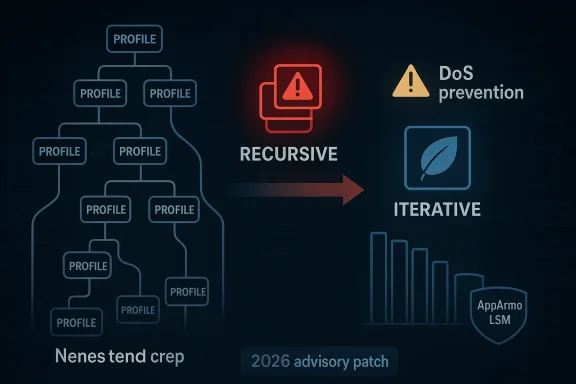
CVE-2026-23404 has all the hallmarks of a small-looking kernel bug with outsized operational consequences: it turns a recursive AppArmor profile-removal routine into an iterative one to avoid kernel stack exhaustion and crashes. The issue sits in a security module many administrators treat as background plumbing, yet the fix speaks directly to reliability, containment, and how Linux hardens itself against pathological nested policy structures. Microsoft’s advisory entry and Ubuntu’s security page both frame the problem as more than a code-style cleanup; it is a stability and security correction with real denial-of-service implications or is one of Linux’s core mandatory access control systems, built to confine applications with task-centered profiles rather than relying only on traditional discretionary permissions. The kernel documentation describes it as a security module that loads profiles from user space and applies them to running tasks, which makes profile lifecycle management a sensitive part of the overall trust model
That matters because profile management is not just administrative bookkeeping. If removal logic walks deeply nested profiles recursively, it can consume stack space in proportion to the nesting depth, which is exactly the kind of behavior kernel developers try to eliminate in security-sensitive code. In this case, the fix was to replace recursive profile release with an iterative walk that repeatedly removes leaf profiles until the subtree is gones without depending on call-stack depth
Ubuntu’s vulnerability page is especially helpful here because it ties the bug to a concrete reproduction pattern and explains the root cause in direct language. Its description says the recursive
The larger context is that this CVE is part of a broader AppArmor security wave being tracked across the Linux ecosystem in early 2026. Ubuntu’s security material notes that Qualys found multiple AppArmor LSM issues that could support denial of service, kernel memory disclosure, local privilege escalation, or even container escape in certain combinations, which helps explain why this advisory was treated as part of a broader hardening effort rather than an isolated bugfix
The immediate problem is straightforward: when AppArmor removes a nested profile tree, the old code path recursed through that structure. If an attacker could construct enough nesting, the kernel would be forced into deep recursive removal, risking stack exrather than completing the deletion safely
This is a classic kernel-pattern failure. Recursion is elegant in user-space code, but in kernel code it often becomes a liability because kernel stacks are small and failures are catastrophic. The bug does not need to grant code execution to become security-relevant; a reliable crash is already enough for a denial-of-service vulnerability, especially if the attacker can trigger it locally and repeatedly
The security significance is compounded by the fact that profile removal is part of normal policy management. If the vulnerable path can be reached through legitimate administrative or container orchestration flows, then the issue may be reachable without exotic prerequisites, which increases exposure in real environments. That is the kind of bug that hides in plain sight until someone stress-tests the edge cases
This is also a textbook example of how kernel code gets safer over time. Rather than adding a special-case guard or a brittle depth limit, the patch eliminates the structural cause. That is almost always the cleaner answer in low-level code: change the algorithm so the failure mode no longer exists, rather than trying to cap it after the fact
This design choice also reflects a broader kernel hardening trend: eliminate unbounded recursion in code paths that can be influenced by user-controlled structures. In security code, bounded behavior is not a nicety; it is part of the threat model. A safer algorithm is usually preferable to a smaller patch that leaves the same structural hazard intact
That makes this CVE strategically important even if the bug is local. When profile management fails, the immediate impact can be a crash, but the broader impact is trust erosion: administrators start to wonder whether the policy subsystem is safe to automate, safe to scale, and safe to expose to untrusted tenants or orchestration systems. In enterprise Linux, that matters almost as much as the exploit class itself
Container environments raise the stakes further. Even if the bug is not a direct container escape on its own, any kernel flaw that can be triggered by policy manipulation or nested profile handling deserves attention in shared-host scenarios. In practice, the question is not just “Can it be exploited?” but “What breaks when it is stressed?”
