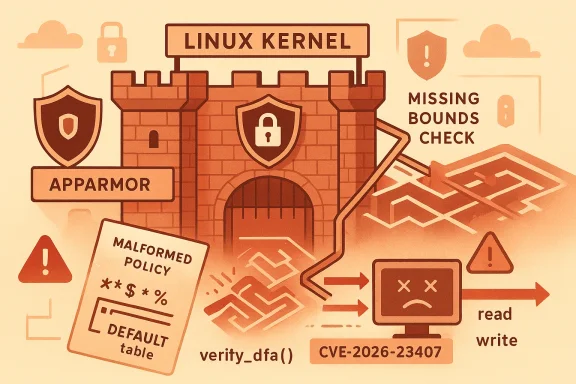
The AppArmor bug tracked as CVE-2026-23407 is a serious kernel memory-safety issue that can turn a malformed policy into a system-level denial of service, and in some cases a broader integrity and confidentiality problem. The flaw sits in verify_dfa(), where the kernel fails to apply a bounds check consistently to the DEFAULT table while walking a differential-encoding chain, allowing invalid table values to become array indexes. Ubuntu’s security record describes the result as both out-of-bounds reads and writes, and OSV records a 7.8 High CVSS score with impacts to confidentiality, integrity, and availability. (osv.dev)
AppArmor is one of Linux’s best-known mandatory access control systems, and on many enterprise and cloud deployments it is effectively part of the default trust model. It is widely used to confine applications, limit container breakout paths, and reduce the blast radius when a process is compromised. That makes any kernel bug in its policy-parsing and verification pipeline especially sensitive, because the attacker is not just poking at a userspace helper but at the core mechanism that decides whether a process may act at all.
CVE-2026-23407 is notable because it is not a simple logic bug in policy enforcement, but a memory-safety failure in the code that validates AppArmor DFA data structures. The vulnerable path only checks DEFAULTTABLE bounds in one branch, and then assumes the index is safe when the DFA state is differentially encoded. That is precisely the kind of “safe in the common case, unsafe in the edge case” mistake that kernel attackers love, because malformed input can steer execution into a code path that developers do not exercise often enough in testing. (osv.dev)
The bug is also a reminder that security modules themselves have attack surface. AppArmor’s value comes from the fact that it sits very close to the kernel, but that proximity also means parser mistakes can become kernel bugs. In practice, the risk is strongest where systems accept policy updates from local administrators, orchestration agents, containers, or package-management workflows, because those are the pathways through which malformed or adversarial policy artifacts can reach the verifier.
What makes this case particularly relevant to WindowsForum readers is the broader pattern it illustrates: defense mechanisms can become the attack surface. AppArmor is meant to reduce risk, but a flaw in its verification logic can create exactly the opposite effect, especially when the resulting out-of-bounds access can be driven repeatedly. The latest Ubuntu security entry ties the issue to affected kernel packages across multiple supported releases, showing that the problem is not academic or limited to a single test build. (osv.dev)
That distinction matters. A read-only overflow can leak kernel memory, crash a process, or corrupt internal logic. A write primitive, even if limited, is more dangerous because it can alter adjacent data structures and turn a parser bug into a broader kernel compromise. OSV’s description explicitly says the malformed DFA can cause both out-of-bounds reads and writes, which is why the issue is being treated as more than a harmless crash bug. (osv.dev)
The kernel stack trace embedded in the Ubuntu record shows KASAN catching a slab-out-of-bounds read while
In AppArmor’s case, availability is not just about one host falling over. Because the module is used to enforce confinement policies across server estates, container hosts, and cloud images, a crash in the right place can affect a large number of workloads at once. In environments with automated remediation, the system may reboot, reapply the same policy, and fail again, creating an availability loop that is far more disruptive than a one-time fault.
There is also a subtle issue around repeated exploitation. If an attacker can feed malformed policy data multiple times, they may not need a perfect one-shot exploit. Sustained denial can be enough to keep services offline, especially when policy refreshes, agent restarts, or health checks re-trigger the faulty verifier. That is one reason memory-safety bugs in kernel security paths are taken so seriously, even before exploit chaining is proven. (osv.dev)
But the same familiarity can encourage complacency. Because AppArmor is often treated as a background control, administrators may assume that vulnerabilities in the module are unlikely or merely theoretical. Recent disclosure patterns have disabused the industry of that notion. Qualys’ March 2026 CrackArmor research, followed by Ubuntu’s coordinated vulnerability handling, showed that AppArmor issues can span denial of service, information disclosure, local privilege escalation, and container escape scenarios.
