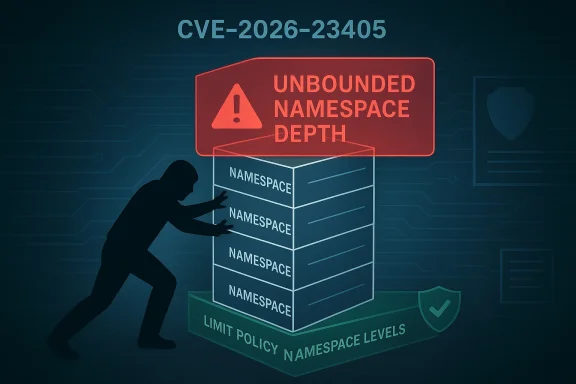
CVE-2026-23405 exposes a deceptively simple AppArmor flaw with potentially serious consequences: the Linux security module did not properly bound the number of levels in policy namespaces. In practical terms, that means a local attacker could potentially construct an excessively deep namespace chain and stress assumptions in the kernel’s AppArmor policy machinery. The fix, summarized by the kernel as “limit the number of levels of policy namespaces,” is a reminder that security boundaries are only as strong as the metadata structures that support them.
AppArmor has become one of the most important hardening layers in modern Linux, especially across Ubuntu and other enterprise-focused distributions that ship it by default or rely on it heavily. It works by enforcing mandatory access control policies that constrain what programs can do, even when traditional discretionary permissions would otherwise allow it. Over the last few release cycles, AppArmor’s role has expanded beyond classic file and process mediation to include deeper kernel interfaces, including user namespaces and container-related paths.
That expansion has improved security posture, but it has also enlarged the attack surface. The kernel and userspace components that implement AppArmor policy handling now have to reason about more layers of inheritance, more nested contexts, and more opportunities for policy confusion. The recent wave of AppArmor disclosures in 2026 underscores that a mature security subsystem can still harbor structural weaknesses when its namespace model is not tightly constrained.
CVE-2026-23405 fits into that pattern. The issue is not a flashy memory corruption bug or a dramatic remote exploit. Instead, it is a structural flaw in how AppArmor policy namespaces are allowed to stack. The danger is that unbounded depth can undermine kernel robustness, create opportunities for privilege escalation, or at minimum open the door to denial-of-service conditions and policy-management instability.
The advisory landscape around AppArmor in early 2026 suggests this was not an isolated finding. Ubuntu’s March 2026 kernel notices explicitly refer to multiple AppArmor issues discovered by Qualys, including flaws that could allow an unprivileged attacker to load, replace, or remove arbitrary AppArmor profiles, with outcomes ranging from denial of service to local privilege escalation and possible container escape. CVE-2026-23405 is one piece of that broader security picture, and the fact that the kernel patch is narrowly framed suggests a targeted hardening response rather than a wholesale redesign.
The key takeaway is that AppArmor’s namespace machinery has become important enough that its limits matter as much as its rules. When policy namespaces can grow without a strict ceiling, the system inherits an unnecessary risk profile. Security engineering often fails not because the main logic is wrong, but because boundary conditions are under-specified, and this vulnerability looks very much like that kind of boundary failure.
The problem with any namespace hierarchy is that nesting can become a resource and logic problem at the same time. Each additional layer increases bookkeeping, and each level can add complexity to policy evaluation, credential inheritance, and kernel-side accounting. If the number of levels is not constrained, an attacker may be able to force edge-case behavior that the original design did not intend to support.
That evolution was partly driven by the rise of sandboxed applications, browser isolation, and container workflows. Distributions increasingly wanted to allow legitimate applications to use unprivileged user namespaces while still blocking unsafe patterns. The result was a more nuanced AppArmor policy model, but nuance comes with cost: more knobs, more states, and more chances for implementation gaps.
That kind of change also suggests the developers preferred predictable enforcement over trying to infer safe behavior dynamically. A fixed limit is easier to audit, easier to test, and easier to document. It may not feel elegant, but in kernel code predictable restraint is often the right answer.
