networking code is not something to casually postpone.
- No CVSS score does not mean low risk.
- Exposure depends on whether flowtables are in use.
- Vendor backports may lag mainline by days or weeks.
- High-performance networking environments should prioritize this patching should start from bug class, not just the score.
Strengths and Opportunities
The encouraging part of this CVE is that it looks like a classic well-scoped kernel fix rather than a sprawling redesign. The vulnerability appears to have been identified cleanly, the remedy is focused, and the affected path is rare enough that the remediation should be low risk for most systems. That is the ideal profile for a security update: narrow blast radius, clear rationale, and a fix that alem’s existing synchronization model.- The fix is conceptually simple and easy to backport.
synchronize_rcu()matches the subsystem’s lifetime rules.- The affected error path is rare, which limits routine disruption.
- KASAN detection suggests the bug was caught before wide exploitation.
- The patch can likely be carried in stable trees without major behavioral change.
- The issue may prompt broader cleanup of hook parsing and validation.
- Enterprises get a clear kernel-update item even before formal CVSS scoring.
Risks and Concerns
The main concern is that use-after-free bugs in kernel networking are always worth taking seriously, even when they appear rare. The network stack is full of asynchronous readers, introspection paths, and offload logic, so an object that should have died can remain visible longer than expected. That makes the bug class dangerous even when the trigger path is uncommoe exploitable if a stale object is reused in the wrong way.- Rare error paths are harder to test thoroughly.
- Hook dumping and control-plane queries widen the reader set.
- Hardware offload failures may produce environment-specific behavior.
- Lack of an initial CVSS score can delay triage in some organizations.
- Vendors may backport the fix under different package versions, complicating verification.
- Adjacent networking code may contain similar lifetime assumptions.
Looking Ahead
The first thing to overage** across major distro and vendor kernels. Because the issue was received from kernel.org with stable references attached, it is likely to move quickly into maintained branches, but administrators still need to confirm exactly which build numbers contain the fix. Microsoft’s advisory page signals broader ecosystem tracking, yet the practical remediation path will still depend on how each vendor packages the patch.What to monitor next
- Vendor advisories that map thpackage versions.
- Stable-kernel backports in long-term support branches.
- Any follow-up parser hardening that makes the error path less reachable.
- Signs of similar lifetime bugs in adjacent nf_tables or flowtable code.
- Whether NVD later assigns a score that aligns with the observed bug class.
The third thing to watch is whether enterprise security teams use this as a reminder to audit advares more aggressively. Flowtables, hardware offload, and hook management are exactly the sort of capabilities that make servers faster while also enlarging the concurrency surface. A bug like CVE-2026-23392 is a good argument for pairing performance features with stronger validation and better observability.
CVE-2026-23392 is not a flashy exploit story, but it is a very real example of why kernel security work remains so unforgiving: a tiny teardown mistake, hidden in an uncommon path, can still undermine the integrity of a high-speed networking subsystem. The best response is also the most kernel-native one—respect the RCU model, patch the error path, and treat rare lifetime bugs as first-class security issues before they become practical ones.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center