The timing of these disclosures also matters. Ubuntu’s security data shows CVE-2026-23407 published on 1 April 2026 and modified on 8 April 2026, which suggests active triage and ongoing update work rather than a static, one-and-done advisory. For defenders, that usually means the patch ecosystem is still converging across releases, especially where long-term support kernels and OEM or cloud-flavored derivatives are involved. (osv.dev)
Seen through a software-engineering lens, this is a classic state-dependent validation failure. The code is correct in one branch and unsafe in another, which is often harder to catch than a uniformly broken function. Reviewers may focus on the obvious branch because it contains the explicit check, while the alternate traversal path hides the real hazard behind a state transition that looks benign during code inspection. (osv.dev)
This is also why automated fuzzing and runtime sanitizers remain so valuable. The Ubuntu record includes a KASAN-detected out-of-bounds event, which implies the bug is observable under instrumentation before it becomes a customer incident. In security engineering terms, that is fortunate: it means the issue can be reproduced, understood, and patched using concrete evidence rather than speculation. (osv.dev)
The current Ubuntu record also shows that several releases are already fixed while others remain vulnerable or unsupported. For example, the page lists fixes for Ubuntu 24.04 LTS, 22.04 LTS, 20.04 LTS, and current development or interim branches, while older EOL releases remain vulnerable or ignored because they are outside standard support. That is the familiar but painful reality of kernel security: the newest supported branches are easier to patch, but the long tail can linger in production for years. (staging.ubuntu.com)
There is also an operational wrinkle: many orgs do not think of kernel security modules as patch candidates in the same way they think of browsers or OpenSSL. But because the vulnerability sits in a kernel parser path, it must be handled with the same urgency as other high-severity kernel bugs. In practice, that means maintenance windows, kernel version inventories, and reboot planning matter just as much as the patch itself. (osv.dev)
The consumer concern is less about targeted exploitation by random attackers and more about collateral exposure from packaging and distribution churn. A malformed local package, a bad administrative script, or a compromised management agent could still poke the vulnerable path on a desktop or workstation. That is enough to justify patching, because local kernel crashes are disproportionately frustrating on personal machines where the user often lacks the operational controls enterprise teams take for granted. (osv.dev)
That said, consumers should keep the threat model in perspective. This is not a mass remote worm bug in the classic sense. It is a high-severity kernel flaw that matters most when an attacker can reach a local policy-management path or when a compromised local process can feed malicious data into AppArmor’s verifier. Important, yes; universally exploitable from a browser tab, no. (osv.dev)
That matters because defenders should not treat the presence of one fixed CVE as evidence that the entire module is now safe. Security modules are large, stateful, and historically under-studied compared with flashier userland targets. Once researchers start finding one category of bug, adjacent logic often deserves renewed scrutiny. The fact that Ubuntu’s records and related advisories point to several AppArmor weaknesses reinforces that view.
This makes the broader response important. Patching CVE-2026-23407 is necessary, but it should also trigger a review of adjacent AppArmor code paths, especially around array indexing, recursive data walks, and any logic that decodes compact representations before validation. Defense in depth only works when each layer is tested as if it were the only layer. (osv.dev)
For defenders, the event creates an opportunity to tighten operational discipline around kernel and LSM updates. Organizations that already inventory kernel branches, map image provenance, and rehearse reboot windows will be better positioned than those that patch reactively. And for distribution maintainers, the disclosure reinforces the value of shipping signed fixes across all supported streams at once, rather than leaving security modules to drift. (staging.ubuntu.com)
Another concern is that the bug combines availability damage with potential memory corruption. That combination tends to complicate triage because outages may mask the original exploit and make forensics harder, while memory corruption raises the possibility of worse outcomes than a clean crash. In security terms, crash-only assumptions are dangerous here. (osv.dev)
It is also worth watching whether additional AppArmor-related advisories follow. The March 2026 CrackArmor disclosures showed that one bug family can rapidly expose neighboring weaknesses once researchers focus on the module’s parser and verifier code. If that pattern continues, CVE-2026-23407 may be remembered less as an isolated issue and more as part of a broader corrective cycle for Linux MAC frameworks.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Overview
Overview
AppArmor is one of Linux’s best-known mandatory access control systems, and on many enterprise and cloud deployments it is effectively part of the default trust model. It is widely used to confine applications, limit container breakout paths, and reduce the blast radius when a process is compromised. That makes any kernel bug in its policy-parsing and verification pipeline especially sensitive, because the attacker is not just poking at a userspace helper but at the core mechanism that decides whether a process may act at all.CVE-2026-23407 is notable because it is not a simple logic bug in policy enforcement, but a memory-safety failure in the code that validates AppArmor DFA data structures. The vulnerable path only checks DEFAULTTABLE bounds in one branch, and then assumes the index is safe when the DFA state is differentially encoded. That is precisely the kind of “safe in the common case, unsafe in the edge case” mistake that kernel attackers love, because malformed input can steer execution into a code path that developers do not exercise often enough in testing. (osv.dev)
The bug is also a reminder that security modules themselves have attack surface. AppArmor’s value comes from the fact that it sits very close to the kernel, but that proximity also means parser mistakes can become kernel bugs. In practice, the risk is strongest where systems accept policy updates from local administrators, orchestration agents, containers, or package-management workflows, because those are the pathways through which malformed or adversarial policy artifacts can reach the verifier.