The structure of the vulnerability set matters. A flaw that affects policy loading, a flaw that affects namespace handling, and a flaw that affects memory safety are very different bugs technically, but operationally they all attack the same trust layer. For defenders, that means one subsystem can create multiple classes of exposure, and the patch cadence becomes a measure of how quickly vendors can reassert control.
The hard part for consumer ecosystems is that confinement features are increasingly intertwined with normal app behavior. Ubuntu’s work on restricted unprivileged user namespaces, for example, was designed to let applications like browsers continue working while preserving sensible defaults. That means a fix to one security boundary can affect the usability of another, and users may perceive it as instability even when it is a security correction.
The tricky part is that enterprises often customize AppArmor heavily. Policies are tuned, exceptions are added, and workloads rely on profiles that have evolved over years. A flaw in namespace policy handling can therefore intersect with bespoke rule sets in unexpected ways, which increases validation effort after patching.
That lesson is not limited to AppArmor. Modern Linux hardening increasingly depends on stacked mechanisms: namespaces, cgroups, seccomp, MAC frameworks, capabilities, and container orchestration policies. Each layer solves a real problem, but interactions between layers are often where vulnerabilities hide. Security teams should expect the next wave of kernel findings to keep focusing on inter-layer assumptions rather than on obvious memory bugs alone.
Another strength is that this issue has forced attention onto a part of Linux security that is often invisible until it fails. That is uncomfortable, but useful. Better documentation, better test coverage, and more explicit policy limits can come out of a disclosure like this, especially for distributions that have already invested in AppArmor as a default control.
A second concern is patch inconsistency. AppArmor is deeply embedded across multiple Ubuntu kernel flavors and related enterprise branches, and not every environment updates on the same schedule. If the fix lands unevenly, operators may incorrectly assume their fleets are safe simply because one package stream was updated.
There is also a good chance this CVE becomes a reference point in discussions about the cost of security expressiveness. AppArmor is trying to do more, not less, and that ambition is reasonable. But the more powerful a policy system becomes, the more it depends on disciplined limits, especially when policies can be nested through namespaces and inherited across contexts.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Overview
Overview
AppArmor has become one of the most important hardening layers in modern Linux, especially across Ubuntu and other enterprise-focused distributions that ship it by default or rely on it heavily. It works by enforcing mandatory access control policies that constrain what programs can do, even when traditional discretionary permissions would otherwise allow it. Over the last few release cycles, AppArmor’s role has expanded beyond classic file and process mediation to include deeper kernel interfaces, including user namespaces and container-related paths.That expansion has improved security posture, but it has also enlarged the attack surface. The kernel and userspace components that implement AppArmor policy handling now have to reason about more layers of inheritance, more nested contexts, and more opportunities for policy confusion. The recent wave of AppArmor disclosures in 2026 underscores that a mature security subsystem can still harbor structural weaknesses when its namespace model is not tightly constrained.
CVE-2026-23405 fits into that pattern. The issue is not a flashy memory corruption bug or a dramatic remote exploit. Instead, it is a structural flaw in how AppArmor policy namespaces are allowed to stack. The danger is that unbounded depth can undermine kernel robustness, create opportunities for privilege escalation, or at minimum open the door to denial-of-service conditions and policy-management instability.
The advisory landscape around AppArmor in early 2026 suggests this was not an isolated finding. Ubuntu’s March 2026 kernel notices explicitly refer to multiple AppArmor issues discovered by Qualys, including flaws that could allow an unprivileged attacker to load, replace, or remove arbitrary AppArmor profiles, with outcomes ranging from denial of service to local privilege escalation and possible container escape. CVE-2026-23405 is one piece of that broader security picture, and the fact that the kernel patch is narrowly framed suggests a targeted hardening response rather than a wholesale redesign.
The key takeaway is that AppArmor’s namespace machinery has become important enough that its limits matter as much as its rules. When policy namespaces can grow without a strict ceiling, the system inherits an unnecessary risk profile. Security engineering often fails not because the main logic is wrong, but because boundary conditions are under-specified, and this vulnerability looks very much like that kind of boundary failure.