From an operations perspective, the reproducer matters because it suggests a class of workload more than a one-off exploit string. Any environment that programmatically creates deeply nested policy hierarchies, or that accepts policy content fros, could be at heightened risk if running an unfixed kernel. This is the kind of issue that can sit dormant until a deployment pipeline or test harness accidentally trips it
A second operational lesson is that denial-of-service CVEs in kernel security modules are often more serious than they look on paper. Thutomation, interrupt remote management sessions, and cause cascading support issues if the crash happens during maintenance windows or image rollout. Those are the kinds of failures that stretch far beyond the immediate bug
The pattern is important. When multiple bugs land in the same subsystem, it usually means maintainers and researchers are probing the same design boundaries from different angles. That is not necessarily a sign of systemic collapse; it is often what healthy security review looks like when a mature subsystem gets more aggressive testing
It also means the patch queue may be wider than the one CVE number suggests. If a fleet is already test it is prudent to check whether adjacent releases contain companion hardening changes, since those often arrive close together once maintainers identify a sharp edge. The practical takeaway is simple: patching one AppArmor issue should trigger a broader review
That cross-platform visibility is useful for defenders. It means security teams can track a Linux kernel issue throughworkflow, even if the underlying fix ships through distro channels rather than Microsoft itself. In practical terms, the advisory acts as an indexing layer for enterprise response, not as the original source of the patch
The downside is obvious too. When different vendors describe the same issue with different urgency or in differentn underestimate the overlap. That makes concrete, technical descriptions like “replace recursive profile removal with iterative approach” particularly valuable, because they map directly to code behavior rather than marketing language
There is also an opportunity here for administrators and distro maintainers to tighten policy-testing practices. If a nested-profile teardown can crash the kernel, then stress testing AppArmor management paths should become part of routine validation, especially in environments that automate policy deployment at scale. The fix can become a trigger for better operational hygiene, not just a patch event
There is also the usual backporting risk. Kernel fixes that are straightforward upstream can become messy when applied to vendor trees with different AppArmor or LSM backends, so administrators should not assume that a CVE entry automatically means their shipped kernel is safe. Verification still matters, especially on long-term support and OEM branches
It is also worth watching whether this CVE becomes a reference point for further AppArmor cleanup. When one code path is refactored to remove an unsafe pattern, maintainers often look for nearby spots where the same assumption might still exist. That is especially true in security modules, where consistency failures tend to cluster around lifecycle management
Source: MSRC Security Update Guide - Microsoft Security Response Center
That matters because profile management is not just administrative bookkeeping. If removal logic walks deeply nested profiles recursively, it can consume stack space in proportion to the nesting depth, which is exactly the kind of behavior kernel developers try to eliminate in security-sensitive code. In this case, the fix was to replace recursive profile release with an iterative walk that repeatedly removes leaf profiles until the subtree is gones without depending on call-stack depth
Ubuntu’s vulnerability page is especially helpful here because it ties the bug to a concrete reproduction pattern and explains the root cause in direct language. Its description says the recursive
__aa_profile_list_release() approach could lead to kernel stack exhaustion and system crashes, and that the remedy was to replace it with an ite_remove_profile()`The larger context is that this CVE is part of a broader AppArmor security wave being tracked across the Linux ecosystem in early 2026. Ubuntu’s security material notes that Qualys found multiple AppArmor LSM issues that could support denial of service, kernel memory disclosure, local privilege escalation, or even container escape in certain combinations, which helps explain why this advisory was treated as part of a broader hardening effort rather than an isolated bugfix
 What the bug actually does
What the bug actually does
The immediate problem is straightforward: when AppArmor removes a nested profile tree, the old code path recursed through that structure. If an attacker could construct enough nesting, the kernel would be forced into deep recursive removal, risking stack exrather than completing the deletion safelyThis is a classic kernel-pattern failure. Recursion is elegant in user-space code, but in kernel code it often becomes a liability because kernel stacks are small and failures are catastrophic. The bug does not need to grant code execution to become security-relevant; a reliable crash is already enough for a denial-of-service vulnerability, especially if the attacker can trigger it locally and repeatedly
Why stack exhaustion is serious
Kernel stack exhaustion is not a graceful failure mode. When the stack overflows, the system may panic, corrupt state, or become unstable in ways that are difficult to diagnose after the fact. That makes even “just a crash” a meaningful security outcome ilarly on systems that rely on AppArmor for application confinement or multi-tenant isolationThe security significance is compounded by the fact that profile removal is part of normal policy management. If the vulnerable path can be reached through legitimate administrative or container orchestration flows, then the issue may be reachable without exotic prerequisites, which increases exposure in real environments. That is the kind of bug that hides in plain sight until someone stress-tests the edge cases
- Recursive deletion made profile removal proportional to nesting depth.
- Deeply nested profiles could exhaust the kernel stack.
- A stack crash in the kernel is a denial-of-service event.
- Iterative removal preserves behavior without recursive depth risk.