What makes this case particularly relevant to WindowsForum readers is the broader pattern it illustrates: defense mechanisms can become the attack surface. AppArmor is meant to reduce risk, but a flaw in its verification logic can create exactly the opposite effect, especially when the resulting out-of-bounds access can be driven repeatedly. The latest Ubuntu security entry ties the issue to affected kernel packages across multiple supported releases, showing that the problem is not academic or limited to a single test build. (osv.dev)
What the bug actually does
At the center of the issue is a missing validation step in verify_dfa(). According to Ubuntu’s OSV record, the function only checks the bounds of the default table when the state is not differentially encoded; during traversal of the differential chain, it readsk = DEFAULT TABLE[j] and then uses that value as an array index without validating it. If DEFAULT TABLE[j] is greater than or equal to the number of states, the code can perform both invalid reads and invalid writes. (osv.dev)That distinction matters. A read-only overflow can leak kernel memory, crash a process, or corrupt internal logic. A write primitive, even if limited, is more dangerous because it can alter adjacent data structures and turn a parser bug into a broader kernel compromise. OSV’s description explicitly says the malformed DFA can cause both out-of-bounds reads and writes, which is why the issue is being treated as more than a harmless crash bug. (osv.dev)
Why the DEFAULT table matters
The DEFAULT table is part of the DFA structure AppArmor uses to represent policy behavior. A verifier is supposed to ensure that every index, transition, and fallback target remains inside the expected state space before the data is trusted. If one table entry can point outside that space, the verifier becomes a liability rather than a safeguard. That is the real lesson here: validation code has to be stricter than the data it is validating, not merely usually correct. (osv.dev)The kernel stack trace embedded in the Ubuntu record shows KASAN catching a slab-out-of-bounds read while
su was processing policy data. That indicates the bug is reachable in a realistic local workflow, not just in a synthetic fuzzing harness. It also tells us something important about exploitability: the issue sits in a hot path that is already designed to process untrusted policy input, which tends to make security-module bugs more dependable than many obscure kernel defects. (osv.dev)- The flaw is in policy verification, not just policy loading.
- The bad index can trigger out-of-bounds reads and writes.
- The bug is reachable through a local attack path.
- KASAN has already observed a slab-out-of-bounds condition.
- The issue lives inside a security module, so the impact can be counterintuitive. (osv.dev)
Availability impact and why MSRC-style language matters
The description provided in your prompt emphasizes total loss of availability or a serious, repeated denial of service. That framing is consistent with how high-severity kernel flaws are often classified when they can crash the system, disrupt service restart loops, or make a critical component unusable under ongoing attack. Even when the immediate consequence is a kernel warning or a single crash, the practical outcome in production can still be prolonged service outage if the vulnerable path is repeatedly triggered. (osv.dev)In AppArmor’s case, availability is not just about one host falling over. Because the module is used to enforce confinement policies across server estates, container hosts, and cloud images, a crash in the right place can affect a large number of workloads at once. In environments with automated remediation, the system may reboot, reapply the same policy, and fail again, creating an availability loop that is far more disruptive than a one-time fault.
Why a crash can be worse than it looks
A kernel crash in a lightly used lab box is annoying. A crash in a node that runs container orchestration, authentication, or fleet management is a platform incident. AppArmor’s role in defending those workloads means the blast radius depends less on the line of code and more on where that code sits in the architecture. That is why vulnerability databases often elevate “crash potential” when the crash is in a subsystem that is central to system policy enforcement.There is also a subtle issue around repeated exploitation. If an attacker can feed malformed policy data multiple times, they may not need a perfect one-shot exploit. Sustained denial can be enough to keep services offline, especially when policy refreshes, agent restarts, or health checks re-trigger the faulty verifier. That is one reason memory-safety bugs in kernel security paths are taken so seriously, even before exploit chaining is proven. (osv.dev)
- Kernel crashes can cascade into service restarts and node eviction.
- Repeated triggering can create persistent outage conditions.
- Security-module bugs often affect shared infrastructure, not just one app.
- Availability losses can be operationally severe even without RCE.
- Local bugs still matter in cloud and container estates when the host is shared.
Historical context: why AppArmor bugs keep drawing attention
AppArmor has been in the mainline Linux kernel since the 2010 era and ships enabled by default in several major Linux distributions. Its purpose is straightforward: confine processes with task-centric profiles so that even a compromised application cannot wander far outside its authorized behavior. That design has made it popular with Ubuntu users, container platforms, and organizations that want a practical MAC layer without the operational overhead of more elaborate frameworks.But the same familiarity can encourage complacency. Because AppArmor is often treated as a background control, administrators may assume that vulnerabilities in the module are unlikely or merely theoretical. Recent disclosure patterns have disabused the industry of that notion. Qualys’ March 2026 CrackArmor research, followed by Ubuntu’s coordinated vulnerability handling, showed that AppArmor issues can span denial of service, information disclosure, local privilege escalation, and container escape scenarios.
From “security layer” to attack surface
The bigger lesson is that a security layer is still software. It has parsers, verifiers, data structures, and edge cases, all of which can harbor bugs. When those bugs live inside the kernel, the impact is amplified because the bug can bypass normal userspace containment guarantees. In other words, AppArmor is valuable precisely because it is close to the kernel, but that is also why mistakes there are high leverage mistakes.The timing of these disclosures also matters. Ubuntu’s security data shows CVE-2026-23407 published on 1 April 2026 and modified on 8 April 2026, which suggests active triage and ongoing update work rather than a static, one-and-done advisory. For defenders, that usually means the patch ecosystem is still converging across releases, especially where long-term support kernels and OEM or cloud-flavored derivatives are involved. (osv.dev)
- AppArmor is widely deployed and often enabled by default.
- Security-module bugs can become kernel-level attack primitives.
- Recent AppArmor research has shown a broader pattern of serious flaws.
- Coordinated disclosure often leads to rolling package updates.
- Long-term support environments can take longer to fully converge.
Technical root cause in plain English
The bug stems from inconsistent bounds checking in a verifier that walks a DFA representation of policy. In the non-differential case, the code validates the DEFAULT table index. In the differential case, it trusts a value extracted from the table chain and uses it as an index without rechecking it. That asymmetry is what turns a malformed input into a memory-safety violation. (osv.dev)Seen through a software-engineering lens, this is a classic state-dependent validation failure. The code is correct in one branch and unsafe in another, which is often harder to catch than a uniformly broken function. Reviewers may focus on the obvious branch because it contains the explicit check, while the alternate traversal path hides the real hazard behind a state transition that looks benign during code inspection. (osv.dev)
Why differential encoding complicates security reviews
Differential encoding is a space-saving technique, but it makes correctness harder to reason about because one entry can implicitly depend on another. That means a simple “is this field in range?” question sometimes becomes “is this field, after decoding through several indirections, still in range?” Those are very different verification problems, and the second one is where memory bugs often hide. (osv.dev)This is also why automated fuzzing and runtime sanitizers remain so valuable. The Ubuntu record includes a KASAN-detected out-of-bounds event, which implies the bug is observable under instrumentation before it becomes a customer incident. In security engineering terms, that is fortunate: it means the issue can be reproduced, understood, and patched using concrete evidence rather than speculation. (osv.dev)
- Differential encoding increases reasoning complexity.
- The unsafe path is hidden behind an alternate traversal state.
- A single missed revalidation can become a write primitive.
- Sanitizers like KASAN are crucial for finding these bugs.
- Security bugs often live in the gap between expected invariants and actual control flow. (osv.dev)
Enterprise exposure and deployment realities
For enterprises, the most important question is not whether a CVE exists, but where the vulnerable code is actually active. AppArmor is especially common in Ubuntu-based fleets, cloud images, and container hosts, and Ubuntu’s vulnerability data shows affected packages across multiple kernel tracks, including general, HWE, and cloud-oriented builds. That makes this a fleet management problem as much as a vulnerability problem. (osv.dev)The current Ubuntu record also shows that several releases are already fixed while others remain vulnerable or unsupported. For example, the page lists fixes for Ubuntu 24.04 LTS, 22.04 LTS, 20.04 LTS, and current development or interim branches, while older EOL releases remain vulnerable or ignored because they are outside standard support. That is the familiar but painful reality of kernel security: the newest supported branches are easier to patch, but the long tail can linger in production for years. (staging.ubuntu.com)
Cloud, containers, and multi-tenant risk
Multi-tenant environments deserve special attention because a local privilege problem on one workload can still have platform-wide implications. If AppArmor is used to reduce container escape risk or to constrain tenant workloads, a flaw in the verifier can weaken the very boundary administrators are relying on. Even if the initial exploit requires local code execution, that is not a meaningful consolation when cloud workloads already assume an adversary can land code through a separate bug.There is also an operational wrinkle: many orgs do not think of kernel security modules as patch candidates in the same way they think of browsers or OpenSSL. But because the vulnerability sits in a kernel parser path, it must be handled with the same urgency as other high-severity kernel bugs. In practice, that means maintenance windows, kernel version inventories, and reboot planning matter just as much as the patch itself. (osv.dev)
- Ubuntu’s package matrix shows broad kernel coverage.
- Multi-tenant hosts can inherit cross-workload risk.
- Older EOL systems may stay exposed indefinitely.
- Kernel fixes usually require reboot coordination.
- Security modules are often overlooked in patch prioritization. (osv.dev)
Consumer and desktop implications
For consumer desktops, the practical exposure is narrower but still real. Most home users are unlikely to hand-craft malicious AppArmor DFAs, and many won’t knowingly interact with the affected code path at all. But modern Linux desktop security increasingly relies on policy frameworks, so the difference between “unlikely” and “impossible” is not one to dismiss lightly.The consumer concern is less about targeted exploitation by random attackers and more about collateral exposure from packaging and distribution churn. A malformed local package, a bad administrative script, or a compromised management agent could still poke the vulnerable path on a desktop or workstation. That is enough to justify patching, because local kernel crashes are disproportionately frustrating on personal machines where the user often lacks the operational controls enterprise teams take for granted. (osv.dev)
Why desktop users should still care
Desktop security often depends on a chain of trust that includes kernel-enforced confinement. If a flaw in AppArmor’s verification logic can destabilize that chain, the impact extends beyond one application. Users may experience service failures, lockups, or repeated crashes that are hard to diagnose because the root cause sits in the security layer, not the visible app.That said, consumers should keep the threat model in perspective. This is not a mass remote worm bug in the classic sense. It is a high-severity kernel flaw that matters most when an attacker can reach a local policy-management path or when a compromised local process can feed malicious data into AppArmor’s verifier. Important, yes; universally exploitable from a browser tab, no. (osv.dev)
- Home users still benefit from timely kernel updates.
- Local crashes can be disruptive even without data theft.
- Security frameworks can fail in ways that are opaque to users.
- The bug is serious, but it is not a broad remote-execution event.
- Desktop fleets that auto-apply updates are better positioned. (osv.dev)
How this compares with other AppArmor issues
CVE-2026-23407 should be understood alongside the broader AppArmor vulnerability wave reported in March and April 2026. Ubuntu’s blog and vulnerability database refer to a set of AppArmor-related issues collectively associated with CrackArmor, and Qualys highlighted multiple attack classes including privilege escalation, container escape, KASLR bypass, and denial of service. In that context, CVE-2026-23407 looks like one piece of a larger pattern rather than an isolated oddity.That matters because defenders should not treat the presence of one fixed CVE as evidence that the entire module is now safe. Security modules are large, stateful, and historically under-studied compared with flashier userland targets. Once researchers start finding one category of bug, adjacent logic often deserves renewed scrutiny. The fact that Ubuntu’s records and related advisories point to several AppArmor weaknesses reinforces that view.
The pattern behind the pattern
Most AppArmor bugs in this cycle revolve around trust boundaries that were assumed to be safe but were not. Whether the issue is profile loading, policy replacement, parser behavior, or verifier logic, the common thread is that the kernel accepted malformed or adversarial input too far into the pipeline. That is a recurring theme in Linux security work: the parser is often the first place developers think to harden, but the verifier and cleanup paths can be just as dangerous. (osv.dev)This makes the broader response important. Patching CVE-2026-23407 is necessary, but it should also trigger a review of adjacent AppArmor code paths, especially around array indexing, recursive data walks, and any logic that decodes compact representations before validation. Defense in depth only works when each layer is tested as if it were the only layer. (osv.dev)
- The issue fits a broader CrackArmor pattern.
- Adjacent verifier paths deserve additional review.
- One fixed CVE does not guarantee the rest are safe.
- Recursive or encoded data structures deserve extra scrutiny.
- Kernel security layers need continuous hardening, not one-time cleanup.
Strengths and Opportunities
The good news is that this class of issue is usually fixable in a straightforward way once it is identified. Ubuntu’s record says the corrective action is to validate all DEFAULT table entries unconditionally, which is the kind of targeted patch security teams can reason about, test, and ship quickly. It is also a reminder that modern kernel tooling can catch these issues before they become widespread incidents. (osv.dev)For defenders, the event creates an opportunity to tighten operational discipline around kernel and LSM updates. Organizations that already inventory kernel branches, map image provenance, and rehearse reboot windows will be better positioned than those that patch reactively. And for distribution maintainers, the disclosure reinforces the value of shipping signed fixes across all supported streams at once, rather than leaving security modules to drift. (staging.ubuntu.com)
- The fix appears to be surgical and testable.
- Sanitizer evidence speeds up verification.
- Kernel inventory practices become more valuable.
- Supported releases can be patched in a coordinated way.
- The incident may improve scrutiny of other security-module code paths.
- Fleet-wide update automation is a real advantage.
- The disclosure reinforces why defense layers must be maintained like any other code. (osv.dev)
Risks and Concerns
The main concern is that the vulnerability sits in a code path designed to process policy data, which means the bug is reachable by an attacker who can get malformed input into the right workflow. Even if that workflow is “local only,” local is still a meaningful foothold in modern enterprise environments, particularly on shared hosts, build systems, and administrative jump boxes. A local kernel flaw can be the difference between a contained compromise and a full host takeover. (osv.dev)Another concern is that the bug combines availability damage with potential memory corruption. That combination tends to complicate triage because outages may mask the original exploit and make forensics harder, while memory corruption raises the possibility of worse outcomes than a clean crash. In security terms, crash-only assumptions are dangerous here. (osv.dev)
- Attackers may only need local code execution or local policy access.
- Availability failures can hide the underlying exploit path.
- Memory corruption broadens the risk beyond simple DoS.
- Multi-tenant systems have a larger potential blast radius.
- EOL systems may remain exposed for long periods.
- Administrators may underestimate security-module CVEs because they are not user-facing.
- Recovery loops can turn an isolated crash into ongoing downtime. (osv.dev)
Looking Ahead
The next few days and weeks will likely be about patch propagation, package verification, and confirmation that all supported Ubuntu kernel streams are aligned on the fix. Because the OSV record was modified on 8 April 2026, there is already evidence of active maintenance work, but that does not mean every downstream image has caught up. The usual gap between upstream availability and operational deployment remains the practical risk window. (osv.dev)It is also worth watching whether additional AppArmor-related advisories follow. The March 2026 CrackArmor disclosures showed that one bug family can rapidly expose neighboring weaknesses once researchers focus on the module’s parser and verifier code. If that pattern continues, CVE-2026-23407 may be remembered less as an isolated issue and more as part of a broader corrective cycle for Linux MAC frameworks.
What to watch next
- Confirmation that all supported kernel streams have received the fix.
- Whether downstream vendors issue additional advisories for the same code path.
- Signs of exploit chaining with other AppArmor weaknesses.
- Enterprise guidance on reboot scheduling and fleet validation.
- Any follow-on hardening in AppArmor’s DFA verification logic.
- Whether other security modules receive similar scrutiny after this disclosure. (osv.dev)
Source: MSRC Security Update Guide - Microsoft Security Response Center