How AppArmor Namespace Policy Works
AppArmor policy namespaces exist to allow distinct policy views and layered confinement. They are not merely administrative wrappers; they shape how profiles are resolved and how policy decisions are inherited across contexts. In a system that uses user namespaces and container workloads, those boundaries become even more relevant because policy stacks are expected to remain predictable as tasks move into nested environments.The problem with any namespace hierarchy is that nesting can become a resource and logic problem at the same time. Each additional layer increases bookkeeping, and each level can add complexity to policy evaluation, credential inheritance, and kernel-side accounting. If the number of levels is not constrained, an attacker may be able to force edge-case behavior that the original design did not intend to support.
Why depth limits matter
A depth limit is not just a housekeeping choice. It is a security control that prevents recursion-like behavior from becoming an attack primitive. Systems with layered security models need hard ceilings to prevent nested contexts from becoming a vector for exhaustion or subtle bypass.- Unbounded nesting can amplify kernel bookkeeping costs.
- Complex inheritance chains are harder to reason about correctly.
- Resource exhaustion can become a denial-of-service path.
- Policy confusion becomes more likely as layers multiply.
- Auditing gets harder when namespace ancestry is too deep.
The Security Context in 2026
By 2026, AppArmor was no longer just a desktop Linux hardening tool. It had become a foundational control in distributions that aim to support enterprise desktops, cloud images, container hosts, and workstation security. Ubuntu’s own documentation and release notes show a steady evolution of AppArmor’s role, including support for mediating user namespaces and other kernel interfaces that have historically expanded attack surface.That evolution was partly driven by the rise of sandboxed applications, browser isolation, and container workflows. Distributions increasingly wanted to allow legitimate applications to use unprivileged user namespaces while still blocking unsafe patterns. The result was a more nuanced AppArmor policy model, but nuance comes with cost: more knobs, more states, and more chances for implementation gaps.
Why this matters for enterprises
Enterprises do not just care whether a vulnerability exists. They care whether the vulnerability breaks a layered defense strategy that they assumed was reliable. AppArmor is often deployed precisely because organizations want a MAC layer that survives application mistakes and compensates for privilege creep. When the MAC layer itself has namespace-handling flaws, the confidence penalty can be significant.- Cloud operators depend on AppArmor for container isolation support.
- Desktop fleets rely on it to confine browsers and productivity tools.
- Compliance teams view it as evidence of least-privilege enforcement.
- Security architects use it to reduce blast radius after endpoint compromise.
- Support teams need vendor backports that are timely and complete.
What the Fix Suggests
The patch description is short, but its implications are meaningful. “Limit the number of levels of policy namespaces” tells us the bug likely involved an absence of a hard boundary, rather than a sophisticated exploit chain. In security engineering, that usually means the safest response is a conservative cap that restores invariants the subsystem should have enforced from the beginning.That kind of change also suggests the developers preferred predictable enforcement over trying to infer safe behavior dynamically. A fixed limit is easier to audit, easier to test, and easier to document. It may not feel elegant, but in kernel code predictable restraint is often the right answer.
Why fixed ceilings are common in kernel hardening
Kernel subsystems often use explicit ceilings for recursion, nesting, or table growth because unbounded structures are fragile under adversarial inputs. AppArmor policy namespaces are part security model and part kernel data structure, so they are exactly the kind of component that benefits from a limit. Once a namespace tree becomes too deep, the cost of evaluation and the likelihood of implementation mistakes both rise.- Deterministic behavior is easier to verify.
- Security review is simpler when limits are explicit.
- Backporting is less risky when the fix is narrow.
- Regression testing can focus on boundary cases.
- Operational predictability improves for distro maintainers.
Relationship to the 2026 AppArmor Disclosure Wave
CVE-2026-23405 did not arrive in a vacuum. In March 2026, multiple sources pointed to a set of AppArmor vulnerabilities that affected millions of Linux systems, especially in Ubuntu, Debian, and SUSE ecosystems where AppArmor is heavily used. Those reports described a range of impacts, from denial of service to privilege escalation and container escape, showing that AppArmor had entered a period of unusually intense scrutiny.The structure of the vulnerability set matters. A flaw that affects policy loading, a flaw that affects namespace handling, and a flaw that affects memory safety are very different bugs technically, but operationally they all attack the same trust layer. For defenders, that means one subsystem can create multiple classes of exposure, and the patch cadence becomes a measure of how quickly vendors can reassert control.
Why clustered disclosures are especially disruptive
When several issues in the same subsystem appear together, administrators are forced to treat the subsystem as temporarily suspect. Even if each CVE has a unique root cause, the practical response is usually the same: patch aggressively, verify kernel provenance, and validate confinement behavior after reboot. That is a heavier lift than a single isolated issue.- Patch prioritization becomes urgent across multiple kernel branches.
- Rollback plans need to account for confinement regressions.
- Container hosts require extra validation after kernel updates.
- Desktop users may experience behavior changes in sandboxed apps.
- Vulnerability management teams need clearer mapping between CVEs and packages.
Impact on Consumers and Desktops
For consumer Linux users, especially those on Ubuntu-derived systems, the immediate concern is not arcane namespace theory. It is whether the machine is protected against local compromise and whether a security update changes the behavior of applications that depend on AppArmor allowances. User-facing risks are often indirect, but they can still be serious if an attacker gains a foothold through a browser, file preview, or untrusted app.The hard part for consumer ecosystems is that confinement features are increasingly intertwined with normal app behavior. Ubuntu’s work on restricted unprivileged user namespaces, for example, was designed to let applications like browsers continue working while preserving sensible defaults. That means a fix to one security boundary can affect the usability of another, and users may perceive it as instability even when it is a security correction.
What users may notice
Most users will not notice CVE-2026-23405 directly, which is usually a sign that the kernel change is doing its job. They may, however, notice a reboot into a newer kernel, changes in how confined applications behave, or a package update that resolves a security notice without fanfare. Those are the healthy outcomes; the unhealthy outcome is when the flaw remains unpatched because it is assumed to be “just AppArmor.”- Security updates may arrive through normal distro channels.
- Sandboxed apps should be tested after kernel refreshes.
- Local admin tools that manipulate AppArmor policies deserve attention.
- Desktop gaming and browser sandboxing can expose namespace edge cases.
- Users on older releases may rely on backported fixes rather than kernel upgrades.
Impact on Enterprises and Cloud Operators
For enterprise operators, the stakes are higher because AppArmor often sits underneath container platforms, CI/CD hosts, developer workstations, and managed endpoint fleets. A namespace-depth issue in AppArmor is not merely a workstation bug; it can become part of a broader defense-in-depth failure if local compromise leads to container breakout or policy manipulation. That is why enterprise Linux advisories about AppArmor typically emphasize both local privilege escalation and isolation bypass risk.The tricky part is that enterprises often customize AppArmor heavily. Policies are tuned, exceptions are added, and workloads rely on profiles that have evolved over years. A flaw in namespace policy handling can therefore intersect with bespoke rule sets in unexpected ways, which increases validation effort after patching.
Operational consequences
Security teams should think about patching CVE-2026-23405 as part of a broader kernel hardening action, not as a standalone checkbox. In cloud and datacenter environments, the right response usually involves updating kernel packages, verifying AppArmor status, and checking that container runtimes or service profiles still behave as expected. This is especially true on systems where AppArmor mediates user namespace creation or where profiles are used to gate high-risk workloads.- Container hosts should be patched first.
- Jump hosts and bastions deserve early validation.
- CI runners may surface regressions faster than production.
- Endpoint fleets need rollback-ready patch orchestration.
- Change windows should include AppArmor-specific testing.
Broader Linux Security Lessons
CVE-2026-23405 illustrates a broader truth about Linux security architecture: modularity is powerful, but every new layer adds policy state that can be mismanaged. AppArmor’s namespace capabilities were designed to increase flexibility and make policy more expressive, yet those same features require strict accounting to avoid opening a loophole. The more expressive the security model, the more likely it is that boundary checks become the real attack surface.That lesson is not limited to AppArmor. Modern Linux hardening increasingly depends on stacked mechanisms: namespaces, cgroups, seccomp, MAC frameworks, capabilities, and container orchestration policies. Each layer solves a real problem, but interactions between layers are often where vulnerabilities hide. Security teams should expect the next wave of kernel findings to keep focusing on inter-layer assumptions rather than on obvious memory bugs alone.