The fix and why it is better engineering
The repaired approach is conceptually simple but important: instead of descending the profile tree recursively, the kernel repeatedly looks for leaf profiles and removes them until the entire subtree is gone. Ubuntu’s advisory says this poval semantics while avoiding recursion entirely, which is exactly the kind of minimal-but-effective design change security maintainers preferThis is also a textbook example of how kernel code gets safer over time. Rather than adding a special-case guard or a brittle depth limit, the patch eliminates the structural cause. That is almost always the cleaner answer in low-level code: change the algorithm so the failure mode no longer exists, rather than trying to cap it after the fact
Why iterative deletion scales better
An iterative deletion strategy is easier for the kernel to reason about because each step removes one leaf and updates the remaining tree. That avoids building a deep call chain and makes stack consumption effectively constant with respect to nesting depth, which is the core property security engineers want from a fi that the removal semantics remain unchanged also lowers the risk of policy regressionsThis design choice also reflects a broader kernel hardening trend: eliminate unbounded recursion in code paths that can be influenced by user-controlled structures. In security code, bounded behavior is not a nicety; it is part of the threat model. A safer algorithm is usually preferable to a smaller patch that leaves the same structural hazard intact
- Removes the attack surface created by recursive descent.
- Keeps the same profile-removal semantics.
- Reduces the chance of kernel stack exhaustion.
- Aligns with common kernel-hardening practice.
Why AppArmor matters here
AppArmor is often discussed as a confinement layer, but its enforcement value depends on the reliability of its policy lifecycle. The kernel documentation notes that profiles are loaded from user space and applied to tasks, which means every phase of profile management—load, replace, remove—has to be robust under edge conditionsThat makes this CVE strategically important even if the bug is local. When profile management fails, the immediate impact can be a crash, but the broader impact is trust erosion: administrators start to wonder whether the policy subsystem is safe to automate, safe to scale, and safe to expose to untrusted tenants or orchestration systems. In enterprise Linux, that matters almost as much as the exploit class itself
Enterprise and container implications
For enterprises, AppArmor is frequently part of the defense-in-depth story for servers, containers, and multi-service hosts. A crash in the profile-removal path could iut or teardown in managed environments, which is more disruptive than it first appears because security controls are often updated dynamically during deployment workflowsContainer environments raise the stakes further. Even if the bug is not a direct container escape on its own, any kernel flaw that can be triggered by policy manipulation or nested profile handling deserves attention in shared-host scenarios. In practice, the question is not just “Can it be exploited?” but “What breaks when it is stressed?”
- Security policy engines must be safe under stress.
- Container hosts depend on reliable confinement updates.
- Crash resilience is part of security posture.
- Local-only bugs still matter on shared infrastructure.
Reproduction and operational risk
The Ubuntu page includes a reproducer that builds a chain of nested profiles and then atteot through the AppArmor control interface. That is a strong clue that the issue was not theoretical; it was reachable through a practical path that could be exercised during testing and validationFrom an operations perspective, the reproducer matters because it suggests a class of workload more than a one-off exploit string. Any environment that programmatically creates deeply nested policy hierarchies, or that accepts policy content fros, could be at heightened risk if running an unfixed kernel. This is the kind of issue that can sit dormant until a deployment pipeline or test harness accidentally trips it
What administrators should infer
Administrators should read this as a signal to audit policy lifecycle handling, not only profile syntax. Even if a given fleet never intentionally creates hundreds or thousands of nested profiles, the safe assumption is that kernel control paths must be hardened against malformed or adversarial inputs. That is especially true where security modules are meant to be defensive rather than best-effortA second operational lesson is that denial-of-service CVEs in kernel security modules are often more serious than they look on paper. Thutomation, interrupt remote management sessions, and cause cascading support issues if the crash happens during maintenance windows or image rollout. Those are the kinds of failures that stretch far beyond the immediate bug
- Inventory kernels that include AppArmor support.
- Check whether the vendor branch contains the iterative removal fix.
- Prioritize systems that load or remove nested profiles dynamically.
- Validate policy-management tooling against the patched kernel.
- Watch for crash reports during profile teardown or reload events.