The policy-complexity trap
The policy-complexity trap is simple to describe and hard to fix. Every time a security subsystem becomes more expressive, it also becomes harder to prove safe in every combination of nested context. AppArmor’s movement toward more nuanced namespace mediation is useful, but it also increases the chance that one path is inadvertently left unbounded or under-checked.- More expressiveness means more state to validate.
- More namespace support means more inheritance cases.
- More kernel hooks mean more chance for edge-case drift.
- More backports mean more room for patch divergence.
- More distro customization means more operational variance.
Strengths and Opportunities
The immediate strength of the response to CVE-2026-23405 is that the problem appears to have a narrow, enforceable fix. A bounded namespace depth is easy to reason about, and that makes it easier for vendors to backport without destabilizing unrelated AppArmor behavior. It also gives administrators a clear story: update the kernel, verify AppArmor behavior, and keep moving.Another strength is that this issue has forced attention onto a part of Linux security that is often invisible until it fails. That is uncomfortable, but useful. Better documentation, better test coverage, and more explicit policy limits can come out of a disclosure like this, especially for distributions that have already invested in AppArmor as a default control.
- Clearer kernel invariants around namespace depth.
- Better regression testing for AppArmor policy stacks.
- Stronger distro hardening through conservative defaults.
- Improved operator awareness of AppArmor’s role in isolation.
- More explicit policy guidance for enterprise deployments.
- Opportunity to audit other namespace-related assumptions.
- Potential upstream cleanup beyond the immediate CVE.
Risks and Concerns
The biggest concern is that local privilege escalation bugs are often underestimated when they involve security layers rather than flashy drivers. A flaw in AppArmor can be dismissed as “just policy,” but policy bugs can still affect the kernel’s trust boundaries and the safety of containers or user namespaces. That makes underreaction a real risk, especially on systems where AppArmor is assumed to be a protective layer rather than an attack surface.A second concern is patch inconsistency. AppArmor is deeply embedded across multiple Ubuntu kernel flavors and related enterprise branches, and not every environment updates on the same schedule. If the fix lands unevenly, operators may incorrectly assume their fleets are safe simply because one package stream was updated.
The operational risk profile
The operational risk is compounded when confinement behavior changes after a kernel update. Systems that depend on fine-grained AppArmor policies may experience unexpected denials, which can lead administrators to disable or weaken protections in the name of uptime. That would be the worst outcome: a security patch that indirectly encourages insecure workarounds.- Delayed patching leaves local attack paths open.
- Incomplete backports can create false confidence.
- Regression-driven disablement can weaken overall security.
- Container hosts may be especially sensitive to policy shifts.
- Desktop users may tolerate security risk to avoid app breakage.
- Poor communication can turn a narrow CVE into a broader support problem.
- Overreliance on AppArmor can obscure other hardening gaps.
Looking Ahead
The immediate future for CVE-2026-23405 is straightforward: vendors will continue shipping fixes through kernel update streams, and administrators will need to verify that AppArmor confinement still behaves as expected after those updates. The more interesting question is whether this disclosure leads to broader review of namespace boundaries in AppArmor and adjacent security modules. Given the cluster of AppArmor issues already surfacing in 2026, the answer should probably be yes.There is also a good chance this CVE becomes a reference point in discussions about the cost of security expressiveness. AppArmor is trying to do more, not less, and that ambition is reasonable. But the more powerful a policy system becomes, the more it depends on disciplined limits, especially when policies can be nested through namespaces and inherited across contexts.
What to watch next
- Vendor advisories mapping CVE-2026-23405 to specific kernel package versions.
- Backport coverage across Ubuntu, Debian, and enterprise derivatives.
- Follow-up AppArmor fixes if related namespace assumptions are found.
- Container-runtime testing after kernel rollouts.
- Documentation updates explaining namespace-depth expectations.
Source: MSRC Security Update Guide - Microsoft Security Response Center