Relationship to other 2026 AppArmor issues
This CVE does not exist in isolation. Ubuntu’s 2026 vulnerability material on AppArmor indicates that multiple flaws were discovered in the LSM, with impacts ranging from denial of service to privilege escalation, kernel memory disclosure, and possible container escape. That broader cluster explains why AppArmor is under unusually close scrutiny this yearThe pattern is important. When multiple bugs land in the same subsystem, it usually means maintainers and researchers are probing the same design boundaries from different angles. That is not necessarily a sign of systemic collapse; it is often what healthy security review looks like when a mature subsystem gets more aggressive testing
Why clusters of bugs matter
Clusters create operational urgency because they raise the chance that one subsystem’s failures can be chained or misinterpreted in the field. A bug that first looks like a crash may coexist with unrelated policy bugs or namespace issues, making triage harder for vendors and administrators. That is why security teams should treat this as part of an AppArmor patch wave rather than a single isolated advisoryIt also means the patch queue may be wider than the one CVE number suggests. If a fleet is already test it is prudent to check whether adjacent releases contain companion hardening changes, since those often arrive close together once maintainers identify a sharp edge. The practical takeaway is simple: patching one AppArmor issue should trigger a broader review
- Multiple AppArmor bugs surfaced in the same period.
- Subsystem-wide review often uncovers adjacent flaws.
- One fix may not be the only one an administrator needs.
- Broader patch validation reduces repeat exposure.
How Microsoft’s advisory fits into the picture
Microsoft’s vulnerability guide listing for CVE-2026-23404 is notable because it refrprise guidance increasingly spans operating-system boundaries. Even though this is a Linux kernel issue, it matters to hybrid fleets, virtualization hosts, and environments where Linux and Windows security operations are managed in parallelThat cross-platform visibility is useful for defenders. It means security teams can track a Linux kernel issue throughworkflow, even if the underlying fix ships through distro channels rather than Microsoft itself. In practical terms, the advisory acts as an indexing layer for enterprise response, not as the original source of the patch
Why cross-ecosystem tracking helps
Modern fleets rarely live entirely inside one ecosystem. A vulnerability catalog that spans Microsoft guidance, Ubuntu notices, and kernel documentation makes it easier for teams to correlate patch status across appliances, cloud images, and managed endpoints. That is increasingly how real-world security works: the source of truth is distributed, and operators have to reconcile itThe downside is obvious too. When different vendors describe the same issue with different urgency or in differentn underestimate the overlap. That makes concrete, technical descriptions like “replace recursive profile removal with iterative approach” particularly valuable, because they map directly to code behavior rather than marketing language
- Hybrid fleets need cross-vendor visibility.
- Advisory aggregation improves operational triage.
- Technical descriptions help map fixes to code.
- Different vendor taxonomies can obscure the same flaw.
Strengths and Opportunities
The strongest aspect of this fix is that it is algorithmic. It removes an entire class of failure by changing the control flow, and it does so without altering the intended semantics of profile removal. That is a clean security outcome and a good sign for maintainabilityThere is also an opportunity here for administrators and distro maintainers to tighten policy-testing practices. If a nested-profile teardown can crash the kernel, then stress testing AppArmor management paths should become part of routine validation, especially in environments that automate policy deployment at scale. The fix can become a trigger for better operational hygiene, not just a patch event
- Eliminates recursion from a kernel security path.
- Preserves existing removal behavior.
- Reduces crash risk during policy teardown.
- Encourages better stress testing of policy workflows.
- Improves confidence in AppArmor-managed environments.
- Fits well with broader kernel hardening practice.
Risks and Concerns
The biggest concern is that local kernel bugs often get dismissed as lower priority until they interrupt production. Even when the immediate issue is “only” denial of service, the operational consequences can be severe if the affected kernel protects a fleet, appliance, or container host. Local does not mean low impactThere is also the usual backporting risk. Kernel fixes that are straightforward upstream can become messy when applied to vendor trees with different AppArmor or LSM backends, so administrators should not assume that a CVE entry automatically means their shipped kernel is safe. Verification still matters, especially on long-term support and OEM branches
- Older kernels may remain exposed longer than expected.
- Vendor backports can differ from upstream fixes.
- Policy-management crashes can interrupt production workflows.
- Container and appliance hosts are especially sensitive.
- Security teams may underestimate “local” denial-of-service issues.
- Patch validation is still required even after advisories appear.
Looking Ahead
The most important next step is confirming which downstream kernels have absorbed the iterative-removal change and which have not. Ubuntu has already published its technical summary, while Microsoft’s advisory provides the cross-ecosystem tracking point, but fleet operators still need to map those notices to the exact kernel builds they runIt is also worth watching whether this CVE becomes a reference point for further AppArmor cleanup. When one code path is refactored to remove an unsafe pattern, maintainers often look for nearby spots where the same assumption might still exist. That is especially true in security modules, where consistency failures tend to cluster around lifecycle management
- Downstream vendor backports for long-term support kernels.
- Additional AppArmor hardening advisories in the same release window.
- Verification of profile-management behavior on production systems.
- Any evidence of related recursion or depth issues elsewhere in LSM code.
- Container-host guidance from distribution security teams.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: